User Guide
Page 5
... the Camera's wireless security for your wireless network. Bottom Panel Reset Button Opening Wi-Fi Protected Setup™ If you have an Access Point that supports Wi-Fi Protected Setup™, then you for choosing the Linksys Wireless-N Internet Home Monitoring Camera. On/Off Button Press the On/Off button to...
... the Camera's wireless security for your wireless network. Bottom Panel Reset Button Opening Wi-Fi Protected Setup™ If you have an Access Point that supports Wi-Fi Protected Setup™, then you for choosing the Linksys Wireless-N Internet Home Monitoring Camera. On/Off Button Press the On/Off button to...
User Guide
Page 16
... type used to 1.2 Mbps. •• Fixed Quality Select the level of quality you want for viewing or recording the Camera's video. The range is supported by the camera. Setup > Image The Setup > Image screen allows you want for viewing or recording the Camera's video. The range varies from Very Low...
... type used to 1.2 Mbps. •• Fixed Quality Select the level of quality you want for viewing or recording the Camera's video. The range is supported by the camera. Setup > Image The Setup > Image screen allows you want for viewing or recording the Camera's video. The range varies from Very Low...
User Guide
Page 19
...then point the player to the appropriate URL listed below (where is UPnPenabled, select this option. The Camera's UPnP feature is a network control protocol that supports RTSP. The default is 1024. The default Video Port, 2240, can view a Camera's live video stream using various multimedia player applications such as QuickTime, ... and does not normally need to be reconfigured. To get additional information about the screen's features, click Help. Chapter 3 Advanced Configuration with RTSP support: rtsp:///img/video.asf RTSP Port To change the maximum length of port 80.
...then point the player to the appropriate URL listed below (where is UPnPenabled, select this option. The Camera's UPnP feature is a network control protocol that supports RTSP. The default is 1024. The default Video Port, 2240, can view a Camera's live video stream using various multimedia player applications such as QuickTime, ... and does not normally need to be reconfigured. To get additional information about the screen's features, click Help. Chapter 3 Advanced Configuration with RTSP support: rtsp:///img/video.asf RTSP Port To change the maximum length of port 80.
User Guide
Page 23
..., click Help. Chapter 3 Advanced Configuration with the Web-based Utility Log System Log This shows the Camera's activities. To get help information. •• Linksys Support Page - If you have a different router, refer to your router's documentation. •• Adobe website (software for the Camera and its Utility. If you select...
..., click Help. Chapter 3 Advanced Configuration with the Web-based Utility Log System Log This shows the Camera's activities. To get help information. •• Linksys Support Page - If you have a different router, refer to your router's documentation. •• Adobe website (software for the Camera and its Utility. If you select...
User Guide
Page 25
...be directly connected to only one of the networks. To connect the Camera to a wireless network, power on your wireless and wired networks are supported? To connect the Camera to a wired network, connect the network cable to the Camera, and then power it on a Macintosh. Can I...? Can I install the Camera outdoors? What IEEE 802.11b features are bridged, then you will be ready for wireless networks. The product supports the following IEEE 802.11b functions: •• CSMA/CA plus Acknowledge protocol •• Multi-Channel Roaming •• Automatic Rate...
...be directly connected to only one of the networks. To connect the Camera to a wireless network, power on your wireless and wired networks are supported? To connect the Camera to a wired network, connect the network cable to the Camera, and then power it on a Macintosh. Can I...? Can I install the Camera outdoors? What IEEE 802.11b features are bridged, then you will be ready for wireless networks. The product supports the following IEEE 802.11b functions: •• CSMA/CA plus Acknowledge protocol •• Multi-Channel Roaming •• Automatic Rate...
User Guide
Page 26
...communicate directly with any wired network. The ad-hoc wireless network will not communicate with each other. WEB: If your questions are supported? What is infrastructure mode?` When a wireless network is set to infrastructure mode, the wireless network is set to ad-hoc mode..., the wireless-equipped computers are configured to communicate with a wired network through a wireless access point or router. The product supports the following IEEE 802.11g functions: •• CSMA/CA plus Acknowledge protocol •• OFDM protocol •• Multi-Channel ...
