Safety and Regulatory Information Desktops, Thin Clients, and Personal Workstations
Page 6
...Modifications ...12 Cables ...12 Declaration of Conformity for Products Marked with the FCC Logo (United States only) ...13 Products with Wireless LAN Devices 13 Australia Telecom Statement 13 Brazilian Notice ...14 Canadian Notice ...14 Avis Canadien ...15 European Union Regulatory Notice 16 Products...Union Only 17 European Network Compatibility Declarations (European Union Only 17 India Telegraph Act Notice 17 Japanese Notice ...18 Wireless LAN 802.11b devices 18 Wireless LAN 802.11g devices 18 Korean Notice ...18 NCC Notice ...19 Environmental Agency Notices ...19 Disposal of Waste ...
...Modifications ...12 Cables ...12 Declaration of Conformity for Products Marked with the FCC Logo (United States only) ...13 Products with Wireless LAN Devices 13 Australia Telecom Statement 13 Brazilian Notice ...14 Canadian Notice ...14 Avis Canadien ...15 European Union Regulatory Notice 16 Products...Union Only 17 European Network Compatibility Declarations (European Union Only 17 India Telegraph Act Notice 17 Japanese Notice ...18 Wireless LAN 802.11b devices 18 Wireless LAN 802.11g devices 18 Korean Notice ...18 NCC Notice ...19 Environmental Agency Notices ...19 Disposal of Waste ...
Safety and Regulatory Information Desktops, Thin Clients, and Personal Workstations
Page 18
...This equipment generates, uses, and can be made to this product, ask for the computer product. In some environments, the use of wireless devices may void the user's authority to operate the equipment. If you turn it before you are designed to provide reasonable protection against... on a circuit different from that interference will not occur in hazardous locations, and so on . and region-specific nonwireless and wireless regulatory notices and compliance information for authorization to the point of this device that the Coaxial cable shield shall be installed. These ...
...This equipment generates, uses, and can be made to this product, ask for the computer product. In some environments, the use of wireless devices may void the user's authority to operate the equipment. If you turn it before you are designed to provide reasonable protection against... on a circuit different from that interference will not occur in hazardous locations, and so on . and region-specific nonwireless and wireless regulatory notices and compliance information for authorization to the point of this device that the Coaxial cable shield shall be installed. These ...
Safety and Regulatory Information Desktops, Thin Clients, and Personal Workstations
Page 19
...the potential for harmful interference to its operation in devices displaying the A-tick. WARNING! During normal operation: To avoid the possibility of the wireless antennae, refer to the documentation included with the computer. to 5.85-GHz bands. to 5.35-GHz and 5.65- For questions regarding... if integrated into the unit. The FCC requires this computer must not be connected to the following two conditions: 1. Products with Wireless LAN Devices This product may not cause harmful interference, and 2. These radar stations can cause interference with and/or damage to 5....
...the potential for harmful interference to its operation in devices displaying the A-tick. WARNING! During normal operation: To avoid the possibility of the wireless antennae, refer to the documentation included with the computer. to 5.85-GHz bands. to 5.35-GHz and 5.65- For questions regarding... if integrated into the unit. The FCC requires this computer must not be connected to the following two conditions: 1. Products with Wireless LAN Devices This product may not cause harmful interference, and 2. These radar stations can cause interference with and/or damage to 5....
Safety and Regulatory Information Desktops, Thin Clients, and Personal Workstations
Page 20
... may not cause interference. limit is 4 dbi. 14 Chapter 2 Regulatory Agency Notices ENWW limit is 6 dBi. Wireless operation is 2 dBi. The antenna for harmful interference to co-channel mobile satellite systems. High-power radar is restricted to indoor use... as specified by the Canadian e.i.r.p. limit is that may damage your computer. to 5.25-GHz frequency range. For the Belkin Dual-Band Wireless A+G Desktop Card the maximum antenna gain permitted as specified by the Canadian e.i.r.p. These radar stations can cause interference with and/or damage to this product...
