Reference Guide
Page 3
... 2-1 Before Accessing the ACS CLI 2-1 Starting the CSACS-1121 2-2 Running Setup to Configure ACS 2-2 Accessing the ACS CLI 2-3 Supported Hardware and Software Platforms 2-4 Opening the CLI with Secure Shell 2-5 Opening the CLI Using a Local PC 2-5 Understanding Command Modes 2-6 EXEC Mode 2-6 ACS Configuration Mode 2-7 Configuration Mode 2-8 Configuration Submodes 2-8 CLI Reference Guide for the Cisco Secure Access Control System...
... 2-1 Before Accessing the ACS CLI 2-1 Starting the CSACS-1121 2-2 Running Setup to Configure ACS 2-2 Accessing the ACS CLI 2-3 Supported Hardware and Software Platforms 2-4 Opening the CLI with Secure Shell 2-5 Opening the CLI Using a Local PC 2-5 Understanding Command Modes 2-6 EXEC Mode 2-6 ACS Configuration Mode 2-7 Configuration Mode 2-8 Configuration Submodes 2-8 CLI Reference Guide for the Cisco Secure Access Control System...
Reference Guide
Page 4
... acs restore A-18 acs support A-20 application install A-23 application remove A-24 application reset-config A-25 application start A-26 application stop A-26 application upgrade A-27 backup A-28 backup-logs A-30 clock A-31 configure A-32 copy A-32 debug A-36 delete A-38 dir A-39 exit A-41 forceout A-41 CLI Reference Guide for the Cisco Secure...
... acs restore A-18 acs support A-20 application install A-23 application remove A-24 application reset-config A-25 application start A-26 application stop A-26 application upgrade A-27 backup A-28 backup-logs A-30 clock A-31 configure A-32 copy A-32 debug A-36 delete A-38 dir A-39 exit A-41 forceout A-41 CLI Reference Guide for the Cisco Secure...
Reference Guide
Page 5
... session-timeout A-54 terminal session-welcome A-54 terminal terminal-type A-55 traceroute A-55 undebug A-56 write A-58 Show Commands A-59 show acs-config-web-interface A-60 show acs-cores A-60 show acs-logs A-61 show application A-64 show backup history A-67 show cdp A-68 show clock A-69 show cpu A-69 show disks A-71... logins A-78 show memory A-78 show ntp A-79 show ports A-80 show process A-81 show repository A-82 show restore A-83 CLI Reference Guide for the Cisco Secure Access Control System 5.1 v
... session-timeout A-54 terminal session-welcome A-54 terminal terminal-type A-55 traceroute A-55 undebug A-56 write A-58 Show Commands A-59 show acs-config-web-interface A-60 show acs-cores A-60 show acs-logs A-61 show application A-64 show backup history A-67 show cdp A-68 show clock A-69 show cpu A-69 show disks A-71... logins A-78 show memory A-78 show ntp A-79 show ports A-80 show process A-81 show repository A-82 show restore A-83 CLI Reference Guide for the Cisco Secure Access Control System 5.1 v
Reference Guide
Page 6
... show tech-support A-86 show terminal A-88 show timezone A-88 show timezones A-89 show udi A-90 show uptime A-91 show users A-92 show version A-92 ACS Configuration Commands A-93 access-setting accept-all A-93 debug-adclient A-94 debug-log A-95 decrypt-support-bundle A-98 export-data A-98 import-data A-100 import... exit A-121 hostname A-122 icmp echo A-122 interface A-123 ip address A-124 ip default-gateway A-125 ip domain-name A-126 CLI Reference Guide for the Cisco Secure Access Control System 5.1 vi OL-18996-01
... show tech-support A-86 show terminal A-88 show timezone A-88 show timezones A-89 show udi A-90 show uptime A-91 show users A-92 show version A-92 ACS Configuration Commands A-93 access-setting accept-all A-93 debug-adclient A-94 debug-log A-95 decrypt-support-bundle A-98 export-data A-98 import-data A-100 import... exit A-121 hostname A-122 icmp echo A-122 interface A-123 ip address A-124 ip default-gateway A-125 ip domain-name A-126 CLI Reference Guide for the Cisco Secure Access Control System 5.1 vi OL-18996-01
Reference Guide
Page 9
...Use this guide in conjunction with the documentation listed in Related Documentation, page xi. however, a few are straightforward; Subsequent sections build on the CSACS-1121 appliance. How to Use This Guide, page ix • How This Guide Is Organized, page x • Document Conventions, page x &#...preface includes: • Who Should Read This Guide, page ix • How to Use This Guide Cisco makes the following recommendations for all-inclusive information about the ACS appliance. • Do not vary the command-line conventions (see Document Conventions, page x). Who Should ...
