Quick Start Guide
Page 20
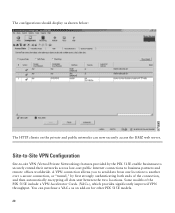
... businesses to securely extend their networks across low-cost public Internet connections to another over a secure connection, or "tunnel," by first strongly authenticating both ends of the PIX 515E include a VPN Accelerator Card+ (VAC+), which provides significantly improved VPN throughput. Some models of the connection, and ...display as an add-on the private and public networks can purchase a VAC+ as shown below: The HTTP clients on for other PIX 515E models. 20 A VPN connection allows you to send data from one location to business partners and remote offices worldwide. You can now ...
... businesses to securely extend their networks across low-cost public Internet connections to another over a secure connection, or "tunnel," by first strongly authenticating both ends of the PIX 515E include a VPN Accelerator Card+ (VAC+), which provides significantly improved VPN throughput. Some models of the connection, and ...display as an add-on the private and public networks can purchase a VAC+ as shown below: The HTTP clients on for other PIX 515E models. 20 A VPN connection allows you to send data from one location to business partners and remote offices worldwide. You can now ...
Quick Start Guide
Page 21
... from the Wizards drop-down menu as the enabled interface for the current VPN tunnel. The illustration below shows an example VPN tunnel between two PIX 515E, and will be referenced in five simple steps. Select the Site to configure PIX 1. c. At the first VPN Wizard page, do the following steps. Note The Site to... the main PDM page, select the VPN Wizard option from the drop-down menu. PDM provides an easy-to-use VPN Wizard that can include PIX Firewalls, VPN concentrators, or other devices that support site-to-site IPSec connectivity.
... from the Wizards drop-down menu as the enabled interface for the current VPN tunnel. The illustration below shows an example VPN tunnel between two PIX 515E, and will be referenced in five simple steps. Select the Site to configure PIX 1. c. At the first VPN Wizard page, do the following steps. Note The Site to... the main PDM page, select the VPN Wizard option from the drop-down menu. PDM provides an easy-to-use VPN Wizard that can include PIX Firewalls, VPN concentrators, or other devices that support site-to-site IPSec connectivity.
Quick Start Guide
Page 24
... the Encryption (DES/3DES/AES), Authentication algorithms (MD5/SHA), and the Diffie-Hellman group (1/2/5) used by the PIX 515E during an IKE security association. Click the Next button to establish secure VPN tunnels between two peers. Step 3 Configure the IKE Policy This step is comprised of VPN... tunnel failures and can slow down the process. Note When configuring PIX 2, enter the exact values for each of the options that you selected for PIX 1. In most cases, the default values are a common cause of two...
... the Encryption (DES/3DES/AES), Authentication algorithms (MD5/SHA), and the Diffie-Hellman group (1/2/5) used by the PIX 515E during an IKE security association. Click the Next button to establish secure VPN tunnels between two peers. Step 3 Configure the IKE Policy This step is comprised of VPN... tunnel failures and can slow down the process. Note When configuring PIX 2, enter the exact values for each of the options that you selected for PIX 1. In most cases, the default values are a common cause of two...
Quick Start Guide
Page 25
Note When configuring PIX 2, enter the exact same values for each of VPN tunnel failures and can slow down the process. Click the Next button to the next window. Confirm all values before continuing to continue. 25 2. a. b. Configure the IPSec parameters. In the second window, select the Encryption algorithm (DES/3DES/AES) and Authentication algorithm (MD5/SHA). Encryption and algorithm mismatches are a common cause of the options that you selected for PIX 1.
Note When configuring PIX 2, enter the exact same values for each of VPN tunnel failures and can slow down the process. Click the Next button to the next window. Confirm all values before continuing to continue. 25 2. a. b. Configure the IPSec parameters. In the second window, select the Encryption algorithm (DES/3DES/AES) and Authentication algorithm (MD5/SHA). Encryption and algorithm mismatches are a common cause of the options that you selected for PIX 1.
