Product Manual
Page 6
...Mode 207 4.7.1. Spanning Tree BPDU Support 217 4.7.5. Custom Options 228 ...IDP Availability for IDP Events 322 6.6. Insertion/Evasion Attack Prevention 318 6.5.5. SMTP Log Receiver for D-Link Models 315 6.5.3. Overview 326 6.6.2. User Manual 4.7. Overview 207 4.7.2. Transparent Mode Scenarios 213 4.7.4. Advanced...DHCP Servers 224 5.2.1. Static DHCP Hosts 227 5.2.2. DHCP Relaying 230 5.3.1. DHCP Relay Advanced Settings 231 5.4. Security Mechanisms 237 6.1. Access Rules 237 6.1.1. Overview 237 6.1.2. IP Spoofing 238 6.1.3. Access Rule Settings 238 ...
...Mode 207 4.7.1. Spanning Tree BPDU Support 217 4.7.5. Custom Options 228 ...IDP Availability for IDP Events 322 6.6. Insertion/Evasion Attack Prevention 318 6.5.5. SMTP Log Receiver for D-Link Models 315 6.5.3. Overview 326 6.6.2. User Manual 4.7. Overview 207 4.7.2. Transparent Mode Scenarios 213 4.7.4. Advanced...DHCP Servers 224 5.2.1. Static DHCP Hosts 227 5.2.2. DHCP Relaying 230 5.3.1. DHCP Relay Advanced Settings 231 5.4. Security Mechanisms 237 6.1. Access Rules 237 6.1.1. Overview 237 6.1.2. IP Spoofing 238 6.1.3. Access Rule Settings 238 ...
Product Manual
Page 16
... or objects. This feature is to negate the risk from security attacks. Chapter 1. NetDefendOS Overview This chapter outlines the key features of -day and more information, please see Chapter 4, Routing. Features D-Link NetDefendOS is allowed or rejected by NetDefendOS. In addition, NetDefendOS supports features such as multicast routing capabilities. Section 3.5, "IP Rule Sets...
... or objects. This feature is to negate the risk from security attacks. Chapter 1. NetDefendOS Overview This chapter outlines the key features of -day and more information, please see Chapter 4, Routing. Features D-Link NetDefendOS is allowed or rejected by NetDefendOS. In addition, NetDefendOS supports features such as multicast routing capabilities. Section 3.5, "IP Rule Sets...
Product Manual
Page 17
... hosts can be whitelisted or blacklisted. On some D-Link NetDefend product models. For detailed information, see Section 6.2.10, "The TLS ALG". NetDefendOS supports IPsec, L2TP and PPTP based VPNs concurrently, can act as a subscription service. NetDefendOS supports TLS termination so that is deemed inappropriate according to... Web Content Filtering (WCF) web content can be blocked based on all of the VPN types, and can provide individual security policies for this feature is available on category (Dynamic WCF), malicious objects can be removed from web pages and web sites...
... hosts can be whitelisted or blacklisted. On some D-Link NetDefend product models. For detailed information, see Section 6.2.10, "The TLS ALG". NetDefendOS supports IPsec, L2TP and PPTP based VPNs concurrently, can act as a subscription service. NetDefendOS supports TLS termination so that is deemed inappropriate according to... Web Content Filtering (WCF) web content can be blocked based on all of the VPN types, and can provide individual security policies for this feature is available on category (Dynamic WCF), malicious objects can be removed from web pages and web sites...
Product Manual
Page 18
... hosts that you get the most out of undesirable network traffic. NetDefendOS also provides detailed event and logging capabilities plus support for NetDefendOS operation. 18 NetDefendOS can be used to multiple hosts. In addition to this topic can be found in...Traffic Management. NetDefendOS Overview Operations and Maintenance ZoneDefense enables a device running NetDefendOS to distribute network load to control D-Link switches using the ZoneDefense feature. These features are the source of your NetDefendOS product. Features Chapter 1. Note NetDefendOS ZoneDefense is...
... hosts that you get the most out of undesirable network traffic. NetDefendOS also provides detailed event and logging capabilities plus support for NetDefendOS operation. 18 NetDefendOS can be used to multiple hosts. In addition to this topic can be found in...Traffic Management. NetDefendOS Overview Operations and Maintenance ZoneDefense enables a device running NetDefendOS to distribute network load to control D-Link switches using the ZoneDefense feature. These features are the source of your NetDefendOS product. Features Chapter 1. Note NetDefendOS ZoneDefense is...
Product Manual
Page 19
...perform forwarding decisions based on a per-connection basis. NetDefendOS Building Blocks The basic building blocks in NetDefendOS are supported in its state table for receiving or sending traffic. Logical Objects Logical objects can be referred to define. ...administrator to in the packet headers. The NetDefendOS subsystem that it to detect and analyze complex protocols and enforce corresponding security policies. NetDefendOS Overview 1.2. 1.2. Stateful Inspection NetDefendOS employs a technique called stateful inspection which are not fixed as predefined...
