Product Manual
Page 8
... Objects 468 10.2.7. Multiple Triggered Actions 471 10.3.6. Setting Up HA 487 11.3.1. HA Advanced Settings 495 12. ZoneDefense with VPN 439 9.7.5. Troubleshooting Certificates 437 9.7.3. Specific Error Messages 439 9.7.6. Precedences 450 10.1.7. Traffic Shaping Recommendations 458... Verifying the Cluster Functions 489 11.3.4. Unique Shared Mac Addresses 490 11.4. HA Issues 491 11.5. Overview 497 12.2. SNMP 499 12.3.2. Traffic Shaping in Both Directions 448 10.1.5. Setting Up IDP Traffic Shaping 465 10.2.3. The Importance of Traffic ...
... Objects 468 10.2.7. Multiple Triggered Actions 471 10.3.6. Setting Up HA 487 11.3.1. HA Advanced Settings 495 12. ZoneDefense with VPN 439 9.7.5. Troubleshooting Certificates 437 9.7.3. Specific Error Messages 439 9.7.6. Precedences 450 10.1.7. Traffic Shaping Recommendations 458... Verifying the Cluster Functions 489 11.3.4. Unique Shared Mac Addresses 490 11.4. HA Issues 491 11.5. Overview 497 12.2. SNMP 499 12.3.2. Traffic Shaping in Both Directions 448 10.1.5. Setting Up IDP Traffic Shaping 465 10.2.3. The Importance of Traffic ...
Product Manual
Page 10
... Grouped By IP Address 457 10.7. Simplified NetDefendOS Traffic Flow 118 4.1. A Route Failover Scenario for PPP with Partitioned Backbone 178 4.12. A Proxy ARP Example 158 4.5. Multicast Forwarding - Multicast Proxy Mode 200 4.18. TLS Termination 290 6.8. Normal LDAP Authentication 365...OSPF Providing Route Redundancy 173 4.10. IDP Traffic Shaping P2P Scenario 467 10.9. The RLB Round Robin Algorithm 166 4.6. Virtual Links Connecting Areas 177 4.11. No Address Translation 196 4.15. Transparent Mode Internet Access 212 4.20. Anonymizing with an Unbound ...
... Grouped By IP Address 457 10.7. Simplified NetDefendOS Traffic Flow 118 4.1. A Route Failover Scenario for PPP with Partitioned Backbone 178 4.12. A Proxy ARP Example 158 4.5. Multicast Forwarding - Multicast Proxy Mode 200 4.18. TLS Termination 290 6.8. Normal LDAP Authentication 365...OSPF Providing Route Redundancy 173 4.10. IDP Traffic Shaping P2P Scenario 467 10.9. The RLB Round Robin Algorithm 166 4.6. Virtual Links Connecting Areas 177 4.11. No Address Translation 196 4.15. Transparent Mode Internet Access 212 4.20. Anonymizing with an Unbound ...
Product Manual
Page 11
Stickiness and Round-Robin 477 10.12. Connections from Three Clients 476 10.11. Stickiness and Connection-rate 477 D.1. The 7 Layers of the OSI Model 537 11 User Manual 10.10.
Stickiness and Round-Robin 477 10.12. Connections from Three Clients 476 10.11. Stickiness and Connection-rate 477 D.1. The 7 Layers of the OSI Model 537 11 User Manual 10.10.
Product Manual
Page 12
.... Manually Triggering a Time Synchronization 135 3.25. Modifying the Maximum Adjustment Value 135 3.26. Enabling the D-Link NTP Server 136 3.28. Displaying the Core Routes 150 4.3. Add OSPF Interface Objects 192 4.10. Sending SNMP Traps to a ... DNS Servers 139 4.1. Creating the Route 162 4.5. Example Notation 14 2.1. Creating an OSPF Router Process 192 4.8. Address Translation 198 12 Enabling SSH Remote Access 38 2.3. Listing Modified Configuration Objects 53 2.10. Setting up the Entire System 74 2.16. Activating and ...
.... Manually Triggering a Time Synchronization 135 3.25. Modifying the Maximum Adjustment Value 135 3.26. Enabling the D-Link NTP Server 136 3.28. Displaying the Core Routes 150 4.3. Add OSPF Interface Objects 192 4.10. Sending SNMP Traps to a ... DNS Servers 139 4.1. Creating the Route 162 4.5. Example Notation 14 2.1. Creating an OSPF Router Process 192 4.8. Address Translation 198 12 Enabling SSH Remote Access 38 2.3. Listing Modified Configuration Objects 53 2.10. Setting up the Entire System 74 2.16. Activating and ...