Quick Start Guide
Page 26
Note Use the Browse button to select from the selected panel by clicking on the >> or a. Add or remove networks dynamically from preconfigured groups. Select the Local Host/Network based on the local PIX 515E encrypted through the VPN tunnel. Select network traffic on the IP Address, Name, or Group. Step 4 Configure Internal Traffic This step is comprised of two windows: 1.
Note Use the Browse button to select from the selected panel by clicking on the >> or a. Add or remove networks dynamically from preconfigured groups. Select the Local Host/Network based on the local PIX 515E encrypted through the VPN tunnel. Select network traffic on the IP Address, Name, or Group. Step 4 Configure Internal Traffic This step is comprised of two windows: 1.
Quick Start Guide
Page 27
Select traffic permitted from this tunnel is the local network for remote network configuration. a. The remote network for PIX 1 is permitted through the tunnel. b. Click the Finish button to complete the configuration. 27 For PIX 1, the remote network is Network B (20.20.20.0) so traffic encrypted from the remote PIX Firewall. In the second window, select VPN traffic for PIX 2 and vice versa. Note When configuring PIX 2, ensure that the values are correctly entered. 2.
Select traffic permitted from this tunnel is the local network for remote network configuration. a. The remote network for PIX 1 is permitted through the tunnel. b. Click the Finish button to complete the configuration. 27 For PIX 1, the remote network is Network B (20.20.20.0) so traffic encrypted from the remote PIX Firewall. In the second window, select VPN traffic for PIX 2 and vice versa. Note When configuring PIX 2, ensure that the values are correctly entered. 2.
Getting Started Guide
Page 4
...Topology 3-1 Implementing the IPsec Remote-Access VPN Scenario 3-2 Information to Have Available 3-3 Starting ASDM 3-3 Configuring the PIX 515E for an IPsec Remote-Access VPN 3-5 Selecting VPN Client Types 3-6 Specifying the VPN Tunnel Group Name and Authentication Method 3-7 Specifying a User Authentication Method 3-8 (Optional) Configuring User Accounts 3-10 Configuring ...About the Remote VPN Peer 4-6 Configuring the IKE Policy 4-7 Configuring IPsec Encryption and Authentication Parameters 4-9 Specifying Hosts and Networks 4-10 PIX 515E Security Appliance Getting Started Guide iv 78-17645-01
...Topology 3-1 Implementing the IPsec Remote-Access VPN Scenario 3-2 Information to Have Available 3-3 Starting ASDM 3-3 Configuring the PIX 515E for an IPsec Remote-Access VPN 3-5 Selecting VPN Client Types 3-6 Specifying the VPN Tunnel Group Name and Authentication Method 3-7 Specifying a User Authentication Method 3-8 (Optional) Configuring User Accounts 3-10 Configuring ...About the Remote VPN Peer 4-6 Configuring the IKE Policy 4-7 Configuring IPsec Encryption and Authentication Parameters 4-9 Specifying Hosts and Networks 4-10 PIX 515E Security Appliance Getting Started Guide iv 78-17645-01
Getting Started Guide
Page 43
...VPN enables you are implementing an Easy VPN solution, this chapter describes how to off-site users. If you to create secure connections, or tunnels, across the Internet, thus providing secure access to configure the Easy VPN server (sometimes called a headend device). This chapter includes the following sections: •... This chapter describes how to use the security appliance to accept requests from and establish IPsec connections with VPN clients, such as a Cisco Easy VPN hardware client, over the Internet. 78-17645-01 PIX 515E Security Appliance Getting Started Guide 3-1
...VPN enables you are implementing an Easy VPN solution, this chapter describes how to off-site users. If you to create secure connections, or tunnels, across the Internet, thus providing secure access to configure the Easy VPN server (sometimes called a headend device). This chapter includes the following sections: •... This chapter describes how to use the security appliance to accept requests from and establish IPsec connections with VPN clients, such as a Cisco Easy VPN hardware client, over the Internet. 78-17645-01 PIX 515E Security Appliance Getting Started Guide 3-1
