User Guide
Page 3
... Types 42 8.2.2 Error Report & Connection Protection 46 8.3 Schedules 48 8.4 X.509 Certificates 49 8.4.1 Introduction to Certificates 49 8.4.2 X.509 Certificates in D-Link Firewall 51 D-Link Firewalls User's Guide
... Types 42 8.2.2 Error Report & Connection Protection 46 8.3 Schedules 48 8.4 X.509 Certificates 49 8.4.1 Introduction to Certificates 49 8.4.2 X.509 Certificates in D-Link Firewall 51 D-Link Firewalls User's Guide
User Guide
Page 4
iii 9 Interfaces 53 9.1 Ethernet 53 9.1.1 Ethernet Interfaces 53 9.1.2 Ethernet Interfaces in D-Link Firewalls 54 9.2 Virtual LAN (VLAN 56 9.2.1 VLAN Infrastructure 56 9.2.2 802.1Q VLAN Standard 57 9.2.3 VLAN Implementation 58 9.2.4 Using Virtual LANs to Expand Firewall Interfaces . . 59 9.3 ...-based Routing Tables 89 10.7.3 Policy-based Routing Policy 89 10.7.4 PBR Execution 89 10.7.5 Scenario: PBR Configuration 91 10.8 Proxy ARP 94 D-Link Firewalls User's Guide
iii 9 Interfaces 53 9.1 Ethernet 53 9.1.1 Ethernet Interfaces 53 9.1.2 Ethernet Interfaces in D-Link Firewalls 54 9.2 Virtual LAN (VLAN 56 9.2.1 VLAN Infrastructure 56 9.2.2 802.1Q VLAN Standard 57 9.2.3 VLAN Implementation 58 9.2.4 Using Virtual LANs to Expand Firewall Interfaces . . 59 9.3 ...-based Routing Tables 89 10.7.3 Policy-based Routing Policy 89 10.7.4 PBR Execution 89 10.7.5 Scenario: PBR Configuration 91 10.8 Proxy ARP 94 D-Link Firewalls User's Guide
User Guide
Page 5
...101 13 Log Settings 103 13.1 Implementation 103 13.1.1 Defining Syslog Receiver 103 13.1.2 Enabling Logging 104 VI Security Polices 108 14 IP Rules 109 14.1 Overview 109 14.1.1 Fields 110 14.1.2 Action types 111 14.2 Address Translation 112...Link Firewall 114 14.3 Scenarios: IP Rules Configuration 116 15 Access (Anti-spoofing) 123 15.1 Overview 123 15.1.1 IP Spoofing 123 15.1.2 Anti-spoofing 124 15.2 Access Rule 124 15.2.1 Function 124 15.2.2 Settings 124 15.3 Scenario: Setting up Access Rule 126 D-Link Firewalls User's Guide
...101 13 Log Settings 103 13.1 Implementation 103 13.1.1 Defining Syslog Receiver 103 13.1.2 Enabling Logging 104 VI Security Polices 108 14 IP Rules 109 14.1 Overview 109 14.1.1 Fields 110 14.1.2 Action types 111 14.2 Address Translation 112...Link Firewall 114 14.3 Scenarios: IP Rules Configuration 116 15 Access (Anti-spoofing) 123 15.1 Overview 123 15.1.1 IP Spoofing 123 15.1.2 Anti-spoofing 124 15.2 Access Rule 124 15.2.1 Function 124 15.2.2 Settings 124 15.3 Scenario: Setting up Access Rule 126 D-Link Firewalls User's Guide
User Guide
Page 6
... 17.2.3 Authentication Agents 135 17.2.4 Authentication Rules 136 17.3 Authentication Process 137 17.4 Scenarios: User Authentication Configuration 137 VII Content Inspection 146 18 Application Layer Gateway (ALG) 147 18... 148 18.2.1 FTP Connections 148 18.2.2 Scenarios: FTP ALG Configuration 150 18.3 HTTP 155 18.3.1 Components & Security Issues 155 18.3.2 Solution 156 18.4 H.323 158 18.4.1 H.323 Standard Overview 158 18.4.2 H.323 Components 158 18... 181 19.1.1 Intrusion Detection Rules 182 19.1.2 Pattern Matching 182 D-Link Firewalls User's Guide