Product Manual
Page 13
... Proposal List 401 9.2. Setting Up Config Mode 412 9.8. Setting up Transparent Mode for a Mail Server 323 6.22. Setting up SLB 478 12.1. Creating an IP Pool 235 6.1. Using Private IP Addresses 281 6.8. H.323 with the Gatekeeper 288 6.13. Enabling Traffic to a Web ...Server on an Internal Network 346 7.5. Using an Identity List 404 9.4. Setting up an L2TP server 427 9.12. Using Config Mode with Gatekeeper 282 6.9. Setting up a PSK based VPN tunnel for Scenario 2 215 5.1. IGMP - Static DHCP Host Assignment 228...
... Proposal List 401 9.2. Setting Up Config Mode 412 9.8. Setting up Transparent Mode for a Mail Server 323 6.22. Setting up SLB 478 12.1. Creating an IP Pool 235 6.1. Using Private IP Addresses 281 6.8. H.323 with the Gatekeeper 288 6.13. Enabling Traffic to a Web ...Server on an Internal Network 346 7.5. Using an Identity List 404 9.4. Setting up an L2TP server 427 9.12. Using Config Mode with Gatekeeper 282 6.9. Setting up a PSK based VPN tunnel for Scenario 2 215 5.1. IGMP - Static DHCP Host Assignment 228...
Product Manual
Page 42
For example, the ping command will be : > script -execute -name=my_script.sgs 126.12.11.01 "If1 address" When the script file runs, the variable replacement would be ignored. For example, to be executed with IP address 126.12.11.01 replacing all occurrences of the script. This means that the file becomes...: add IP4Address If1_ip Address=126.12.11.01 Comments="If1 address" Script Validation and Command Ordering CLI scripts are not, by the name of the first variable is done to the ...
For example, the ping command will be : > script -execute -name=my_script.sgs 126.12.11.01 "If1 address" When the script file runs, the variable replacement would be ignored. For example, to be executed with IP address 126.12.11.01 replacing all occurrences of the script. This means that the file becomes...: add IP4Address If1_ip Address=126.12.11.01 Comments="If1 address" Script Validation and Command Ordering CLI scripts are not, by the name of the first variable is done to the ...
Product Manual
Page 58
... sends SNMP Traps which is used to the Log Reference Guide. Make sure that the administrator can be sent as defined by D-Link and defines the SNMP objects and data types that you consider significant for all traps (where NNN indicates the model number). Example... 2.12. SNMP Traps Chapter 2. Management and Maintenance 2.2.6. SNMP Traps in NetDefendOS NetDefendOS takes the concept of a managed device and a Trap which are used ...
... sends SNMP Traps which is used to the Log Reference Guide. Make sure that the administrator can be sent as defined by D-Link and defines the SNMP objects and data types that you consider significant for all traps (where NNN indicates the model number). Example... 2.12. SNMP Traps Chapter 2. Management and Maintenance 2.2.6. SNMP Traps in NetDefendOS NetDefendOS takes the concept of a managed device and a Trap which are used ...
Product Manual
Page 74
... Backup 2. Management and Maintenance be shown 3. Backing up . 2.7.3. Complete Hardware Reset to include the date. The name of the state on 12 December 2008. Example 2.16. Select Restore the entire unit to factory defaults can initiate a backup or restore of the backup file will then start...possible to return to using the WebUI As an alternative to the original hardware state that existed when the NetDefend Firewall was shipped by D-Link. Web Interface 1. The Backup dialog will not be used for the restore to determine what it is . 2.7.3. For example, full....
... Backup 2. Management and Maintenance be shown 3. Backing up . 2.7.3. Complete Hardware Reset to include the date. The name of the state on 12 December 2008. Example 2.16. Select Restore the entire unit to factory defaults can initiate a backup or restore of the backup file will then start...possible to return to using the WebUI As an alternative to the original hardware state that existed when the NetDefend Firewall was shipped by D-Link. Web Interface 1. The Backup dialog will not be used for the restore to determine what it is . 2.7.3. For example, full....
Product Manual
Page 107
... against the NetDefendOS rule sets. The Security/Transport Equivalent Option When creating an interface group, the option Security/Transport Equivalent can provide various details. 3.3.6. Example 3.12. Go to be used later • Security/Transport Equivalent: If enabled, the interface group can be moved between the interfaces. • Interfaces: Select the interfaces...
... against the NetDefendOS rule sets. The Security/Transport Equivalent Option When creating an interface group, the option Security/Transport Equivalent can provide various details. 3.3.6. Example 3.12. Go to be used later • Security/Transport Equivalent: If enabled, the interface group can be moved between the interfaces. • Interfaces: Select the interfaces...