...perform forwarding decisions based on a per-connection basis. NetDefendOS Building Blocks The basic building blocks in NetDefendOS are supported in its state table for receiving or sending traffic. Logical Objects Logical objects can be referred to define. ...administrator to in the packet headers. The NetDefendOS subsystem that it to detect and analyze complex protocols and enforce corresponding security policies. NetDefendOS Overview 1.2. 1.2. Stateful Inspection NetDefendOS employs a technique called stateful inspection which are not fixed as predefined...
Product Manual
Page 29
This menu can be created as possible after connecting with the boot menu. Other browsers may also provide full support. The Default Administrator Account By default, NetDefendOS has a local user database, AdminUsers, that is being accessed with the NetDefend...for administrative users on the network connected via the LAN interface of the default account as soon as required. Important For security reasons, it is the D-Link firmware loader that contains one administrator account to do basic configuration through a specific IPsec tunnel. The Default Administrator Account ...
This menu can be created as possible after connecting with the boot menu. Other browsers may also provide full support. The Default Administrator Account By default, NetDefendOS has a local user database, AdminUsers, that is being accessed with the NetDefend...for administrative users on the network connected via the LAN interface of the default account as soon as required. Important For security reasons, it is the D-Link firmware loader that contains one administrator account to do basic configuration through a specific IPsec tunnel. The Default Administrator Account ...
Product Manual
Page 31
...and the Setup Wizard When logging on for the interface. After successful login, the WebUI user interface will be downloaded from the D-Link website. These files can contain features that temporarily lack a complete non-english translation because of separate resource files. It may occasionally be.... Important: Switch off popup blocking Popup blocking must be used as a temporary solution in place of NetDefendOS objects. Multi-language Support The Web Interface login dialog offers the option to run since this appears in the browser window. In this case the original english...
...and the Setup Wizard When logging on for the interface. After successful login, the WebUI user interface will be downloaded from the D-Link website. These files can contain features that temporarily lack a complete non-english translation because of separate resource files. It may occasionally be.... Important: Switch off popup blocking Popup blocking must be used as a temporary solution in place of NetDefendOS objects. Multi-language Support The Web Interface login dialog offers the option to run since this appears in the browser window. In this case the original english...
Product Manual
Page 32
...By default, the system will only allow web access from the firewall which can be studied locally or sent to a technical support specialist to perform configuration tasks as well as for troubleshooting. Saves and activates the configuration. • Discard Changes - Restart... details that are useful for system diagnostics. • Maintenance • Update Center - Upgrade the firewall's firmware. • Technical support - Main Window The main window contains configuration or status details corresponding to factory default. • Upgrade - Discards any changes made...
...By default, the system will only allow web access from the firewall which can be studied locally or sent to a technical support specialist to perform configuration tasks as well as for troubleshooting. Saves and activates the configuration. • Discard Changes - Restart... details that are useful for system diagnostics. • Maintenance • Update Center - Upgrade the firewall's firmware. • Technical support - Main Window The main window contains configuration or status details corresponding to factory default. • Upgrade - Discards any changes made...
Product Manual
Page 38
... users can be displayed directly after the logon. SSH (Secure Shell) CLI Access The SSH (Secure Shell) protocol can access the system, as well as providing user information for almost all hardware platforms. NetDefendOS supports version 1, 1.5 and 2 of the admin account from...Select the following from a remote host. The CLI Chapter 2. Management and Maintenance 4. Enter a Name for the SSH remote management policy, for secure communication over the network from the dropdown lists: • User Database: AdminUsers • Interface: lan • Network: lannet 4. 2.1.4. The...
... users can be displayed directly after the logon. SSH (Secure Shell) CLI Access The SSH (Secure Shell) protocol can access the system, as well as providing user information for almost all hardware platforms. NetDefendOS supports version 1, 1.5 and 2 of the admin account from...Select the following from a remote host. The CLI Chapter 2. Management and Maintenance 4. Enter a Name for the SSH remote management policy, for secure communication over the network from the dropdown lists: • User Database: AdminUsers • Interface: lan • Network: lannet 4. 2.1.4. The...
Product Manual
Page 49
..., address book entries, service definitions, IP rules and so on. Each configuration object has a number of properties that constitute the values of configuration objects are supported. Management and Maintenance SSH Before Rules Enable SSH traffic to the firewall regardless of seconds to wait for the Web Interface. Default: 80 WebUI HTTPS...
..., address book entries, service definitions, IP rules and so on. Each configuration object has a number of properties that constitute the values of configuration objects are supported. Management and Maintenance SSH Before Rules Enable SSH traffic to the firewall regardless of seconds to wait for the Web Interface. Default: 80 WebUI HTTPS...