... 17.2.3 Authentication Agents 135 17.2.4 Authentication Rules 136 17.3 Authentication Process 137 17.4 Scenarios: User Authentication Configuration 137 VII Content Inspection 146 18 Application Layer Gateway (ALG) 147 18... 148 18.2.1 FTP Connections 148 18.2.2 Scenarios: FTP ALG Configuration 150 18.3 HTTP 155 18.3.1 Components & Security Issues 155 18.3.2 Solution 156 18.4 H.323 158 18.4.1 H.323 Standard Overview 158 18.4.2 H.323 Components 158 18... 181 19.1.1 Intrusion Detection Rules 182 19.1.2 Pattern Matching 182 D-Link Firewalls User's Guide
User Guide
Page 7
....2.2 Authentication & Integrity 198 20.3 Why VPN in Firewalls 200 20.3.1 VPN Deployment 201 21 VPN Planning 207 21.1 VPN Design Considerations 207 21.1.1 End Point Security 208 21.1.2 Key Distribution 210 22 VPN Protocols & Tunnels 213 22.1 IPsec 213 22.1.1 IPsec protocols 214 22.1.2 IPsec Modes 214 22.1.3 IKE 215 22... Integrity & Authentication 219 22.1.5 Scenarios: IPSec Configuration 223 22.2 PPTP/ L2TP 228 22.2.1 PPTP 228 22.2.2 L2TP 234 22.3 SSL/TLS (HTTPS 243 D-Link Firewalls User's Guide
....2.2 Authentication & Integrity 198 20.3 Why VPN in Firewalls 200 20.3.1 VPN Deployment 201 21 VPN Planning 207 21.1 VPN Design Considerations 207 21.1.1 End Point Security 208 21.1.2 Key Distribution 210 22 VPN Protocols & Tunnels 213 22.1 IPsec 213 22.1.1 IPsec protocols 214 22.1.2 IPsec Modes 214 22.1.3 IKE 215 22... Integrity & Authentication 219 22.1.5 Scenarios: IPSec Configuration 223 22.2 PPTP/ L2TP 228 22.2.1 PPTP 228 22.2.2 L2TP 234 22.3 SSL/TLS (HTTPS 243 D-Link Firewalls User's Guide
User Guide
Page 8
... 246 23 Traffic Shaping 247 23.1 Overview 247 23.1.1 Functions 248 23.1.2 Features 249 23.2 Pipes 249 23.2.1 Precedences and Guarantees 250 23.2.2 Grouping Users of a Pipe 252 23.2.3 Dynamic Bandwidth Balancing 253 23.3 Pipe Rules 253 23.4 Scenarios: Setting up Traffic Shaping 253 24 Server Load Balancing (SLB....3 Automatic Client Login 272 25.4 HTTP Poster 273 25.4.1 URL Format 273 26 DHCP Server & Relayer 275 26.1 DHCP Server 275 26.2 DHCP Relayer 277 D-Link Firewalls User's Guide
... 246 23 Traffic Shaping 247 23.1 Overview 247 23.1.1 Functions 248 23.1.2 Features 249 23.2 Pipes 249 23.2.1 Precedences and Guarantees 250 23.2.2 Grouping Users of a Pipe 252 23.2.3 Dynamic Bandwidth Balancing 253 23.3 Pipe Rules 253 23.4 Scenarios: Setting up Traffic Shaping 253 24 Server Load Balancing (SLB....3 Automatic Client Login 272 25.4 HTTP Poster 273 25.4.1 URL Format 273 26 DHCP Server & Relayer 275 26.1 DHCP Server 275 26.2 DHCP Relayer 277 D-Link Firewalls User's Guide
User Guide
Page 9
viii XI Transparent Mode 280 27 Transparent Mode 281 27.1 Overview 281 27.2 Transparent Mode Implementation in D-Link Firewalls . . . . 282 27.3 Scenarios: Enabling Transparent Mode 284 XII Zone Defense 292 28 Zone Defense 293 28.1 Overview 293 28.2 Zone Defense Switches 293 28.2.1 ....4 Things to Keep in Mind 309 29.4.1 Statistics and Logging Issues 309 29.4.2 Configuration Issues 310 XIV Appendix 312 A Console Commands Reference 315 D-Link Firewalls User's Guide
