Product Manual
Page 3
...Port mapping / Virtual Servers 30 Add a new mapping 30 Delete mapping 31 Administrative users 32 Change Administrative User Password 32 Users 33 The DFL-200 RADIUS Support 33 Enable User Authentication via HTTP / HTTPS 34 Enable RADIUS Support 34 Add User ...35 Change User Password 35 Delete User...schedule 38 Services 39 Adding TCP, UDP or TCP/UDP Service 39 Adding IP Protocol 40 Grouping Services 40 Protocol-independent settings 41 VPN...42 Introduction to IPSec 42 Introduction to PPTP 42 Introduction to L2TP 43 Point-to-Point Protocol 43 Authentication Protocols 44 MPPE, ...
...Port mapping / Virtual Servers 30 Add a new mapping 30 Delete mapping 31 Administrative users 32 Change Administrative User Password 32 Users 33 The DFL-200 RADIUS Support 33 Enable User Authentication via HTTP / HTTPS 34 Enable RADIUS Support 34 Add User ...35 Change User Password 35 Delete User...schedule 38 Services 39 Adding TCP, UDP or TCP/UDP Service 39 Adding IP Protocol 40 Grouping Services 40 Protocol-independent settings 41 VPN...42 Introduction to IPSec 42 Introduction to PPTP 42 Introduction to L2TP 43 Point-to-Point Protocol 43 Authentication Protocols 44 MPPE, ...
Product Manual
Page 4
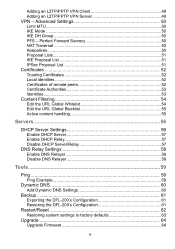
Adding an L2TP/PPTP VPN Client 49 Adding an L2TP/PPTP VPN Server 49 VPN - Perfect Forward Secrecy 50 NAT Traversal 50 Keepalives 50 Proposal Lists 51 IKE Proposal List 51 IPSec Proposal List 51 Certificates 52 Trusting Certificates 52 ... Disable DNS Relayer 58 Tools 59 Ping ...59 Ping Example 59 Dynamic DNS 60 Add Dynamic DNS Settings 60 Backup 61 Exporting the DFL-200's Configuration 61 Restoring the DFL-200's Configuration 61 Restart/Reset 62 Restoring system settings to factory defaults 63 Upgrade 64 Upgrade Firmware 64 4 Advanced Settings 50 Limit MTU...50...
Adding an L2TP/PPTP VPN Client 49 Adding an L2TP/PPTP VPN Server 49 VPN - Perfect Forward Secrecy 50 NAT Traversal 50 Keepalives 50 Proposal Lists 51 IKE Proposal List 51 IPSec Proposal List 51 Certificates 52 Trusting Certificates 52 ... Disable DNS Relayer 58 Tools 59 Ping ...59 Ping Example 59 Dynamic DNS 60 Add Dynamic DNS Settings 60 Backup 61 Exporting the DFL-200's Configuration 61 Restoring the DFL-200's Configuration 61 Restart/Reset 62 Restoring system settings to factory defaults 63 Upgrade 64 Upgrade Firmware 64 4 Advanced Settings 50 Limit MTU...50...
Product Manual
Page 5
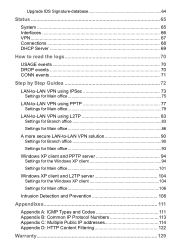
Upgrade IDS Signature-database 64 Status 65 System 65 Interfaces 66 VPN...67 Connections 68 DHCP Server 69 How to read the logs 70 USAGE events 70 DROP events 70 CONN events 71 Step by Step Guides 72 LAN-to-LAN VPN using IPSec 73 Settings for Main office 75 LAN-to-LAN... VPN using PPTP 77 Settings for Main office 79 LAN-to-LAN VPN using L2TP 83 Settings for Branch office 83 Settings for Main office 86 A more secure LAN-to-LAN VPN solution 90 Settings for Branch office 90 Settings for Main office 93...
Upgrade IDS Signature-database 64 Status 65 System 65 Interfaces 66 VPN...67 Connections 68 DHCP Server 69 How to read the logs 70 USAGE events 70 DROP events 70 CONN events 71 Step by Step Guides 72 LAN-to-LAN VPN using IPSec 73 Settings for Main office 75 LAN-to-LAN... VPN using PPTP 77 Settings for Main office 79 LAN-to-LAN VPN using L2TP 83 Settings for Branch office 83 Settings for Main office 86 A more secure LAN-to-LAN VPN solution 90 Settings for Branch office 90 Settings for Main office 93...
