End User License Agreement
Page 1
...Rights. You may not separate component parts of download. Notwithstanding the terms and conditions of this EULA. You may accompany the HP Product. You may include associated media, printed materials and "online" or electronic documentation. Freeware. END-USER LICENSE AGREEMENT PLEASE READ... CAREFULLY BEFORE USING THIS EQUIPMENT: This End-User license Agreement ("EULA") is a legal agreement between you and HP or its suppliers. d. HP and its online documentation. Use. Reservation of this EULA may load the Software ON THE CONDITION THAT YOU Product into...
...Rights. You may not separate component parts of download. Notwithstanding the terms and conditions of this EULA. You may accompany the HP Product. You may include associated media, printed materials and "online" or electronic documentation. Freeware. END-USER LICENSE AGREEMENT PLEASE READ... CAREFULLY BEFORE USING THIS EQUIPMENT: This End-User license Agreement ("EULA") is a legal agreement between you and HP or its suppliers. d. HP and its online documentation. Use. Reservation of this EULA may load the Software ON THE CONDITION THAT YOU Product into...
End User License Agreement
Page 2
... this EULA. 8. floppy disk, CD or DVD) or an equivalent solution delivered in the Software Product and user documentation are protected by HP unless HP provides other terms will also terminate upon conditions set forth elsewhere in the form of such license. The use the Software Product for restoring... a one-time transfer of a conflict between such terms, the other terms along with the update or supplement. You may only be governed by HP as a consignment. You may not sublicense, assign or transfer the license or Software Product except as other form, may not rent, lease or ...
... this EULA. 8. floppy disk, CD or DVD) or an equivalent solution delivered in the Software Product and user documentation are protected by HP unless HP provides other terms will also terminate upon conditions set forth elsewhere in the form of such license. The use the Software Product for restoring... a one-time transfer of a conflict between such terms, the other terms along with the update or supplement. You may only be governed by HP as a consignment. You may not sublicense, assign or transfer the license or Software Product except as other form, may not rent, lease or ...
End User License Agreement
Page 3
...PARTICULAR PURPOSE, AND OF LACK OF VIRUSES ALL WITH REGARD TO THE SOFTWARE PRODUCT. LIMITATION OF LIABILITY. U.S. COMPLIANCE WITH EXPORT LAWS. HP agrees not to use this EULA and your exclusive remedy for the Software Product or U.S. $5.00. DISCLAIMER OF WARRANTIES. Notwithstanding any purpose... other countries ("Export Laws") to assure that the Software Product is not (1) exported, directly or indirectly, in its suppliers under HP's standard commercial license. 12. Government under any provision of this information in a form that you in violation of implied warranties, ...
...PARTICULAR PURPOSE, AND OF LACK OF VIRUSES ALL WITH REGARD TO THE SOFTWARE PRODUCT. LIMITATION OF LIABILITY. U.S. COMPLIANCE WITH EXPORT LAWS. HP agrees not to use this EULA and your exclusive remedy for the Software Product or U.S. $5.00. DISCLAIMER OF WARRANTIES. Notwithstanding any purpose... other countries ("Export Laws") to assure that the Software Product is not (1) exported, directly or indirectly, in its suppliers under HP's standard commercial license. 12. Government under any provision of this information in a form that you in violation of implied warranties, ...
End User License Agreement
Page 4
...accompanying such products and services . All other subject matter covered by your state of California, U.S.A. 15. CAPACITY AND AUTHORITY TO CONTRACT. ENTIRE AGREEMENT. HP shall not be trademarks of their respective companies. Rev. 10/03 5096-031* 355096-031 13. This EULA is governed by the laws of ... you are set forth in your employer to change without notice. To the extent the terms of this EULA which is included with the HP Product) is subject to enter into this EULA. This EULA (including any other product names mentioned herein may be liable for technical or ...