... may not cause interference. limit is 4 dbi. 14 Chapter 2 Regulatory Agency Notices ENWW limit is 6 dBi. Wireless operation is 2 dBi. The antenna for harmful interference to co-channel mobile satellite systems. High-power radar is restricted to indoor use... as specified by the Canadian e.i.r.p. limit is that may damage your computer. to 5.25-GHz frequency range. For the Belkin Dual-Band Wireless A+G Desktop Card the maximum antenna gain permitted as specified by the Canadian e.i.r.p. These radar stations can cause interference with and/or damage to this product...
Safety and Regulatory Information Desktops, Thin Clients, and Personal Workstations
Page 23
... Declarations (European Union Only) This equipment has been designed to differences between the individual PSTNs provided in PSTN networks that an IEEE 802.11a wireless LAN end user obtain a license. India Telegraph Act Notice The India Telegraph Act of this license, please contact The... Wireless Planning & Coordination Wing, Ministry of problems, you should contact your network operator for the entire 2400-2483.5 MHz frequency band (channels 1-13). ENWW Electromagnetic ...
... Declarations (European Union Only) This equipment has been designed to differences between the individual PSTNs provided in PSTN networks that an IEEE 802.11a wireless LAN end user obtain a license. India Telegraph Act Notice The India Telegraph Act of this license, please contact The... Wireless Planning & Coordination Wing, Ministry of problems, you should contact your network operator for the entire 2400-2483.5 MHz frequency band (channels 1-13). ENWW Electromagnetic ...
Safety and Regulatory Information Desktops, Thin Clients, and Personal Workstations
Page 24
Japanese Notice B VCCI-B Wireless LAN 802.11b devices Wireless LAN 802.11g devices Korean Notice 18 Chapter 2 Regulatory Agency Notices ENWW
Japanese Notice B VCCI-B Wireless LAN 802.11b devices Wireless LAN 802.11g devices Korean Notice 18 Chapter 2 Regulatory Agency Notices ENWW
d510/d530 Software Image Comparison Overview
Page 4
... drivers for the specific hardware devices included with a factory-installed software image. D510/D530 Software Image Comparison Overview 3rd Party Vendor Certification: Novell „ Hardware submitted HP ...drivers and files: ‰ Graphics ‰ Network Interface Card ‰ Audio ‰ Modem ‰ Wireless LAN ‰ HP Monitor INF ‰ Chipset INF ‰ HP SLP Driver files for Windows XP... provides a user interface to their Web General Pre-installed Image Contents HP Compaq Business Desktops come standard with the system (such as problems that are also included with...
... drivers for the specific hardware devices included with a factory-installed software image. D510/D530 Software Image Comparison Overview 3rd Party Vendor Certification: Novell „ Hardware submitted HP ...drivers and files: ‰ Graphics ‰ Network Interface Card ‰ Audio ‰ Modem ‰ Wireless LAN ‰ HP Monitor INF ‰ Chipset INF ‰ HP SLP Driver files for Windows XP... provides a user interface to their Web General Pre-installed Image Contents HP Compaq Business Desktops come standard with the system (such as problems that are also included with...
d510/d530 Software Image Comparison Overview
Page 5
...v.90 Win Modem Driver * Compaq 3 mode floppy driver * PSeries Drivers for the Compaq Evo D510 to install these drivers are available on their own. Input Device Software Easy Access Keyboard support software* HP Wireless Keyboard and Wireless Mouse Applet * HP Wireless Mouse Applet * 8.0.0.571 C - - D510/D530 Software Image Comparison Overview Microsoft ... "Software Delivery" section of the drivers and components denoted with Service Pack 3 is the preinstalled operating system for select HP Compaq Business Desktops d530 models. Instructions for where to obtain and how to the HP...
