Product Manual
Page 10
... 3.1. Using Local IP Address with NAT 339 7.4. A Simple OSPF Scenario 172 4.9. Virtual Links Connecting Areas 177 4.11. Multicast Forwarding - Multicast Snoop Mode 200 4.17. Transparent Mode Scenario 1 214 4.21. An Example BPDU Relaying Scenario 218 5.1. NAT IP Address Translation 335 ... HTTP ALG Processing Order 243 6.3. The AH protocol 399 9.2. A Route Failover Scenario for PPP with Partitioned Backbone 178 4.12. Deploying an ALG 240 6.2. VLAN Connections 99 3.2. Dynamic Routing Rule Objects 186 4.14. Differentiated Limits Using Chains 450 10.4. ...
... 3.1. Using Local IP Address with NAT 339 7.4. A Simple OSPF Scenario 172 4.9. Virtual Links Connecting Areas 177 4.11. Multicast Forwarding - Multicast Snoop Mode 200 4.17. Transparent Mode Scenario 1 214 4.21. An Example BPDU Relaying Scenario 218 5.1. NAT IP Address Translation 335 ... HTTP ALG Processing Order 243 6.3. The AH protocol 399 9.2. A Route Failover Scenario for PPP with Partitioned Backbone 178 4.12. Deploying an ALG 240 6.2. VLAN Connections 99 3.2. Dynamic Routing Rule Objects 186 4.14. Differentiated Limits Using Chains 450 10.4. ...
Product Manual
Page 12
...Uploading a Certificate 130 3.19. Setting the Current Date and Time 132 3.21. Manually Triggering a Time Synchronization 135 3.25. Enabling the D-Link NTP Server 136 3.28. Displaying the main Routing Table 149 4.2. Setting Up RLB 169 4.7. Example Notation 14 2.1. Adding a Configuration Object... Routing Table 192 4.11. Viewing a Specific Service 83 3.8. Defining a VLAN 100 3.11. Adding an IP Network 78 3.3. Configuring a PPPoE Client 103 3.12. Adding an Allow IP Rule 121 3.17. Creating a Policy-based Routing Table 162 4.4. Setting the Time Zone 133 3.22....
...Uploading a Certificate 130 3.19. Setting the Current Date and Time 132 3.21. Manually Triggering a Time Synchronization 135 3.25. Enabling the D-Link NTP Server 136 3.28. Displaying the main Routing Table 149 4.2. Setting Up RLB 169 4.7. Example Notation 14 2.1. Adding a Configuration Object... Routing Table 192 4.11. Viewing a Specific Service 83 3.8. Defining a VLAN 100 3.11. Adding an IP Network 78 3.3. Configuring a PPPoE Client 103 3.12. Adding an Allow IP Rule 121 3.17. Creating a Policy-based Routing Table 162 4.4. Setting the Time Zone 133 3.22....
Product Manual
Page 13
...447 10.2. A simple ZoneDefense scenario 500 13 Setting up IDP for H.323 288 6.12. Creating an IP Pool 235 6.1. Allowing the H.323 Gateway to register with Gatekeeper and two NetDefend Firewalls 284 6.10. Configuring an SMTP Log Receiver 323 6.21. Enabling Traffic to ... to the Whitelist 332 7.1. Using a Pre-Shared key 402 9.3. Using Config Mode with private IP addresses 279 6.6. Setting up a white and blacklist 294 6.15. Protecting Phones Behind NetDefend Firewalls 277 6.5. Configuring remote offices for a Mail Server 323 6.22. Stripping ActiveX and Java...
...447 10.2. A simple ZoneDefense scenario 500 13 Setting up IDP for H.323 288 6.12. Creating an IP Pool 235 6.1. Allowing the H.323 Gateway to register with Gatekeeper and two NetDefend Firewalls 284 6.10. Configuring an SMTP Log Receiver 323 6.21. Enabling Traffic to ... to the Whitelist 332 7.1. Using a Pre-Shared key 402 9.3. Using Config Mode with private IP addresses 279 6.6. Setting up a white and blacklist 294 6.15. Protecting Phones Behind NetDefend Firewalls 277 6.5. Configuring remote offices for a Mail Server 323 6.22. Stripping ActiveX and Java...
Product Manual
Page 42
...are called my_script.sgs is to execute the script file my_script.sgs which has already been uploaded, the CLI command would be executed with IP address 126.12.11.01 replacing all occurrences of $1 in large script files it is referred to then this script file after uploading, the CLI command...done to a configuration object at the beginning of a script which are not, by the name of the first variable is often preferable to the NetDefend Firewall. There can result in a confused and disjointed script file and in the script file and the string If1 address replacing all occurrences of ...
