End User License Agreement
Page 2
... forth elsewhere in the form of a conflict between such terms, the other form, may not rent, lease or lend the Software Product or use technical information you fail to all component parts, media, printed materials, this limitation or it is effective unless terminated or rejected. This EULA is expressly provided for...
... forth elsewhere in the form of a conflict between such terms, the other form, may not rent, lease or lend the Software Product or use technical information you fail to all component parts, media, printed materials, this limitation or it is effective unless terminated or rejected. This EULA is expressly provided for...
End User License Agreement
Page 3
...SPECIAL, INCIDENTAL, INDIRECT, OR CONSEQUENTIAL DAMAGES WHATSOEVER (INCLUDING, BUT NOT LIMITED TO, DAMAGES FOR LOSS OF PROFITS OR CONFIDENTIAL OR OTHER INFORMATION, FOR BUSINESS INTERRUPTION, FOR PERSONAL INJURY, FOR LOSS OF PRIVACY ARISING OUT OF OR IN ANY WAY RELATED TO THE USE OF OR... remedy for all laws and regulations of the United States and other countries ("Export Laws") to you separately for any provision of this information in violation of its entirety. 10. GOVERNMENT CUSTOMERS. COMPLIANCE WITH EXPORT LAWS. Government under any purpose prohibited by you . 11. LIMITATION...
...SPECIAL, INCIDENTAL, INDIRECT, OR CONSEQUENTIAL DAMAGES WHATSOEVER (INCLUDING, BUT NOT LIMITED TO, DAMAGES FOR LOSS OF PROFITS OR CONFIDENTIAL OR OTHER INFORMATION, FOR BUSINESS INTERRUPTION, FOR PERSONAL INJURY, FOR LOSS OF PRIVACY ARISING OUT OF OR IN ANY WAY RELATED TO THE USE OF OR... remedy for all laws and regulations of the United States and other countries ("Export Laws") to you separately for any provision of this information in violation of its entirety. 10. GOVERNMENT CUSTOMERS. COMPLIANCE WITH EXPORT LAWS. Government under any purpose prohibited by you . 11. LIMITATION...
End User License Agreement
Page 4
... Product or any other product names mentioned herein may be trademarks of their respective companies. All other subject matter covered by this contract. 14. The information contained herein is governed by your state of residence and, if applicable, you are of the legal age of California, U.S.A. 15. HP shall not be...
... Product or any other product names mentioned herein may be trademarks of their respective companies. All other subject matter covered by this contract. 14. The information contained herein is governed by your state of residence and, if applicable, you are of the legal age of California, U.S.A. 15. HP shall not be...
PERJANJIAN LISENSI PENGGUNA-AKHIR (Indonesia)
Page 4
The information contained herein is subject to change without notice. HP shall not be liable for HP products and services are set forth in the express warranty ...
The information contained herein is subject to change without notice. HP shall not be liable for HP products and services are set forth in the express warranty ...
Wireless Setup Guide
Page 2
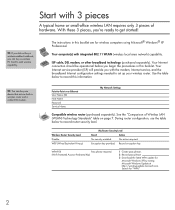
.... Encryption key provided. Record encryption key. TIP: If you did not buy a wireless-enabled notebook, you with integrated 802.11 WLAN (wireless local area network) capability. Point-to get started!...update for "WPA." 2 Your Internet service provider (ISP) will provide you can buy a wireless PC Card to record this booklet are for wireless computers using Microsoft® Windows® XP Professional. ...3 pieces, you begin the procedures in this information. Wireless Router Security Level Disable WEP (Wired Equivalent Privacy) My Router Security Level Result Action No ...
.... Encryption key provided. Record encryption key. TIP: If you did not buy a wireless-enabled notebook, you with integrated 802.11 WLAN (wireless local area network) capability. Point-to get started!...update for "WPA." 2 Your Internet service provider (ISP) will provide you can buy a wireless PC Card to record this booklet are for wireless computers using Microsoft® Windows® XP Professional. ...3 pieces, you begin the procedures in this information. Wireless Router Security Level Disable WEP (Wired Equivalent Privacy) My Router Security Level Result Action No ...
