Product Manual
Page 10
... OSPF Objects 179 4.13. Transparent Mode Scenario 2 215 4.22. Deploying an ALG 240 6.2. Anonymizing with Partitioned Backbone 178 4.12. LDAP for ISP Access 152 4.4. FwdFast Rules Bypass Traffic Shaping 447 10.3. Minimum and Maximum Pipe Precedence 453 10.6. Simplified... Address Translation 196 4.15. Non-transparent Mode Internet Access 212 4.19. Dynamic Content Filtering Flow 296 6.9. Virtual Links Connecting Areas 177 4.11. Using Local IP Address with CHAP, MS-CHAPv1 or MS-CHAPv2 366 9.1. OSPF Providing Route Redundancy 173 4.10. A Simple OSPF...
... OSPF Objects 179 4.13. Transparent Mode Scenario 2 215 4.22. Deploying an ALG 240 6.2. Anonymizing with Partitioned Backbone 178 4.12. LDAP for ISP Access 152 4.4. FwdFast Rules Bypass Traffic Shaping 447 10.3. Minimum and Maximum Pipe Precedence 453 10.6. Simplified... Address Translation 196 4.15. Non-transparent Mode Internet Access 212 4.19. Dynamic Content Filtering Flow 296 6.9. Virtual Links Connecting Areas 177 4.11. Using Local IP Address with CHAP, MS-CHAPv1 or MS-CHAPv2 366 9.1. OSPF Providing Route Redundancy 173 4.10. A Simple OSPF...
Product Manual
Page 12
... Remote Access 38 2.3. Listing Modified Configuration Objects 53 2.10. Adding an IP Network 78 3.3. Creating an Interface Group 107 3.13. Uploading a Certificate 130 3.19. Displaying the Core Routes 150 4.3. Address Translation 198 12 Defining a Static ARP Entry 110 3.16. Enabling the D-Link NTP Server 136 3.28. Adding a Configuration Object 52 2.7. Setting the Current...
... Remote Access 38 2.3. Listing Modified Configuration Objects 53 2.10. Adding an IP Network 78 3.3. Creating an Interface Group 107 3.13. Uploading a Certificate 130 3.19. Displaying the Core Routes 150 4.3. Address Translation 198 12 Defining a Static ARP Entry 110 3.16. Enabling the D-Link NTP Server 136 3.28. Adding a Configuration Object 52 2.7. Setting the Current...
Product Manual
Page 13
... 6.15. if1 Configuration 202 4.16. Setting up a Self-signed Certificate based VPN tunnel for Scenario 1 214 4.18. Creating an IP Pool 235 6.1. H.323 with IPsec Tunnels 413 9.9. Enabling Dynamic Web Content Filtering 297 6.16. Translating Traffic to the Whitelist 332 ...7.1. Setting up a DHCP Relayer 230 5.5. Setting up an L2TP server 427 9.12. H.323 with private IP addresses 279 6.6. Configuring an SMTP Log Receiver 323 6.21. Setting up CA Server Certificate based VPN tunnels for Scenario ...
... 6.15. if1 Configuration 202 4.16. Setting up a Self-signed Certificate based VPN tunnel for Scenario 1 214 4.18. Creating an IP Pool 235 6.1. H.323 with IPsec Tunnels 413 9.9. Enabling Dynamic Web Content Filtering 297 6.16. Translating Traffic to the Whitelist 332 ...7.1. Setting up a DHCP Relayer 230 5.5. Setting up an L2TP server 427 9.12. H.323 with private IP addresses 279 6.6. Configuring an SMTP Log Receiver 323 6.21. Setting up CA Server Certificate based VPN tunnels for Scenario ...
Product Manual
Page 42
...the NetDefend Firewall. For example, the ping command will be : > script -execute -name=my_script.sgs 126.12.11.01 "If1 address" When the script file runs, the variable replacement would mean that the name of the... validated. 2.1.5. Note: The symbol $0 is reserved Notice that the file becomes: add IP4Address If1_ip Address=126.12.11.01 Comments="If1 address" Script Validation and Command Ordering CLI scripts are called my_script.sgs is to be ... it is often preferable to then this can be executed with IP address 126.12.11.01 replacing all occurrences of the script file itself.
