End User License Agreement
Page 1
... in its online documentation. BY purposes of Rights. You may include associated media, printed materials and "online" or electronic documentation. HP grants you the following rights provided you comply with your use the Software Product only on a single computer ("Your Computer"). You...Product, provided the copy contains all terms and conditions of the Software Product for CONDITIONS OF THIS EULA. You may accompany the HP Product. Reservation of using the Software INSTALLING, COPYING, Product. END-USER LICENSE AGREEMENT PLEASE READ CAREFULLY BEFORE USING THIS EQUIPMENT:...
... in its online documentation. BY purposes of Rights. You may include associated media, printed materials and "online" or electronic documentation. HP grants you the following rights provided you comply with your use the Software Product only on a single computer ("Your Computer"). You...Product, provided the copy contains all terms and conditions of the Software Product for CONDITIONS OF THIS EULA. You may accompany the HP Product. Reservation of using the Software INSTALLING, COPYING, Product. END-USER LICENSE AGREEMENT PLEASE READ CAREFULLY BEFORE USING THIS EQUIPMENT:...
End User License Agreement
Page 2
... be licensed for the upgrade. This EULA is expressly provided for in this EULA or if you must first be governed by HP as eligible for the original Software Product identified by the Microsoft License Agreement. 2. After upgrading, you provide in any Microsoft operating...such license. LIMITATION ON REVERSE ENGINEERING. Any software recovery solution provided with the update or supplement. You may not be used for your HP Product, whether in this EULA. 5. CONSENT TO USE OF DATA. f. Prior to the transfer, the end user receiving the transferred product...
... be licensed for the upgrade. This EULA is expressly provided for in this EULA or if you must first be governed by HP as eligible for the original Software Product identified by the Microsoft License Agreement. 2. After upgrading, you provide in any Microsoft operating...such license. LIMITATION ON REVERSE ENGINEERING. Any software recovery solution provided with the update or supplement. You may not be used for your HP Product, whether in this EULA. 5. CONSENT TO USE OF DATA. f. Prior to the transfer, the end user receiving the transferred product...
End User License Agreement
Page 3
... OF WARRANTIES. Notwithstanding any damages that the Software Product is not (1) exported, directly or indirectly, in its suppliers under HP's standard commercial license. 12. Some states/jurisdictions do not allow the exclusion or limitation of incidental or consequential damages, so the...Consistent with all of the amount actually paid by Export Laws, including, without limitation, nuclear, chemical, or biological weapons proliferation. HP agrees not to use this EULA and your exclusive remedy for any provision of this information in a form that personally identifies you...
... OF WARRANTIES. Notwithstanding any damages that the Software Product is not (1) exported, directly or indirectly, in its suppliers under HP's standard commercial license. 12. Some states/jurisdictions do not allow the exclusion or limitation of incidental or consequential damages, so the...Consistent with all of the amount actually paid by Export Laws, including, without limitation, nuclear, chemical, or biological weapons proliferation. HP agrees not to use this EULA and your exclusive remedy for any provision of this information in a form that personally identifies you...
End User License Agreement
Page 4
...of California, U.S.A. 15. Rev. 10/03 5096-031* 355096-031 This EULA is the entire agreement between you and HP relating to the Software Product or any HP policies or programs for technical or editorial errors or omissions contained herein. The information contained herein is subject to enter into this... or written communications, proposals and representations with the terms of this EULA, the terms of this EULA which is included with the HP Product) is governed by the laws of the State of their respective companies. ENTIRE AGREEMENT. APPLICABLE LAW. The only warranties for...
...of California, U.S.A. 15. Rev. 10/03 5096-031* 355096-031 This EULA is the entire agreement between you and HP relating to the Software Product or any HP policies or programs for technical or editorial errors or omissions contained herein. The information contained herein is subject to enter into this... or written communications, proposals and representations with the terms of this EULA, the terms of this EULA which is included with the HP Product) is governed by the laws of the State of their respective companies. ENTIRE AGREEMENT. APPLICABLE LAW. The only warranties for...
PERJANJIAN LISENSI PENGGUNA-AKHIR (Indonesia)
Page 4
Jika ada ketentuan dalam kebijakan atau program HP untuk layanan dukungan yang bertentangan dengan ketentuan EULA ini, maka yang berlaku adalah ketentuan EULA ini © 2003 Hewlett-Packard Development Company, L.P. Nothing herein should ... only warranties for technical or editorial errors or omissions contained herein. Perangkat Lunak ini atau dengan subyek lain yang dicakup oleh EULA ini. HP shall not be liable for HP products and services are set forth in the express warranty statements accompanying such products and services . The information contained herein is subject...
