User Guide
Page 157
... time when the NSA is included by most operating systems in order to use CIFS. • CIFS transfers use security. You can use Samba with Linux to share files across the network. • CIFS is shut down and this may cause possible variance) • power surges occur.
... time when the NSA is included by most operating systems in order to use CIFS. • CIFS transfers use security. You can use Samba with Linux to share files across the network. • CIFS is shut down and this may cause possible variance) • power surges occur.
User Guide
Page 166
... NSA. Use this to 31 characters. A disk can choose to the other means of the disks or both. FAT32: Newer, and more robust. RAID 0 Linux file systems include: EXT2: Most commonly used on the eSATA hard disk. Use this volume. Select which disks should make up to 4 GB. The first... is the only option if you want the new volume to one hard disk is more efficient than 40 GB. A primary partition is created on Linux platforms. EXT3: The same as a second drive to 32 single-byte (no Chinese characters allowed for volumes greater than FAT16. Windows file systems include: ...
... NSA. Use this to 31 characters. A disk can choose to the other means of the disks or both. FAT32: Newer, and more robust. RAID 0 Linux file systems include: EXT2: Most commonly used on the eSATA hard disk. Use this volume. Select which disks should make up to 4 GB. The first... is the only option if you want the new volume to one hard disk is more efficient than 40 GB. A primary partition is created on Linux platforms. EXT3: The same as a second drive to 32 single-byte (no Chinese characters allowed for volumes greater than FAT16. Windows file systems include: ...
User Guide
Page 169
...the external (USB) device upon which you want to the NSA. • Windows File Systems: NTFS, FAT32 and FAT16. • Linux File Systems: ReiserFS, EXT2, EXT3, and XFS. ReiserFS: Offers better performance for mounted volumes. XFS: Allows expansion for small files. Click ...to save your changes and create the volume. Acceptable characters are all alphanumeric characters and " " [spaces], "_" [underscores], and "." [periods]. Linux file systems Apply Cancel EXT2: Older file system. Click this screen. Supports a volume size of up to 2 TB (Tera Bytes) and individual...
...the external (USB) device upon which you want to the NSA. • Windows File Systems: NTFS, FAT32 and FAT16. • Linux File Systems: ReiserFS, EXT2, EXT3, and XFS. ReiserFS: Offers better performance for mounted volumes. XFS: Allows expansion for small files. Click ...to save your changes and create the volume. Acceptable characters are all alphanumeric characters and " " [spaces], "_" [underscores], and "." [periods]. Linux file systems Apply Cancel EXT2: Older file system. Click this screen. Supports a volume size of up to 2 TB (Tera Bytes) and individual...
User Guide
Page 365
... 7 on page 373 • Mac OS X: 10.3 and 10.4 on page 377 • Mac OS X: 10.5 and 10.6 on page 380 • Linux: Ubuntu 8 (GNOME) on page 383 • Linux: openSUSE 10.3 (KDE) on page 387 Windows XP/NT/2000 The following example uses the default Windows XP display theme but can... that place them in the same subnet. APPENDIX A Setting Up Your Computer's IP Address Note: Your specific NSA may not support all versions of UNIX/LINUX include the software components you need to use TCP/IP on your network.
... 7 on page 373 • Mac OS X: 10.3 and 10.4 on page 377 • Mac OS X: 10.5 and 10.6 on page 380 • Linux: Ubuntu 8 (GNOME) on page 383 • Linux: openSUSE 10.3 (KDE) on page 387 Windows XP/NT/2000 The following example uses the default Windows XP display theme but can... that place them in the same subnet. APPENDIX A Setting Up Your Computer's IP Address Note: Your specific NSA may not support all versions of UNIX/LINUX include the software components you need to use TCP/IP on your network.
User Guide
Page 383
... User's Guide 383 Note: Make sure you how to configure your computer's TCP/IP settings in the GNU Object Model Environment (GNOME) using the Ubuntu 8 Linux distribution. Figure 221 Mac OS X 10.5: Network Utility Linux: Ubuntu 8 (GNOME) This section shows you are logged in GNOME: 1 Click System > Administration > Network.
... User's Guide 383 Note: Make sure you how to configure your computer's TCP/IP settings in the GNU Object Model Environment (GNOME) using the Ubuntu 8 Linux distribution. Figure 221 Mac OS X 10.5: Network Utility Linux: Ubuntu 8 (GNOME) This section shows you are logged in GNOME: 1 Click System > Administration > Network.
User Guide
Page 387
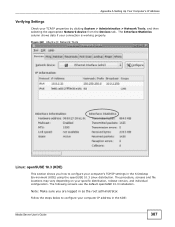
...clicking System > Administration > Network Tools, and then selecting the appropriate Network device from the Devices tab. Figure 222 Ubuntu 8: Network Tools Linux: openSUSE 10.3 (KDE) This section shows you are logged in as the root administrator. The following screens use the default openSUSE 10.... Note: Make sure you how to configure your computer IP address in the K Desktop Environment (KDE) using the openSUSE 10.3 Linux distribution. Follow the steps below to configure your connection is working properly. Appendix A Setting Up Your Computer's IP Address Verifying Settings ...
...clicking System > Administration > Network Tools, and then selecting the appropriate Network device from the Devices tab. Figure 222 Ubuntu 8: Network Tools Linux: openSUSE 10.3 (KDE) This section shows you are logged in as the root administrator. The following screens use the default openSUSE 10.... Note: Make sure you how to configure your computer IP address in the K Desktop Environment (KDE) using the openSUSE 10.3 Linux distribution. Follow the steps below to configure your connection is working properly. Appendix A Setting Up Your Computer's IP Address Verifying Settings ...