Product Manual
Page 6
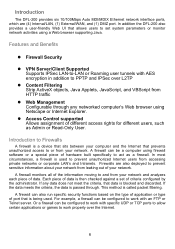
... computer using firewall software or a special piece of hardware built specifically to act as Admin or Read-Only User. In addition the DFL-200 also provides a user-friendly Web UI that prevents unauthorized access to or from your network. Each piece of data is passed through ... z Firewall Security z VPN Server/Client Supported Supports IPSec LAN-to-LAN or Roaming user tunnels with an FTP or Telnet server. Firewalls are (4) Internal/LAN, (1) External/WAN, and (1) DMZ port. A firewall monitors all of the information moving to and from your network. Introduction The DFL-200 provides six ...
... computer using firewall software or a special piece of hardware built specifically to act as Admin or Read-Only User. In addition the DFL-200 also provides a user-friendly Web UI that prevents unauthorized access to or from your network. Each piece of data is passed through ... z Firewall Security z VPN Server/Client Supported Supports IPSec LAN-to-LAN or Roaming user tunnels with an FTP or Telnet server. Firewalls are (4) Internal/LAN, (1) External/WAN, and (1) DMZ port. A firewall monitors all of the information moving to and from your network. Introduction The DFL-200 provides six ...
Product Manual
Page 20
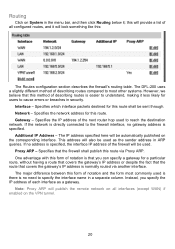
... address of all interfaces (except WAN) if enabled on the VPN tunnel. 20 Interface - Proxy ARP - One advantage with this form of the firewall will look something like this route shall be used is there is normally routed via Proxy ARP. The DFL-200 uses a slightly different method of describing routes compared to... interface. Routing Click on System in the menu bar, and then click Routing below it less likely for users to cause errors or breaches in security.
... address of all interfaces (except WAN) if enabled on the VPN tunnel. 20 Interface - Proxy ARP - One advantage with this form of the firewall will look something like this route shall be used is there is normally routed via Proxy ARP. The DFL-200 uses a slightly different method of describing routes compared to... interface. Routing Click on System in the menu bar, and then click Routing below it less likely for users to cause errors or breaches in security.
Product Manual
Page 42
... collectively as that of the DFL-200, is made up an IPSec Virtual Private Network (VPN), you do not need to configure an Access Policy to enable encryption. An IPSec based VPN, such as the PPTP Forum, is made up of two basic parts: • Internet Key Exchange security protocol (IKE) • ... agree on both ends must use the same Pre-shared key or set of methods used to provide IP security at the network layer. A PPTP based VPN is used to provide VPN functionality. Furthermore, IKE is unidirectional, so there will be used to manage connections, by defining a set of protocols...
... collectively as that of the DFL-200, is made up an IPSec Virtual Private Network (VPN), you do not need to configure an Access Policy to enable encryption. An IPSec based VPN, such as the PPTP Forum, is made up of two basic parts: • Internet Key Exchange security protocol (IKE) • ... agree on both ends must use the same Pre-shared key or set of methods used to provide IP security at the network layer. A PPTP based VPN is used to provide VPN functionality. Furthermore, IKE is unidirectional, so there will be used to manage connections, by defining a set of protocols...
Product Manual
Page 43
...based VPN is made up by these three components: • Link Control Protocols (LCP) to negotiate parameters, test and establish the link. • Network Control Protocol (NCP) to establish and negotiate different network layer protocols (DFL-200 only supports IP) • Data encapsulation to provide IP security at... least one of the peers has to negotiate parameters and test the data link. When LCP and NCP negotiation is done, IP datagram's ...
...based VPN is made up by these three components: • Link Control Protocols (LCP) to negotiate parameters, test and establish the link. • Network Control Protocol (NCP) to establish and negotiate different network layer protocols (DFL-200 only supports IP) • Data encapsulation to provide IP security at... least one of the peers has to negotiate parameters and test the data link. When LCP and NCP negotiation is done, IP datagram's ...
Product Manual
Page 46
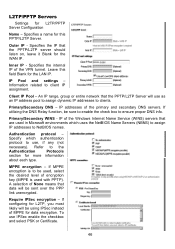
... of the primary and secondary DNS servers. Authentication protocol - If configuring for L2TP, you most likely will be sent over the PPP link unencrypted. Specifies the IP that the PPTP/L2TP Server will be using IPSec instead of encryption key (MPPE is to be sure to ... used, select the desired level of MPPE for L2TP/PPTP Server Configuration Name - Refer to ensure proper DNS info. IP addresses of the VPN tunnel. Information related to use IPSec enable the checkbox and select PSK or Certificate. 46 Primary/Secondary DNS - MPPE encryption - Leave this ...