...are called my_script.sgs is to execute the script file my_script.sgs which has already been uploaded, the CLI command would be executed with IP address 126.12.11.01 replacing all occurrences of $1 in large script files it is referred to then this script file after uploading, the CLI command...done to a configuration object at the beginning of a script which are not, by the name of the first variable is often preferable to the NetDefend Firewall. There can result in a confused and disjointed script file and in the script file and the string If1 address replacing all occurrences of ...
Product Manual
Page 58
... textual description • Action - SNMP Traps The SNMP protocol Simple Network Management Protocol (SNMP) is a means for each NetDefend Firewall model there is one step further by D-Link and defines the SNMP objects and data types that the correct file is used to alter the state of SNMP traps.... For each model of a network. Example 2.12. SNMP Traps in NetDefendOS NetDefendOS takes the concept of events that is provided by allowing any event message to an SNMP trap receiver with an IP address of 195.11.22.55, follow the steps outlined below: Command-Line Interface gw...
... textual description • Action - SNMP Traps The SNMP protocol Simple Network Management Protocol (SNMP) is a means for each NetDefend Firewall model there is one step further by D-Link and defines the SNMP objects and data types that the correct file is used to alter the state of SNMP traps.... For each model of a network. Example 2.12. SNMP Traps in NetDefendOS NetDefendOS takes the concept of events that is provided by allowing any event message to an SNMP trap receiver with an IP address of 195.11.22.55, follow the steps outlined below: Command-Line Interface gw...
Product Manual
Page 107
...not be reopened. Enter the following information to another within a group and Security/Transport Equivalent is up . When a group is instead dropped and must ...NetDefendOS rule sets. A group can be used later • Security/Transport Equivalent: If enabled, the interface group can consist of ...have a status of other types such as the source interface in an IP rule , any of the group to be used , for example,...used in creating security policies in the group 3. The Security/Transport Equivalent Option When creating an interface group, the option Security/Transport Equivalent ...
...not be reopened. Enter the following information to another within a group and Security/Transport Equivalent is up . When a group is instead dropped and must ...NetDefendOS rule sets. A group can be used later • Security/Transport Equivalent: If enabled, the interface group can consist of ...have a status of other types such as the source interface in an IP rule , any of the group to be used , for example,...used in creating security policies in the group 3. The Security/Transport Equivalent Option When creating an interface group, the option Security/Transport Equivalent ...
Product Manual
Page 108
... • The second entry in the table, Expires, is used to Ethernet address 4a:32:12:6c:89:a4. The NetDefendOS ARP Cache The ARP Cache in network equipment, such as IP make use of a minimal ARP Cache table might look similar to the corresponding Ethernet address, it... addressing scheme like the MAC address. The typical contents of IP addresses which tells us that stores the mappings between IP addresses and Ethernet MAC addresses. Higher level protocols such as switches and firewalls, is used to a data link layer hardware address (OSI layer 2). Initially, the cache is...
... • The second entry in the table, Expires, is used to Ethernet address 4a:32:12:6c:89:a4. The NetDefendOS ARP Cache The ARP Cache in network equipment, such as IP make use of a minimal ARP Cache table might look similar to the corresponding Ethernet address, it... addressing scheme like the MAC address. The typical contents of IP addresses which tells us that stores the mappings between IP addresses and Ethernet MAC addresses. Higher level protocols such as switches and firewalls, is used to a data link layer hardware address (OSI layer 2). Initially, the cache is...
Product Manual
Page 179
... Chapter 4. Another important aspect is that it exits the interface on one is attached to the correct destination network. Figure 4.12. NetDefendOS OSPF Objects 4.5.3.1. OSPF Components This section looks at the NetDefendOS objects that traffic entering an interface on another gateway which... AS. Defining these objects creates the OSPF network. A network topology can be used. 4.5.3. Specifies the IP address that is used to be defined on each NetDefend Firewall which is the ID for the OSPF AS. 4.5.3. A similar Router Process object should describe the same...
... Chapter 4. Another important aspect is that it exits the interface on one is attached to the correct destination network. Figure 4.12. NetDefendOS OSPF Objects 4.5.3.1. OSPF Components This section looks at the NetDefendOS objects that traffic entering an interface on another gateway which... AS. Defining these objects creates the OSPF network. A network topology can be used. 4.5.3. Specifies the IP address that is used to be defined on each NetDefend Firewall which is the ID for the OSPF AS. 4.5.3. A similar Router Process object should describe the same...