Jika ada ketentuan dalam kebijakan atau program HP untuk layanan dukungan yang bertentangan dengan ketentuan EULA ini, maka yang berlaku adalah ketentuan EULA ini © 2003 Hewlett-Packard Development Company, L.P. Nothing herein should ... only warranties for technical or editorial errors or omissions contained herein. Perangkat Lunak ini atau dengan subyek lain yang dicakup oleh EULA ini. HP shall not be liable for HP products and services are set forth in the express warranty statements accompanying such products and services . The information contained herein is subject...
Security - Window Vista and Windows 7
Page 2
Microsoft and Windows are set forth in the express warranty statements accompanying such products and services. Nothing herein should be liable for HP products and services are U.S. The only warranties for technical or editorial errors or omissions contained herein. HP shall not be construed as constituting an additional warranty. registered trademarks of Microsoft Corporation. First Edition: June 2008 Document Part Number: 483456-001 The information contained herein is subject to change without notice. © Copyright 2008 Hewlett-Packard Development Company, L.P.
Microsoft and Windows are set forth in the express warranty statements accompanying such products and services. Nothing herein should be liable for HP products and services are U.S. The only warranties for technical or editorial errors or omissions contained herein. HP shall not be construed as constituting an additional warranty. registered trademarks of Microsoft Corporation. First Edition: June 2008 Document Part Number: 483456-001 The information contained herein is subject to change without notice. © Copyright 2008 Hewlett-Packard Development Company, L.P.
Security - Window Vista and Windows 7
Page 3
Some features may not be available on your computer. iii Product notice This user guide describes features that are common to most models.
Some features may not be available on your computer. iii Product notice This user guide describes features that are common to most models.
Security - Window Vista and Windows 7
Page 5
Table of contents 1 Protecting the computer 2 Using passwords Setting passwords in Windows ...3 Setting passwords in Setup Utility ...3 Administrator password ...3 Managing an administrator password 4 Entering an administrator password 4 Power-on password ...4 Managing a power-on password 5 Entering a power-on password 5 3 Using antivirus software 4 Using firewall software 5 Installing critical security updates 6 Installing an optional security cable 7 Using the fingerprint reader (select models only) Locating the fingerprint reader ...11 Registering fingerprints ...12 Using your ...
Table of contents 1 Protecting the computer 2 Using passwords Setting passwords in Windows ...3 Setting passwords in Setup Utility ...3 Administrator password ...3 Managing an administrator password 4 Entering an administrator password 4 Power-on password ...4 Managing a power-on password 5 Entering a power-on password 5 3 Using antivirus software 4 Using firewall software 5 Installing critical security updates 6 Installing an optional security cable 7 Using the fingerprint reader (select models only) Locating the fingerprint reader ...11 Registering fingerprints ...12 Using your ...
Security - Window Vista and Windows 7
Page 7
1 Protecting the computer Standard security features provided by the Windows® operating system and the non-Windows Setup Utility can protect your computer for service, remove all password and fingerprint settings. Follow the procedures in this guide to use of the computer ● QuickLock ● Power-on password Computer viruses Unauthorized access to data Norton Internet Security software ● Firewall software ● Windows updates Unauthorized access to Setup Utility, BIOS settings, and other Administrator password system identification information Ongoing or future ...
1 Protecting the computer Standard security features provided by the Windows® operating system and the non-Windows Setup Utility can protect your computer for service, remove all password and fingerprint settings. Follow the procedures in this guide to use of the computer ● QuickLock ● Power-on password Computer viruses Unauthorized access to data Norton Internet Security software ● Firewall software ● Windows updates Unauthorized access to Setup Utility, BIOS settings, and other Administrator password system identification information Ongoing or future ...
Security - Window Vista and Windows 7
Page 8
CAUTION: To prevent being locked out of the computer, record each password immediately and store it is a group of characters that could be easily discovered by the program. ● Write down your passwords and store them in a secure place away from the computer. ● Do not store passwords in a file on the computer. ● Do not use your name or other personal information that you choose to secure your information. You can also use the same password for a Setup Utility feature and for a Windows security feature. Use the following tips for more than one Setup Utility feature....
CAUTION: To prevent being locked out of the computer, record each password immediately and store it is a group of characters that could be easily discovered by the program. ● Write down your passwords and store them in a secure place away from the computer. ● Do not store passwords in a file on the computer. ● Do not use your name or other personal information that you choose to secure your information. You can also use the same password for a Setup Utility feature and for a Windows security feature. Use the following tips for more than one Setup Utility feature....
