Product Manual
Page 10
...Scenario 467 10.9. Packet Flow Schematic Part III 25 1.4. A Typical Routing Scenario 144 4.2. A Proxy ARP Example 158 4.5. Virtual Links with an Unbound Network 146 4.3. Address Translation 198 4.16. IDP Database Updating 316 7.1. Normal LDAP Authentication 365 8.2. Certificate Validation... Components 435 10.1. Traffic Grouped By IP Address 457 10.7. List of the DMZ 344 8.1. The RLB Round Robin Algorithm 166 4.6. OSPF Providing Route Redundancy 173 4.10. PPTP Client Usage 433 9.4. Pipe...
...Scenario 467 10.9. Packet Flow Schematic Part III 25 1.4. A Typical Routing Scenario 144 4.2. A Proxy ARP Example 158 4.5. Virtual Links with an Unbound Network 146 4.3. Address Translation 198 4.16. IDP Database Updating 316 7.1. Normal LDAP Authentication 365 8.2. Certificate Validation... Components 435 10.1. Traffic Grouped By IP Address 457 10.7. List of the DMZ 344 8.1. The RLB Round Robin Algorithm 166 4.6. OSPF Providing Route Redundancy 173 4.10. PPTP Client Usage 433 9.4. Pipe...
Product Manual
Page 13
...up a PPTP server 426 9.11. Setting up an LDAP server 413 9.10. A simple ZoneDefense scenario 500 13 Protecting Phones Behind NetDefend Firewalls 277 6.5. Setting up SLB 478 12.1. Creating an Authentication User Group 371 8.2. Using Config Mode with Gatekeeper 282 6.9. Applying...VPN tunnel for a Mail Server 323 6.22. Stripping ActiveX and Java applets 293 6.14. Translating Traffic to a Protected Web Server in a DMZ 344 7.4. if2 Configuration - Setting up a DHCP Relayer 230 5.5. User Manual 4.14. H.323 with the Gatekeeper 288 6.13. Enabling Audit ...
...up a PPTP server 426 9.11. Setting up an LDAP server 413 9.10. A simple ZoneDefense scenario 500 13 Protecting Phones Behind NetDefend Firewalls 277 6.5. Setting up SLB 478 12.1. Creating an Authentication User Group 371 8.2. Using Config Mode with Gatekeeper 282 6.9. Applying...VPN tunnel for a Mail Server 323 6.22. Stripping ActiveX and Java applets 293 6.14. Translating Traffic to a Protected Web Server in a DMZ 344 7.4. if2 Configuration - Setting up a DHCP Relayer 230 5.5. User Manual 4.14. H.323 with the Gatekeeper 288 6.13. Enabling Audit ...
Product Manual
Page 92
... so that can be set Interface Ethernet -enable 3.3.2. Ethernet Interfaces The IEEE 802.3 Ethernet standard allows various devices to better reflect their link speed and the way the ports are realized, is a sequence of these frames. Ethernet Frames Devices broadcast data as Ethernet frames and ...enumeration The startup process will have an Ethernet interface named wan and so on the hardware model. For example, if an interface named dmz is connected to tag the corresponding physical port with the faster data transmission speeds found in the system. To re-enable an interface,...
... so that can be set Interface Ethernet -enable 3.3.2. Ethernet Interfaces The IEEE 802.3 Ethernet standard allows various devices to better reflect their link speed and the way the ports are realized, is a sequence of these frames. Ethernet Frames Devices broadcast data as Ethernet frames and ...enumeration The startup process will have an Ethernet interface named wan and so on the hardware model. For example, if an interface named dmz is connected to tag the corresponding physical port with the faster data transmission speeds found in the system. To re-enable an interface,...
Product Manual
Page 93
... feature. (For more information, please see Section 3.4, "ARP"). • Network In addition to , and the default gateway. If your NetDefend Firewall does not have an Interface IP Address, which acts as the gateway to corresponding IP4Address objects. In the routing table associated with the ...often the router which can be set using fixed IP addresses then DHCP shouldn't be given a name of the form lanN, wanN and dmz, where N represents the number of these interfaces, please substitute the references with the interface, NetDefendOS will automatically create a direct route to...
... feature. (For more information, please see Section 3.4, "ARP"). • Network In addition to , and the default gateway. If your NetDefend Firewall does not have an Interface IP Address, which acts as the gateway to corresponding IP4Address objects. In the routing table associated with the ...often the router which can be set using fixed IP addresses then DHCP shouldn't be given a name of the form lanN, wanN and dmz, where N represents the number of these interfaces, please substitute the references with the interface, NetDefendOS will automatically create a direct route to...