Getting Started Guide
Page 45
...3 Scenario: IPsec Remote-Access VPN Configuration Implementing the IPsec Remote-Access VPN Scenario • Specifying the VPN Tunnel Group Name and Authentication Method, page 3-7 • Specifying a User Authentication Method, page 3-8 • ...• Configuring IPsec Encryption and Authentication Parameters, page 3-15 • Specifying Address Translation Exception and Split Tunneling, page 3-16 • Verifying the Remote-Access VPN Configuration, page 3-17 Information to Have Available Before...192.168.1.1/admin/. 78-17645-01 PIX 515E Security Appliance Getting Started Guide 3-3
...3 Scenario: IPsec Remote-Access VPN Configuration Implementing the IPsec Remote-Access VPN Scenario • Specifying the VPN Tunnel Group Name and Authentication Method, page 3-7 • Specifying a User Authentication Method, page 3-8 • ...• Configuring IPsec Encryption and Authentication Parameters, page 3-15 • Specifying Address Translation Exception and Split Tunneling, page 3-16 • Verifying the Remote-Access VPN Configuration, page 3-17 Information to Have Available Before...192.168.1.1/admin/. 78-17645-01 PIX 515E Security Appliance Getting Started Guide 3-3
Getting Started Guide
Page 47
...-down menu. Chapter 3 Scenario: IPsec Remote-Access VPN Configuration Implementing the IPsec Remote-Access VPN Scenario Configuring the PIX 515E for an IPsec Remote-Access VPN To begin the process for the incoming VPN tunnels. Step 2 In Step 1 of the VPN Wizard, perform the following steps: Step 1 In the main ASDM window, choose...
...-down menu. Chapter 3 Scenario: IPsec Remote-Access VPN Configuration Implementing the IPsec Remote-Access VPN Scenario Configuring the PIX 515E for an IPsec Remote-Access VPN To begin the process for the incoming VPN tunnels. Step 2 In Step 1 of the VPN Wizard, perform the following steps: Step 1 In the main ASDM window, choose...
Getting Started Guide
Page 49
...the type of authentication that method of authentication. 78-17645-01 PIX 515E Security Appliance Getting Started Guide 3-7 Chapter 3 Scenario: IPsec Remote-Access VPN Configuration Implementing the IPsec Remote-Access VPN Scenario Specifying the VPN Tunnel Group Name and Authentication Method In Step 3 of the VPN ...Wizard, perform the following steps: • To use a static preshared key for authentication, click the Pre-Shared Key radio button and enter a preshared key (for example, "Cisco"). This key ...
...the type of authentication that method of authentication. 78-17645-01 PIX 515E Security Appliance Getting Started Guide 3-7 Chapter 3 Scenario: IPsec Remote-Access VPN Configuration Implementing the IPsec Remote-Access VPN Scenario Specifying the VPN Tunnel Group Name and Authentication Method In Step 3 of the VPN ...Wizard, perform the following steps: • To use a static preshared key for authentication, click the Pre-Shared Key radio button and enter a preshared key (for example, "Cisco"). This key ...
Getting Started Guide
Page 50
... can be authenticated either by a local authentication database or by using external authentication, authorization, and accounting (AAA) servers (RADIUS, TACACS+, SDI, NT, Kerberos, and LDAP). PIX 515E Security Appliance Getting Started Guide 3-8 78-17645-01 Implementing the IPsec Remote-Access VPN Scenario Chapter 3 Scenario: IPsec Remote-Access VPN Configuration Step 2 Step 3 Enter...
... can be authenticated either by a local authentication database or by using external authentication, authorization, and accounting (AAA) servers (RADIUS, TACACS+, SDI, NT, Kerberos, and LDAP). PIX 515E Security Appliance Getting Started Guide 3-8 78-17645-01 Implementing the IPsec Remote-Access VPN Scenario Chapter 3 Scenario: IPsec Remote-Access VPN Configuration Step 2 Step 3 Enter...