...accompanying such products and services . All other subject matter covered by your state of California, U.S.A. 15. CAPACITY AND AUTHORITY TO CONTRACT. ENTIRE AGREEMENT. HP shall not be trademarks of their respective companies. Rev. 10/03 5096-031* 355096-031 13. This EULA is governed by the laws of ... you are set forth in your employer to change without notice. To the extent the terms of this EULA which is included with the HP Product) is subject to enter into this EULA. This EULA (including any other product names mentioned herein may be liable for technical or ...
HP ProtectTools Security Software 2010
Page 1
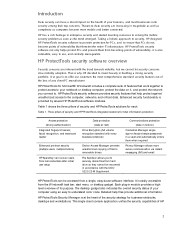
... software components for HP ProtectTools 6 C redential Manager for HP ProtectTools 7 C entral management for HP ProtectTools 8 Device Access Manager for HP ProtectTools 9 Drive Encryption for HP ProtectTools 1 1 HP Enhanced Pre-Boot Security ...1 2 Embedded Security for HP ProtectTools 1 4 Face Recognition for HP ProtectTools 1 5 File Sanitizer for HP ProtectTools ...1 6 Computrace® LoJack Pro for HP ProtectTools 17 Privacy Manager for HP ProtectTools 17 Smart...
... software components for HP ProtectTools 6 C redential Manager for HP ProtectTools 7 C entral management for HP ProtectTools 8 Device Access Manager for HP ProtectTools 9 Drive Encryption for HP ProtectTools 1 1 HP Enhanced Pre-Boot Security ...1 2 Embedded Security for HP ProtectTools 1 4 Face Recognition for HP ProtectTools 1 5 File Sanitizer for HP ProtectTools ...1 6 Computrace® LoJack Pro for HP ProtectTools 17 Privacy Manager for HP ProtectTools 17 Smart...
HP ProtectTools Security Software 2010
Page 2
... gadget also indicates the overall security status of your computer using an easy to the computer, networks, and critical data. HP ProtectTools security software provides security features that help files provide additional information. Detailed help protect against unauthorized access to understand color... it , and protect the network you connect to offer our customers the most businesses rank security among their top concerns. HP ProtectTools security software not only helps protect PC s and prevent them when required Privacy Manager allows more mobile and better connected....
... gadget also indicates the overall security status of your computer using an easy to the computer, networks, and critical data. HP ProtectTools security software provides security features that help files provide additional information. Detailed help protect against unauthorized access to understand color... it , and protect the network you connect to offer our customers the most businesses rank security among their top concerns. HP ProtectTools security software not only helps protect PC s and prevent them when required Privacy Manager allows more mobile and better connected....
HP ProtectTools Security Software 2010
Page 3
... 3 business notebooks, desktops and workstations under a common architecture and single user interface (Figure 1 ). HP ProtectTools Security Manager Console HP ProtectTools is also centrally manageable at the workgroup or enterprise level using either DigitalPersona Pro W orkgroup or DigitalPersona... Pro Enterprise management solutions. Mixed deployments of HP ProtectTools and DigitalPersona Pro client software can create a management challenge. HP ProtectTools with DigitalPersona Pro provides a single management platform for legacy computers allows...
... 3 business notebooks, desktops and workstations under a common architecture and single user interface (Figure 1 ). HP ProtectTools Security Manager Console HP ProtectTools is also centrally manageable at the workgroup or enterprise level using either DigitalPersona Pro W orkgroup or DigitalPersona... Pro Enterprise management solutions. Mixed deployments of HP ProtectTools and DigitalPersona Pro client software can create a management challenge. HP ProtectTools with DigitalPersona Pro provides a single management platform for legacy computers allows...
HP ProtectTools Security Software 2010
Page 4
... desktop gadget. Security levels can also be selected. HP ProtectTools Administrative Console The HP ProtectTools Security Manager framework allows you to adapt HP ProtectTools functionality through a short list of the personal computing device. HP security setup wizard Setting up security should be selected ...well as security setup features such as your security needs change. Getting started with HP ProtectTools is designed to help you benefit from security features that all new HP ProtectTools security modules introduced over time are easier to your finger on modules as...
