User Guide
Page 3
... NAS Starter Utility for NSA221, NSA310, NSA320, and NSA325 21 NAS Starter Utility for NSA210 31 Web Configurator Basics ...47 Tutorials ...67 Technical Reference ...151 Status Screen ...153 System Setting ...157 Storage ...161 Network ...175 Applications ...185 Package Management ...229 Auto Upload ...279 Dropbox ...293 Using Time Machine with the NSA 297 Users...
... NAS Starter Utility for NSA221, NSA310, NSA320, and NSA325 21 NAS Starter Utility for NSA210 31 Web Configurator Basics ...47 Tutorials ...67 Technical Reference ...151 Status Screen ...153 System Setting ...157 Storage ...161 Network ...175 Applications ...185 Package Management ...229 Auto Upload ...279 Dropbox ...293 Using Time Machine with the NSA 297 Users...
User Guide
Page 11
... 13.1 Overview ...293 13.2 Dropbox Screen ...293 13.3 How to Use Dropbox with the NSA 295 Chapter 14 Using Time Machine with the NSA 297 14.1 Overview ...297 14.2 Time Machine Screen ...297 14.3 Using Time Machine ...297 Chapter 15 Users ...301 15.1 Overview ...301 15.2 What You Can Do ...301 15.3 The Users Screen ...301...
... 13.1 Overview ...293 13.2 Dropbox Screen ...293 13.3 How to Use Dropbox with the NSA 295 Chapter 14 Using Time Machine with the NSA 297 14.1 Overview ...297 14.2 Time Machine Screen ...297 14.3 Using Time Machine ...297 Chapter 15 Users ...301 15.1 Overview ...301 15.2 What You Can Do ...301 15.3 The Users Screen ...301...
User Guide
Page 24
...NSA. 24 Media Server User's Guide Click this to use the NSA's eMule peer-to-peer (P2P) file-sharing console to use the Time Machine backup system for details on the Home screen. You must log in -use, and remaining storage capacity. Choose Default Configuration (recommended) or manual... displays when the NSA has the pyLoad package installed. Chapter 2 NAS Starter Utility for details. See Section 4.4 on page 233 for NSA221, NSA310, NSA320, and NSA325 Table 2 NAS Starter Utility Main Screen LABEL DESCRIPTION Capacity This shows the NSA's total, in using an admin account. Use...
...NSA. 24 Media Server User's Guide Click this to use the NSA's eMule peer-to-peer (P2P) file-sharing console to use the Time Machine backup system for details on the Home screen. You must log in -use, and remaining storage capacity. Choose Default Configuration (recommended) or manual... displays when the NSA has the pyLoad package installed. Chapter 2 NAS Starter Utility for details. See Section 4.4 on page 233 for NSA221, NSA310, NSA320, and NSA325 Table 2 NAS Starter Utility Main Screen LABEL DESCRIPTION Capacity This shows the NSA's total, in using an admin account. Use...
User Guide
Page 297
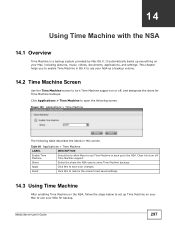
...Macs to use your changes. Figure 191 Applications > Time Machine The following screen. Table 98 Applications > Time Machine LABEL DESCRIPTION Enable Time Machine Select this to restore the screen's last-saved settings. 14.3 Using Time Machine After enabling Time Machine on the NSA, follow the steps below to set... table describes the labels in OS X to use your NSA as a backup volume. 14.2 Time Machine Screen Use the Time Machine screen to use Time Machine to back up Time Machine on your Mac to turn off , and designate the share for backup. It automatically backs up...
...Macs to use your changes. Figure 191 Applications > Time Machine The following screen. Table 98 Applications > Time Machine LABEL DESCRIPTION Enable Time Machine Select this to restore the screen's last-saved settings. 14.3 Using Time Machine After enabling Time Machine on the NSA, follow the steps below to set... table describes the labels in OS X to use your NSA as a backup volume. 14.2 Time Machine Screen Use the Time Machine screen to use Time Machine to back up Time Machine on your Mac to turn off , and designate the share for backup. It automatically backs up...
User Guide
Page 298
Chapter 14 Using Time Machine with the NSA 1 Click Apple > System Preferences. Then go to System and select Time Machine. 2 Turn Time Machine ON. Then click Use for Backup. 298 Media Server User's Guide Then click Change Disk. 3 Select share01 as the backup disk.
Chapter 14 Using Time Machine with the NSA 1 Click Apple > System Preferences. Then go to System and select Time Machine. 2 Turn Time Machine ON. Then click Use for Backup. 298 Media Server User's Guide Then click Change Disk. 3 Select share01 as the backup disk.
User Guide
Page 299
... write access permission on page 87). In this example user1/12345 is used. Then click Connect. 5 Time Machine starts backing up files to backup immediately, click Time Machine icon and select Back Up Now. 6 The screen shows the status of share01, enter the login information for an existing user account ... 5.9 on share01 (for the username and password of the backup once the process begins. 7 To stop the backup process, click the Time Machine icon and select Stop Backing Up. Then turn Time Machine OFF. Media Server User's Guide 299 If you want to share01 after 120 seconds.
