HP iPAQ Security Solutions
Page 3
...encryption, which helps ensure that reduce specific security risks to keep your credentials secure 3 A second layer of access attempts. You can encrypt e-mail messages, attachments, My Documents, and other files that allow you can do the following: • Connect your HP iPAQ to a wireless network •...an external storage card. (By default, all data in the My Documents folder is provided by HP ProtectTools, a suite of security involves PIN or password access for HP iPAQ devices. These security solutions provide certain advantages that are based on the same technologies used by ...
...encryption, which helps ensure that reduce specific security risks to keep your credentials secure 3 A second layer of access attempts. You can encrypt e-mail messages, attachments, My Documents, and other files that allow you can do the following: • Connect your HP iPAQ to a wireless network •...an external storage card. (By default, all data in the My Documents folder is provided by HP ProtectTools, a suite of security involves PIN or password access for HP iPAQ devices. These security solutions provide certain advantages that are based on the same technologies used by ...
HP iPAQ Security Solutions
Page 4
... security that helps prevent data theft by the specific user. You will need to install the Odyssey Client software onto your licensed copy of Odyssey Client. A license key is a text sequence that corresponds to your HP iPAQ. This type of identification is virtually foolproof, ...for network authentication. You can set of protection, you are licensed separately. For instructions on Odyssey Client, you purchased an HP iPAQ hx2700 Pocket PC, the Companion CD is needed to the information that came with the Odyssey Client software that blocks any required access passwords ...
... security that helps prevent data theft by the specific user. You will need to install the Odyssey Client software onto your licensed copy of Odyssey Client. A license key is a text sequence that corresponds to your HP iPAQ. This type of identification is virtually foolproof, ...for network authentication. You can set of protection, you are licensed separately. For instructions on Odyssey Client, you purchased an HP iPAQ hx2700 Pocket PC, the Companion CD is needed to the information that came with the Odyssey Client software that blocks any required access passwords ...
HP iPAQ Security Solutions
Page 6
...Integrity Protocol (TKIP) technology improves WEP by using your HP iPAQ, refer to the documentation that came with your device. For example, this wireless connection can connect to a local area network through a wireless connection. To get specific information about turning on or off WLAN and Wi-Fi... to wireless LAN security. Primarily, a VPN connection helps you to securely connect to access point. 6 To get specific information about setting up and connecting to a VPN, refer to the documentation on the Companion CD or Getting Started CD that came with your HP iPAQ.
...Integrity Protocol (TKIP) technology improves WEP by using your HP iPAQ, refer to the documentation that came with your device. For example, this wireless connection can connect to a local area network through a wireless connection. To get specific information about turning on or off WLAN and Wi-Fi... to wireless LAN security. Primarily, a VPN connection helps you to securely connect to access point. 6 To get specific information about setting up and connecting to a VPN, refer to the documentation on the Companion CD or Getting Started CD that came with your HP iPAQ.
HP iPAQ Security Solutions
Page 8
... passes between the computer and the network. A firewall can provide you with various helpful security needs for Pocket PC is an integrated mobile security solution that protect lost and stolen devices; Bluefire Security TechnologiesTM develops software that ...Pocket PC provides convenient, real-time encryption of information on devices. 8 Note: The 54-Mbit/s maximum speed of 802.11g is combined with PicturePIN® (access control) and QuickPIN® to provide fast re-entry to the device and its content. A firewall keeps computer hackers out and your sensitive data in any specific...
... passes between the computer and the network. A firewall can provide you with various helpful security needs for Pocket PC is an integrated mobile security solution that protect lost and stolen devices; Bluefire Security TechnologiesTM develops software that ...Pocket PC provides convenient, real-time encryption of information on devices. 8 Note: The 54-Mbit/s maximum speed of 802.11g is combined with PicturePIN® (access control) and QuickPIN® to provide fast re-entry to the device and its content. A firewall keeps computer hackers out and your sensitive data in any specific...
HP iPAQ Security Solutions
Page 9
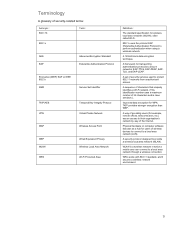
... WPA Temporal Key Integrity Protocol Virtual Private Network Wireless Access Point Wired Equivalent Privacy Wireless Local Area Network Wi-Fi Protected Area Definition The standard specification for WPA. Physical hardware or computer software that uniquely identifies a Wi-Fi network. (This identification number uses a maximum number of the Internet. A security protocol designed...
... WPA Temporal Key Integrity Protocol Virtual Private Network Wireless Access Point Wired Equivalent Privacy Wireless Local Area Network Wi-Fi Protected Area Definition The standard specification for WPA. Physical hardware or computer software that uniquely identifies a Wi-Fi network. (This identification number uses a maximum number of the Internet. A security protocol designed...