Getting Started Guide
Page 55
In most cases, the ASDM default values are sufficient to continue. Step 2 Click Next to establish secure VPN tunnels. 78-17645-01 PIX 515E Security Appliance Getting Started Guide 3-13 Configuring the IKE Policy IKE is also an authentication method to ensure the identity of the VPN Wizard, perform ...
In most cases, the ASDM default values are sufficient to continue. Step 2 Click Next to establish secure VPN tunnels. 78-17645-01 PIX 515E Security Appliance Getting Started Guide 3-13 Configuring the IKE Policy IKE is also an authentication method to ensure the identity of the VPN Wizard, perform ...
Getting Started Guide
Page 58
... Translation (NAT) to prevent internal IP addresses from the Selected Hosts/Networks pane, click Add or Delete, respectively. 3-16 PIX 515E Security Appliance Getting Started Guide 78-17645-01 To add or remove hosts, groups, and networks dynamically from being exposed externally....Scenario Chapter 3 Scenario: IPsec Remote-Access VPN Configuration Specifying Address Translation Exception and Split Tunneling Split tunneling lets a remote-access IPsec client conditionally direct packets over an IPsec tunnel in encrypted form or to a network interface in the list of internal resources made ...
... Translation (NAT) to prevent internal IP addresses from the Selected Hosts/Networks pane, click Add or Delete, respectively. 3-16 PIX 515E Security Appliance Getting Started Guide 78-17645-01 To add or remove hosts, groups, and networks dynamically from being exposed externally....Scenario Chapter 3 Scenario: IPsec Remote-Access VPN Configuration Specifying Address Translation Exception and Split Tunneling Split tunneling lets a remote-access IPsec client conditionally direct packets over an IPsec tunnel in encrypted form or to a network interface in the list of internal resources made ...
Getting Started Guide
Page 59
... similar to the following: 78-17645-01 PIX 515E Security Appliance Getting Started Guide 3-17 The displayed configuration should be sent out directly to continue. Verifying the Remote-Access VPN Configuration In Step 11 of over the encrypted VPN tunnel. Step 2 Click Next to the Internet... instead of the VPN Wizard, review the configuration attributes for the VPN tunnel you just created. Chapter 3 Scenario: IPsec Remote-Access VPN Configuration Implementing the...
... similar to the following: 78-17645-01 PIX 515E Security Appliance Getting Started Guide 3-17 The displayed configuration should be sent out directly to continue. Verifying the Remote-Access VPN Configuration In Step 11 of over the encrypted VPN tunnel. Step 2 Click Next to the Internet... instead of the VPN Wizard, review the configuration attributes for the VPN tunnel you just created. Chapter 3 Scenario: IPsec Remote-Access VPN Configuration Implementing the...
Getting Started Guide
Page 63
...-cost public Internet connections to -Site VPN Network Topology Figure 4-1 shows an example VPN tunnel between the two sites. A VPN connection enables you to send data from one location to another over a secure connection..., or tunnel, first by authenticating both ends of the VPN Connection, page 4-13 • What to Do Next, ... provided by automatically encrypting all data sent between two security appliances. 78-17645-01 PIX 515E Security Appliance Getting Started Guide 4-1 Site-to -site VPN.
...-cost public Internet connections to -Site VPN Network Topology Figure 4-1 shows an example VPN tunnel between the two sites. A VPN connection enables you to send data from one location to another over a secure connection..., or tunnel, first by authenticating both ends of the VPN Connection, page 4-13 • What to Do Next, ... provided by automatically encrypting all data sent between two security appliances. 78-17645-01 PIX 515E Security Appliance Getting Started Guide 4-1 Site-to -site VPN.