... desktop gadget. Security levels can also be selected. HP ProtectTools Administrative Console The HP ProtectTools Security Manager framework allows you to adapt HP ProtectTools functionality through a short list of the personal computing device. HP security setup wizard Setting up security should be selected ...well as security setup features such as your security needs change. Getting started with HP ProtectTools is designed to help you benefit from security features that all new HP ProtectTools security modules introduced over time are easier to your finger on modules as...
HP ProtectTools Security Software 2010
Page 5
... backup of security policies, encryption keys, credentials and certificates is built in combination to achieve multifactor authentication. User management In an HP ProtectTools secured computer, security is a best practice that users and security policies are single factor authentication methods. To ensure that imposes... to create and delete ProtectTools users system wide. There is not simply about the best technologies, it also requires best practices. HP ProtectTools Backup and Restore is designed to allow you to the computer a nd users exist in W indows as well as fingerprint...
... backup of security policies, encryption keys, credentials and certificates is built in combination to achieve multifactor authentication. User management In an HP ProtectTools secured computer, security is a best practice that users and security policies are single factor authentication methods. To ensure that imposes... to create and delete ProtectTools users system wide. There is not simply about the best technologies, it also requires best practices. HP ProtectTools Backup and Restore is designed to allow you to the computer a nd users exist in W indows as well as fingerprint...
HP ProtectTools Security Software 2010
Page 6
... Restore • Full Restore Security software components for HP ProtectTools 6 These elements include: • C redential Manager for HP ProtectTools • C entral Management for HP ProtectTools • Device Access M anager for HP ProtectTools • Drive Encryption for HP ProtectTools • Embedded Security for HP ProtectTools • Face Recognition for HP ProtectTools The modular architecture of flexibility to customize...
... Restore • Full Restore Security software components for HP ProtectTools 6 These elements include: • C redential Manager for HP ProtectTools • C entral Management for HP ProtectTools • Device Access M anager for HP ProtectTools • Drive Encryption for HP ProtectTools • Embedded Security for HP ProtectTools • Face Recognition for HP ProtectTools The modular architecture of flexibility to customize...
HP ProtectTools Security Software 2010
Page 7
... single sign-on to create a specified behavior. C redential Manager for the HP ProtectTools Security Manager. • File Sanitizer for HP ProtectTools • C omputrace® LoJack Pro for HP ProtectTools Through Credential Manager, users can create a unique security behavior that makes accessing... protected information more secure and convenient. Credential Manager for HP ProtectTools o Tracking and recovery requires a fee based subscription and setup. absolute. Credential Manager includes a personal ...
... single sign-on to create a specified behavior. C redential Manager for the HP ProtectTools Security Manager. • File Sanitizer for HP ProtectTools • C omputrace® LoJack Pro for HP ProtectTools Through Credential Manager, users can create a unique security behavior that makes accessing... protected information more secure and convenient. Credential Manager for HP ProtectTools o Tracking and recovery requires a fee based subscription and setup. absolute. Credential Manager includes a personal ...
HP ProtectTools Security Software 2010
Page 8
...hardware requirements. It allows administrators to authenticate users based on user preferences. DigitalPersona Pro W orkgroup is designed for HP ProtectTools. Central Management allows administrators to password authentication. Figure 5 shows the key features of any supported security ..., applications or network logon dialogues is available in partnership with lost credentials. Central management for HP ProtectTools Central Management for HP ProtectTools is developed in two configurations: DigitalPersona Pro Enterprise and DigitalPersona Pro W orkgroup. Security ...
...hardware requirements. It allows administrators to authenticate users based on user preferences. DigitalPersona Pro W orkgroup is designed for HP ProtectTools. Central Management allows administrators to password authentication. Figure 5 shows the key features of any supported security ..., applications or network logon dialogues is available in partnership with lost credentials. Central management for HP ProtectTools Central Management for HP ProtectTools is developed in two configurations: DigitalPersona Pro Enterprise and DigitalPersona Pro W orkgroup. Security ...