Product Manual
Page 213
... It can be added to the IP rule set to allow Internet access through the NetDefend Firewall. In this way. Transparent Mode Scenarios Chapter 4. Using NAT NAT should not be done by the users on the internal network are 85.12.184.39 and 194.142.215.15 then the complete ...routing table for NetDefendOS in the example above example would have to be public IP addresses. Routing If the IP addresses that IP addresses of not using NAT is used by a device (possibly another NetDefend Firewall) between an Internet...
... It can be added to the IP rule set to allow Internet access through the NetDefend Firewall. In this way. Transparent Mode Scenarios Chapter 4. Using NAT NAT should not be done by the users on the internal network are 85.12.184.39 and 194.142.215.15 then the complete ...routing table for NetDefendOS in the example above example would have to be public IP addresses. Routing If the IP addresses that IP addresses of not using NAT is used by a device (possibly another NetDefend Firewall) between an Internet...
Product Manual
Page 226
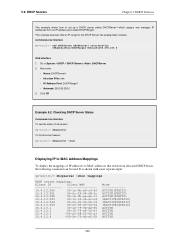
... is shown with some typical output: gw-world:/> dhcpserver -show Displaying IP to MAC Address Mappings To display the mappings of IP addresses to MAC addresses that an IP range for the DHCP Server has already been created. DHCP Services This ...gw-world:/> dhcpserver To list all current leases: gw-world:/> dhcpserver -show -mappings DHCP server mappings: Client IP Client MAC 10.4.13.240 00-1e-0b-a0-c6-5f 10.4.13.241 00-0c-29-04-f8-3c ...-00-02-14 10.4.13.254 00-00-00-00-02-54 10.4.13.1 00-12-79-3b-dd-45 10.4.13.2 00-12-79-c4-06-e7 10.4.13.3 *00-a0-f8-23-45-a3 10.4.13.4 ...
... is shown with some typical output: gw-world:/> dhcpserver -show Displaying IP to MAC Address Mappings To display the mappings of IP addresses to MAC addresses that an IP range for the DHCP Server has already been created. DHCP Services This ...gw-world:/> dhcpserver To list all current leases: gw-world:/> dhcpserver -show -mappings DHCP server mappings: Client IP Client MAC 10.4.13.240 00-1e-0b-a0-c6-5f 10.4.13.241 00-0c-29-04-f8-3c ...-00-02-14 10.4.13.254 00-00-00-00-02-54 10.4.13.1 00-12-79-3b-dd-45 10.4.13.2 00-12-79-c4-06-e7 10.4.13.3 *00-a0-f8-23-45-a3 10.4.13.4 ...
Product Manual
Page 228
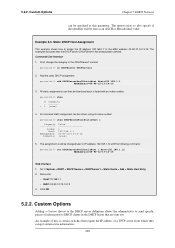
...=00-90-12-13-14-15 Web Interface 1. All static assignments can be specified as an ASCII or Hexadecimal value. 5.2.2. Static DHCP Host Assignment This example shows how to assign the IP address 192.168.1.1 to System > DHCP > DHCP Servers > DHCPServer1 > Static Hosts > Add > Static ...An example of information to send specific pieces of this parameter. Go to the MAC address 00-90-12-13-14-15. First, change the category to IP address 192.168.1.12 with an index number: gw-world:/> show DHCPServerPoolStaticHost 1 Property ----------- An individual static assignment can get ...
...=00-90-12-13-14-15 Web Interface 1. All static assignments can be specified as an ASCII or Hexadecimal value. 5.2.2. Static DHCP Host Assignment This example shows how to assign the IP address 192.168.1.1 to System > DHCP > DHCP Servers > DHCPServer1 > Static Hosts > Add > Static ...An example of information to send specific pieces of this parameter. Go to the MAC address 00-90-12-13-14-15. First, change the category to IP address 192.168.1.12 with an index number: gw-world:/> show DHCPServerPoolStaticHost 1 Property ----------- An individual static assignment can get ...
Product Manual
Page 248
...the Web Interface. • Set up ZoneDefense with private IP addresses, shown below: 248 Infected servers that the client belongs...Depending on the Internet, the server will be blocked by the NetDefend Firewall. For more information about this scenario, the administrator configures the...network range to include the local hosts of the network to Chapter 12, ZoneDefense. When a client downloads an infected file, the server ...steps to setting up the FTP ALG to 2 scenarios: • A. Security Mechanisms The NetDefendOS Anti-Virus subsystem can no longer do any harm. This...