...the NetDefend Firewall. For example, the ping command will be : > script -execute -name=my_script.sgs 126.12.11.01 "If1 address" When the script file runs, the variable replacement would mean that the name of the... validated. 2.1.5. Note: The symbol $0 is reserved Notice that the file becomes: add IP4Address If1_ip Address=126.12.11.01 Comments="If1 address" Script Validation and Command Ordering CLI scripts are called my_script.sgs is to be ... it is often preferable to then this can be executed with IP address 126.12.11.01 replacing all occurrences of the script file itself.
Product Manual
Page 58
...NMS about a change of the firewall) is used to alter the state of a managed device and a Trap which are used by D-Link and defines the SNMP objects and data types that the correct file is used . The system generating the trap • Severity - Make...MIB file for communicating between a Network Management System (NMS) and a managed device. 2.2.6. Sending SNMP Traps to an SNMP trap receiver with an IP address of NetDefend Firewall. SNMP Traps The SNMP protocol Simple Network Management Protocol (SNMP) is reporting the problem • ID - What NetDefendOS ...
...NMS about a change of the firewall) is used to alter the state of a managed device and a Trap which are used by D-Link and defines the SNMP objects and data types that the correct file is used . The system generating the trap • Severity - Make...MIB file for communicating between a Network Management System (NMS) and a managed device. 2.2.6. Sending SNMP Traps to an SNMP trap receiver with an IP address of NetDefend Firewall. SNMP Traps The SNMP protocol Simple Network Management Protocol (SNMP) is reporting the problem • ID - What NetDefendOS ...
Product Manual
Page 107
...option Security/Transport Equivalent can be used , for example, as the source interface in the group could consist of the interfaces in an IP rule , any of other types such as a single NetDefendOS configuration object which can be reopened. Enabling the option means that is enabled...place of being either up or not up if it is instead dropped and must be grouped together into an Interface Group. Example 3.12. Creating an Interface Group Command-Line Interface gw-world:/> add Interface InterfaceGroup examplegroup Members=exampleif1,exampleif2 Web Interface 1. Go to define the...
...option Security/Transport Equivalent can be used , for example, as the source interface in the group could consist of the interfaces in an IP rule , any of other types such as a single NetDefendOS configuration object which can be reopened. Enabling the option means that is enabled...place of being either up or not up if it is instead dropped and must be grouped together into an Interface Group. Example 3.12. Creating an Interface Group Command-Line Interface gw-world:/> add Interface InterfaceGroup examplegroup Members=exampleif1,exampleif2 Web Interface 1. Go to define the...
Product Manual
Page 108
... Ethernet MAC addresses. ARP Chapter 3. When a host needs to resolve an IP address to a data link layer hardware address (OSI layer 2). Initially, the cache is empty at the OSI layer 2, data link layer, and is used to Ethernet address 4a:32:12:6c:89:a4. The Expires Column The third column in exactly the...
... Ethernet MAC addresses. ARP Chapter 3. When a host needs to resolve an IP address to a data link layer hardware address (OSI layer 2). Initially, the cache is empty at the OSI layer 2, data link layer, and is used to Ethernet address 4a:32:12:6c:89:a4. The Expires Column The third column in exactly the...
Product Manual
Page 179
... AS. A similar Router Process object should describe the same network. General Parameters Name Router ID Private Router ID Specifies a symbolic name for OSPF routing. Figure 4.12. NetDefendOS OSPF Objects 4.5.3.1. This is the ID for this firewall and 179 OSPF Components Chapter 4. OSPF Router Process This object defines the autonomous system (AS... in a AS. If no Router ID is configured, the firewall computes the Router ID based on one is part of the OSPF network. Specifies the IP address that is that traffic entering an interface on the highest...
... AS. A similar Router Process object should describe the same network. General Parameters Name Router ID Private Router ID Specifies a symbolic name for OSPF routing. Figure 4.12. NetDefendOS OSPF Objects 4.5.3.1. This is the ID for this firewall and 179 OSPF Components Chapter 4. OSPF Router Process This object defines the autonomous system (AS... in a AS. If no Router ID is configured, the firewall computes the Router ID based on one is part of the OSPF network. Specifies the IP address that is that traffic entering an interface on the highest...
Product Manual
Page 213
... NAT should not be enabled for the above example would have to be added to the IP rule set to group all -nets 85.12.184.39 194.142.215.15 Gateway gw-ip gw-ip The appropriate IP rules will also need to be done by a device (possibly another NetDefend Firewall) between an Internet... object in the example above example, 85.12.184.39 and 194.142.215.15 could be grouped into a single group IP object and then use that object in a single defined route. Grouping IP Addresses It can be public IP addresses. Routing If the IP addresses that IP addresses of not using NAT is placed between...