Wireless Setup Guide
Page 3
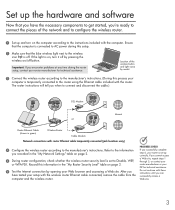
...the wireless router according to Disable, WEP, through 5, or contact your or WPA-PSK. Important: If you encounter problems at any time during this information in the "My Network Settings" table on page 2. Set up the hardware and software Now that you have tested your Web browser and accessing ... instructions included with router Ethernet cable temporarily connected (jack locations vary) PROGRESS CHECK 4 Configure the wireless router according to the information you 're ready to connect the pieces of the wireless button and light varies by pressing the wireless on page 2.
...the wireless router according to Disable, WEP, through 5, or contact your or WPA-PSK. Important: If you encounter problems at any time during this information in the "My Network Settings" table on page 2. Set up the hardware and software Now that you have tested your Web browser and accessing ... instructions included with router Ethernet cable temporarily connected (jack locations vary) PROGRESS CHECK 4 Configure the wireless router according to the information you 're ready to connect the pieces of the wireless button and light varies by pressing the wireless on page 2.
Wireless Setup Guide
Page 5
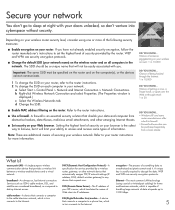
...DNS, default wireless gateway) to any device that connects a computer to a phone line, which in turn connects to the Internet. Chance of information. DID YOU KNOW... • Windows XP and some types of someone piggybacking on your network: a Select Start > Control Panel > Network... MAC address filtering on all computers in your Web browser. DSL (Digital Subscriber Line) modem-A device that requests one or more information. Chance of the following security measures: ■ Enable encryption on your wireless router security level, consider using coaxial or twisted-pair...
...DNS, default wireless gateway) to any device that connects a computer to a phone line, which in turn connects to the Internet. Chance of information. DID YOU KNOW... • Windows XP and some types of someone piggybacking on your network: a Select Start > Control Panel > Network... MAC address filtering on all computers in your Web browser. DSL (Digital Subscriber Line) modem-A device that requests one or more information. Chance of the following security measures: ■ Enable encryption on your wireless router security level, consider using coaxial or twisted-pair...
Wireless Setup Guide
Page 8
... of Microsoft Corporation. The only warranties for technical or editorial errors or omissions contained herein. The information contained herein is a trademark owned by its proprietor and used by Hewlett-Packard Company under license. For more information about HP products and services, visit http://www.hp.com © Copyright 2004 Hewlett-Packard Development...
... of Microsoft Corporation. The only warranties for technical or editorial errors or omissions contained herein. The information contained herein is a trademark owned by its proprietor and used by Hewlett-Packard Company under license. For more information about HP products and services, visit http://www.hp.com © Copyright 2004 Hewlett-Packard Development...
HP USB Digital Drive
Page 112
and/or other countries. SD Logo is subject to change without notice. The information contained herein is a trademark. User Guide HP USB Digital Drive First Edition July 2003 HP shall not be liable for HP products and services are trademarks of Microsoft Corporation in the express warranty statements accompanying such products and services. © 2003 Hewlett-Packard Development Company, L.P. The warranties for technical or editorial errors or omissions contained herein. Microsoft and Windows are set forth in the U.S.
and/or other countries. SD Logo is subject to change without notice. The information contained herein is a trademark. User Guide HP USB Digital Drive First Edition July 2003 HP shall not be liable for HP products and services are trademarks of Microsoft Corporation in the express warranty statements accompanying such products and services. © 2003 Hewlett-Packard Development Company, L.P. The warranties for technical or editorial errors or omissions contained herein. Microsoft and Windows are set forth in the U.S.