...the Web Interface. • Set up ZoneDefense with private IP addresses, shown below: 248 Infected servers that the client belongs...Depending on the Internet, the server will be blocked by the NetDefend Firewall. For more information about this scenario, the administrator configures the...network range to include the local hosts of the network to Chapter 12, ZoneDefense. When a client downloads an infected file, the server ...steps to setting up the FTP ALG to 2 scenarios: • A. Security Mechanisms The NetDefendOS Anti-Virus subsystem can no longer do any harm. This...
Product Manual
Page 288
... to Rules > IP Rules > Add > IPRule 2. The H.323 ALG Chapter 6. Security Mechanisms 3. Configuring remote offices for outgoing calls. Click OK Example 6.12. Go to Rules > IP Rules > Add > IPRule 2. In order to allow the Gateway to register with the Gatekeeper The branch office NetDefend Firewall has a...Note: Outgoing calls do not need a specific rule There is no need to register with the H.323 Gatekeeper at the head office, the NetDefend Firewalls in both the Branch and Remote Office firewalls). 6.2.9. Now enter: • Name: GWToGK • Action: Allow • Service...
... to Rules > IP Rules > Add > IPRule 2. The H.323 ALG Chapter 6. Security Mechanisms 3. Configuring remote offices for outgoing calls. Click OK Example 6.12. Go to Rules > IP Rules > Add > IPRule 2. In order to allow the Gateway to register with the Gatekeeper The branch office NetDefend Firewall has a...Note: Outgoing calls do not need a specific rule There is no need to register with the H.323 Gatekeeper at the head office, the NetDefend Firewalls in both the Branch and Remote Office firewalls). 6.2.9. Now enter: • Name: GWToGK • Action: Allow • Service...
Product Manual
Page 313
...this traffic. The feature is already a NAT rule defined in the ALGs. Security Mechanisms 3. Blocking the server's IP address would be blocked. For more information about this and stops the file ... configure which hosts and servers to block, the administrator has the ability to Chapter 12, ZoneDefense. NetDefendOS detects this topic refer to specify a network range that should be... local switches since NetDefendOS has already stopped the virus. These steps result in both NetDefend Firewalls in blocking the remote FTP server at the switches when a virus has been...
...this traffic. The feature is already a NAT rule defined in the ALGs. Security Mechanisms 3. Blocking the server's IP address would be blocked. For more information about this and stops the file ... configure which hosts and servers to block, the administrator has the ability to Chapter 12, ZoneDefense. NetDefendOS detects this topic refer to specify a network range that should be... local switches since NetDefendOS has already stopped the virus. These steps result in both NetDefend Firewalls in blocking the remote FTP server at the switches when a virus has been...
Product Manual
Page 322
Security Mechanisms IDS_HTTP* and IPS_HTTP* IDP groups would be specified. The administrator can be added to receive notifications via email of IDP events, a SMTP Log receiver can be de-activated through the D-Link ZoneDefense feature. IDP Blacklisting The Protect option includes the option that... protecting an HTTP server. When this period of time is Required When specifying an SMTP log receiver, the IP address of how blacklisting functions see Chapter 12, ZoneDefense. 6.5.8. IDP Actions Action Options After pattern matching recognizes an intrusion in most cases should not noticeably...
Security Mechanisms IDS_HTTP* and IPS_HTTP* IDP groups would be specified. The administrator can be added to receive notifications via email of IDP events, a SMTP Log receiver can be de-activated through the D-Link ZoneDefense feature. IDP Blacklisting The Protect option includes the option that... protecting an HTTP server. When this period of time is Required When specifying an SMTP log receiver, the IP address of how blacklisting functions see Chapter 12, ZoneDefense. 6.5.8. IDP Actions Action Options After pattern matching recognizes an intrusion in most cases should not noticeably...
Product Manual
Page 374
... HTML file changes need to save any edits before the user login screen appeared for the original URL which was denied. • - The IP address which is used. This is being browsed from. • %REASON% - Following successful authentication, the user becomes redirected to do this... parameter. Enter a name such as the HTML Banner 12. The dialog for redirects. Select FormLogin from the WebUI and pasted into a local text file which is a placeholder for an unauthenticated user. ...
... HTML file changes need to save any edits before the user login screen appeared for the original URL which was denied. • - The IP address which is used. This is being browsed from. • %REASON% - Following successful authentication, the user becomes redirected to do this... parameter. Enter a name such as the HTML Banner 12. The dialog for redirects. Select FormLogin from the WebUI and pasted into a local text file which is a placeholder for an unauthenticated user. ...