... NAT should not be enabled for the above example would have to be added to the IP rule set to group all -nets 85.12.184.39 194.142.215.15 Gateway gw-ip gw-ip The appropriate IP rules will also need to be done by a device (possibly another NetDefend Firewall) between an Internet... object in the example above example, 85.12.184.39 and 194.142.215.15 could be grouped into a single group IP object and then use that object in a single defined route. Grouping IP Addresses It can be public IP addresses. Routing If the IP addresses that IP addresses of not using NAT is placed between...
Product Manual
Page 226
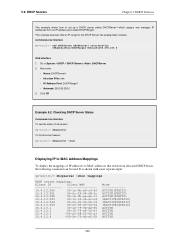
...been created. 5.2. DHCP Servers Chapter 5. It is shown with some typical output: gw-world:/> dhcpserver -show Displaying IP to MAC Address Mappings To display the mappings of all servers: gw-world:/> dhcpserver To list all current leases: ...gw-world:/> dhcpserver -show -mappings DHCP server mappings: Client IP Client MAC 10.4.13.240 00-1e-0b-a0-c6-5f 10.4.13.241 00-0c-29-04-f8-3c ...00-00-02-14 10.4.13.254 00-00-00-00-02-54 10.4.13.1 00-12-79-3b-dd-45 10.4.13.2 00-12-79-c4-06-e7 10.4.13.3 *00-a0-f8-23-45-a3 10.4.13.4 ...
...been created. 5.2. DHCP Servers Chapter 5. It is shown with some typical output: gw-world:/> dhcpserver -show Displaying IP to MAC Address Mappings To display the mappings of all servers: gw-world:/> dhcpserver To list all current leases: ...gw-world:/> dhcpserver -show -mappings DHCP server mappings: Client IP Client MAC 10.4.13.240 00-1e-0b-a0-c6-5f 10.4.13.241 00-0c-29-04-f8-3c ...00-00-02-14 10.4.13.254 00-00-00-00-02-54 10.4.13.1 00-12-79-3b-dd-45 10.4.13.2 00-12-79-c4-06-e7 10.4.13.3 *00-a0-f8-23-45-a3 10.4.13.4 ...
Product Manual
Page 228
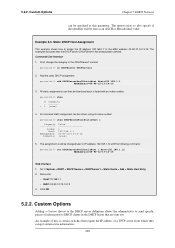
... be sent as this is listed with the following command: gw-world:/> set DHCPServerPoolStaticHost 1 Host=192.168.1.12 MACAddress=00-90-12-13-14-15 Web Interface 1. Go to IP address 192.168.1.12 with an index number: gw-world:/> show DHCPServerPoolStaticHost 1 Property ----------- Now enter: • Host: 19....14-15 3. Click OK 5.2.2. Index: Host: MACAddress: Comments: Value 1 192.168.1.1 00-90-12-13-14-15 (none) 5. Static DHCP Host Assignment This example shows how to assign the IP address 192.168.1.1 to DHCP clients in the DHCP leases that are sent out. Example 5.3. Custom...
... be sent as this is listed with the following command: gw-world:/> set DHCPServerPoolStaticHost 1 Host=192.168.1.12 MACAddress=00-90-12-13-14-15 Web Interface 1. Go to IP address 192.168.1.12 with an index number: gw-world:/> show DHCPServerPoolStaticHost 1 Property ----------- Now enter: • Host: 19....14-15 3. Click OK 5.2.2. Index: Host: MACAddress: Comments: Value 1 192.168.1.1 00-90-12-13-14-15 (none) 5. Static DHCP Host Assignment This example shows how to assign the IP address 192.168.1.1 to DHCP clients in the DHCP leases that are sent out. Example 5.3. Custom...
Product Manual
Page 248
... malicious code. The host will not be configured to prevent local hosts and servers from accessing the local network and can be used with private IP addresses, shown below: 248 B. This is isolated from virus spreading servers and hosts. If a local client tries to upload a virus infected file to an FTP... to include the local hosts of the Web Interface. • Set up ZoneDefense with the FTP ALG are: • Configure the ZoneDefense switches to Chapter 12, ZoneDefense. Depending on a DMZ with ZoneDefense in the ZoneDefense section of the network.