Getting Started Guide
Page 64
....20.20.0 132066 Creating a VPN site-to-site deployment such as the one on each side of remote hosts and networks permitted to use the tunnel to communicate with resources on the remote site • IP addresses of the connection. Implementing the Site-to-Site Scenario This section describes how to..., gather the following information: • IP address of the remote security appliance peer • IP addresses of local hosts and networks permitted to use the tunnel to communicate with local resources PIX 515E Security Appliance Getting Started Guide 4-2 78-17645-01
....20.20.0 132066 Creating a VPN site-to-site deployment such as the one on each side of remote hosts and networks permitted to use the tunnel to communicate with resources on the remote site • IP addresses of the connection. Implementing the Site-to-Site Scenario This section describes how to..., gather the following information: • IP address of the remote security appliance peer • IP addresses of local hosts and networks permitted to use the tunnel to communicate with local resources PIX 515E Security Appliance Getting Started Guide 4-2 78-17645-01
Getting Started Guide
Page 67
Click the Site-to continue. 78-17645-01 PIX 515E Security Appliance Getting Started Guide 4-5 Click Next to -Site VPN radio button. From the drop-down list, choose Outside as the enabled interface for the current VPN tunnel. Chapter 4 Scenario: Site-to-Site VPN Configuration Implementing the Site-to -site IPsec connectivity. Note The Site-to-Site VPN option connects two IPsec security gateways, which can include security appliances, VPN concentrators, or other devices that support site-to -Site Scenario In Step 1 of the VPN Wizard, perform the following steps: a. c. b.
Click the Site-to continue. 78-17645-01 PIX 515E Security Appliance Getting Started Guide 4-5 Click Next to -Site VPN radio button. From the drop-down list, choose Outside as the enabled interface for the current VPN tunnel. Chapter 4 Scenario: Site-to-Site VPN Configuration Implementing the Site-to -site IPsec connectivity. Note The Site-to-Site VPN option connects two IPsec security gateways, which can include security appliances, VPN concentrators, or other devices that support site-to -Site Scenario In Step 1 of the VPN Wizard, perform the following steps: a. c. b.
Getting Started Guide
Page 68
...radio button to as Security Appliance 2 from the drop-down list, and then choose a preconfigured trustpoint name from this point forward. PIX 515E Security Appliance Getting Started Guide 4-6 78-17645-01 Implementing the Site-to-Site Scenario Chapter 4 Scenario: Site-to-Site VPN Configuration...the other two options. This key is Security Appliance 1. Note In this scenario 209.165.200.236) and a Tunnel Group Name (for example, "Cisco"). Note When you use digital certificates for IPsec negotiations between the security appliances. Be sure to enter the same ...
...radio button to as Security Appliance 2 from the drop-down list, and then choose a preconfigured trustpoint name from this point forward. PIX 515E Security Appliance Getting Started Guide 4-6 78-17645-01 Implementing the Site-to-Site Scenario Chapter 4 Scenario: Site-to-Site VPN Configuration...the other two options. This key is Security Appliance 1. Note In this scenario 209.165.200.236) and a Tunnel Group Name (for example, "Cisco"). Note When you use digital certificates for IPsec negotiations between the security appliances. Be sure to enter the same ...
Getting Started Guide
Page 69
... (DES/3DES/AES), authentication algorithms (MD5/SHA), and the Diffie-Hellman group (1/2/5) used by the security appliance during an IKE security association. 78-17645-01 PIX 515E Security Appliance Getting Started Guide 4-7 In Step 3 of the peers. Configuring the IKE Policy IKE is also an authentication method to protect data and ensure... values are sufficient to continue. Chapter 4 Scenario: Site-to-Site VPN Configuration Implementing the Site-to-Site Scenario Step 3 Click Next to establish secure VPN tunnels between two peers.
... (DES/3DES/AES), authentication algorithms (MD5/SHA), and the Diffie-Hellman group (1/2/5) used by the security appliance during an IKE security association. 78-17645-01 PIX 515E Security Appliance Getting Started Guide 4-7 In Step 3 of the peers. Configuring the IKE Policy IKE is also an authentication method to protect data and ensure... values are sufficient to continue. Chapter 4 Scenario: Site-to-Site VPN Configuration Implementing the Site-to-Site Scenario Step 3 Click Next to establish secure VPN tunnels between two peers.