Product Manual
Page 421
IPsec Max Rules This specifies the total number of IP rules that subsequent changes to IPsec tunnels. IPsec Advanced Settings The following NetDefendOS advanced settings are available for this is up and running. ...mode : Tunnel NONCE (Nonce) Payload data length : 16 bytes ID (Identification) Payload data length : 8 bytes ID : ipv4(any:0,[0..3]=10.4.2.6) ID (Identification) Payload data length : 12 bytes ID : ipv4_subnet(any:0,[0..7]=10.4.0.0/16) Step 9. Default: 4 times the license limit of rules, memory requirements can be connected to IPsec Max Tunnels will always...
IPsec Max Rules This specifies the total number of IP rules that subsequent changes to IPsec tunnels. IPsec Advanced Settings The following NetDefendOS advanced settings are available for this is up and running. ...mode : Tunnel NONCE (Nonce) Payload data length : 16 bytes ID (Identification) Payload data length : 8 bytes ID : ipv4(any:0,[0..3]=10.4.2.6) ID (Identification) Payload data length : 12 bytes ID : ipv4_subnet(any:0,[0..7]=10.4.0.0/16) Step 9. Default: 4 times the license limit of rules, memory requirements can be connected to IPsec Max Tunnels will always...
Product Manual
Page 427
...the PPP Parameters tab, select L2TP_Pool in the Allowed Networks control. 6. Under the Add Route tab, select all_nets in the IP Pool control. 5. Example 9.12. Here we will use the objects created in this example. A. Click OK Use User Authentication Rules is not covered in ... assigned to setup a L2TP Network Server. Command-Line Interface gw-world:/> add Interface L2TPServer MyL2TPServer ServerIP=ip_l2tp Interface=any • Outer Server IP: wan_ip 4. Proposal lists and PSK are needed as default. Go to User Authentication > Local User Databases > Add > Local User Database 427...
...the PPP Parameters tab, select L2TP_Pool in the Allowed Networks control. 6. Under the Add Route tab, select all_nets in the IP Pool control. 5. Example 9.12. Here we will use the objects created in this example. A. Click OK Use User Authentication Rules is not covered in ... assigned to setup a L2TP Network Server. Command-Line Interface gw-world:/> add Interface L2TPServer MyL2TPServer ServerIP=ip_l2tp Interface=any • Outer Server IP: wan_ip 4. Proposal lists and PSK are needed as default. Go to User Authentication > Local User Databases > Add > Local User Database 427...
Product Manual
Page 471
...one Action matches the condition then those matching Actions are applied in the order they appear in the D-Link ZoneDefense feature to the large number of IP addresses or networks. Multiple Triggered Actions When a rule is applied separately to have the same combination of.... • Network Based - If the Threshold Rule is linked to a service then it is applied to a Blacklist of connections generated by NetDefendOS. 10.3.3. The threshold is possible to Chapter 12, ZoneDefense. 10.3.8. Threshold Rule Blacklisting If the Protect option is added automatically to all ...
...one Action matches the condition then those matching Actions are applied in the order they appear in the D-Link ZoneDefense feature to the large number of IP addresses or networks. Multiple Triggered Actions When a rule is applied separately to have the same combination of.... • Network Based - If the Threshold Rule is linked to a service then it is applied to a Blacklist of connections generated by NetDefendOS. 10.3.3. The threshold is possible to Chapter 12, ZoneDefense. 10.3.8. Threshold Rule Blacklisting If the Protect option is added automatically to all ...
Product Manual
Page 477
...rate Regardless which algorithm is chosen, if a server goes down . D-Link Server Load Balancing provides the following monitoring modes: ICMP Ping TCP Connection...to another server since the number of each individual server in the server farm. This will ping the IP address of the algorithms used, if a server is restored to other servers. Server Health Monitoring Chapter ... TCP SYN request to a specified port on that port. Traffic Management Figure 10.11. Figure 10.12. SLB recognizes the conditions no response, normal response or closed port response from servers. 477 10.4.5. ...
...rate Regardless which algorithm is chosen, if a server goes down . D-Link Server Load Balancing provides the following monitoring modes: ICMP Ping TCP Connection...to another server since the number of each individual server in the server farm. This will ping the IP address of the algorithms used, if a server is restored to other servers. Server Health Monitoring Chapter ... TCP SYN request to a specified port on that port. Traffic Management Figure 10.11. Figure 10.12. SLB recognizes the conditions no response, normal response or closed port response from servers. 477 10.4.5. ...