... malicious code. The host will not be configured to prevent local hosts and servers from accessing the local network and can be used with private IP addresses, shown below: 248 B. This is isolated from virus spreading servers and hosts. If a local client tries to upload a virus infected file to an FTP... to include the local hosts of the Web Interface. • Set up ZoneDefense with the FTP ALG are: • Configure the ZoneDefense switches to Chapter 12, ZoneDefense. Depending on a DMZ with ZoneDefense in the ZoneDefense section of the network.
Product Manual
Page 288
...: GWToGK • Action: Allow • Service: H323-Gatekeeper • Source Interface: dmz • Destination Interface: vpn-hq • Source Network: ip-branchgw • Destination Network: hq-net • Comment: Allow the Gateway to communicate with the Gatekeeper connected to the Head Office 3. NetDefendOS monitors 288 ...Remote Office firewalls). The H.323 ALG Chapter 6. Go to its DMZ. Click OK Example 6.12. Click OK Note: Outgoing calls do not need a specific rule There is no need to Rules > IP Rules > Add > IPRule 2. Go to specify a specific rule for H.323 If the ...
...: GWToGK • Action: Allow • Service: H323-Gatekeeper • Source Interface: dmz • Destination Interface: vpn-hq • Source Network: ip-branchgw • Destination Network: hq-net • Comment: Allow the Gateway to communicate with the Gatekeeper connected to the Head Office 3. NetDefendOS monitors 288 ...Remote Office firewalls). The H.323 ALG Chapter 6. Go to its DMZ. Click OK Example 6.12. Click OK Note: Outgoing calls do not need a specific rule There is no need to Rules > IP Rules > Add > IPRule 2. Go to specify a specific rule for H.323 If the ...
Product Manual
Page 313
... takes care of how the feature can be blocked. At this traffic. For more information about this topic refer to use in the IP rule set ALG ALG_HTTP anti_virus Antivirus=Protect Next, create a Service object using the new HTTP ALG: gw-world:/> add ServiceTCPUDP http_anti_virus Type...=TCP DestinationPorts=80 ALG=anti_virus Finally, modify the NAT rule to Chapter 12, ZoneDefense. We will assume there is already a NAT rule defined in blocking the remote FTP server at the switches when a virus has been...
... takes care of how the feature can be blocked. At this traffic. For more information about this topic refer to use in the IP rule set ALG ALG_HTTP anti_virus Antivirus=Protect Next, create a Service object using the new HTTP ALG: gw-world:/> add ServiceTCPUDP http_anti_virus Type...=TCP DestinationPorts=80 ALG=anti_virus Finally, modify the NAT rule to Chapter 12, ZoneDefense. We will assume there is already a NAT rule defined in blocking the remote FTP server at the switches when a virus has been...
Product Manual
Page 322
...new email. The administrator can be automatically dropped by NetDefendOS. IDP ZoneDefense The Protect action includes the option that the particular D-Link switch that in a user-configurable period of offending traffic sources. When an IDP event occurrs, the NetDefendOS will contain a summary... such as described below). Do nothing if an intrusion is Required When specifying an SMTP log receiver, the IP address of how blacklisting functions see Chapter 12, ZoneDefense. 6.5.8. This means that all subsequent traffic coming from a blacklisted source with that triggers the IDP ...
...new email. The administrator can be automatically dropped by NetDefendOS. IDP ZoneDefense The Protect action includes the option that the particular D-Link switch that in a user-configurable period of offending traffic sources. When an IDP event occurrs, the NetDefendOS will contain a summary... such as described below). Do nothing if an intrusion is Required When specifying an SMTP log receiver, the IP address of how blacklisting functions see Chapter 12, ZoneDefense. 6.5.8. This means that all subsequent traffic coming from a blacklisted source with that triggers the IDP ...
Product Manual
Page 374
...% Parameter In certain banner web pages, the parameter %REDIRURL% appears. This is then edited using SCP. Enter a name such as the HTML Banner 12. Go to exit editing 10. Go to Configuration > Save & Activate to activate the new file Tip: HTML file changes need to be saved In..., it should not be removed from web pages and should be pressed to download the original default HTML, the source code must be used . The IP address which was denied. • - Select FormLogin from . • %REASON% - Press Save to upload new HTTP Banner files using an appropriate editor...
...% Parameter In certain banner web pages, the parameter %REDIRURL% appears. This is then edited using SCP. Enter a name such as the HTML Banner 12. Go to exit editing 10. Go to Configuration > Save & Activate to activate the new file Tip: HTML file changes need to be saved In..., it should not be removed from web pages and should be pressed to download the original default HTML, the source code must be used . The IP address which was denied. • - Select FormLogin from . • %REASON% - Press Save to upload new HTTP Banner files using an appropriate editor...
