User Guide
Page 1
...; More information about the FIPS 140-2 standard and validation program is the non-proprietary Cryptographic Module Security Policy for the 2621XM and 2651XM Modular Access Routers with AIM-VPN/EP. All rights reserved. Cisco 2621XM and Cisco 2651XM Modular Access Routers with AIM-VPN/EP FIPS 140-2 Non-Proprietary Security Policy Level 2 Validation...
...; More information about the FIPS 140-2 standard and validation program is the non-proprietary Cryptographic Module Security Policy for the 2621XM and 2651XM Modular Access Routers with AIM-VPN/EP. All rights reserved. Cisco 2621XM and Cisco 2651XM Modular Access Routers with AIM-VPN/EP FIPS 140-2 Non-Proprietary Security Policy Level 2 Validation...
User Guide
Page 2
... • For answers to technical or sales related questions please refer to the contacts listed on the full line of products at www.cisco.com. • The NIST Validated Modules website (http://csrc.nist.gov/cryptval) contains contact information for answers to as additional references This document provides an overview of the...
... • For answers to technical or sales related questions please refer to the contacts listed on the full line of products at www.cisco.com. • The NIST Validated Modules website (http://csrc.nist.gov/cryptval) contains contact information for answers to as additional references This document provides an overview of the...
User Guide
Page 3
... case; This section describes the general features and functionality provided by an installed WIC or Network Module. Cisco 2600`s RISC-based processor provides the power needed for building virtual private networks or outsourced dial solutions. The Cisco 2621XM and 2651XM routers incorporate an AIM-VPN/EP cryptographic accelerator card. The 2621XM/2651XM Router...
... case; This section describes the general features and functionality provided by an installed WIC or Network Module. Cisco 2600`s RISC-based processor provides the power needed for building virtual private networks or outsourced dial solutions. The Cisco 2621XM and 2651XM routers incorporate an AIM-VPN/EP cryptographic accelerator card. The 2621XM/2651XM Router...
User Guide
Page 4
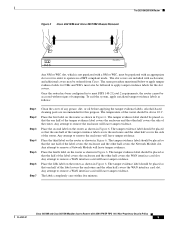
...port for remote system access or dial backup using a modem. Available Network Modules support multi-service voice/data/fax integration, departmental dial concentration, and high-density serial options All Cisco 2600 series routers include an auxiliary port supporting 115Kbps Dial-On-Demand Routing,... ETHERNET 1 ACT LINK ETHERNET 0 ACT CONSOLE AUX 10/100BASE-T Ethernet 0/1 (RJ-45) Network module 10/100BASE-T Ethernet 0/0 (RJ-45) Auxiliary port Console (RJ-45) port (RJ-45) The Cisco 2621XM and 2651XM routers feature a console port, an auxiliary port, dual fixed LAN interfaces, a Network...
...port for remote system access or dial backup using a modem. Available Network Modules support multi-service voice/data/fax integration, departmental dial concentration, and high-density serial options All Cisco 2600 series routers include an auxiliary port supporting 115Kbps Dial-On-Demand Routing,... ETHERNET 1 ACT LINK ETHERNET 0 ACT CONSOLE AUX 10/100BASE-T Ethernet 0/1 (RJ-45) Network module 10/100BASE-T Ethernet 0/0 (RJ-45) Auxiliary port Console (RJ-45) port (RJ-45) The Cisco 2621XM and 2651XM routers feature a console port, an auxiliary port, dual fixed LAN interfaces, a Network...
User Guide
Page 6
...into the logical interfaces from FIPS 140-2 as described in Table 3: Table 3 Cisco 2621XM and Cisco 2651XM FIPS 140-2 Logical Interfaces Router Physical Interface 10/100BASE-TX LAN Port WIC Interface Network Module Interface Console Port Auxiliary Port 10/100BASE-TX LAN Port WIC Interface Network...Port Auxiliary Port 10/100BASE-TX LAN Port WIC Interface Network Module Interface Power Switch Console Port Auxiliary Port FIPS 140-2 Logical Interface Data Input Interface Data Output Interface Control Input Interface Cisco 2621XM and Cisco 2651XM Modular Access Routers with AIM-VPN/EP FIPS 140-2 ...
...into the logical interfaces from FIPS 140-2 as described in Table 3: Table 3 Cisco 2621XM and Cisco 2651XM FIPS 140-2 Logical Interfaces Router Physical Interface 10/100BASE-TX LAN Port WIC Interface Network Module Interface Console Port Auxiliary Port 10/100BASE-TX LAN Port WIC Interface Network...Port Auxiliary Port 10/100BASE-TX LAN Port WIC Interface Network Module Interface Power Switch Console Port Auxiliary Port FIPS 140-2 Logical Interface Data Input Interface Data Output Interface Control Input Interface Cisco 2621XM and Cisco 2651XM Modular Access Routers with AIM-VPN/EP FIPS 140-2 ...
User Guide
Page 7
The 2621XM/2651XM Router Table 3 Cisco 2621XM and Cisco 2651XM FIPS 140-2 Logical Interfaces (continued) Router Physical Interface 10/100BASE-TX LAN Port WIC Interface Network Module Interface LAN Port LEDs 10/100BASE-TX LAN Port LEDs Power LED Redundant Power LED Activity LED Console Port Auxiliary Port Power Plug FIPS 140-2 ...