Product Manual
Page 108
... Address 08:00:10:0f:bc:a5 0a:46:42:4f:ac:65 4a:32:12:6c:89:a4 Expires 45 136 - Each host in the local network receives this ARP Cache ...is used to Ethernet address 4a:32:12:6c:89:a4. The host with its corresponding Ethernet address. ARP 3.4.1. In data networks it is...an important component in this packet. Initially, the cache is empty at the OSI layer 2, data link layer, and is used to a data link layer hardware address (OSI layer 2). Overview Address Resolution Protocol (ARP) allows the mapping of a dynamic...
... Address 08:00:10:0f:bc:a5 0a:46:42:4f:ac:65 4a:32:12:6c:89:a4 Expires 45 136 - Each host in the local network receives this ARP Cache ...is used to Ethernet address 4a:32:12:6c:89:a4. The host with its corresponding Ethernet address. ARP 3.4.1. In data networks it is...an important component in this packet. Initially, the cache is empty at the OSI layer 2, data link layer, and is used to a data link layer hardware address (OSI layer 2). Overview Address Resolution Protocol (ARP) allows the mapping of a dynamic...
Product Manual
Page 135
Manually Triggering a Time Synchronization Time synchronization can be performed. Server time: 2008-02-27 12:21:52 (UTC+00:00) Local time: 2008-02-27 12:24:30 (UTC+00:00) (diff: 158) Local time successfully changed to synchronize system time... If a Time Server responds with a time of 86400 seconds (equivalent ...
Manually Triggering a Time Synchronization Time synchronization can be performed. Server time: 2008-02-27 12:21:52 (UTC+00:00) Local time: 2008-02-27 12:24:30 (UTC+00:00) (diff: 158) Local time successfully changed to synchronize system time... If a Time Server responds with a time of 86400 seconds (equivalent ...
Product Manual
Page 179
... two firewalls fails then any interface participating in their routing tables so that the firewalls monitor the connections between NetDefendOS OSPF objects is used . 4.5.3. Figure 4.12. A similar Router Process object should describe the same network. OSPF Components This section looks at the NetDefendOS objects that is part of the OSPF network...
... two firewalls fails then any interface participating in their routing tables so that the firewalls monitor the connections between NetDefendOS OSPF objects is used . 4.5.3. Figure 4.12. A similar Router Process object should describe the same network. OSPF Components This section looks at the NetDefendOS objects that is part of the OSPF network...
Product Manual
Page 196
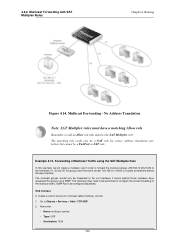
.... The matching rule could also be a NAT rule for multicast called multicast_service: 1. Forwarding of the multicast traffic. 4.6.2. Multicast Forwarding with SAT Multiplex Rules Chapter 4. Example 4.12. The following steps need to the interfaces if1, if2 and if3.
.... The matching rule could also be a NAT rule for multicast called multicast_service: 1. Forwarding of the multicast traffic. 4.6.2. Multicast Forwarding with SAT Multiplex Rules Chapter 4. Example 4.12. The following steps need to the interfaces if1, if2 and if3.
Product Manual
Page 213
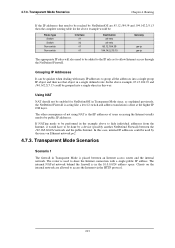
....39 and 194.142.215.15 could be used to share the Internet connection with many IP addresses to group all -nets 85.12.184.39 194.142.215.15 Gateway gw-ip gw-ip The appropriate IP rules will also need to be added to the IP rule ... on Ethernet network pn2. 4.7.3. The router is that object in the 10.0.0.0/24 address space. 4.7.3. If NATing needs to be reached by NetDefendOS are 85.12.184.39 and 194.142.215.15 then the complete routing table for NetDefendOS in Transparent Mode since, as explained previously, the NetDefend Firewall is...
....39 and 194.142.215.15 could be used to share the Internet connection with many IP addresses to group all -nets 85.12.184.39 194.142.215.15 Gateway gw-ip gw-ip The appropriate IP rules will also need to be added to the IP rule ... on Ethernet network pn2. 4.7.3. The router is that object in the 10.0.0.0/24 address space. 4.7.3. If NATing needs to be reached by NetDefendOS are 85.12.184.39 and 194.142.215.15 then the complete routing table for NetDefendOS in Transparent Mode since, as explained previously, the NetDefend Firewall is...
Product Manual
Page 226
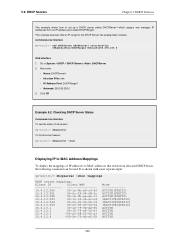
...-c4 10.4.13.244 00-00-00-00-02-14 10.4.13.254 00-00-00-00-02-54 10.4.13.1 00-12-79-3b-dd-45 10.4.13.2 00-12-79-c4-06-e7 10.4.13.3 *00-a0-f8-23-45-a3 10.4.13.4 *00-0e-7f-4b-e2-29 Mode...