viii XI Transparent Mode 280 27 Transparent Mode 281 27.1 Overview 281 27.2 Transparent Mode Implementation in D-Link Firewalls . . . . 282 27.3 Scenarios: Enabling Transparent Mode 284 XII Zone Defense 292 28 Zone Defense 293 28.1 Overview 293 28.2 Zone Defense Switches 293 28.2.1 ....4 Things to Keep in Mind 309 29.4.1 Statistics and Logging Issues 309 29.4.2 Configuration Issues 310 XIV Appendix 312 A Console Commands Reference 315 D-Link Firewalls User's Guide
User Guide
Page 10
ix List of Commands 315 About 315 Access 316 ARP 316 ARPSnoop 317 Buffers 317 Certcache 318 CfgLog 319 Connections 319 Cpuid 320 DHCP 320 DHCPRelay 321 DHCPServer 321 DynRoute 321 Frags 322 HA 322 HTTPPoster 322 Ifacegroups 323 IfStat 323 Ikesnoop 324 Ipseckeepalive 325 IPSectunnels 325 IPSecstats 325 Killsa 326 License 326 Lockdown 327 Loghosts 327 Memory 327 Netcon 327 Netobjects 328 OSPF 328 Ping 329 Pipes 329 Proplists 330 ReConfigure 330 Remotes 331 Routes 331 Rules 332 Scrsave 332 Services 333 Shutdown 333 D-Link Firewalls User's Guide
ix List of Commands 315 About 315 Access 316 ARP 316 ARPSnoop 317 Buffers 317 Certcache 318 CfgLog 319 Connections 319 Cpuid 320 DHCP 320 DHCPRelay 321 DHCPServer 321 DynRoute 321 Frags 322 HA 322 HTTPPoster 322 Ifacegroups 323 IfStat 323 Ikesnoop 324 Ipseckeepalive 325 IPSectunnels 325 IPSecstats 325 Killsa 326 License 326 Lockdown 327 Loghosts 327 Memory 327 Netcon 327 Netobjects 328 OSPF 328 Ping 329 Pipes 329 Proplists 330 ReConfigure 330 Remotes 331 Routes 331 Rules 332 Scrsave 332 Services 333 Shutdown 333 D-Link Firewalls User's Guide
User Guide
Page 13
... 262 24.2 A SLB Scenario 266 27.1 Transparent Mode Scenario 1 284 27.2 Transparent Mode Scenario 2 287 28.1 A Zone Defense Scenario 297 29.1 Example HA Setup 303 D-Link Firewalls User's Guide
... 262 24.2 A SLB Scenario 266 27.1 Transparent Mode Scenario 1 284 27.2 Transparent Mode Scenario 2 287 28.1 A Zone Defense Scenario 297 29.1 Example HA Setup 303 D-Link Firewalls User's Guide
User Guide
Page 18
... enable the reader to learn various functions. Document Version Version No.: 1.0 Disclaimer Information in this Document This User's Guide is designed to be a handy configuration manual as well as an Internetworking and security knowledge learning tool for accomplishing certain operations of the product, but provides fundamentals on what concepts the functions...
... enable the reader to learn various functions. Document Version Version No.: 1.0 Disclaimer Information in this Document This User's Guide is designed to be a handy configuration manual as well as an Internetworking and security knowledge learning tool for accomplishing certain operations of the product, but provides fundamentals on what concepts the functions...
User Guide
Page 23
Capabilities • Zone Defence • High Availability (Some models) Details about how to make these features work can be found in specific chapters in this user's guide. D-Link Firewalls User's Guide 4 Chapter 1.