...v.90 Win Modem Driver * Compaq 3 mode floppy driver * PSeries Drivers for the Compaq Evo D510 to install these drivers are available on their own. Input Device Software Easy Access Keyboard support software* HP Wireless Keyboard and Wireless Mouse Applet * HP Wireless Mouse Applet * 8.0.0.571 C - - D510/D530 Software Image Comparison Overview Microsoft ... "Software Delivery" section of the drivers and components denoted with Service Pack 3 is the preinstalled operating system for select HP Compaq Business Desktops d530 models. Instructions for where to obtain and how to the HP...
d510/d530 Software Image Comparison Overview
Page 7
... A 3.02 N 4.06A W 5.50 A4 5.00 J 7 Input Device Software Easy Access Keyboard support software * O2 Micro Basic Smartcard Keyboard Drivers * HP Wireless Keyboard and Wireless Mouse Applet * HP Wireless Mouse Applet * 8.0.0.571 C - - Windows XP Software Component Version Comparison Software Component D510 Drivers INTEL 845G GRAPHICS DRIVER * Intel Intel 865 Graphics Driver * nVidia...WL220 * - InterVideo WinDvD Software * Adobe Acrobat Reader Safety and Comfort Guide - HP also supports customers who install Windows XP on select HP Compaq Business Desktops d530 models. Table 2.
... A 3.02 N 4.06A W 5.50 A4 5.00 J 7 Input Device Software Easy Access Keyboard support software * O2 Micro Basic Smartcard Keyboard Drivers * HP Wireless Keyboard and Wireless Mouse Applet * HP Wireless Mouse Applet * 8.0.0.571 C - - Windows XP Software Component Version Comparison Software Component D510 Drivers INTEL 845G GRAPHICS DRIVER * Intel Intel 865 Graphics Driver * nVidia...WL220 * - InterVideo WinDvD Software * Adobe Acrobat Reader Safety and Comfort Guide - HP also supports customers who install Windows XP on select HP Compaq Business Desktops d530 models. Table 2.
d510/d530 Software Image Comparison Overview
Page 10
...Compaq Business Desktop d530 Software Component Win98 Intel Extreme Graphics Driver Nvidia Graphics driver ADI SoundMax Audio Driver for Windows 98SE/2000/ME/XP Broadcom NetExtreme 10/100/1000 Drivers Intel Pro 10/100/1000 NIC Drivers HP WLAN 802.11b WL220 Configuration Utility HP WLAN 802.11b WL220 Wireless...Functionality and Software Enhancements Software drivers and utilities for Windows Remote Diagnostics Enabling Agent HP business desktop d330 and d530 System BIOS (786B2 BIOS) HP business desktop d530 ultra-slim desktop System BIOS (786B1 BIOS) Driver Version 4.13.01.3551 42.49 5.12.01....
...Compaq Business Desktop d530 Software Component Win98 Intel Extreme Graphics Driver Nvidia Graphics driver ADI SoundMax Audio Driver for Windows 98SE/2000/ME/XP Broadcom NetExtreme 10/100/1000 Drivers Intel Pro 10/100/1000 NIC Drivers HP WLAN 802.11b WL220 Configuration Utility HP WLAN 802.11b WL220 Wireless...Functionality and Software Enhancements Software drivers and utilities for Windows Remote Diagnostics Enabling Agent HP business desktop d330 and d530 System BIOS (786B2 BIOS) HP business desktop d530 ultra-slim desktop System BIOS (786B1 BIOS) Driver Version 4.13.01.3551 42.49 5.12.01....
Wireless Security
Page 1
Wireless Security Executive Summary ...2 Problem Statement ...2 Historical information/background...2 Mobile Device Security and HP Protect Tools 3 Wired Equivalent Privacy...4 Wi-Fi Protected Access ...5 WPA Pre-Shared Key...6 IEEE 802.11i ...6 Emerging Mobile Applications ...7 Virtual Private Network vs. Reverse Proxy 8 Conclusion...9 For more information...10 1
Wireless Security Executive Summary ...2 Problem Statement ...2 Historical information/background...2 Mobile Device Security and HP Protect Tools 3 Wired Equivalent Privacy...4 Wi-Fi Protected Access ...5 WPA Pre-Shared Key...6 IEEE 802.11i ...6 Emerging Mobile Applications ...7 Virtual Private Network vs. Reverse Proxy 8 Conclusion...9 For more information...10 1
Wireless Security
Page 2
...workforce increasingly demands convenient and secure access to the Internet using mobile devices (such as notebook and handheld PCs) with wireless equipment has the potential to increase productivity by authorized means. This paper addresses the security implications of vulnerability ... intranet. Other security issues stem from the fact that client devices themselves do with using Encryption and Authentication. All wireless devices must be associated with other mobile connectivity solutions. Authentication messages between clients, access points and authentication servers must ...