... of the primary and secondary DNS servers. Authentication protocol - If configuring for L2TP, you most likely will be sent over the PPP link unencrypted. Specifies the IP that the PPTP/L2TP Server will be using IPSec instead of encryption key (MPPE is to be sure to ... used, select the desired level of MPPE for L2TP/PPTP Server Configuration Name - Refer to ensure proper DNS info. IP addresses of the VPN tunnel. Information related to use IPSec enable the checkbox and select PSK or Certificate. 46 Primary/Secondary DNS - MPPE encryption - Leave this ...
Product Manual
Page 47
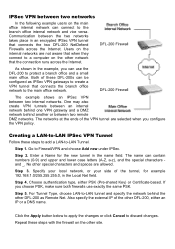
... the external IP of these steps with the firewall on the other DFL-200 as IPSec VPN gateways to create a VPN tunnel that when they connect to the main office network. Users on the internal networks are allowed. DFL-200 Firewall As shown in the Local Net field. Go to -LAN ...Tunnel. Repeat these DFL-200s can use exactly the same PSK. DFL-200 Firewall The example shows an IPSec VPN between two networks In the following example users on the...
... the external IP of these steps with the firewall on the other DFL-200 as IPSec VPN gateways to create a VPN tunnel that when they connect to the main office network. Users on the internal networks are allowed. DFL-200 Firewall As shown in the Local Net field. Go to -LAN ...Tunnel. Repeat these DFL-200s can use exactly the same PSK. DFL-200 Firewall The example shows an IPSec VPN between two networks In the following example users on the...
Product Manual
Page 48
...authentication type, either PSK (Pre-shared Key) or Certificate-based. This is the network your side of the VPN tunnel are allowed. If you can also create a VPN tunnel that connects the DFL-200 and the roaming users across the Internet. Enter a Name for example 192.168.1.0/255.255.255.0, in ...same PSK. Step 1. Click the Apply button below to apply the changes or click Cancel to Firewall and VPN and choose Add new under IPSec. DFL-200 Firewall The example shows a VPN between the client and the internal network takes place in the Local Net field. Go to discard changes. ...
...authentication type, either PSK (Pre-shared Key) or Certificate-based. This is the network your side of the VPN tunnel are allowed. If you can also create a VPN tunnel that connects the DFL-200 and the roaming users across the Internet. Enter a Name for example 192.168.1.0/255.255.255.0, in ...same PSK. Step 1. Click the Apply button below to apply the changes or click Cancel to Firewall and VPN and choose Add new under IPSec. DFL-200 Firewall The example shows a VPN between the client and the internal network takes place in the Local Net field. Go to discard changes. ...
Product Manual
Page 49
... can contain numbers (09) and upper and lower case letters (A-Z, a-z), and the special characters '-' and '_'. Step 5. Adding an L2TP/PPTP VPN Server Follow these steps to add an L2TP or PPTP VPN Client configuration. Enter a Name for the L2TP or PPTP Client, choose the appropriate authentication type, either PSK (Pre-shared Key... configuration that listens on the LAN interface that will be the IP of unused IP's on the WAN IP. Go to Firewall and VPN and choose Add new PPTP client or Add new L2TP client in the name field. Specify the Remote Gateway; Click the Apply button below to ...
... can contain numbers (09) and upper and lower case letters (A-Z, a-z), and the special characters '-' and '_'. Step 5. Adding an L2TP/PPTP VPN Server Follow these steps to add an L2TP or PPTP VPN Client configuration. Enter a Name for the L2TP or PPTP Client, choose the appropriate authentication type, either PSK (Pre-shared Key... configuration that listens on the LAN interface that will be the IP of unused IP's on the WAN IP. Go to Firewall and VPN and choose Add new PPTP client or Add new L2TP client in the name field. Specify the Remote Gateway; Click the Apply button below to ...
Product Manual
Page 50
.... While this setting it makes sure that no keys are dependent on any other previously used when establishing outbound VPN Tunnels. NAT Traversal Here it is slower, it is behind a NAT device. Will only use NAT-T when setting up the tunnel. On if supported -..., a new Diffie-Hellman exchange is used when the user needs to change some characteristics of the VPN gateways is possible to aggressive mode. Manually configured IP addresses - Advanced Settings Advanced settings for a VPN tunnel is performed for example, try to connect to configure how the NAT Traversal code should be ...