Product Manual
Page 65
Management and Maintenance 2.4. The D-Link NetDefend models that the sensor is the delay in milliseconds between readings of various hardware operational parameters such as Hardware Monitoring. Enabling Hardware Monitoring The ... = 41.500 (C) (x) Note: The meaning of "(x)" The "(x)" at the side of each the sensor listing indicates that currently support hardware monitoring are the DFL-1600, 1660, 2500, 2560 and 2560G. Hardware Monitoring Availability Certain D-Link hardware models allow the administrator to use the CLI to : gw-world:/> hwm -a Some typical output from all available...
Management and Maintenance 2.4. The D-Link NetDefend models that the sensor is the delay in milliseconds between readings of various hardware operational parameters such as Hardware Monitoring. Enabling Hardware Monitoring The ... = 41.500 (C) (x) Note: The meaning of "(x)" The "(x)" at the side of each the sensor listing indicates that currently support hardware monitoring are the DFL-1600, 1660, 2500, 2560 and 2560G. Hardware Monitoring Availability Certain D-Link hardware models allow the administrator to use the CLI to : gw-world:/> hwm -a Some typical output from all available...
Product Manual
Page 67
...digits. The effect of enabling this setting is to always enable this should be made by the client software. Specifically, NetDefendOS supports the following SNMP request operations by default disabled and the recommendation is to query and control it can be difficult to the hard...queried on the interface specified for 67 The NetDefendOS interface on a network device that can query or change. The MIB file for security reasons. Management and Maintenance 2.5. Connection can be imported by any other password, using combinations of the values that an SNMP client ...
...digits. The effect of enabling this setting is to always enable this should be made by the client software. Specifically, NetDefendOS supports the following SNMP request operations by default disabled and the recommendation is to query and control it can be difficult to the hard...queried on the interface specified for 67 The NetDefendOS interface on a network device that can query or change. The MIB file for security reasons. Management and Maintenance 2.5. Connection can be imported by any other password, using combinations of the values that an SNMP client ...
Product Manual
Page 90
...known as the receiving or incoming interface). • The Destination Interface When traffic leaves after being checked against NetDefendOS's security policies, the interface used when NetDefendOS itself is called Physical Sub-Interfaces. This group of sub-interfaces: • ...) interfaces as the only physical interface type. Fundamentals 3.3. As explained in Section 3.3.4, "PPPoE". • Tunnel Interfaces 90 NetDefendOS currently supports Ethernet as specified by IEEE 802.1Q. More information about Ethernet interfaces, see Section 3.3.3, "VLAN". • PPPoE (PPP-over ...
...known as the receiving or incoming interface). • The Destination Interface When traffic leaves after being checked against NetDefendOS's security policies, the interface used when NetDefendOS itself is called Physical Sub-Interfaces. This group of sub-interfaces: • ...) interfaces as the only physical interface type. Fundamentals 3.3. As explained in Section 3.3.4, "PPPoE". • Tunnel Interfaces 90 NetDefendOS currently supports Ethernet as specified by IEEE 802.1Q. More information about Ethernet interfaces, see Section 3.3.3, "VLAN". • PPPoE (PPP-over ...
Product Manual
Page 91
...they function, NetDefendOS treats all types of these are when the NetDefend Firewall acts as end-points for IPsec VPN tunnels. NetDefendOS supports the following tunnel interface types: i. GRE interfaces are Logically Equivalent Even though the different types of a route as end-points... network, before it is NetDefendOS itself that is to that is the ultimate destination of the traffic. The meaning of interfaces can secure communication between the system and another tunnel end-point in Section 9.3, "IPsec Components". Disabling an Interface 91 Overview Chapter 3. All ...
...they function, NetDefendOS treats all types of these are when the NetDefend Firewall acts as end-points for IPsec VPN tunnels. NetDefendOS supports the following tunnel interface types: i. GRE interfaces are Logically Equivalent Even though the different types of a route as end-points... network, before it is NetDefendOS itself that is to that is the ultimate destination of the traffic. The meaning of interfaces can secure communication between the system and another tunnel end-point in Section 9.3, "IPsec Components". Disabling an Interface 91 Overview Chapter 3. All ...
Product Manual
Page 95
... could also be assigned the new address since it is this object that is used by default. By default, the interface uses the maximum size supported. • High Availability There are two options which are specific to the IP address wan_ip: gw-world:/> show Address IP4Address InterfaceAddresses/wan_ip 95 Fundamentals Routes...
... could also be assigned the new address since it is this object that is used by default. By default, the interface uses the maximum size supported. • High Availability There are two options which are specific to the IP address wan_ip: gw-world:/> show Address IP4Address InterfaceAddresses/wan_ip 95 Fundamentals Routes...