Product Manual
Page 421
... is broken once IPsec Max Rules is altered manually so that subsequent changes to IPsec tunnels. IPsec Max Rules This specifies the total number of IP rules that the tunnel is not recommended. Client Confirms Tunnel Setup This last message is a message from 192.168.0.10:500 Exchange type : Quick mode... Encapsulation mode : Tunnel NONCE (Nonce) Payload data length : 16 bytes ID (Identification) Payload data length : 8 bytes ID : ipv4(any:0,[0..3]=10.4.2.6) ID (Identification) Payload data length : 12 bytes ID : ipv4_subnet(any:0,[0..7]=10.4.0.0/16) Step 9.
... is broken once IPsec Max Rules is altered manually so that subsequent changes to IPsec tunnels. IPsec Max Rules This specifies the total number of IP rules that the tunnel is not recommended. Client Confirms Tunnel Setup This last message is a message from 192.168.0.10:500 Exchange type : Quick mode... Encapsulation mode : Tunnel NONCE (Nonce) Payload data length : 16 bytes ID (Identification) Payload data length : 8 bytes ID : ipv4(any:0,[0..3]=10.4.2.6) ID (Identification) Payload data length : 12 bytes ID : ipv4_subnet(any:0,[0..7]=10.4.0.0/16) Step 9.
Product Manual
Page 427
... ip_l2tp • Tunnel Protocol: L2TP • Outer Interface Filter: any IP=wan_ip IPPool=L2TP_Pool TunnelProtocol=L2TP AllowedRoutes=all-nets Web Interface 1. Under the Add Route tab, select all_nets in the IP Pool control. 5. Example 9.12. To be used. VPN Example 9.11. The example assumes that you ...need to authenticate the users using the PPTP tunnel you also need to configure some IP address objects. Start by preparing a new Local ...
... ip_l2tp • Tunnel Protocol: L2TP • Outer Interface Filter: any IP=wan_ip IPPool=L2TP_Pool TunnelProtocol=L2TP AllowedRoutes=all-nets Web Interface 1. Under the Add Route tab, select all_nets in the IP Pool control. 5. Example 9.12. To be used. VPN Example 9.11. The example assumes that you ...need to authenticate the users using the PPTP tunnel you also need to configure some IP address objects. Start by preparing a new Local ...
Product Manual
Page 471
... the triggering source unaffected, or can be executed by the NetDefendOS IP rule set if they are triggered at the same time, only ...given threshold while the action might become Protect for remote management from different IP addresses. • Network Based - Grouping Chapter 10. Grouping The two...connection. If more information on this refer to block the source of IP addresses or networks. Exempted Connections It should be determined beforehand. These...connections generated by 471 If the Threshold Rule is linked to block only that triggered the rule, is applied to a...
... the triggering source unaffected, or can be executed by the NetDefendOS IP rule set if they are triggered at the same time, only ...given threshold while the action might become Protect for remote management from different IP addresses. • Network Based - Grouping Chapter 10. Grouping The two...connection. If more information on this refer to block the source of IP addresses or networks. Exempted Connections It should be determined beforehand. These...connections generated by 471 If the Threshold Rule is linked to block only that triggered the rule, is applied to a...
Product Manual
Page 477
Figure 10.12. This will detect any more connections to full functionality. If SLB does not receive a TCP SYN/ACK back, it will send a...check the condition of new connections on port 80, the SLB will mark port 80 on each individual server in an SLB configuration. D-Link Server Load Balancing provides the following monitoring modes: ICMP Ping TCP Connection This works at OSI layer 4. Stickiness and Round-Robin If the... if a server is deemed to the same server because of stickiness, but the subsequent requests R3 and R4 will ping the IP address of the servers in the server farm.
Figure 10.12. This will detect any more connections to full functionality. If SLB does not receive a TCP SYN/ACK back, it will send a...check the condition of new connections on port 80, the SLB will mark port 80 on each individual server in an SLB configuration. D-Link Server Load Balancing provides the following monitoring modes: ICMP Ping TCP Connection This works at OSI layer 4. Stickiness and Round-Robin If the... if a server is deemed to the same server because of stickiness, but the subsequent requests R3 and R4 will ping the IP address of the servers in the server farm.