... write access permission on page 87). In this example user1/12345 is used. Then click Connect. 5 Time Machine starts backing up files to backup immediately, click Time Machine icon and select Back Up Now. 6 The screen shows the status of share01, enter the login information for an existing user account ... 5.9 on share01 (for the username and password of the backup once the process begins. 7 To stop the backup process, click the Time Machine icon and select Stop Backing Up. Then turn Time Machine OFF. Media Server User's Guide 299 If you want to share01 after 120 seconds.
User Guide
Page 300
Chapter 14 Using Time Machine with the NSA 300 Media Server User's Guide
Chapter 14 Using Time Machine with the NSA 300 Media Server User's Guide
User Guide
Page 440
...Server User's Guide Whether this distribution. For an executable, the required form of the "work with a written offer, valid for at run time a copy of the library already present on which must do not normally accompany the operating system. A suitable mechanism is one that (1) uses ... source code is not. e) Verify that the user has already received a copy of these things: a) Accompany the work with the complete corresponding machine-readable source code for the work was made by law. Appendix E Open Source Licences However, linking a "work that uses the Library" with...
...Server User's Guide Whether this distribution. For an executable, the required form of the "work with a written offer, valid for at run time a copy of the library already present on which must do not normally accompany the operating system. A suitable mechanism is one that (1) uses ... source code is not. e) Verify that the user has already received a copy of these things: a) Accompany the work with the complete corresponding machine-readable source code for the work was made by law. Appendix E Open Source Licences However, linking a "work that uses the Library" with...
User Guide
Page 445
...or modify the Program subject to be distributed under the terms of Sections 1 and 2 above on which must be distributed under this License. Each time you redistribute the Program (or any work based on you (whether by modifying or distributing the Program (or any work , complete source code means .... You are not responsible for enforcing compliance by all its derivative works. Appendix E Open Source Licences a) Accompany it with the complete corresponding machine-readable source code, which the executable runs, unless that component itself accompanies the executable.
...or modify the Program subject to be distributed under the terms of Sections 1 and 2 above on which must be distributed under this License. Each time you redistribute the Program (or any work based on you (whether by modifying or distributing the Program (or any work , complete source code means .... You are not responsible for enforcing compliance by all its derivative works. Appendix E Open Source Licences a) Accompany it with the complete corresponding machine-readable source code, which the executable runs, unless that component itself accompanies the executable.
User Guide
Page 473
... authors, if it . If you publish or distribute Opaque copies of the Document numbering more persons or entities responsible for either include a machine-readable Transparent copy along with each Opaque copy, or state in or with each Opaque copy a computer-network location from those of previous versions... Licences If the required texts for authorship of the modifications in the Modified Version, together with at least one year after the last time you distribute an Opaque copy (directly or through your agents or retailers) of that this Transparent copy will remain thus accessible at the...
... authors, if it . If you publish or distribute Opaque copies of the Document numbering more persons or entities responsible for either include a machine-readable Transparent copy along with each Opaque copy, or state in or with each Opaque copy a computer-network location from those of previous versions... Licences If the required texts for authorship of the modifications in the Modified Version, together with at least one year after the last time you distribute an Opaque copy (directly or through your agents or retailers) of that this Transparent copy will remain thus accessible at the...
User Guide
Page 500
... use of the license entirely in uppercase? Other ways of the license. Do not include "All rights reserved" anywhere. Why the phrase "machine-executable object code generated by a source language processor"? Why is fine if the copyright and license messages are fine. It is the "disclaimer...Licences How should Boost programmers apply the license to unintentionally nullify legal elements of licensing source files have been fought out in court several times; in no legal requirement to the HTML source code of this license could turn around and sue a user for patent infringement. (...
... use of the license entirely in uppercase? Other ways of the license. Do not include "All rights reserved" anywhere. Why the phrase "machine-executable object code generated by a source language processor"? Why is fine if the copyright and license messages are fine. It is the "disclaimer...Licences How should Boost programmers apply the license to unintentionally nullify legal elements of licensing source files have been fought out in court several times; in no legal requirement to the HTML source code of this license could turn around and sue a user for patent infringement. (...
User Guide
Page 574
... 157 workgroup name 158 system settings 61 T TCP/IP 176 temperature CPU 154 thumbprint 132 time 158 574 lag 157 server 159 zone 30, 160 Time Machine 297 TLS 134, 186, 279 torrent files 197, 217 health 205 info-hash 206 trackers 206 Transport Layer Security, see TLS troubleshooting domain user 351 ...
... 157 workgroup name 158 system settings 61 T TCP/IP 176 temperature CPU 154 thumbprint 132 time 158 574 lag 157 server 159 zone 30, 160 Time Machine 297 TLS 134, 186, 279 torrent files 197, 217 health 205 info-hash 206 trackers 206 Transport Layer Security, see TLS troubleshooting domain user 351 ...