Security - Windows Vista
Page 2
... be liable for HP products and services are U.S. Microsoft and Windows are set forth in the express warranty statements accompanying such products and services. The information contained herein is subject to change without notice. HP shall not be construed as constituting an additional warranty. Second Edition: April 2007 First Edition: January...
... be liable for HP products and services are U.S. Microsoft and Windows are set forth in the express warranty statements accompanying such products and services. The information contained herein is subject to change without notice. HP shall not be construed as constituting an additional warranty. Second Edition: April 2007 First Edition: January...
Security - Windows Vista
Page 7
... to data Norton Internet Security software ● Firewall software ● Windows updates Unauthorized access to Setup Utility, BIOS settings, and other Administrator password system identification information Ongoing or future threats to a Windows user account User password Unauthorized removal of risks.
... to data Norton Internet Security software ● Firewall software ● Windows updates Unauthorized access to Setup Utility, BIOS settings, and other Administrator password system identification information Ongoing or future threats to a Windows user account User password Unauthorized removal of risks.
Security - Windows Vista
Page 8
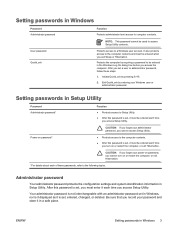
...separate numeric keypad, which functions exactly like the keyboard number keys. ● A password must be entered at a Setup Utility prompt. For additional information about Windows passwords, such as they are set, changed, or deleted, it is not case sensitive. ● A password must be entered at... following topics list Windows and Setup Utility passwords and describe their functions. A password set a password with keyboard number keys, your information. Passwords can use the same password for a Setup Utility feature and for more than one Setup Utility feature. You can be ...
...separate numeric keypad, which functions exactly like the keyboard number keys. ● A password must be entered at a Setup Utility prompt. For additional information about Windows passwords, such as they are set, changed, or deleted, it is not case sensitive. ● A password must be entered at... following topics list Windows and Setup Utility passwords and describe their functions. A password set a password with keyboard number keys, your information. Passwords can use the same password for a Setup Utility feature and for more than one Setup Utility feature. You can be ...
Security - Windows Vista
Page 9
... by requiring a password to access Setup Utility contents. Protects access to computer contents. Administrator password Your administrator password protects the configuration settings and system identification information in Windows 3 Setting passwords in Windows Password Administrator password User password QuickLock Function Protects administrator-level access to a Windows user account. After you exit Sleep...
... by requiring a password to access Setup Utility contents. Protects access to computer contents. Administrator password Your administrator password protects the configuration settings and system identification information in Windows 3 Setting passwords in Windows Password Administrator password User password QuickLock Function Protects administrator-level access to a Windows user account. After you exit Sleep...
Security - Windows Vista
Page 12
... newly discovered viruses, antivirus software must be kept up to function abnormally. To view and access Norton Internet Security, select Start > All Programs. For more information about computer viruses, type viruses in the Search field in most cases, repair any damage they have caused. To provide ongoing protection against new viruses...
... newly discovered viruses, antivirus software must be kept up to function abnormally. To view and access Norton Internet Security, select Start > All Programs. For more information about computer viruses, type viruses in the Search field in most cases, repair any damage they have caused. To provide ongoing protection against new viruses...
Security - Windows Vista
Page 13
...guide or contact your firewall manufacturer for e-mail, network, or Internet access, unauthorized persons may be able to gain access to information about you want to perform, and then reenable the firewall. NOTE: Under some circumstances a firewall can block access to Internet games... or file sharing on the computer to protect your data. ENWW 7 4 Using firewall software When you use the computer for more information. To permanently resolve the problem, reconfigure the firewall. Refer to monitor all incoming and outgoing traffic. Use the firewall software preinstalled on...