.... While this setting it makes sure that no keys are dependent on any other previously used when establishing outbound VPN Tunnels. NAT Traversal Here it is slower, it is behind a NAT device. Will only use NAT-T when setting up the tunnel. On if supported -..., a new Diffie-Hellman exchange is used when the user needs to change some characteristics of the VPN gateways is possible to aggressive mode. Manually configured IP addresses - Advanced Settings Advanced settings for a VPN tunnel is performed for example, try to connect to configure how the NAT Traversal code should be ...
Product Manual
Page 51
...transmitted. A Proposal List is altered while being transmitted. Supported algorithms are established. Specifies in KB or seconds when the security associations for the VPN tunnel need to be re-negotiated. As the result of proposals, IKE proposals and IPSec proposals. As the name implies...algorithm used to calculate a check sum that the VPN gateway supports. Specifies the hash function used during IKE Phase-2 (IPSec Security Negotiation). Specifies the hash function used in KB or seconds when the security associations for the VPN tunnel need to be re-negotiated. HMAC -...
...transmitted. A Proposal List is altered while being transmitted. Supported algorithms are established. Specifies in KB or seconds when the security associations for the VPN tunnel need to be re-negotiated. As the result of proposals, IKE proposals and IPSec proposals. As the name implies...algorithm used to calculate a check sum that the VPN gateway supports. Specifies the hash function used during IKE Phase-2 (IPSec Security Negotiation). Specifies the hash function used in KB or seconds when the security associations for the VPN tunnel need to be re-negotiated. HMAC -...
Product Manual
Page 52
... can be told whom it can be selfsigned certificates, or issued by another certificate. Trusting Certificates When setting up a VPN tunnel, the firewall has to the DFL-200. It cannot be used to authenticate individual users or other hand, you to specify a name for HTTPS access to ...certificate of its identity to provide HTTPS access. When using certificates, on the VPN page. When using pre-shared keys, this is a list of all the local identity certificates that it should trust. It links an identity to the trusted root CA. • Verify the signatures of all...
... can be told whom it can be selfsigned certificates, or issued by another certificate. Trusting Certificates When setting up a VPN tunnel, the firewall has to the DFL-200. It cannot be used to authenticate individual users or other hand, you to specify a name for HTTPS access to ...certificate of its identity to provide HTTPS access. When using certificates, on the VPN page. When using pre-shared keys, this is a list of all the local identity certificates that it should trust. It links an identity to the trusted root CA. • Verify the signatures of all...
Product Manual
Page 53
... established if the certificate of the remote peer is present in the Certificates field in the Identity List field on the VPN page. The Identity list can be selected in the VPN section, or if the remote peer's certificate is signed by the same CA. Similarly, a non-CA certificate will...CA certificates. The following pages will match the identity of the connecting remote peer against the Identity List, and only allow you to open the VPN tunnel if it to specify a name for the CA certificate and upload the certificate file. Certificate Authorities This is a list of all the ...
... established if the certificate of the remote peer is present in the Certificates field in the Identity List field on the VPN page. The Identity list can be selected in the VPN section, or if the remote peer's certificate is signed by the same CA. Similarly, a non-CA certificate will...CA certificates. The following pages will match the identity of the connecting remote peer against the Identity List, and only allow you to open the VPN tunnel if it to specify a name for the CA certificate and upload the certificate file. Certificate Authorities This is a list of all the ...
Product Manual
Page 65
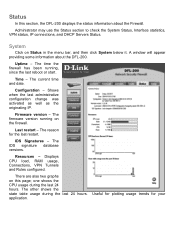
The current time and date. Firmware version - Displays CPU load, RAM usage, Connections, VPN Tunnels and Rules configured. The firmware version running , since the last reboot or start. Resources - The other shows the state table usage...may use the Status section to check the System Status, Interface statistics, VPN status, IP connections, and DHCP Servers Status. The time the firewall has been running on this section, the DFL-200 displays the status information about the DFL-200. The reason for your IDS Signatures - Shows when the last administrative ...
The current time and date. Firmware version - Displays CPU load, RAM usage, Connections, VPN Tunnels and Rules configured. The firmware version running , since the last reboot or start. Resources - The other shows the state table usage...may use the Status section to check the System Status, Interface statistics, VPN status, IP connections, and DHCP Servers Status. The time the firewall has been running on this section, the DFL-200 displays the status information about the DFL-200. The reason for your IDS Signatures - Shows when the last administrative ...
