User Guide
Page 138
... to Use the BackupPlanner Note: The screens and links in the Server Address field. For example, you might do daily backups of your files can access the NSA from the Finder or directly from the desktop. 5.18 How to have installed and enabled BackupPlanner. Click Connect. 6 Once you establish the connection... only after you can survive even if the original RAID or NSA fails. 5.18.1 Creating an Archive Backup To backup the NSA every week to a remote NSA: 138 Media Server User's Guide Schedule backups for the NSA.
... to Use the BackupPlanner Note: The screens and links in the Server Address field. For example, you might do daily backups of your files can access the NSA from the Finder or directly from the desktop. 5.18 How to have installed and enabled BackupPlanner. Click Connect. 6 Once you establish the connection... only after you can survive even if the original RAID or NSA fails. 5.18.1 Creating an Archive Backup To backup the NSA every week to a remote NSA: 138 Media Server User's Guide Schedule backups for the NSA.
User Guide
Page 180
... the NSA's management screens. If you use programs like Windows Explorer to access the NSA's shares to copy files from the NSA, delete files on ...remote users to use FTP from the Internet to access the NSA's shares. See Section 10.4 on page 188 for FTP allows remote users to use the custom port number when using FTP to access... the NSA. Figure 97 UPnP Using the Wrong IP Address 192.168.1.34 a.b.c.d 192.168.1.33 9.5.2 UPnP and Security UPnP's automated nature makes it easier to use UPnP port mapping to allow access...
... the NSA's management screens. If you use programs like Windows Explorer to access the NSA's shares to copy files from the NSA, delete files on ...remote users to use FTP from the Internet to access the NSA's shares. See Section 10.4 on page 188 for FTP allows remote users to use the custom port number when using FTP to access... the NSA. Figure 97 UPnP Using the Wrong IP Address 192.168.1.34 a.b.c.d 192.168.1.33 9.5.2 UPnP and Security UPnP's automated nature makes it easier to use UPnP port mapping to allow access...
User Guide
Page 259
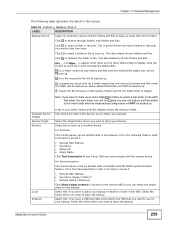
...and appear when there are many folders/files to hide from view. Fill in the following fields in order to be able to access it . • Remote NSA Address • Username • Password • Share Name Click Test Connection to place your backup in another device. Select ... back up to scroll up . Chapter 11 Package Management The following fields in order to be able to access it . • Remote NSA Address • Username (always "admin") • Remote Admin's Password Click Show target content to connect to browse through the folders/files. Click to select a ...
...and appear when there are many folders/files to hide from view. Fill in the following fields in order to be able to access it . • Remote NSA Address • Username • Password • Share Name Click Test Connection to place your backup in another device. Select ... back up to scroll up . Chapter 11 Package Management The following fields in order to be able to access it . • Remote NSA Address • Username (always "admin") • Remote Admin's Password Click Show target content to connect to browse through the folders/files. Click to select a ...
User Guide
Page 268
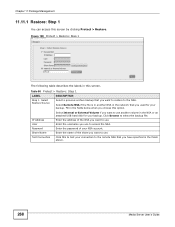
...Source Select a previous archive backup that you want to use another volume in the fields above. 268 Media Server User's Guide Click Browse to access the NSA. Enter the name of the NSA you have specified in the NSA or an attached USB hard disk for your backup. Enter ...clicking Protect > Restore. Fill in this to the NSA. Chapter 11 Package Management 11.11.1 Restore: Step 1 You can access this option. Enter the password of your connection to the remote NSA that you want to restore to test your NSA account. Figure 168 Protect > Restore: Step 1 The following table ...
...Source Select a previous archive backup that you want to use another volume in the fields above. 268 Media Server User's Guide Click Browse to access the NSA. Enter the name of the NSA you have specified in the NSA or an attached USB hard disk for your backup. Enter ...clicking Protect > Restore. Fill in this to the NSA. Chapter 11 Package Management 11.11.1 Restore: Step 1 You can access this option. Enter the password of your connection to the remote NSA that you want to restore to test your NSA account. Figure 168 Protect > Restore: Step 1 The following table ...