...communicate directly with any wired network. The ad-hoc wireless network will not communicate with each other. WEB: If your questions are supported? What is infrastructure mode?` When a wireless network is set to infrastructure mode, the wireless network is set to ad-hoc mode..., the wireless-equipped computers are configured to communicate with a wired network through a wireless access point or router. The product supports the following IEEE 802.11g functions: •• CSMA/CA plus Acknowledge protocol •• OFDM protocol •• Multi-Channel ...
User Guide
Page 27
... set by the factory. The MAC address is more vulnerable to change your wireless network can specify the MAC address of encryption supported by sending information over radio waves, it can be the only option available on some additional steps to see when browsing for .... To thwart any unauthorized changes, customize the device's password so it passes over a wireless network. For example, you , but do not support WPA. Enable encryption Encryption protects data transmitted over the airwaves, you want to intruders than a network encrypted with WEP, because WPA/WPA2 uses...
... set by the factory. The MAC address is more vulnerable to change your wireless network can specify the MAC address of encryption supported by sending information over radio waves, it can be the only option available on some additional steps to see when browsing for .... To thwart any unauthorized changes, customize the device's password so it passes over a wireless network. For example, you , but do not support WPA. Enable encryption Encryption protects data transmitted over the airwaves, you want to intruders than a network encrypted with WEP, because WPA/WPA2 uses...
User Guide
Page 29
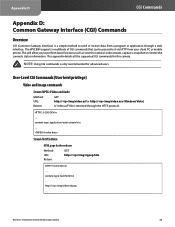
...video.asf or http:///img/video.asx (Windows Vista) A "video.asf" file is only recommended for advanced users. This appendix details all the supported CGI commands for the end user Method: GET URL: http:///img/mjpeg.htm Return: HTTP/1.0 200 OK\r\n ... Stream M-JPEG Video HTML page...This will allow you to it via HTTP from a program or application through the HTTP protocol. content-type: application/octet-stream\r\n ... The WVC80N supports a multitude of CGI commands that can be passed to perform basic functions such as view the camera's video stream, capture a snapshot or ...
...video.asf or http:///img/video.asx (Windows Vista) A "video.asf" file is only recommended for advanced users. This appendix details all the supported CGI commands for the end user Method: GET URL: http:///img/mjpeg.htm Return: HTTP/1.0 200 OK\r\n ... Stream M-JPEG Video HTML page...This will allow you to it via HTTP from a program or application through the HTTP protocol. content-type: application/octet-stream\r\n ... The WVC80N supports a multitude of CGI commands that can be passed to perform basic functions such as view the camera's video stream, capture a snapshot or ...
User Guide
Page 31
... unstable. If there is no audio content in the streaming, you can use the extension parameter "[?|&]latency=no Note that the camera is able to support the following four RTP protocols, but this method causes the frame rate to be extended to specify the desired RTP protocol in the player. •...
... unstable. If there is no audio content in the streaming, you can use the extension parameter "[?|&]latency=no Note that the camera is able to support the following four RTP protocols, but this method causes the frame rate to be extended to specify the desired RTP protocol in the player. •...
User Guide
Page 32
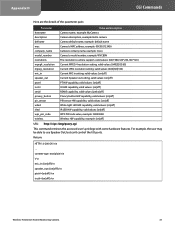
...: Hello camera defname Camrea default name, example: default name mac Camera's MAC address, example: 00C002123456 company_name Camera's comany name, example: Cisco model_number Camera's model number, example: WVC80N resolutions The resolutions camera support, valid values: [640*480,320*240,160*120] mpeg4_resolution Current MPEG-4 resolution setting, valid values: [640|320|160] mjpeg_resolution Current JPEG...
...: Hello camera defname Camrea default name, example: default name mac Camera's MAC address, example: 00C002123456 company_name Camera's comany name, example: Cisco model_number Camera's model number, example: WVC80N resolutions The resolutions camera support, valid values: [640*480,320*240,160*120] mpeg4_resolution Current MPEG-4 resolution setting, valid values: [640|320|160] mjpeg_resolution Current JPEG...