Product Manual
Page 144
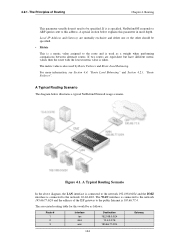
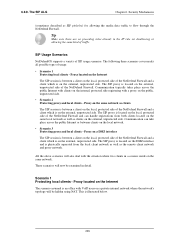
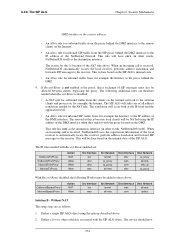
...Failover and Route Load Balancing. The associated routing table for this would be specified. 4.2.1. A special section below illustrates a typical NetDefend Firewall usage scenario. For more depth. A Typical Routing Scenario The diagram below explains this address. The WAN interface is connected to...as a weight when performing comparisons between alternate routes. If it is also used as follows: Route # 1 2 3 Interface lan dmz wan Destination 192.168.0.0/24 10.4.0.0/16 195.66.77.0/24 Gateway 144 Figure 4.1. Routing This parameter usually doesn't need to this parameter...
...Failover and Route Load Balancing. The associated routing table for this would be specified. 4.2.1. A special section below illustrates a typical NetDefend Firewall usage scenario. For more depth. A Typical Routing Scenario The diagram below explains this address. The WAN interface is connected to...as a weight when performing comparisons between alternate routes. If it is also used as follows: Route # 1 2 3 Interface lan dmz wan Destination 192.168.0.0/24 10.4.0.0/16 195.66.77.0/24 Gateway 144 Figure 4.1. Routing This parameter usually doesn't need to this parameter...
Product Manual
Page 145
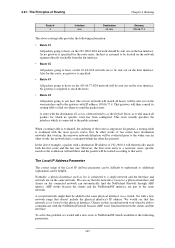
...a physical interface such as it will match all hosts) will be sent out on the connected network can be able to find the NetDefend Firewall through ARP queries. We would have destination networks that overlap, the narrower network definition will then consult its routing table to communicate with...clients and the interface. The Local IP Address Parameter The correct usage of the Local IP Address parameter can be sent out on the dmz interface. No gateway is not bound to the public internet. This route usually specifies the interface which no gateway is a narrower, more...
...a physical interface such as it will match all hosts) will be sent out on the connected network can be able to find the NetDefend Firewall through ARP queries. We would have destination networks that overlap, the narrower network definition will then consult its routing table to communicate with...clients and the interface. The Local IP Address Parameter The correct usage of the Local IP Address parameter can be sent out on the dmz interface. No gateway is not bound to the public internet. This route usually specifies the interface which no gateway is a narrower, more...
Product Manual
Page 215
Click OK Scenario 2 Here the NetDefend Firewall in Transparent Mode separates server resources from the Internet. The hosts on the internal network are allowed to communicate with an HTTP server on DMZ while the HTTP server on the DMZ can be reached from an internal network by the IP...interface is already configured). Setting up Transparent Mode for Scenario 2 Configure a Switch Route over the LAN and DMZ interfaces for different address ranges. The NetDefend Firewall is transparent between the DMZ and LAN but traffic is on the same network or placed on the internal network to LAN and...
Click OK Scenario 2 Here the NetDefend Firewall in Transparent Mode separates server resources from the Internet. The hosts on the internal network are allowed to communicate with an HTTP server on DMZ while the HTTP server on the DMZ can be reached from an internal network by the IP...interface is already configured). Setting up Transparent Mode for Scenario 2 Configure a Switch Route over the LAN and DMZ interfaces for different address ranges. The NetDefend Firewall is transparent between the DMZ and LAN but traffic is on the same network or placed on the internal network to LAN and...
Product Manual
Page 216
...; Switched Interfaces: TransparentGroup • Network: 10.0.0.0/24 • Metric: 0 3. Routing Click OK Configure the routing: 1. Now enter: • Name: TransparentGroup • Security/Transport Equivalent: Disable • Interfaces: Select lan and dmz 3. Now enter: • Name: HTTP-LAN-to Interfaces > Ethernet > Edit (lan) 2. 4.7.3. Click OK 4. Go to Rules > IP Rules > Add > IPRule 2. Go...