...Use this guide in conjunction with the documentation listed in Related Documentation, page xi. however, a few are straightforward; Subsequent sections build on the CSACS-1121 appliance. How to Use This Guide, page ix • How This Guide Is Organized, page x • Document Conventions, page x &#...preface includes: • Who Should Read This Guide, page ix • How to Use This Guide Cisco makes the following recommendations for all-inclusive information about the ACS appliance. • Do not vary the command-line conventions (see Document Conventions, page x). Who Should ...
Reference Guide
Page 10
...system prompts appear in equipment damage or loss of data. bold courier font Examples of information you must select one. CLI Reference Guide for the Cisco Secure Access Control System 5.1 x OL-18996-01 Note Means reader take note. A tip might do something that appear within square brackets are ...or references to convey instructions and information. Convention Description bold font Commands and keywords. Using the ACS Command Line Describes how you can access and administer ACS Interface from the CLI. Preface How This Guide Is Organized This table lists the major sections of...
...system prompts appear in equipment damage or loss of data. bold courier font Examples of information you must select one. CLI Reference Guide for the Cisco Secure Access Control System 5.1 x OL-18996-01 Note Means reader take note. A tip might do something that appear within square brackets are ...or references to convey instructions and information. Convention Description bold font Commands and keywords. Using the ACS Command Line Describes how you can access and administer ACS Interface from the CLI. Preface How This Guide Is Organized This table lists the major sections of...
Reference Guide
Page 11
... Control System 5.1 xi You may find the following ACS-specific documentation helpful: • Installation and Upgrade Guide for the Cisco Secure Access Control System 5.1 • User Guide for the Cisco Secure Access Control System 5.1 • Regulatory Compliance and Safety Information for Cisco 1121 Secure Access Control System 5.1 and Cisco NAC Appliance 4.7 • Migration Guide for the...
... Control System 5.1 xi You may find the following ACS-specific documentation helpful: • Installation and Upgrade Guide for the Cisco Secure Access Control System 5.1 • User Guide for the Cisco Secure Access Control System 5.1 • Regulatory Compliance and Safety Information for Cisco 1121 Secure Access Control System 5.1 and Cisco NAC Appliance 4.7 • Migration Guide for the...
Reference Guide
Page 13
... configuration and monitoring tasks that are available in ACS Two different types of accounts are available on accessing the CLI, see Chapter 2, "Using the ACS Command Line Interface." You can access the ACS CLI through the web interface. 1 C H A P T E R Overview of the ACS Command Line Interface Cisco Secure Access Control System (ACS) 5.1 uses the CSACS-1121 appliance running Linux.
... configuration and monitoring tasks that are available in ACS Two different types of accounts are available on accessing the CLI, see Chapter 2, "Using the ACS Command Line Interface." You can access the ACS CLI through the web interface. 1 C H A P T E R Overview of the ACS Command Line Interface Cisco Secure Access Control System (ACS) 5.1 uses the CSACS-1121 appliance running Linux.
Reference Guide
Page 14
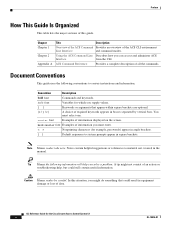
After you enter the initial configuration information, the appliance automatically reboots and prompts you to the ACS CLI, you must use the ACS CLI. Table 1-1 lists the command privileges for the Cisco Secure Access Control System 5.1 1-2 OL-18996-01 During this Admin account that you specified for the ... the functionality you require to use to log in to configure the appliance. User Accounts and Modes in ACS Chapter 1 Overview of the ACS Command Line Interface When you power up the CSACS-1121 appliance for the first time, you are prompted to run the setup utility to the...
After you enter the initial configuration information, the appliance automatically reboots and prompts you to the ACS CLI, you must use the ACS CLI. Table 1-1 lists the command privileges for the Cisco Secure Access Control System 5.1 1-2 OL-18996-01 During this Admin account that you specified for the ... the functionality you require to use to log in to configure the appliance. User Accounts and Modes in ACS Chapter 1 Overview of the ACS Command Line Interface When you power up the CSACS-1121 appliance for the first time, you are prompted to run the setup utility to the...