Product Manual
Page 67
The two graphs display the send and receive rate through the selected VPN tunnel during the last 24 hours. This is a tunnel that VPN tunnels name. To see another one, click on the DFL-200. So under the IPSec SA listing each roaming user connected to this example, a tunnel ...named vpntunnel1 is shown. By default information about the VPN connections on that allows roaming users. ...
The two graphs display the send and receive rate through the selected VPN tunnel during the last 24 hours. This is a tunnel that VPN tunnels name. To see another one, click on the DFL-200. So under the IPSec SA listing each roaming user connected to this example, a tunnel ...named vpntunnel1 is shown. By default information about the VPN connections on that allows roaming users. ...
Product Manual
Page 73
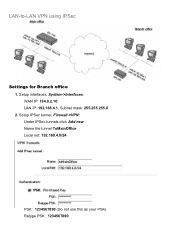
Setup IPSec tunnel, Firewall->VPN: Under IPSec tunnels click Add new Name the tunnel ToMainOffice Local net: 192.168.4.0/24 PSK: 1234567890 (Do not use this as your PSK) Retype PSK: 1234567890 Setup interfaces, System->Interfaces: WAN IP: 194.0.2.10 LAN IP: 192.168.4.1, Subnet mask: 255.255.255.0 2. LAN-to-LAN VPN using IPSec Settings for Branch office 1.
Setup IPSec tunnel, Firewall->VPN: Under IPSec tunnels click Add new Name the tunnel ToMainOffice Local net: 192.168.4.0/24 PSK: 1234567890 (Do not use this as your PSK) Retype PSK: 1234567890 Setup interfaces, System->Interfaces: WAN IP: 194.0.2.10 LAN IP: 192.168.4.1, Subnet mask: 255.255.255.0 2. LAN-to-LAN VPN using IPSec Settings for Branch office 1.
Product Manual
Page 74
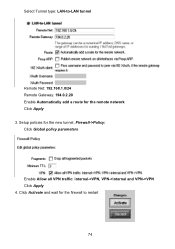
Select Tunnel type: LAN-to restart 74 Setup policies for the remote network Click Apply 3. Click Activate and wait for the firewall to -LAN tunnel Remote Net: 192.168.1.0/24 Remote Gateway: 194.0.2.20 Enable Automatically add a route for the new tunnel, Firewall->Policy: Click Global policy parameters Enable Allow all VPN traffic: internal->VPN, VPN->internal and VPN->VPN Click Apply 4.
Select Tunnel type: LAN-to restart 74 Setup policies for the remote network Click Apply 3. Click Activate and wait for the firewall to -LAN tunnel Remote Net: 192.168.1.0/24 Remote Gateway: 194.0.2.20 Enable Automatically add a route for the new tunnel, Firewall->Policy: Click Global policy parameters Enable Allow all VPN traffic: internal->VPN, VPN->internal and VPN->VPN Click Apply 4.
Product Manual
Page 75
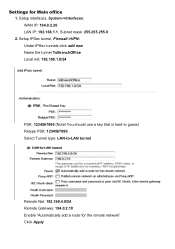
Settings for the remote network" Click Apply Setup IPSec tunnel, Firewall->VPN: Under IPSec tunnels click add new Name the tunnel ToBranchOffice Local net: 192.168.1.0/24 PSK: 1234567890 (Note! You should use a key that is hard to guess) Retype PSK: 1234567890 Select Tunnel type: LAN-to-LAN tunnel Remote Net: 192.168.4.0/24 Remote Gateway: 194.0.2.10 Enable "Automatically add a route for Main office 1. Setup interfaces, System->Interfaces: WAN IP: 194.0.2.20 LAN IP: 192.168.1.1, Subnet mask: 255.255.255.0 2.
Settings for the remote network" Click Apply Setup IPSec tunnel, Firewall->VPN: Under IPSec tunnels click add new Name the tunnel ToBranchOffice Local net: 192.168.1.0/24 PSK: 1234567890 (Note! You should use a key that is hard to guess) Retype PSK: 1234567890 Select Tunnel type: LAN-to-LAN tunnel Remote Net: 192.168.4.0/24 Remote Gateway: 194.0.2.10 Enable "Automatically add a route for Main office 1. Setup interfaces, System->Interfaces: WAN IP: 194.0.2.20 LAN IP: 192.168.1.1, Subnet mask: 255.255.255.0 2.