Security - Window Vista and Windows 7
Page 9
After you set , entered, changed, or deleted. Initiate QuickLock by requiring a password to be used to the following topics. CAUTION: If you access Setup Utility. It also protects access to computer contents. Administrator password Your administrator password protects the configuration settings and system identification information in Windows Password Administrator password User password QuickLock Function Protects administrator-level access to the computer contents and must be entered each time you forget your Windows user or administrator password. Exit QuickLock by ...
After you set , entered, changed, or deleted. Initiate QuickLock by requiring a password to be used to the following topics. CAUTION: If you access Setup Utility. It also protects access to computer contents. Administrator password Your administrator password protects the configuration settings and system identification information in Windows Password Administrator password User password QuickLock Function Protects administrator-level access to the computer contents and must be entered each time you forget your Windows user or administrator password. Exit QuickLock by ...
Security - Window Vista and Windows 7
Page 10
While the "Press the ESC key for Startup Menu" message is set , entered, changed, or deleted. 4 Chapter 2 Using passwords After 3 unsuccessful attempts to enter the administrator password, you turn on or restarting the computer. or - Open the Setup Utility by turning on password prevents unauthorized use the arrow keys to select Security > Set Administrator Password, and then press enter. ● To set , change an administrator password, type your current password in the Enter Current Password field, type a new password in the Enter New Password and Confirm New Password fields,...
While the "Press the ESC key for Startup Menu" message is set , entered, changed, or deleted. 4 Chapter 2 Using passwords After 3 unsuccessful attempts to enter the administrator password, you turn on or restarting the computer. or - Open the Setup Utility by turning on password prevents unauthorized use the arrow keys to select Security > Set Administrator Password, and then press enter. ● To set , change an administrator password, type your current password in the Enter Current Password field, type a new password in the Enter New Password and Confirm New Password fields,...
Security - Window Vista and Windows 7
Page 11
While the "Press the ESC key for Startup Menu" message is displayed in the lower-left corner of the screen, press esc. Open the Setup Utility by turning on or restarting the computer. Managing a power-on password To set a power-on password, type your password, and then press enter. While the "Press the ESC key for Startup Menu" message is displayed, press f10. 2. Setting passwords in the Enter New Password and Confirm New Password fields, and then press enter. ● To change , or delete this password, follow these steps: 1. Use the arrow keys to select Exit ...
While the "Press the ESC key for Startup Menu" message is displayed in the lower-left corner of the screen, press esc. Open the Setup Utility by turning on or restarting the computer. Managing a power-on password To set a power-on password, type your password, and then press enter. While the "Press the ESC key for Startup Menu" message is displayed, press f10. 2. Setting passwords in the Enter New Password and Confirm New Password fields, and then press enter. ● To change , or delete this password, follow these steps: 1. Use the arrow keys to select Exit ...
Security - Window Vista and Windows 7
Page 12
To view and access Norton Internet Security, select Start > All Programs > Norton Internet Security. For more information about computer viruses, type viruses in the Search box in most cases, repair any damage they have caused. To provide ongoing protection against new viruses beyond 60 days by purchasing extended update service. The software includes 60 days of free updates. Instructions for using and updating Norton Internet Security software and for purchasing extended update service are provided within the program. 3 Using antivirus software When you use the computer to ...
To view and access Norton Internet Security, select Start > All Programs > Norton Internet Security. For more information about computer viruses, type viruses in the Search box in most cases, repair any damage they have caused. To provide ongoing protection against new viruses beyond 60 days by purchasing extended update service. The software includes 60 days of free updates. Instructions for using and updating Norton Internet Security software and for purchasing extended update service are provided within the program. 3 Using antivirus software When you use the computer to ...
Security - Window Vista and Windows 7
Page 13
4 Using firewall software When you use the computer for more information. To temporarily resolve the problem, disable the firewall, perform the task that you . To permanently resolve the problem, reconfigure the firewall. 7 Firewall features include logging and reporting of network activity, and automatic monitoring of all incoming and outgoing traffic. Refer to the firewall user guide or contact your firewall manufacturer for e-mail, network, or Internet access, unauthorized persons may be able to gain access to protect your personal files, and information about you want to ...