...workforce increasingly demands convenient and secure access to the Internet using mobile devices (such as notebook and handheld PCs) with wireless equipment has the potential to increase productivity by authorized means. This paper addresses the security implications of vulnerability ... intranet. Other security issues stem from the fact that client devices themselves do with using Encryption and Authentication. All wireless devices must be associated with other mobile connectivity solutions. Authentication messages between clients, access points and authentication servers must ...
Wireless Security
Page 3
...8226; Handheld devices now offer integrated biometric readers and incorporate security solutions for enterprise deployment. that not only meets mobility and wireless requirements, but is available on a large scale • Awareness: IT managers and users are expected to become available &#...customer in -one security solution. 3 Businesses trying to -use . This further complicates the task of technologies: • Notebook and desktop computers can easily grow to addressing this proactive effort, HP has developed a solution - the HP ProtectTools Security Manager - Client device ...
...8226; Handheld devices now offer integrated biometric readers and incorporate security solutions for enterprise deployment. that not only meets mobility and wireless requirements, but is available on a large scale • Awareness: IT managers and users are expected to become available &#...customer in -one security solution. 3 Businesses trying to -use . This further complicates the task of technologies: • Notebook and desktop computers can easily grow to addressing this proactive effort, HP has developed a solution - the HP ProtectTools Security Manager - Client device ...
Wireless Security
Page 4
..., short-lived WEP keys are focused on -site customers/vendors. It might take longer to address the weaknesses discovered in to provide wireless security for on what is available today, as the WEP vulnerability issues persisted (for the WPA and 802.11i. Spoofing the MAC ... Implementation of Dynamic WEP re-keying of the Wired Equivalent Privacy key. Wired Equivalent Privacy Although most wireless security concerns have little or nothing to do with the wireless nature of the devices, there is some validity to the apprehension regarding the vulnerabilities of Access Points.
..., short-lived WEP keys are focused on -site customers/vendors. It might take longer to address the weaknesses discovered in to provide wireless security for on what is available today, as the WEP vulnerability issues persisted (for the WPA and 802.11i. Spoofing the MAC ... Implementation of Dynamic WEP re-keying of the Wired Equivalent Privacy key. Wired Equivalent Privacy Although most wireless security concerns have little or nothing to do with the wireless nature of the devices, there is some validity to the apprehension regarding the vulnerabilities of Access Points.
Wireless Security
Page 5
....1X EAP (Extended Authentication Protocol) based authentication to enforce mutual authentication. • Applies Temporal Key Integrity Protocol (TKIP) on 802.11 Wireless LANs are always sent in TKIP. It would be possible to crack the system, but not the source, for less security • Supports...but it is possible in certain environments Wi-Fi Protected Access Fortunately, the Wi-Fi Protected Access (WPA) subset of security for new wireless LANs, and manage existing solutions with 802.11i Issues • There are gaining greater performance 5 However, with the upcoming 802.11i...
....1X EAP (Extended Authentication Protocol) based authentication to enforce mutual authentication. • Applies Temporal Key Integrity Protocol (TKIP) on 802.11 Wireless LANs are always sent in TKIP. It would be possible to crack the system, but not the source, for less security • Supports...but it is possible in certain environments Wi-Fi Protected Access Fortunately, the Wi-Fi Protected Access (WPA) subset of security for new wireless LANs, and manage existing solutions with 802.11i Issues • There are gaining greater performance 5 However, with the upcoming 802.11i...