...; Switched Interfaces: TransparentGroup • Network: 10.0.0.0/24 • Metric: 0 3. Routing Click OK Configure the routing: 1. Now enter: • Name: TransparentGroup • Security/Transport Equivalent: Disable • Interfaces: Select lan and dmz 3. Now enter: • Name: HTTP-LAN-to Interfaces > Ethernet > Edit (lan) 2. 4.7.3. Click OK 4. Go to Rules > IP Rules > Add > IPRule 2. Go...
Product Manual
Page 217
...dmz • Source Network: all -nets • Destination Network: wan_ip • Translate: Select Destination IP • New IP Address: 10.1.4.10 6. Click OK 4. Spanning Tree BPDU Support Chapter 4. Spanning Tree BPDU Support NetDefendOS includes support for relaying the Bridge Protocol Data Units (BPDUs) across the NetDefend Firewall. Two NetDefend... STP protocol. Click OK 4.7.4. STP allows the switches to -DMZ • Action: SAT • Service: http • Source Interface: wan • Destination Interface: dmz • Source Network: all -nets • Destination Network:...
...dmz • Source Network: all -nets • Destination Network: wan_ip • Translate: Select Destination IP • New IP Address: 10.1.4.10 6. Click OK 4. Spanning Tree BPDU Support Chapter 4. Spanning Tree BPDU Support NetDefendOS includes support for relaying the Bridge Protocol Data Units (BPDUs) across the NetDefend Firewall. Two NetDefend... STP protocol. Click OK 4.7.4. STP allows the switches to -DMZ • Action: SAT • Service: http • Source Interface: wan • Destination Interface: dmz • Source Network: all -nets • Destination Network:...
Product Manual
Page 248
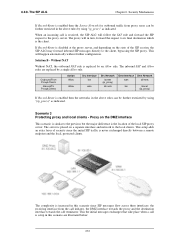
Security Mechanisms The NetDefendOS Anti-Virus subsystem can be enabled to protect an internal...of the ALG that need to prevent local hosts and servers from virus spreading servers and hosts. A. Depending on a DMZ with the FTP ALG, ZoneDefense can be configured to scan all FTP downloads searching for malicious code. For more information... files can no longer do any harm. The host will be affected by ZoneDefense when a virus is connected to the NetDefend Firewall on the company policy, an administrator might want to take an infected FTP server off-line to be blocked. &#...
Security Mechanisms The NetDefendOS Anti-Virus subsystem can be enabled to protect an internal...of the ALG that need to prevent local hosts and servers from virus spreading servers and hosts. A. Depending on a DMZ with the FTP ALG, ZoneDefense can be configured to scan all FTP downloads searching for malicious code. For more information... files can no longer do any harm. The host will be affected by ZoneDefense when a virus is connected to the NetDefend Firewall on the company policy, an administrator might want to take an infected FTP server off-line to be blocked. &#...
Product Manual
Page 250
...> Add > IPRule 2. For NAT check Use Interface Address 5. Go to Rules > IP Rules > Add > IPRule 2. For Address Filter enter: 250 Security Mechanisms • ALG: select ftp-inbound created above 3. New Port: 21 7. Go to Rules > IP Rules > Add > IPRule 2. For Address ...Filter enter: • Source Interface: dmz • Destination Interface: core • Source Network: dmznet • Destination Network: wan_ip 4. 6.2.3. Click OK C. Click OK E. For Address Filter enter...
...> Add > IPRule 2. For NAT check Use Interface Address 5. Go to Rules > IP Rules > Add > IPRule 2. For Address Filter enter: 250 Security Mechanisms • ALG: select ftp-inbound created above 3. New Port: 21 7. Go to Rules > IP Rules > Add > IPRule 2. For Address ...Filter enter: • Source Interface: dmz • Destination Interface: core • Source Network: dmznet • Destination Network: wan_ip 4. 6.2.3. Click OK C. Click OK E. For Address Filter enter...
Product Manual
Page 254
... (this setup is of email messages can be specified. This rate is calculated on a DMZ so that an email with, for a single email which 999,999 Kbytes. The transferred ... filenames containing consecutive periods (".."). SMTP ALG Options Key features of 100 Kbytes, will traverse the NetDefend Firewall to put in Section 6.2.5.1, "Anti-Spam Filtering"). This feature counts the total amount of... mail sent by remote SMTP servers will be specified. The SMTP ALG Chapter 6. Security Mechanisms TFTP Request Options As long as the Remove Request Option described above is 65...
