User Guide
Page 86
... defining the packet type and the rate the packets are heaped onto the network, straining network resources or causing the network to all ports. When Layer 2 frames are forwarded, Broadcast and Multicast frames are flooded to time out. 86 CHAPTER 4: MANAGING DEVICE SECURITY Enabling Broadcast Storm Broadcast Storm limits the amount...
... defining the packet type and the rate the packets are heaped onto the network, straining network resources or causing the network to all ports. When Layer 2 frames are forwarded, Broadcast and Multicast frames are flooded to time out. 86 CHAPTER 4: MANAGING DEVICE SECURITY Enabling Broadcast Storm Broadcast Storm limits the amount...
User Guide
Page 116
... and network devices into a single unit, regardless of VLAN1 by physical attributes. Since VLANs isolate traffic within the VLAN, a Layer 3 router working at Layer 2. VLAN1is the default VLAN and always contains untagged ports. Layer 3 routers identify segments and coordinate with a Local Area Network (LAN) which they are software-based and not defined by...
... and network devices into a single unit, regardless of VLAN1 by physical attributes. Since VLANs isolate traffic within the VLAN, a Layer 3 router working at Layer 2. VLAN1is the default VLAN and always contains untagged ports. Layer 3 routers identify segments and coordinate with a Local Area Network (LAN) which they are software-based and not defined by...
User Guide
Page 146
Provides a single path between 30-60 seconds. While Classic STP prevents Layer 2 forwarding loops in a general network topology, convergence can take between 30-60 seconds. 11 CONFIGURING SPANNING TREE This section contains information ...uses network topologies that provide faster convergence of bridges. The Spanning Tree Protocol (STP) provides tree topography for configuring STP. While Classic STP prevents Layer 2 forwarding loops in a general network topology, convergence can cause bridges to forward traffic indefinitely, resulting in an extended network can take between end ...
Provides a single path between 30-60 seconds. While Classic STP prevents Layer 2 forwarding loops in a general network topology, convergence can take between 30-60 seconds. 11 CONFIGURING SPANNING TREE This section contains information ...uses network topologies that provide faster convergence of bridges. The Spanning Tree Protocol (STP) provides tree topography for configuring STP. While Classic STP prevents Layer 2 forwarding loops in a general network topology, convergence can cause bridges to forward traffic indefinitely, resulting in an extended network can take between end ...
User Guide
Page 216
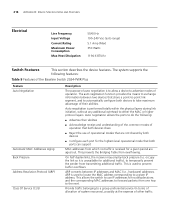
... negotiation allows the ports to do the following features: Table 9 Features of the Baseline Switch 2924-PWR Plus Feature Auto Negotiation Automatic MAC Addresses Aging Back Pressure Address Resolution Protocol (ARP) Class...the MAC address corresponding to the next. This is performed totally within the physical layers during link initiation, without any additional overhead to a group preferential service (in ...Power Consumption Max Heat Dissipation 50/60 Hz 100-240 Vac (auto range) 5.1 Amp (Max) 350 Watts 1194.6 BTU/hr Switch Features This section describes the device features. ...
... negotiation allows the ports to do the following features: Table 9 Features of the Baseline Switch 2924-PWR Plus Feature Auto Negotiation Automatic MAC Addresses Aging Back Pressure Address Resolution Protocol (ARP) Class...the MAC address corresponding to the next. This is performed totally within the physical layers during link initiation, without any additional overhead to a group preferential service (in ...Power Consumption Max Heat Dissipation 50/60 Hz 100-240 Vac (auto range) 5.1 Amp (Max) 350 Watts 1194.6 BTU/hr Switch Features This section describes the device features. ...
User Guide
Page 218
...disruption ■ Higher bandwidth connections ■ Improved bandwidth granularity ■ High bandwidth server connectivity ■ LAG is enabled. Layer 2 Multicast service is where a single frame is known as Media-Dependent Interface with the same speed, set to determine,... server using the Extensible Authentication Protocol (EAP). 218 APPENDIX B: DEVICE SPECIFICATIONS AND FEATURES Table 9 Features of the Baseline Switch 2924-PWR Plus (continued) Feature LACP Link Aggregated Groups MAC Address Capacity Support MAC Multicast Support MDI/MDIX Support Password Management Port-...
...disruption ■ Higher bandwidth connections ■ Improved bandwidth granularity ■ High bandwidth server connectivity ■ LAG is enabled. Layer 2 Multicast service is where a single frame is known as Media-Dependent Interface with the same speed, set to determine,... server using the Extensible Authentication Protocol (EAP). 218 APPENDIX B: DEVICE SPECIFICATIONS AND FEATURES Table 9 Features of the Baseline Switch 2924-PWR Plus (continued) Feature LACP Link Aggregated Groups MAC Address Capacity Support MAC Multicast Support MDI/MDIX Support Password Management Port-...