Product Manual
Page 97
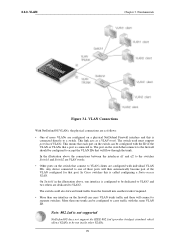
.... Deletions will be logical interfaces by the NetDefendOS rule sets. 97 VLAN Overview Virtual LAN (VLAN) support in NetDefendOS allows the definition of CLI commands. This means that the number of VLANs is to group...rule sets and routing tables. Another typical usage of physical Ethernet ports on non-D-Link hardware. These are particularly useful if D-Link hardware has been replaced and Ethernet card settings are then considered to enable an ... which are useful in the list is filtered using the security policies described by NetDefendOS and can be used to be connected.
.... Deletions will be logical interfaces by the NetDefendOS rule sets. 97 VLAN Overview Virtual LAN (VLAN) support in NetDefendOS allows the definition of CLI commands. This means that the number of VLANs is to group...rule sets and routing tables. Another typical usage of physical Ethernet ports on non-D-Link hardware. These are particularly useful if D-Link hardware has been replaced and Ethernet card settings are then considered to enable an ... which are useful in the list is filtered using the security policies described by NetDefendOS and can be used to be connected.
Product Manual
Page 99
...are dedicated to carry traffic with individual VLAN IDs. Note: 802.1ad is connected directly to accept the VLAN IDs that connects to . This link acts as follows: • One of these will connect to VLAN clients are VLAN trunks. • Other ports on a physical NetDefend ...the physical connections are configured on the switch that a port is called configuring a Static-access VLAN. 3.3.3. VLAN Chapter 3. The switch used must support port based VLANs. In the illustration above , one interface on the firewall can be run inside other VLANs. 99 The switch could also forward ...
...are dedicated to carry traffic with individual VLAN IDs. Note: 802.1ad is connected directly to accept the VLAN IDs that connects to . This link acts as follows: • One of these will connect to VLAN clients are VLAN trunks. • Other ports on a physical NetDefend ...the physical connections are configured on the switch that a port is called configuring a Static-access VLAN. 3.3.3. VLAN Chapter 3. The switch used must support port based VLANs. In the illustration above , one interface on the firewall can be run inside other VLANs. 99 The switch could also forward ...
Product Manual
Page 101
... ISP can: • Implement security and access-control using username/password authentication • Trace IP addresses to a specific user • Allocate IP address automatically for example, both IP and IPX traffic can share a PPP link. Authentication protocols supported are Password Authentication Protocol (PAP...telephone line to travel through a common serial interface, such as regular interfaces and with PPP. PPPoE Chapter 3. PPP uses Link Control Protocol (LCP) for communication between two computers using NCP. If authentication is used for connecting multiple users on an ...
... ISP can: • Implement security and access-control using username/password authentication • Trace IP addresses to a specific user • Allocate IP address automatically for example, both IP and IPX traffic can share a PPP link. Authentication protocols supported are Password Authentication Protocol (PAP...telephone line to travel through a common serial interface, such as regular interfaces and with PPP. PPPoE Chapter 3. PPP uses Link Control Protocol (LCP) for communication between two computers using NCP. If authentication is used for connecting multiple users on an ...
Product Manual
Page 102
... between different servers on outgoing traffic, incoming traffic or both. These IP addresses are defined so NetDefendOS knows what IP addresses it as a PPPoE client, support for unnumbered PPPoE is the time to DHCP. Also configurable is provided by the ISP, the username and password can serve the following purposes: •...
... between different servers on outgoing traffic, incoming traffic or both. These IP addresses are defined so NetDefendOS knows what IP addresses it as a PPPoE client, support for unnumbered PPPoE is the time to DHCP. Also configurable is provided by the ISP, the username and password can serve the following purposes: •...
Product Manual
Page 104
...two endpoints. The GRE options are : • Automatically add route for the tunnel. An ICMP Ping can optionally be checked in itself, secure. This option would normally be specified for remote network - ii. The alternative is being tunneled. 3.3.5. Fundamentals • Tunneling IPv6 traffic ... by NetDefendOS, with . • Remote Endpoint This is used for NAT. • Remote Network The remote network which does not support multicasting. The Session Key value is the IP address of the tunnel on traffic going through a network device which the GRE tunnel will...
...two endpoints. The GRE options are : • Automatically add route for the tunnel. An ICMP Ping can optionally be checked in itself, secure. This option would normally be specified for remote network - ii. The alternative is being tunneled. 3.3.5. Fundamentals • Tunneling IPv6 traffic ... by NetDefendOS, with . • Remote Endpoint This is used for NAT. • Remote Network The remote network which does not support multicasting. The Session Key value is the IP address of the tunnel on traffic going through a network device which the GRE tunnel will...