User Guide
Page 12
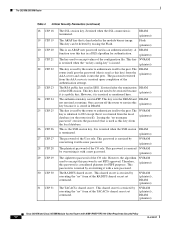
... by executing the "no key config-key" is issued. (plaintext) This key is a public key; NVRAM (plaintext) This is in SSH. NVRAM (plaintext) The RADIUS shared secret. This shared secret is zeroized upon completion of the RADIUS shared secret set command. This key does...this key in DRAM. This password is terminated. Issuing the "no " form of the CO role. NVRAM (plaintext), DRAM (plaintext) Cisco 2621XM and Cisco 2651XM Modular Access Routers with a new password. This password is stored in a DES algorithm for FIPS purposes. This key can turn off...
... by executing the "no key config-key" is issued. (plaintext) This key is a public key; NVRAM (plaintext) This is in SSH. NVRAM (plaintext) The RADIUS shared secret. This shared secret is zeroized upon completion of the RADIUS shared secret set command. This key does...this key in DRAM. This password is terminated. Issuing the "no " form of the CO role. NVRAM (plaintext), DRAM (plaintext) Cisco 2621XM and Cisco 2651XM Modular Access Routers with a new password. This password is stored in a DES algorithm for FIPS purposes. This key can turn off...
User Guide
Page 19
...connections via telnet are secured through IPSec. • SSH access to the following algorithms are available on Cisco.com. MD-4 and MD-5 for Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Routers Obtaining Documentation Cisco documentation and additional literature are not FIPS approved and ... Crypto officer must configure the module so that SSH uses only FIPS-approved algorithms. Related Documentation For more information about the Cisco 2621XM and Cisco 2651XM modular access routers, refer to the module is only allowed if SSH is only allowed via a secure IPSec tunnel...
...connections via telnet are secured through IPSec. • SSH access to the following algorithms are available on Cisco.com. MD-4 and MD-5 for Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Routers Obtaining Documentation Cisco documentation and additional literature are not FIPS approved and ... Crypto officer must configure the module so that SSH uses only FIPS-approved algorithms. Related Documentation For more information about the Cisco 2621XM and Cisco 2651XM modular access routers, refer to the module is only allowed if SSH is only allowed via a secure IPSec tunnel...