User Guide
Page 91
... vulnerable to infection. In this chapter About computer connections 90 Banning computer connections 94 You can ban computers that an Internet connection is a threat. Also, McAfee recommends that you are sure that are associated with trusted IP addresses can be banned from trusted IP addresses in the Networks list. Make sure.... 89 CHAPTER 18 Managing computer connections You can configure Firewall to manage specific remote connections to your computer by a firewall and an up-to-date antivirus program.
... vulnerable to infection. In this chapter About computer connections 90 Banning computer connections 94 You can ban computers that an Internet connection is a threat. Also, McAfee recommends that you are sure that are associated with trusted IP addresses can be banned from trusted IP addresses in the Networks list. Make sure.... 89 CHAPTER 18 Managing computer connections You can configure Firewall to manage specific remote connections to your computer by a firewall and an up-to-date antivirus program.
User Guide
Page 92
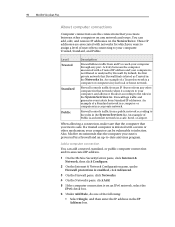
...other mechanism, your computer can be vulnerable to assign a level of Public is an Internet network in the IP Address box. 90 McAfee VirusScan Plus About computer connections Computer connections are associated with a Trusted IP address and your computer is safe. These IP addresses are the connections ... between the computer associated with networks for which you trust is not filtered or analyzed by a firewall and an up-to-date antivirus program. Firewall logs traffic and generates event alerts from a public network according to the rules in the System Services list. An ...
...other mechanism, your computer can be vulnerable to assign a level of Public is an Internet network in the IP Address box. 90 McAfee VirusScan Plus About computer connections Computer connections are associated with a Trusted IP address and your computer is safe. These IP addresses are the connections ... between the computer associated with networks for which you trust is not filtered or analyzed by a firewall and an up-to-date antivirus program. Firewall logs traffic and generates event alerts from a public network according to the rules in the System Services list. An ...