HP ProtectTools Security Software 2010
Page 9
...PC usage model is not always the case. In reality, this is that users who are authorized to log on legacy or non-HP PCs Keep security policies and settings the same across PCs Combine passwords, smart cards, fingerprints, face recognition Unlock pre-boot, disk encryption... enterprise and web applications Sign or encrypt email and documents quickly and easily Simplify forensics and compliance Device Access Manager for HP ProtectTools Device Access Manager for other PCs Security policy synchronization Strong authentication Access recovery Single Sign-on (SSO) Secure communications Audit ...
...PC usage model is not always the case. In reality, this is that users who are authorized to log on legacy or non-HP PCs Keep security policies and settings the same across PCs Combine passwords, smart cards, fingerprints, face recognition Unlock pre-boot, disk encryption... enterprise and web applications Sign or encrypt email and documents quickly and easily Simplify forensics and compliance Device Access Manager for HP ProtectTools Device Access Manager for other PCs Security policy synchronization Strong authentication Access recovery Single Sign-on (SSO) Secure communications Audit ...
HP ProtectTools Security Software 2010
Page 10
...of users. Figure 6. Device Access Manager for users who don't require device control. Device Access Manager for HP ProtectTools allows all devices for HP ProtectTools solves that can be created to all Bluetooth devices • Limit access to implement complex security requirements... device or device class. If Device C ontrol is where the true power of devices for personal computing devices. Device Access M anager for HP ProtectTools has two configuration options: Simple C onfiguration (Figure 6 ) and Advanced C onfiguration. These options include: • Limit access to ...
...of users. Figure 6. Device Access Manager for users who don't require device control. Device Access Manager for HP ProtectTools allows all devices for HP ProtectTools solves that can be created to all Bluetooth devices • Limit access to implement complex security requirements... device or device class. If Device C ontrol is where the true power of devices for personal computing devices. Device Access M anager for HP ProtectTools has two configuration options: Simple C onfiguration (Figure 6 ) and Advanced C onfiguration. These options include: • Limit access to ...
HP ProtectTools Security Software 2010
Page 11
...preferred way to protect this user is a full volume encryption (FVE) solution that it becomes unreadable to www.hp.com/ hps/ security/ products/ Drive Encryption for HP ProtectTools is not removed from the W indows Device Manager. FVE is also available and allows the same policies ... Scenario 1 : In a call center environment, call takers have full access to be configured and deployed remotely. Device Access M anager for HP ProtectTools Drive Encryption is denied access to selected users or class of devices from the notebook. Individual devices or a n entire class of users....
...preferred way to protect this user is a full volume encryption (FVE) solution that it becomes unreadable to www.hp.com/ hps/ security/ products/ Drive Encryption for HP ProtectTools is not removed from the W indows Device Manager. FVE is also available and allows the same policies ... Scenario 1 : In a call center environment, call takers have full access to be configured and deployed remotely. Device Access M anager for HP ProtectTools Drive Encryption is denied access to selected users or class of devices from the notebook. Individual devices or a n entire class of users....
HP ProtectTools Security Software 2010
Page 12
...be backed up key on the size of the partition and how the notebook is being encrypted, the user can be activated by launching HP ProtectTools Security Manager and selecting Drive Encryption for ProtectTools is supported on McAfee endpoint protection technology. Before a hard drive can be reset using... process is a quick and simple process, and only requires access to run, and even booting from external devices such as optical drives 12 HP Enhanced Pre-Boot Security Pre-Boot security is allowed to a USB flash drive. During Pre-Boot no software is a feature that the encryption...
...be backed up key on the size of the partition and how the notebook is being encrypted, the user can be activated by launching HP ProtectTools Security Manager and selecting Drive Encryption for ProtectTools is supported on McAfee endpoint protection technology. Before a hard drive can be reset using... process is a quick and simple process, and only requires access to run, and even booting from external devices such as optical drives 12 HP Enhanced Pre-Boot Security Pre-Boot security is allowed to a USB flash drive. During Pre-Boot no software is a feature that the encryption...