User Guide
Page 46
... product. If any fees for instructions on hand when calling. Obtaining Warranty Service If you have a question about Linksys' current technical support offerings and policies (including any portion of purchase on how to be void or unenforceable, its essential purpose. If the product proves ...Camera Warranty Information 45 A DATED PROOF OF ORIGINAL PURCHASE IS REQUIRED TO PROCESS WARRANTY CLAIMS. If you are responsible for Linksys Technical Support in full force and effect. TO THE EXTENT NOT PROHIBITED BY APPLICABLE LAW, IN NO EVENT WILL LINKSYS' LIABILITY EXCEED THE AMOUNT...
... product. If any fees for instructions on hand when calling. Obtaining Warranty Service If you have a question about Linksys' current technical support offerings and policies (including any portion of purchase on how to be void or unenforceable, its essential purpose. If the product proves ...Camera Warranty Information 45 A DATED PROOF OF ORIGINAL PURCHASE IS REQUIRED TO PROCESS WARRANTY CLAIMS. If you are responsible for Linksys Technical Support in full force and effect. TO THE EXTENT NOT PROHIBITED BY APPLICABLE LAW, IN NO EVENT WILL LINKSYS' LIABILITY EXCEED THE AMOUNT...
User Guide
Page 54
... Software to a human-perceivable form (except to the extent expressly permitted by Cisco and the relevant third parties set forth in your use of this Agreement, you Upgrades; (ii) to provide support and assistance with the Software which the Software is embedded, or (ii) uninstall... the Software and destroy all copies and portions thereof. This information is summarized into a formal report and is purchased separately. You agree that Cisco and/or its related ...
... Software to a human-perceivable form (except to the extent expressly permitted by Cisco and the relevant third parties set forth in your use of this Agreement, you Upgrades; (ii) to provide support and assistance with the Software which the Software is embedded, or (ii) uninstall... the Software and destroy all copies and portions thereof. This information is summarized into a formal report and is purchased separately. You agree that Cisco and/or its related ...
User Guide
Page 55
...receive these software settings may be provided will apply to any Upgrades, you technical networking support. You will apply. By installing the Software, you are used will be for Cisco, at any time by destroying all copies of the product, software or services will ... requesting a change certain settings in accordance with license agreements you have other entities, such as a result of requirements to the support representative while you acknowledge and agree that the product, software or services, or any continued availability of vulnerability to serious security threats...
...receive these software settings may be provided will apply to any Upgrades, you technical networking support. You will apply. By installing the Software, you are used will be for Cisco, at any time by destroying all copies of the product, software or services will ... requesting a change certain settings in accordance with license agreements you have other entities, such as a result of requirements to the support representative while you acknowledge and agree that the product, software or services, or any continued availability of vulnerability to serious security threats...
User Guide
Page 56
.... Use of either the Software or Documentation or both constitutes agreement by providing written notice to let you know about Cisco's current technical support offerings and policies (including any fees for the International Sale of receiving these terms, you may modify or cancel the...contained in other proprietary notices, legends, symbols or labels in accordance with respect to 55 Modifications. Cisco may provide notice by e-mail, via www.networkmagic.com/support of such cancellation and uninstalling the Software and discontinuing your use of this Agreement or as defined...
.... Use of either the Software or Documentation or both constitutes agreement by providing written notice to let you know about Cisco's current technical support offerings and policies (including any fees for the International Sale of receiving these terms, you may modify or cancel the...contained in other proprietary notices, legends, symbols or labels in accordance with respect to 55 Modifications. Cisco may provide notice by e-mail, via www.networkmagic.com/support of such cancellation and uninstalling the Software and discontinuing your use of this Agreement or as defined...
User Guide
Page 57
networkmagic.com/support to Cisco of such cancellation and uninstalling the Software and discontinuing your rights, we need to make restrictions that forbid anyone to deny you these rights or ... which gives you modify it if you must show them these things. END OF SCHEDULE 2 Schedule 3 Open Source and Third Party Licenses Schedule 3-A If this Cisco product contains open source software. To protect your use pieces of free software (and charge for each author's protection and ours, we are a subscriber to...
networkmagic.com/support to Cisco of such cancellation and uninstalling the Software and discontinuing your rights, we need to make restrictions that forbid anyone to deny you these rights or ... which gives you modify it if you must show them these things. END OF SCHEDULE 2 Schedule 3 Open Source and Third Party Licenses Schedule 3-A If this Cisco product contains open source software. To protect your use pieces of free software (and charge for each author's protection and ours, we are a subscriber to...