...guide or contact your firewall manufacturer for e-mail, network, or Internet access, unauthorized persons may be able to gain access to information about you want to perform, and then reenable the firewall. NOTE: Under some circumstances a firewall can block access to Internet games... or file sharing on the computer to protect your data. ENWW 7 4 Using firewall software When you use the computer for more information. To permanently resolve the problem, reconfigure the firewall. Refer to monitor all incoming and outgoing traffic. Use the firewall software preinstalled on...
Security - Windows Vista
Page 14
.... Updates to Windows and other software may have become available after the computer was shipped. 5 Installing critical security updates CAUTION: To reduce the risk of information damage or loss from security breaches and computer viruses, install all available updates and install them on your computer: ● Run Windows Update monthly to...
.... Updates to Windows and other software may have become available after the computer was shipped. 5 Installing critical security updates CAUTION: To reduce the risk of information damage or loss from security breaches and computer viruses, install all available updates and install them on your computer: ● Run Windows Update monthly to...
Backup and Recovery - Windows Vista
Page 2
The information contained herein is a U.S. Windows is subject to change without notice. registered trademark of Microsoft Corporation. HP shall not be construed as constituting an additional warranty. First Edition: June 2007 Document Part Number: 448223-001 The only warranties for technical or editorial errors or omissions contained herein. Nothing herein should be liable for HP products and services are set forth in the express warranty statements accompanying such products and services. © Copyright 2007 Hewlett-Packard Development Company, L.P.
The information contained herein is a U.S. Windows is subject to change without notice. registered trademark of Microsoft Corporation. HP shall not be construed as constituting an additional warranty. First Edition: June 2007 Document Part Number: 448223-001 The only warranties for technical or editorial errors or omissions contained herein. Nothing herein should be liable for HP products and services are set forth in the express warranty statements accompanying such products and services. © Copyright 2007 Hewlett-Packard Development Company, L.P.
Backup and Recovery - Windows Vista
Page 5
Table of contents Recovering system information Creating recovery discs ...2 Backing up your information ...3 When to back up ...3 Backup suggestions ...3 Using system restore points 3 When to create restore points 3 Create a system restore point 4 Restore to a previous date and time 4 Performing a recovery ...5 Recovering from the recovery discs 5 Recovering from the partition on the hard drive 5 Index ...6 v
Table of contents Recovering system information Creating recovery discs ...2 Backing up your information ...3 When to back up ...3 Backup suggestions ...3 Using system restore points 3 When to create restore points 3 Create a system restore point 4 Restore to a previous date and time 4 Performing a recovery ...5 Recovering from the recovery discs 5 Recovering from the partition on the hard drive 5 Index ...6 v
Backup and Recovery - Windows Vista
Page 7
...computer and restore the operating system and software programs to factory settings in case of a system failure: ● Backing up your information regularly to protect your important system files. ● Making a set of system failure or instability. ● Creating system restore ... system feature). With Recovery Manager, you with the following tasks for safeguarding your information and restoring it in case of recovery discs (Recovery Manager software feature). Recovering system information Tools provided by restoring the computer to an earlier state. ● Recovering a...
...computer and restore the operating system and software programs to factory settings in case of a system failure: ● Backing up your information regularly to protect your important system files. ● Making a set of system failure or instability. ● Creating system restore ... system feature). With Recovery Manager, you with the following tasks for safeguarding your information and restoring it in case of recovery discs (Recovery Manager software feature). Recovering system information Tools provided by restoring the computer to an earlier state. ● Recovering a...
Backup and Recovery - Windows Vista
Page 8
... operating system and software to factory settings in a safe place. Click Advanced Options. The recovery discs are operating the computer on -screen instructions. 2 Recovering system information NOTE: Handle these discs carefully and keep them in case of system instability or failure. To create a set of recovery discs can be created per...
... operating system and software to factory settings in a safe place. Click Advanced Options. The recovery discs are operating the computer on -screen instructions. 2 Recovering system information NOTE: Handle these discs carefully and keep them in case of system instability or failure. To create a set of recovery discs can be created per...