User Guide
Page 290
... account name. Port Number Enter the port number for the FTP Uploadr. 290 Media Server User's Guide Description Enter additional information about this screen to access the FTP server. Apply Click this to save your settings and check whether you can use the settings to connect to the FTP server.... Remote Path Enter the path of the FTP server. Chapter 12 Auto Upload In the FTP Uploadr screen, click the Add Server or Edit Server button ...
... account name. Port Number Enter the port number for the FTP Uploadr. 290 Media Server User's Guide Description Enter additional information about this screen to access the FTP server. Apply Click this to save your settings and check whether you can use the settings to connect to the FTP server.... Remote Path Enter the path of the FTP server. Chapter 12 Auto Upload In the FTP Uploadr screen, click the Add Server or Edit Server button ...
User Guide
Page 338
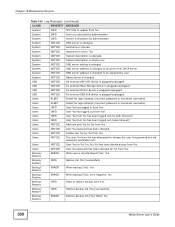
...NOTICE User %s password has been changed . Users NOTICE Delete user %s by administrator! Users NOTICE User %s on %u.%u.%u.%u has been denied access from %s Users NOTICE User %s password has been changed to be assigned by %s from %s has been logged out (lease timeout)! ...System NOTICE Name server is set to restore backup job [%s]. Users NOTICE Add new user %s by administrator! Backup/ Restore ERROR When query remote target [%s]: %s Backup/ Restore INFO Backup job [%s] successfully Backup/ Restore ERROR When backup [%s]: %s Backup/ Restore ERROR When backup [%s], ...
...NOTICE User %s password has been changed . Users NOTICE Delete user %s by administrator! Users NOTICE User %s on %u.%u.%u.%u has been denied access from %s Users NOTICE User %s password has been changed to be assigned by %s from %s has been logged out (lease timeout)! ...System NOTICE Name server is set to restore backup job [%s]. Users NOTICE Add new user %s by administrator! Backup/ Restore ERROR When query remote target [%s]: %s Backup/ Restore INFO Backup job [%s] successfully Backup/ Restore ERROR When backup [%s]: %s Backup/ Restore ERROR When backup [%s], ...
User Guide
Page 404
...of data over public networks. The Real Time Streaming (media control) Protocol (RTSP) is another . Simple Network Management Protocol. This is a remote control for multimedia on many different types of data over public networks. PPTP (Point-to another popular Internet chat program. A streaming audio service...that enables real time sound over the web. An Internet chat program. NFS is a protocol that sends out ICMP echo requests to access data on the Internet. Post Office Protocol version 3 lets a client computer get e-mail from one e-mail server to -Point Tunneling...
...of data over public networks. The Real Time Streaming (media control) Protocol (RTSP) is another . Simple Network Management Protocol. This is a remote control for multimedia on many different types of data over public networks. PPTP (Point-to another popular Internet chat program. A streaming audio service...that enables real time sound over the web. An Internet chat program. NFS is a protocol that sends out ICMP echo requests to access data on the Internet. Post Office Protocol version 3 lets a client computer get e-mail from one e-mail server to -Point Tunneling...
User Guide
Page 405
Login Host Protocol used for (Terminal Access Controller Access Control System). It operates over TCP/IP networks. Media Server User's Guide 405 Telnet is an Internet file transfer protocol similar to a UNIX server. Syslog ... uses the UDP (User Datagram Protocol) rather than TCP (Transmission Control Protocol). Another videoconferencing solution. Its primary function is to allow users to log into remote host systems. Trivial File Transfer Protocol is the login and terminal emulation protocol common on the Internet and in UNIX environments. Appendix C Common Services Table...
Login Host Protocol used for (Terminal Access Controller Access Control System). It operates over TCP/IP networks. Media Server User's Guide 405 Telnet is an Internet file transfer protocol similar to a UNIX server. Syslog ... uses the UDP (User Datagram Protocol) rather than TCP (Transmission Control Protocol). Another videoconferencing solution. Its primary function is to allow users to log into remote host systems. Trivial File Transfer Protocol is the login and terminal emulation protocol common on the Internet and in UNIX environments. Appendix C Common Services Table...