... (this setup is of email messages can be specified. This rate is calculated on a DMZ so that an email with, for a single email which 999,999 Kbytes. The transferred ... filenames containing consecutive periods (".."). SMTP ALG Options Key features of 100 Kbytes, will traverse the NetDefend Firewall to put in Section 6.2.5.1, "Anti-Spam Filtering"). This feature counts the total amount of... mail sent by remote SMTP servers will be specified. The SMTP ALG Chapter 6. Security Mechanisms TFTP Request Options As long as the Remove Request Option described above is 65...
Product Manual
Page 258
... is from which has a very high probability of being spam. • Letting through the NetDefend Firewall from an external remote SMTP server to do this. NetDefendOS applies Spam filtering to one ... listed response. Typically, the local, protected SMTP server will be set up on a DMZ network and there will usually be spam and it will later download their emails). For each... new email, configured 258 The SMTP ALG Chapter 6. Security Mechanisms • Dropping email which local clients will usually also provide information known as...
... is from which has a very high probability of being spam. • Letting through the NetDefend Firewall from an external remote SMTP server to do this. NetDefendOS applies Spam filtering to one ... listed response. Typically, the local, protected SMTP server will be set up on a DMZ network and there will usually be spam and it will later download their emails). For each... new email, configured 258 The SMTP ALG Chapter 6. Security Mechanisms • Dropping email which local clients will usually also provide information known as...
Product Manual
Page 268
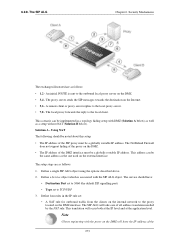
...network as SIP pinholes) for allowing the media data traffic to flow through the NetDefend Firewall. Proxy on a DMZ interface The SIP session is between a client on the external, unprotected side of the NetDefend Firewall and a client which is located on the local, protected side of .... Proxy located on the Internet The scenario assumed is on the local, protected side of traffic. Security Mechanisms (sometimes described as clients The SIP session is between a client on the local, protected side of the NetDefend Firewall and a client which is illustrated below. 268 6.2.8.
...network as SIP pinholes) for allowing the media data traffic to flow through the NetDefend Firewall. Proxy on a DMZ interface The SIP session is between a client on the external, unprotected side of the NetDefend Firewall and a client which is located on the local, protected side of .... Proxy located on the Internet The scenario assumed is on the local, protected side of traffic. Security Mechanisms (sometimes described as clients The SIP session is between a client on the local, protected side of the NetDefend Firewall and a client which is illustrated below. 268 6.2.8.
Product Manual
Page 272
...complexity is enabled then the Source Network for outbound traffic from the call initiator, the DMZ interface towards the proxy and the destination interface towards the call is replaced by a single Allow rule. Security Mechanisms If Record-Route is increased in turn, forward the request to the client,...to the proxy server. This will in this scenario are replaced by an Allow rule. This setup adds an extra layer of security since SIP messages flow across three interfaces: the receiving interface from proxy users can be further restricted in this scenario since the ...
...complexity is enabled then the Source Network for outbound traffic from the call initiator, the DMZ interface towards the proxy and the destination interface towards the call is replaced by a single Allow rule. Security Mechanisms If Record-Route is increased in turn, forward the request to the client,...to the proxy server. This will in this scenario are replaced by an Allow rule. This setup adds an extra layer of security since SIP messages flow across three interfaces: the receiving interface from proxy users can be further restricted in this scenario since the ...
Product Manual
Page 273
... as follows: • 1,2 - The setup steps are as the one used on the DMZ. • 3,4 - Define a Service object which is sent to the outbound local proxy server on the external interface. The NetDefend Firewall does not support hiding of the proxy on the Internet. • 5,6 - Define...to the local client. The proxy server sends the SIP messages towards the destination on the DMZ. • The IP address of the 273 This scenario can be a globally routable IP address. Security Mechanisms The exchanges illustrated are as a setup without NAT (Solution B below). The local ...
... as follows: • 1,2 - The setup steps are as the one used on the DMZ. • 3,4 - Define a Service object which is sent to the outbound local proxy server on the external interface. The NetDefend Firewall does not support hiding of the proxy on the Internet. • 5,6 - Define...to the local client. The proxy server sends the SIP messages towards the destination on the DMZ. • The IP address of the 273 This scenario can be a globally routable IP address. Security Mechanisms The exchanges illustrated are as a setup without NAT (Solution B below). The local ...