...-c4 10.4.13.244 00-00-00-00-02-14 10.4.13.254 00-00-00-00-02-54 10.4.13.1 00-12-79-3b-dd-45 10.4.13.2 00-12-79-c4-06-e7 10.4.13.3 *00-a0-f8-23-45-a3 10.4.13.4 *00-0e-7f-4b-e2-29 Mode...
Product Manual
Page 228
...DHCP Servers > DHCPServer1 > Static Hosts > Add > Static Host Entry 2. Add the static DHCP assignment: gw-world:/> add DHCPServerPoolStaticHost Host=192.168.1.1 MACAddress=00-90-12-13-14-15 3. All static assignments can then be listed and each is certain switches that require the IP address of a TFTP server from which... value. DHCP Services can be sent as this is listed with the following command: gw-world:/> set DHCPServerPoolStaticHost 1 Host=192.168.1.12 MACAddress=00-90-12-13-14-15 Web Interface 1. The examples assumes that are sent out. Go to the MAC address 00-90...
...DHCP Servers > DHCPServer1 > Static Hosts > Add > Static Host Entry 2. Add the static DHCP assignment: gw-world:/> add DHCPServerPoolStaticHost Host=192.168.1.1 MACAddress=00-90-12-13-14-15 3. All static assignments can then be listed and each is certain switches that require the IP address of a TFTP server from which... value. DHCP Services can be sent as this is listed with the following command: gw-world:/> set DHCPServerPoolStaticHost 1 Host=192.168.1.12 MACAddress=00-90-12-13-14-15 Web Interface 1. The examples assumes that are sent out. Go to the MAC address 00-90...
Product Manual
Page 248
... block. In this topic refer to the NetDefend Firewall on the Internet, the server will be affected by ZoneDefense when a virus is connected to Chapter 12, ZoneDefense. Suspect files can no longer do any harm. This feature is described fully in the Anti-Virus configuration of the configured network range. FTP...
... block. In this topic refer to the NetDefend Firewall on the Internet, the server will be affected by ZoneDefense when a virus is connected to Chapter 12, ZoneDefense. Suspect files can no longer do any harm. This feature is described fully in the Anti-Virus configuration of the configured network range. FTP...
Product Manual
Page 257
... NetDefend Firewall on the email's origin. Using ZoneDefense for blocking local email clients. To implement blocking, the administrator configures the ZoneDefense network range to Chapter 12, ZoneDefense. 6.2.5.1. 6.2.5. Security Mechanisms capa=PIPELINING To indicate that any local receiver. Unsolicited email, sent out in massive quantities by the ALG and related log messages...
... NetDefend Firewall on the email's origin. Using ZoneDefense for blocking local email clients. To implement blocking, the administrator configures the ZoneDefense network range to Chapter 12, ZoneDefense. 6.2.5.1. 6.2.5. Security Mechanisms capa=PIPELINING To indicate that any local receiver. Unsolicited email, sent out in massive quantities by the ALG and related log messages...
Product Manual
Page 288
6.2.9. Security Mechanisms 3. Go to Rules > IP Rules > Add > IPRule 2. Click OK Example 6.12. In order to allow the Gateway to register with the Gatekeeper connected to the Head Office 3. Configuring remote offices for outgoing calls. Now enter: • ...
6.2.9. Security Mechanisms 3. Go to Rules > IP Rules > Add > IPRule 2. Click OK Example 6.12. In order to allow the Gateway to register with the Gatekeeper connected to the Head Office 3. Configuring remote offices for outgoing calls. Now enter: • ...
Product Manual
Page 303
...includes the description or depiction of, or instruction in online games. refer to the Investment Sites category (11). refer to the E-Banking category (12). Examples might be: • www.beatthecrook.com Category 14: Personal Beliefs / Cults A web site may be : • www.democrats...This category does not include Investment related content; Examples might be: • www.loadsofmoney.com.au • www.putsandcalls.com Category 12: E-Banking A web site may be classified under the Crime / Terrorism category if its content includes electronic banking information or services. ...
...includes the description or depiction of, or instruction in online games. refer to the Investment Sites category (11). refer to the E-Banking category (12). Examples might be: • www.beatthecrook.com Category 14: Personal Beliefs / Cults A web site may be : • www.democrats...This category does not include Investment related content; Examples might be: • www.loadsofmoney.com.au • www.putsandcalls.com Category 12: E-Banking A web site may be classified under the Crime / Terrorism category if its content includes electronic banking information or services. ...