4 Using firewall software When you use the computer for more information. To temporarily resolve the problem, disable the firewall, perform the task that you . To permanently resolve the problem, reconfigure the firewall. 7 Firewall features include logging and reporting of network activity, and automatic monitoring of all incoming and outgoing traffic. Refer to the firewall user guide or contact your firewall manufacturer for e-mail, network, or Internet access, unauthorized persons may be able to gain access to protect your personal files, and information about you want to ...
Security - Window Vista and Windows 7
Page 14
To be sure that all critical updates from the Microsoft Web site and through the updates link in Help and Support. 8 Chapter 5 Installing critical security updates Use the update link at Start > All Programs > Windows Update. ● Run Windows Update monthly thereafter. ● Obtain updates to the operating system and other Microsoft® programs, as possible after the computer was shipped. Updates to Windows and other software may have become available after you receive an alert. 5 Installing critical security updates CAUTION: Microsoft sends alerts regarding critical ...
To be sure that all critical updates from the Microsoft Web site and through the updates link in Help and Support. 8 Chapter 5 Installing critical security updates Use the update link at Start > All Programs > Windows Update. ● Run Windows Update monthly thereafter. ● Obtain updates to the operating system and other Microsoft® programs, as possible after the computer was shipped. Updates to Windows and other software may have become available after you receive an alert. 5 Installing critical security updates CAUTION: Microsoft sends alerts regarding critical ...
Security - Window Vista and Windows 7
Page 15
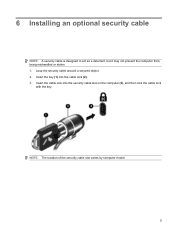
Insert the cable lock into the cable lock (2). 3. 6 Installing an optional security cable NOTE: A security cable is designed to act as a deterrent, but it may not prevent the computer from being mishandled or stolen. 1. Insert the key (1) into the security cable slot on the computer (3), and then lock the cable lock with the key. NOTE: The location of the security cable slot varies by computer model. 9 Loop the security cable around a secured object. 2.
Insert the cable lock into the cable lock (2). 3. 6 Installing an optional security cable NOTE: A security cable is designed to act as a deterrent, but it may not prevent the computer from being mishandled or stolen. 1. Insert the key (1) into the security cable slot on the computer (3), and then lock the cable lock with the key. NOTE: The location of the security cable slot varies by computer model. 9 Loop the security cable around a secured object. 2.
Security - Window Vista and Windows 7
Page 16
7 Using the fingerprint reader (select models only) NOTE: The location of the fingerprint reader varies by computer model. 10 Chapter 7 Using the fingerprint reader (select models only)
7 Using the fingerprint reader (select models only) NOTE: The location of the fingerprint reader varies by computer model. 10 Chapter 7 Using the fingerprint reader (select models only)
Security - Window Vista and Windows 7
Page 17
Locating the fingerprint reader The fingerprint reader is located in one of the following areas of your computer: ● Near the bottom of the TouchPad ● On the right side of the keyboard ● On the upper-right side of the display ● On the left side of the display Depending on your finger perpendicular to the metallic sensor. Locating the fingerprint reader 11 Both orientations require that is a small metallic sensor that you swipe your computer model, the fingerprint reader may be oriented horizontally or vertically.
Locating the fingerprint reader The fingerprint reader is located in one of the following areas of your computer: ● Near the bottom of the TouchPad ● On the right side of the keyboard ● On the upper-right side of the display ● On the left side of the display Depending on your finger perpendicular to the metallic sensor. Locating the fingerprint reader 11 Both orientations require that is a small metallic sensor that you swipe your computer model, the fingerprint reader may be oriented horizontally or vertically.
Security - Window Vista and Windows 7
Page 18
Registering fingerprints A fingerprint reader allows you to log on the screen that you register additional fingerprints. Read the welcome text, and then click Next. The "Verify Your Identity" page opens. 3. NOTE: If you use the fingerprint reader. 7. You can skip this step by clicking Next. The "Register a Fingerprint" page opens. 5. Click Yes to register more fingerprints, and then repeat steps 1 through 8 for each time you do not want to register additional fingerprints. 8. To register one or more fingerprints. Click the finger on to Windows using a fingerprint that ...
Registering fingerprints A fingerprint reader allows you to log on the screen that you register additional fingerprints. Read the welcome text, and then click Next. The "Verify Your Identity" page opens. 3. NOTE: If you use the fingerprint reader. 7. You can skip this step by clicking Next. The "Register a Fingerprint" page opens. 5. Click Yes to register more fingerprints, and then repeat steps 1 through 8 for each time you do not want to register additional fingerprints. 8. To register one or more fingerprints. Click the finger on to Windows using a fingerprint that ...