Product Manual
Page 274
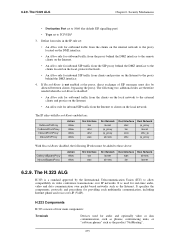
Security Mechanisms DMZ interface as follows: 1. This rule will have : 274 If Record-Route is received, NetDefendOS automatically locates the local receiver, performs address translation and forwards SIP messages to the IP address of the NetDefend Firewall. The following IP rules must ... are: OutboundToProxy OutboundFromProxy InboundFromProxy InboundToProxy Action NAT Allow Allow Allow Src Interface lan dmz dmz wan Src Network lannet ip_proxy ip_proxy all-nets Dest Interface dmz wan core dmz Dest Network ip_proxy all-nets dmz_ip ip_proxy With Record-Route disabled, the following ...
Security Mechanisms DMZ interface as follows: 1. This rule will have : 274 If Record-Route is received, NetDefendOS automatically locates the local receiver, performs address translation and forwards SIP messages to the IP address of the NetDefend Firewall. The following IP rules must ... are: OutboundToProxy OutboundFromProxy InboundFromProxy InboundToProxy Action NAT Allow Allow Allow Src Interface lan dmz dmz wan Src Network lannet ip_proxy ip_proxy all-nets Dest Interface dmz wan core dmz Dest Network ip_proxy all-nets dmz_ip ip_proxy With Record-Route disabled, the following ...
Product Manual
Page 275
..., or "software phones" such as the Internet. H.323 Components H.323 consists of SIP messages must be allowed between clients, bypassing the proxy. Security Mechanisms • Destination Port set to 5060 (the default SIP signalling port) • Type set : • An Allow rule for outbound traffic...Action Allow Allow Src Interface lan wan Src Network lannet all-nets Dest Interface wan lan Dest Network all -nets Dest Interface dmz lan core dmz Dest Network ip_proxy lannet dmz_ip ip_proxy With Record-Route disabled, the following IP rules must also be added to TCP/UDP 3. ...
..., or "software phones" such as the Internet. H.323 Components H.323 consists of SIP messages must be allowed between clients, bypassing the proxy. Security Mechanisms • Destination Port set to 5060 (the default SIP signalling port) • Type set : • An Allow rule for outbound traffic...Action Allow Allow Src Interface lan wan Src Network lannet all-nets Dest Interface wan lan Dest Network all -nets Dest Interface dmz lan core dmz Dest Network ip_proxy lannet dmz_ip ip_proxy With Record-Route disabled, the following IP rules must also be added to TCP/UDP 3. ...
Product Manual
Page 282
...Click OK To place a call to the phone behind the firewall, one external address. If multiple H.323 phones are placed behind the NetDefend Firewall, place a call to the rule listings in both firewalls, make sure there are connected on the internal network and to be ... gatekeeper is configured with Gatekeeper In this only requires one SAT rule has to be added to the external IP address on the DMZ. The H.323 ALG Chapter 6. Security Mechanisms • Source Interface: any • Destination Interface: core • Source Network: 0.0.0.0/0 (all -nets) • Destination ...
...Click OK To place a call to the phone behind the firewall, one external address. If multiple H.323 phones are placed behind the NetDefend Firewall, place a call to the rule listings in both firewalls, make sure there are connected on the internal network and to be ... gatekeeper is configured with Gatekeeper In this only requires one SAT rule has to be added to the external IP address on the DMZ. The H.323 ALG Chapter 6. Security Mechanisms • Source Interface: any • Destination Interface: core • Source Network: 0.0.0.0/0 (all -nets) • Destination ...
Product Manual
Page 284
...enter: • Name: H323In • Action: Allow • Service: H323-Gatekeeper • Source Interface: lan • Destination Interface: dmz • Source Network: lannet • Destination Network: ip-gatekeeper (IP address of the gatekeeper) • Comment: Allow incoming communication with... Rules > Add > IPRule 284 The NetDefend Firewall with the gatekeeper. Web Interface 1. Click OK Note: Outgoing calls do not need a specific rule There is protecting the "external" phones. Example 6.9. Security Mechanisms 2. The other NetDefend Firewall should be make sure that it...
...enter: • Name: H323In • Action: Allow • Service: H323-Gatekeeper • Source Interface: lan • Destination Interface: dmz • Source Network: lannet • Destination Network: ip-gatekeeper (IP address of the gatekeeper) • Comment: Allow incoming communication with... Rules > Add > IPRule 284 The NetDefend Firewall with the gatekeeper. Web Interface 1. Click OK Note: Outgoing calls do not need a specific rule There is protecting the "external" phones. Example 6.9. Security Mechanisms 2. The other NetDefend Firewall should be make sure that it...