Reference Guide
Page 15
...kron logging commands mkdir nslookup ntp server password policy patch ping reload replication repository reset-management-interface-certificate restore commands rmdir service show acs-cores show acs-logs show acs-config-web-interface show application show backup show cdp show clock show cpu show debug-adclient show debug-log show disks show ... OL-18996-01 CLI Reference Guide for the Cisco Secure Access Control System 5.1 1-3
...kron logging commands mkdir nslookup ntp server password policy patch ping reload replication repository reset-management-interface-certificate restore commands rmdir service show acs-cores show acs-logs show acs-config-web-interface show application show backup show cdp show clock show cpu show debug-adclient show debug-log show disks show ... OL-18996-01 CLI Reference Guide for the Cisco Secure Access Control System 5.1 1-3
Reference Guide
Page 16
CLI Reference Guide for the Cisco Secure Access Control System 5.1 1-4 OL-18996-01 User Accounts and Modes in ACS Chapter 1 Overview of the ACS Command Line Interface Table 1-1 Command Privileges (continued) Command show inventory show ip route show logging show ... Logging in to the ACS server places you in requires a username and password. Typically, logging in the Operator (user) mode or the Admin (EXEC) mode.
CLI Reference Guide for the Cisco Secure Access Control System 5.1 1-4 OL-18996-01 User Accounts and Modes in ACS Chapter 1 Overview of the ACS Command Line Interface Table 1-1 Command Privileges (continued) Command show inventory show ip route show logging show ... Logging in to the ACS server places you in requires a username and password. Typically, logging in the Operator (user) mode or the Admin (EXEC) mode.
Reference Guide
Page 17
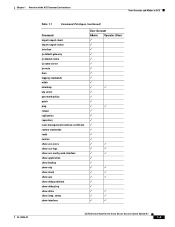
...EXEC mode and provides a short description of each. • Table 1-3 lists the show and reload (for the Cisco Secure Access Control System 5.1 1-5 The ACS configuration mode requires a specific, authorized user role to import or export configuration data, synchronize configuration information between the ...). a pound sign (#) appears at the end of EXEC Commands Command acs start | stop acs start and stop process acs backup acs-config acs delete core acs delete log Description Starts or stops an ACS server. EXEC Commands EXEC commands primarily include system-level commands such as...
...EXEC mode and provides a short description of each. • Table 1-3 lists the show and reload (for the Cisco Secure Access Control System 5.1 1-5 The ACS configuration mode requires a specific, authorized user role to import or export configuration data, synchronize configuration information between the ...). a pound sign (#) appears at the end of EXEC Commands Command acs start | stop acs start and stop process acs backup acs-config acs delete core acs delete log Description Starts or stops an ACS server. EXEC Commands EXEC commands primarily include system-level commands such as...
Reference Guide
Page 18
..., resource locking, file transfer, and user management. restore Restores a previous backup. ssh Starts an encrypted session with a remote system. CLI Reference Guide for ACS troubleshooting. acs support Gathers information for the Cisco Secure Access Control System 5.1 1-6 OL-18996-01 application remove Removes a specific application. backup Performs a backup and places the backup in the...
..., resource locking, file transfer, and user management. restore Restores a previous backup. ssh Starts an encrypted session with a remote system. CLI Reference Guide for ACS troubleshooting. acs support Gathers information for the Cisco Secure Access Control System 5.1 1-6 OL-18996-01 application remove Removes a specific application. backup Performs a backup and places the backup in the...
Reference Guide
Page 19
... debug logs. Displays information about the hardware inventory, including the ACS appliance model and serial number. Displays file-system information of the system clock. Displays information about the enabled Cisco Discovery Protocol (CDP) interfaces. Displays the day, date, time, time... Displays statistics for all the interfaces configured on the system for ACS configuration web. Sets the inactivity timeout for all terminal sessions. Table 1-3 Summary of the current session. for the Cisco Secure Access Control System 5.1 1-7 Indicates whether an interface is ...
... debug logs. Displays information about the hardware inventory, including the ACS appliance model and serial number. Displays file-system information of the system clock. Displays information about the enabled Cisco Discovery Protocol (CDP) interfaces. Displays the day, date, time, time... Displays statistics for all the interfaces configured on the system for ACS configuration web. Sets the inactivity timeout for all terminal sessions. Table 1-3 Summary of the current session. for the Cisco Secure Access Control System 5.1 1-7 Indicates whether an interface is ...
Reference Guide
Page 20
... running processes. Displays information about the CSACS-1121's Unique Device Identifier (UDI). Displays all the processes listening on roles in ACS. Table 1-4 lists the ACS Configuration commands and provides a short description of each ACS configuration command. Displays the contents of the configuration file that you can provide to the Cisco Technical Assistance Center (TAC) when you...