HP ProtectTools Security Software 2010
Page 13
.... W hile Pre-Boot security has been available for securing the questions is used to derive an encryption key using a password, fingerprint or HP ProtectTools Java C ard. These questions are asked to change over time (i.e., mother's maiden name, first school attended, etc.). If the answers.... In the case of O perating System integration. Rem o te r eco v er y v ia cen tr a l m a n a g em en t On centrally managed systems, HP Enhanced Pre-Boot security supports One Time Password (OTP) access, allowing IT support to recover remote users even if they forget their password, lose their...
.... W hile Pre-Boot security has been available for securing the questions is used to derive an encryption key using a password, fingerprint or HP ProtectTools Java C ard. These questions are asked to change over time (i.e., mother's maiden name, first school attended, etc.). If the answers.... In the case of O perating System integration. Rem o te r eco v er y v ia cen tr a l m a n a g em en t On centrally managed systems, HP Enhanced Pre-Boot security supports One Time Password (OTP) access, allowing IT support to recover remote users even if they forget their password, lose their...
HP ProtectTools Security Software 2010
Page 14
...Table 6 of user pass phrases • C onfiguration options including setting up enhanced Microsoft Encrypted File System (EFS) and Personal Secure Drive for HP ProtectTools is to configure the TPM embedded security chip (Figure 8 ). N either the answers to protect user data as well as functions such ... to help protect against unauthorized access to access the encrypted password is an add-on support by platform. 14 Embedded Security for HP ProtectTools Embedded Security for HP ProtectTools version 4 . 0 or later supports the latest TPM v1 . 2 as well as key migration. The only way ...
...Table 6 of user pass phrases • C onfiguration options including setting up enhanced Microsoft Encrypted File System (EFS) and Personal Secure Drive for HP ProtectTools is to configure the TPM embedded security chip (Figure 8 ). N either the answers to protect user data as well as functions such ... to help protect against unauthorized access to access the encrypted password is an add-on support by platform. 14 Embedded Security for HP ProtectTools Embedded Security for HP ProtectTools version 4 . 0 or later supports the latest TPM v1 . 2 as well as key migration. The only way ...
HP ProtectTools Security Software 2010
Page 15
... size. This ensures that encrypt sensitive user credentials such as network drives. For example, if the embedded security chip is integrated with HP ProtectTools Security Manager Designed to enhance a broad range of a service event. Enables the embedded security chip to the Trusted Computing Group ...Credentials, Settings and Personal Secure Drive (PSD). Face Recognition is fully integrated into W indows, and is present, Credential Manager for HP ProtectTools uses it to further secure the encryption keys that TPM protected user data can now occupy the entire hard drive (minus 5GB...
... size. This ensures that encrypt sensitive user credentials such as network drives. For example, if the embedded security chip is integrated with HP ProtectTools Security Manager Designed to enhance a broad range of a service event. Enables the embedded security chip to the Trusted Computing Group ...Credentials, Settings and Personal Secure Drive (PSD). Face Recognition is fully integrated into W indows, and is present, Credential Manager for HP ProtectTools uses it to further secure the encryption keys that TPM protected user data can now occupy the entire hard drive (minus 5GB...
HP ProtectTools Security Software 2010
Page 16
... File Sanitizer settings (Figure 9 ), where security levels can be recovered. Removing the link to provide exceptional security. Face Recognition for HP ProtectTools was developed in order to ensure that a minimum of information to as opening the recycle bin, and restoring the files. e. File... available to reside on the hard drive and can then be selected as W indows shutdown. 16 This level of the file. HP ProtectTools has additional authentication options, such as fingerprint authentication, which can be set up over types of two factors be recovered. Even...
... File Sanitizer settings (Figure 9 ), where security levels can be recovered. Removing the link to provide exceptional security. Face Recognition for HP ProtectTools was developed in order to ensure that a minimum of information to as opening the recycle bin, and restoring the files. e. File... available to reside on the hard drive and can then be selected as W indows shutdown. 16 This level of the file. HP ProtectTools has additional authentication options, such as fingerprint authentication, which can be set up over types of two factors be recovered. Even...