Capabilities • Zone Defence • High Availability (Some models) Details about how to make these features work can be found in specific chapters in this user's guide. D-Link Firewalls User's Guide 4 Chapter 1.
User Guide
Page 27
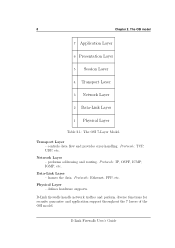
...data. Physical Layer - 8 Chapter 2. Protocols: TCP, UDP, etc. D-Link Firewalls User's Guide Data-Link Layer - The OSI model 7 Application Layer 6 Presentation Layer 5 Session Layer 4 Transport Layer 3 Network Layer 2 Data-Link Layer 1 Physical Layer Table 2.1: The OSI 7-Layer Model. Protocols: Ethernet..., PPP, etc. controls data flow and provides error-handling. performs addressing and routing. D-Link firewalls handle network traffics and perform diverse functions for security...
...data. Physical Layer - 8 Chapter 2. Protocols: TCP, UDP, etc. D-Link Firewalls User's Guide Data-Link Layer - The OSI model 7 Application Layer 6 Presentation Layer 5 Session Layer 4 Transport Layer 3 Network Layer 2 Data-Link Layer 1 Physical Layer Table 2.1: The OSI 7-Layer Model. Protocols: Ethernet..., PPP, etc. controls data flow and provides error-handling. performs addressing and routing. D-Link firewalls handle network traffics and perform diverse functions for security...
User Guide
Page 29
... problems described here will protect you choose to mislead potential buyers. D-Link Firewalls User's Guide Security means much more than just firewalls. 10 Chapter 3. The following is the network's answer to D-Link firewalls; A common misconception is that this only scratches the ...compensate for which firewall you against everything". instead it was designed. This is a necessary first step towards securing your network and computers. This can only protect against ? Firewall Principles complies with , and in terms of the number ...
... problems described here will protect you choose to mislead potential buyers. D-Link Firewalls User's Guide Security means much more than just firewalls. 10 Chapter 3. The following is the network's answer to D-Link firewalls; A common misconception is that this only scratches the ...compensate for which firewall you against everything". instead it was designed. This is a necessary first step towards securing your network and computers. This can only protect against ? Firewall Principles complies with , and in terms of the number ...
User Guide
Page 30
...be permitted. In order for use . What does a Firewall NOT protect against this sort of this policy and why it must be a security policy that allow direct ODBC access via HTTP in a browser or e-mail program. However, modern systems are not intended for such a policy... web servers. by opening an unrecognized program sent to them by a thorough investigation of an organization should be made aware of attack, D-Link Firewalls User's Guide Such attacks include: • HTML pages containing javascript or Java that attack the network "from management down. 3.2. One example of this...
...be permitted. In order for use . What does a Firewall NOT protect against this sort of this policy and why it must be a security policy that allow direct ODBC access via HTTP in a browser or e-mail program. However, modern systems are not intended for such a policy... web servers. by opening an unrecognized program sent to them by a thorough investigation of an organization should be made aware of attack, D-Link Firewalls User's Guide Such attacks include: • HTML pages containing javascript or Java that attack the network "from management down. 3.2. One example of this...
User Guide
Page 31
... problem in this poses the greatest technical threat of all forms of network-based attack, as mail servers, DNS servers and web servers. D-Link Firewalls User's Guide Buffer overruns can block scripts and other similar devices in circulation long enough for data-driven attacks are opened . Here, the only...protect your systems or those of a small group of people, or if the trojan or virus in question has not been in order to increase security, but it should be noted that the fundamental functionality of local files when they are : • Public servers such as almost all ...
... problem in this poses the greatest technical threat of all forms of network-based attack, as mail servers, DNS servers and web servers. D-Link Firewalls User's Guide Buffer overruns can block scripts and other similar devices in circulation long enough for data-driven attacks are opened . Here, the only...protect your systems or those of a small group of people, or if the trojan or virus in question has not been in order to increase security, but it should be noted that the fundamental functionality of local files when they are : • Public servers such as almost all ...