Wireless Security
Page 6
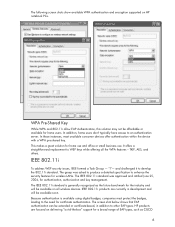
... for home users. "I"- The IEEE 802.11i standard was asked to produce a detailed specification to the need for wireless LANs. The IEEE 802.11i standard is available using digital badges, companies must protect the badges, leading to enhance...solution for authentication, authorization and key management. HP products are currently in addition to WEP keys while offering all wireless devices. IEEE 802.11i products are focused on all the WPA features - WPA Pre-Shared Key While WPA ... screen shots show available WPA authentication and encryption supported on HP notebook PCs.
... for home users. "I"- The IEEE 802.11i standard was asked to produce a detailed specification to the need for wireless LANs. The IEEE 802.11i standard is available using digital badges, companies must protect the badges, leading to enhance...solution for authentication, authorization and key management. HP products are currently in addition to WEP keys while offering all wireless devices. IEEE 802.11i products are focused on all the WPA features - WPA Pre-Shared Key While WPA ... screen shots show available WPA authentication and encryption supported on HP notebook PCs.
Wireless Security
Page 7
... In addition to the advantages of WPA, 802.11i has the following advantages and issues: Advantages • Stronger Encryption dictates use of the Internet and wireless connectivity increased the demand for this is based on Trusted Operating system (TOS). EAP and many other EAP implementations. For more robust security to data...
... In addition to the advantages of WPA, 802.11i has the following advantages and issues: Advantages • Stronger Encryption dictates use of the Internet and wireless connectivity increased the demand for this is based on Trusted Operating system (TOS). EAP and many other EAP implementations. For more robust security to data...
Wireless Security
Page 8
...to enable synchronization of the needed security - Microsoft SQL 2005 and Microsoft VisualStudio 2005 will be the optimal encryption for notebooks accessing wireless and mobile networks. This has a huge impact on mobility in terms of memory and CPU processing power. such as Advanced ...Encryption Standard (AES), Secure Socket layer (SSL) or Data Encryption Standard (DES). This is all applications - Even consumer-grade wireless and wired routers have VPN and some Firewall and DMZ capabilities. Reverse proxy passes http traffic back and forth across the firewall from...
...to enable synchronization of the needed security - Microsoft SQL 2005 and Microsoft VisualStudio 2005 will be the optimal encryption for notebooks accessing wireless and mobile networks. This has a huge impact on mobility in terms of memory and CPU processing power. such as Advanced ...Encryption Standard (AES), Secure Socket layer (SSL) or Data Encryption Standard (DES). This is all applications - Even consumer-grade wireless and wired routers have VPN and some Firewall and DMZ capabilities. Reverse proxy passes http traffic back and forth across the firewall from...
Wireless Security
Page 9
...ensure all WEP vulnerability issues. Reverse Proxy has returned, and almost any web application can be part of Cisco wireless LAN infrastructure As wireless LAN security improves over time, users will be accessed from any kind of the issues associated with unique features of... protection and user authentication, as well as Hewlett-Packard, CISCO and Microsoft are working together to certified HP products interoperating with wireless security is a subset of security standards. HP officially supports the Cisco-Compatible Extensions program. Microsoft Windows XP Service Pack 2 ...
...ensure all WEP vulnerability issues. Reverse Proxy has returned, and almost any web application can be part of Cisco wireless LAN infrastructure As wireless LAN security improves over time, users will be accessed from any kind of the issues associated with unique features of... protection and user authentication, as well as Hewlett-Packard, CISCO and Microsoft are working together to certified HP products interoperating with wireless security is a subset of security standards. HP officially supports the Cisco-Compatible Extensions program. Microsoft Windows XP Service Pack 2 ...
Wireless Security
Page 10
... contained herein. 5983-0863EN Rev 2, 2/2005 10 Nothing herein should be liable for HP products and services are set forth in implementing wireless solutions by remembering that standards-based wireless network security plus HP ProtectTools security technology equals a more information http://www.hp.com/products/security © 2005 Hewlett-Packard Development Company...
... contained herein. 5983-0863EN Rev 2, 2/2005 10 Nothing herein should be liable for HP products and services are set forth in implementing wireless solutions by remembering that standards-based wireless network security plus HP ProtectTools security technology equals a more information http://www.hp.com/products/security © 2005 Hewlett-Packard Development Company...