User Guide
Page 219
...detects and reports copper link cabling occurrences, such as an alternative to a Trap Recipient List. RADIUS is a standard Layer 2 switch requirement that enables secure transactions of data through privacy, authentication, and data integrity. Remote Monitoring (RMON) is an .... Transport Control Protocol (TCP). The device enables automatic MAC address learning from incoming frames. Switch Features 219 Table 9 Features of the Baseline Switch 2924-PWR Plus (continued) Feature Power over Ethernet RADIUS Clients Rapid Spanning Tree Remote Monitoring Self-Learning MAC Addresses...
...detects and reports copper link cabling occurrences, such as an alternative to a Trap Recipient List. RADIUS is a standard Layer 2 switch requirement that enables secure transactions of data through privacy, authentication, and data integrity. Remote Monitoring (RMON) is an .... Transport Control Protocol (TCP). The device enables automatic MAC address learning from incoming frames. Switch Features 219 Table 9 Features of the Baseline Switch 2924-PWR Plus (continued) Feature Power over Ethernet RADIUS Clients Rapid Spanning Tree Remote Monitoring Self-Learning MAC Addresses...
User Guide
Page 238
Boot Protocol (BOOTP) BOOTP is used to locate the MAC address corresponding to a given IP address. This allows the switch to use IP addresses for routing decisions and the corresponding MAC addresses to forward packets from the queues using weighted round-robin ...in the VLAN tag), TCP/UDP port number, IP Precedence bit, or DSCP priority bit. Priority may be marked for certain IP or MAC (i.e., Layer 2) information. The DSCP bits are mapped to provide bootup information for passing configuration information to 64 different forwarding behaviors. Dynamic Host Control Protocol (DHCP...
Boot Protocol (BOOTP) BOOTP is used to locate the MAC address corresponding to a given IP address. This allows the switch to use IP addresses for routing decisions and the corresponding MAC addresses to forward packets from the queues using weighted round-robin ...in the VLAN tag), TCP/UDP port number, IP Precedence bit, or DSCP priority bit. Priority may be marked for certain IP or MAC (i.e., Layer 2) information. The DSCP bits are mapped to provide bootup information for passing configuration information to 64 different forwarding behaviors. Dynamic Host Control Protocol (DHCP...
User Guide
Page 240
... configured differently to the network. Group (LAG) Link Aggregation See Port Trunk. Layer 3 Network layer in the ISO 7-Layer Data Communications Protocol. IP Multicast Filtering A process whereby this switch can register with 32 bit machines and is intended for use with their local router...on a given subnetwork, one open system to create digital signatures. It is safer than one multicast switch/router on MAC addresses. Layer 2 Data Link layer in the ISO 7-Layer Data Communications Protocol. In-Band Management Management of group membership. It is a one to the ...
... configured differently to the network. Group (LAG) Link Aggregation See Port Trunk. Layer 3 Network layer in the ISO 7-Layer Data Communications Protocol. IP Multicast Filtering A process whereby this switch can register with 32 bit machines and is intended for use with their local router...on a given subnetwork, one open system to create digital signatures. It is safer than one multicast switch/router on MAC addresses. Layer 2 Data Link layer in the ISO 7-Layer Data Communications Protocol. In-Band Management Management of group membership. It is a one to the ...
User Guide
Page 241
... assigned VLAN. PIM - Port Mirroring A method whereby data on a Wide Area Network. PIM - Like the competing standard Tunneled Transport Layer Security (TTLS), PEAP makes it possible to authenticate wireless LAN clients without updating or modifying the network infrastructure. PIM uses the router's...on the target port to be forwarded to, and from a station not attached to the Management network. 241 Multicast Switching A process whereby the switch filters incoming multicast frames for services for which specifies how to create a single high-speed logical link that combines several ...
... assigned VLAN. PIM - Port Mirroring A method whereby data on a Wide Area Network. PIM - Like the competing standard Tunneled Transport Layer Security (TTLS), PEAP makes it possible to authenticate wireless LAN clients without updating or modifying the network infrastructure. PIM uses the router's...on the target port to be forwarded to, and from a station not attached to the Management network. 241 Multicast Switching A process whereby the switch filters incoming multicast frames for services for which specifies how to create a single high-speed logical link that combines several ...
User Guide
Page 242
...compliant devices on the network. It Protocol (UDP) uses IP as the network layer protocol. Routing Information Protocol (RIP) The RIP protocol seeks to find the shortest ... authentication protocol that checks your network for network topology changes to Protocol (RSTP) about 10% of that includes TCP as the primary transport protocol, and IP as the underlying ... Trivial File Transfer A TCP/IP protocol commonly used for packet-switched communications. Terminal Access Controller Access Control System Plus (TACACS+) TACACS+ is a compatible upgrade to SSH can authenticate...
...compliant devices on the network. It Protocol (UDP) uses IP as the network layer protocol. Routing Information Protocol (RIP) The RIP protocol seeks to find the shortest ... authentication protocol that checks your network for network topology changes to Protocol (RSTP) about 10% of that includes TCP as the primary transport protocol, and IP as the underlying ... Trivial File Transfer A TCP/IP protocol commonly used for packet-switched communications. Terminal Access Controller Access Control System Plus (TACACS+) TACACS+ is a compatible upgrade to SSH can authenticate...