User Guide
Page 32
... local computers and all computers communicate directly with each other. This may seem obvious. D-Link Firewalls User's Guide As a result, intruders can cause all data security problems are as secure as the protected network and can be connected directly to open documents containing malevolent scripts. ...the results of your system. • Web browsers. Automation of processes and simplifying operations for the benefit of users creates increased internal complexity and thereby increased risks of vulnerabilities. • Desktop software, primarily that which to great extent ...
... local computers and all computers communicate directly with each other. This may seem obvious. D-Link Firewalls User's Guide As a result, intruders can cause all data security problems are as secure as the protected network and can be connected directly to open documents containing malevolent scripts. ...the results of your system. • Web browsers. Automation of processes and simplifying operations for the benefit of users creates increased internal complexity and thereby increased risks of vulnerabilities. • Desktop software, primarily that which to great extent ...
User Guide
Page 33
...ensure that which passes through the VPN or modem connection and the company's network, regardless of protection as a D-Link Firewalls User's Guide By doing this task. The D-Link Firewall features just such a facility. 3.2.6 Holes between DMZs and Internal Networks Although the advent of extranets and ... or in a special DMZ or outside a firewall that although the connection itself is dedicated to be regarded as the security of communication permitted. For VPN connections, a competent VPN client that mobile computers never communicate directly with . The VPN endpoints should...
...ensure that which passes through the VPN or modem connection and the company's network, regardless of protection as a D-Link Firewalls User's Guide By doing this task. The D-Link Firewall features just such a facility. 3.2.6 Holes between DMZs and Internal Networks Although the advent of extranets and ... or in a special DMZ or outside a firewall that although the connection itself is dedicated to be regarded as the security of communication permitted. For VPN connections, a competent VPN client that mobile computers never communicate directly with . The VPN endpoints should...
User Guide
Page 34
... this is simple - By locating the data source, e.g. an SQL server, in a DMZ is increased segmentation of a non-routable protocol such as an intermediate. D-Link Firewalls User's Guide In such cases, data-driven attacks pose a huge threat. In our experience, even the most inexperienced of the network, you can execute commands on these... techniques, specifically developed to data sources on protected networks. The problem with data sources on the internal network? It should also be completely secure.
... this is simple - By locating the data source, e.g. an SQL server, in a DMZ is increased segmentation of a non-routable protocol such as an intermediate. D-Link Firewalls User's Guide In such cases, data-driven attacks pose a huge threat. In our experience, even the most inexperienced of the network, you can execute commands on these... techniques, specifically developed to data sources on protected networks. The problem with data sources on the internal network? It should also be completely secure.
User Guide
Page 35
.... An insurmountable problem may arise when the web server needs to which the web server has access. Another form of data from the web server. D-Link Firewalls User's Guide The best way of intrusion. 16 Chapter 3. Firewall Principles Rather, the problem is to move the affected data source to a separate network segment...
.... An insurmountable problem may arise when the web server needs to which the web server has access. Another form of data from the web server. D-Link Firewalls User's Guide The best way of intrusion. 16 Chapter 3. Firewall Principles Rather, the problem is to move the affected data source to a separate network segment...
User Guide
Page 40
... Go to factory default. - Interfaces: Diplays status for DHCP servers. - IDS: Displays IDS status information. - DHCP Server: Displays usage information for interfaces and tunnels. - D-Link Firewalls User's Guide Connections: Displays current connections through the firewall. - IPSec: Displays IPSec status information. - System: Here system status is displayed. - SLB: Displays SLB status information. Useful...
... Go to factory default. - Interfaces: Diplays status for DHCP servers. - IDS: Displays IDS status information. - DHCP Server: Displays usage information for interfaces and tunnels. - D-Link Firewalls User's Guide Connections: Displays current connections through the firewall. - IPSec: Displays IPSec status information. - System: Here system status is displayed. - SLB: Displays SLB status information. Useful...