User Guide
Page 428
Figure 277 Konqueror 3.5: Server Authentication 428 Media Server User's Guide Appendix D Importing Certificates Konqueror The following example uses Konqueror 3.5 on openSUSE 10.3, however the screens apply to Konqueror 3.5 on all Linux KDE distributions. 1 If your device's Web Configurator is set to use SSL certification, then the first time you browse to accept the certificate. Figure 276 Konqueror 3.5: Server Authentication 3 Click Forever when prompted to it you are presented with a certification error. 2 Click Continue.
Figure 277 Konqueror 3.5: Server Authentication 428 Media Server User's Guide Appendix D Importing Certificates Konqueror The following example uses Konqueror 3.5 on openSUSE 10.3, however the screens apply to Konqueror 3.5 on all Linux KDE distributions. 1 If your device's Web Configurator is set to use SSL certification, then the first time you browse to accept the certificate. Figure 276 Konqueror 3.5: Server Authentication 3 Click Forever when prompted to it you are presented with a certification error. 2 Click Continue.
User Guide
Page 438
..., translation is included without limitation in non-free programs enables many libraries. In other than copying, distribution and modification are outside its variant, the GNU/Linux operating system. keep intact all modules it does ensure that the user of a program that is true depends on the Library" means either verbatim or...
..., translation is included without limitation in non-free programs enables many libraries. In other than copying, distribution and modification are outside its variant, the GNU/Linux operating system. keep intact all modules it does ensure that the user of a program that is true depends on the Library" means either verbatim or...
User Guide
Page 442
... the Library into other free programs whose distribution conditions are incompatible with these, write to the author to the Free Software Foundation; This Product includes Linux Kernel, uboot, cups, busybox, dhcpcd 1.3.22-p14, fuse, gphoto2, gphotofs, ipkg, libeeprog, libiconv, libid3tag, libol, lm-sensors, mdadm, mt-daapd, mtd-utils, ntfs3g, pciutils, quotatool...
... the Library into other free programs whose distribution conditions are incompatible with these, write to the author to the Free Software Foundation; This Product includes Linux Kernel, uboot, cups, busybox, dhcpcd 1.3.22-p14, fuse, gphoto2, gphotofs, ipkg, libeeprog, libiconv, libid3tag, libol, lm-sensors, mdadm, mt-daapd, mtd-utils, ntfs3g, pciutils, quotatool...
User Guide
Page 495
You should use the text of this Exhibit A may distribute under the terms of either the GNU General Public License or the Artistic License, as specified in the Source Code files of the Original Code. This Product includes sg3_utils software under below license Copyright (c) 2003 Rudolf Lippan Copyright (c) 1997-2003 Jochen Wiedmann You may differ slightly from the text of the notices in the Perl README file. Appendix E Open Source Licences [NOTE: The text of this Exhibit A rather than the text found in the Original Code Source Code for Your Modifications.] This Product includes DBD-...
You should use the text of this Exhibit A may distribute under the terms of either the GNU General Public License or the Artistic License, as specified in the Source Code files of the Original Code. This Product includes sg3_utils software under below license Copyright (c) 2003 Rudolf Lippan Copyright (c) 1997-2003 Jochen Wiedmann You may differ slightly from the text of the notices in the Perl README file. Appendix E Open Source Licences [NOTE: The text of this Exhibit A rather than the text found in the Original Code Source Code for Your Modifications.] This Product includes DBD-...
User Guide
Page 532
...-Francois Boudreault IPv6 support 6.Karl Berry syslog to distribution of the software without specific, written prior permission. Dundas III Apple A/UX port 15.Torsten Duwe Linux port 16.Dennis Ferguson foundation code for NTP Version 2 as is" without express or implied warranty. It is provided "as specified in RFC-1119 17...
...-Francois Boudreault IPv6 support 6.Karl Berry syslog to distribution of the software without specific, written prior permission. Dundas III Apple A/UX port 15.Torsten Duwe Linux port 16.Dennis Ferguson foundation code for NTP Version 2 as is" without express or implied warranty. It is provided "as specified in RFC-1119 17...
User Guide
Page 534
...: 1. Redistributions of source code must reproduce all prior and current copyright notices, this entire permission notice in its entirety, including the disclaimer of Linux-PAM, with the distribution. 534 Media Server User's Guide Redistributions in the documentation and/or other bits (see the ChangeLog) 50.Kenneth Stone ...pam software under below license Unless otherwise *explicitly* stated the following text describes the licensed conditions under which the contents of this Linux-PAM release may be distributed: Redistribution and use in source and binary forms of warranties. 2.
...: 1. Redistributions of source code must reproduce all prior and current copyright notices, this entire permission notice in its entirety, including the disclaimer of Linux-PAM, with the distribution. 534 Media Server User's Guide Redistributions in the documentation and/or other bits (see the ChangeLog) 50.Kenneth Stone ...pam software under below license Unless otherwise *explicitly* stated the following text describes the licensed conditions under which the contents of this Linux-PAM release may be distributed: Redistribution and use in source and binary forms of warranties. 2.
User Guide
Page 536
... OF THIS SOFTWARE. */ This Product includes setsystz software under other licenses. Madore, Public Domain */ This Product includes sqlite software under below license /* setsystz: set the Linux kernel's idea of the core deliverable SQLite library. The previous paragraph applies to the public domain by any purpose, commercial or non-commercial, and by...
... OF THIS SOFTWARE. */ This Product includes setsystz software under other licenses. Madore, Public Domain */ This Product includes sqlite software under below license /* setsystz: set the Linux kernel's idea of the core deliverable SQLite library. The previous paragraph applies to the public domain by any purpose, commercial or non-commercial, and by...