... running processes. Displays information about the CSACS-1121's Unique Device Identifier (UDI). Displays all the processes listening on roles in ACS. Table 1-4 lists the ACS Configuration commands and provides a short description of each ACS configuration command. Displays the contents of the configuration file that you can provide to the Cisco Technical Assistance Center (TAC) when you...
Reference Guide
Page 21
... can export that particular configuration data to a remote repository. debug-log Defines the local debug logging level for the Cisco Secure Access Control System 5.1 1-9 Only the super admin can issue the ACS components. import-export-sta Displays the status of the import and tus export processes. can issue this addresses to the...
... can export that particular configuration data to a remote repository. debug-log Defines the local debug logging level for the Cisco Secure Access Control System 5.1 1-9 Only the super admin can issue the ACS components. import-export-sta Displays the status of the import and tus export processes. can issue this addresses to the...
Reference Guide
Page 22
...Sets the time zone for backup and restore operations. Returns to complete hostnames. Configures the ICMP echo requests. For detailed information on ACS Configuration mode commands, see Understanding Command Modes, page 2-6. Some of the system. To access the Configuration mode, run cdp timer...during a DNS query. 1-10 CLI Reference Guide for the Ethernet interface. Specifies how often the ACS server sends CDP updates. Sets the IP address and netmask for the Cisco Secure Access Control System 5.1 OL-18996-01 Note This is an interface configuration command. Specifies ...
...Sets the time zone for backup and restore operations. Returns to complete hostnames. Configures the ICMP echo requests. For detailed information on ACS Configuration mode commands, see Understanding Command Modes, page 2-6. Some of the system. To access the Configuration mode, run cdp timer...during a DNS query. 1-10 CLI Reference Guide for the Ethernet interface. Specifies how often the ACS server sends CDP updates. Sets the IP address and netmask for the Cisco Secure Access Control System 5.1 OL-18996-01 Note This is an interface configuration command. Specifies ...
Reference Guide
Page 23
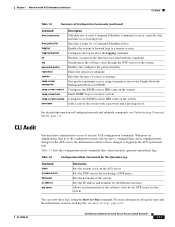
...DNS query. Chapter 1 Overview of the ACS Command Line Interface CLI Audit Table 1-5 Summary of the system. Sends SNMP traps to the Simple Network Management Protocol (SNMP). Enters the repository submode. Sets the DNS servers for the Cisco Secure Access Control System 5.1 1-11 ...Sets the IP address and netmask for a Command Scheduler policy. Specifies a name for the Ethernet interface. Enables the system to forward logs to execute ACS configuration commands. Configures the SNMP location ...
...DNS query. Chapter 1 Overview of the ACS Command Line Interface CLI Audit Table 1-5 Summary of the system. Sends SNMP traps to the Simple Network Management Protocol (SNMP). Enters the repository submode. Sets the DNS servers for the Cisco Secure Access Control System 5.1 1-11 ...Sets the IP address and netmask for a Command Scheduler policy. Specifies a name for the Ethernet interface. Enables the system to forward logs to execute ACS configuration commands. Configures the SNMP location ...
Reference Guide
Page 24
... management interface certificate to factory defaults. Deletes an ACS run -time core file or JVM core log. Table 1-8 ACS Configuration Mode Commands for the Cisco Secure Access Control System 5.1 OL-18996-01 Starts or stops an ACS process. replication Synchronizes configuration information between the primary and secondary ACS. 1-12 CLI Reference Guide for the Operation...
... management interface certificate to factory defaults. Deletes an ACS run -time core file or JVM core log. Table 1-8 ACS Configuration Mode Commands for the Cisco Secure Access Control System 5.1 OL-18996-01 Starts or stops an ACS process. replication Synchronizes configuration information between the primary and secondary ACS. 1-12 CLI Reference Guide for the Operation...
Reference Guide
Page 25
... • Where to Go Next, page 2-13 Before Accessing the ACS CLI Before logging in to Configure ACS, page 2-2 OL-18996-01 CLI Reference Guide for understanding and configuring the Cisco Secure ACS 5.1 from the CLI. Starting the CSACS-1121, page 2-2 2. Running Setup to the ACS CLI, review the tasks that you should have completed during hardware...
... • Where to Go Next, page 2-13 Before Accessing the ACS CLI Before logging in to Configure ACS, page 2-2 OL-18996-01 CLI Reference Guide for understanding and configuring the Cisco Secure ACS 5.1 from the CLI. Starting the CSACS-1121, page 2-2 2. Running Setup to the ACS CLI, review the tasks that you should have completed during hardware...