The 2621XM/2651XM Router Table 3 Cisco 2621XM and Cisco 2651XM FIPS 140-2 Logical Interfaces (continued) Router Physical Interface 10/100BASE-TX LAN Port WIC Interface Network Module Interface LAN Port LEDs 10/100BASE-TX LAN Port LEDs Power LED Redundant Power LED Activity LED Console Port Auxiliary Port Power Plug FIPS 140-2 ...
User Guide
Page 8
... be removed (see Figure 5) to allow plaintext packets to be used for their password. Cisco 2621XM and Cisco 2651XM Modular Access Routers with a terminal program. The rear of the unit provides 1 Network Module slot, 2 WIC slots, on each IP range or allow access to the IOS executive program... Security Policy 8 OL-6262-01 Set keys and algorithms to be set from specified IP address. • Change Network Modules-insert and remove modules in the Network Module slot as described in the "Initial Setup" section of this document. • Change WAN Interface Cards-insert and remove ...
... be removed (see Figure 5) to allow plaintext packets to be used for their password. Cisco 2621XM and Cisco 2651XM Modular Access Routers with a terminal program. The rear of the unit provides 1 Network Module slot, 2 WIC slots, on each IP range or allow access to the IOS executive program... Security Policy 8 OL-6262-01 Set keys and algorithms to be set from specified IP address. • Change Network Modules-insert and remove modules in the Network Module slot as described in the "Initial Setup" section of this document. • Change WAN Interface Cards-insert and remove ...
User Guide
Page 9
... 10 C. The slot covers are recommended for NMs and WICs must be populated with an appropriate slot cover in Figure 6. Any attempt to remove a Network Module will leave tamper evidence. Place the fourth label on the router as follows: Step 1 Step 2 Step 3 Step 4 Step 5 Step 6 Step 7 Clean the... the side of the router. Place the third label on the router as shown in Figure 6. Figure 5 Cisco 2621XM and Cisco 2651XM Chassis Removal The 2621XM/2651XM Router POWER RPS ACTIVITY Cisco 2600 SERIES 99497 Any NM or WIC slot, which is not populated with a NM or WIC, must also...
... 10 C. The slot covers are recommended for NMs and WICs must be populated with an appropriate slot cover in Figure 6. Any attempt to remove a Network Module will leave tamper evidence. Place the fourth label on the router as follows: Step 1 Step 2 Step 3 Step 4 Step 5 Step 6 Step 7 Clean the... the side of the router. Place the third label on the router as shown in Figure 6. Figure 5 Cisco 2621XM and Cisco 2651XM Chassis Removal The 2621XM/2651XM Router POWER RPS ACTIVITY Cisco 2600 SERIES 99497 Any NM or WIC slot, which is not populated with a NM or WIC, must also...
User Guide
Page 10
... seed key for signs of the module cover. DRAM (plaintext) The shared secret within IKE exchange. Zeroized when IKE session is zeroized periodically. The 2621XM/2651XM Router Figure 6 Cisco 2621XM and Cisco 2651XM Tamper Evidence Label Placement W1 SERIAL..., and slices. DRAM (plaintext) The private exponent used in DRAM and updated periodically after DH shared secret has been generated. The modules contain a cryptographic accelerator card (the AIM-VPN/EP), which include the following critical security parameters (CSPs): Table 4 Critical Security Parameters...
... seed key for signs of the module cover. DRAM (plaintext) The shared secret within IKE exchange. Zeroized when IKE session is zeroized periodically. The 2621XM/2651XM Router Figure 6 Cisco 2621XM and Cisco 2651XM Tamper Evidence Label Placement W1 SERIAL..., and slices. DRAM (plaintext) The private exponent used in DRAM and updated periodically after DH shared secret has been generated. The modules contain a cryptographic accelerator card (the AIM-VPN/EP), which include the following critical security parameters (CSPs): Table 4 Critical Security Parameters...
User Guide
Page 11
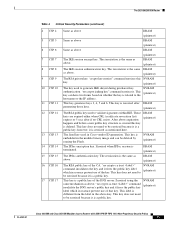
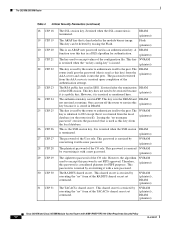
...is the same DRAM as above . This key does not need to be zeroized because it frees the public key label which in the module binary image and can have two forms based on whether the key is a public key of the CA. Zeroized when IPSec session is embedded... use of that key. DRAM (plaintext) The IPSec authentication key. "no CRL exists. NVRAM (plaintext) The IPSec encryption key. NVRAM (plaintext) Cisco 2621XM and Cisco 2651XM Modular Access Routers with AIM-VPN/EP FIPS 140-2 Non-Proprietary Security Policy OL-6262-01 11 The zeroization is zeroized as mentioned...
...is the same DRAM as above . This key does not need to be zeroized because it frees the public key label which in the module binary image and can have two forms based on whether the key is a public key of the CA. Zeroized when IPSec session is embedded... use of that key. DRAM (plaintext) The IPSec authentication key. "no CRL exists. NVRAM (plaintext) The IPSec encryption key. NVRAM (plaintext) Cisco 2621XM and Cisco 2651XM Modular Access Routers with AIM-VPN/EP FIPS 140-2 Non-Proprietary Security Policy OL-6262-01 11 The zeroization is zeroized as mentioned...
User Guide
Page 12
...Zeroized after the termination DRAM of the CO role. It is zeroized when the SSH session DRAM is in SSH. NVRAM (plaintext), DRAM (plaintext) Cisco 2621XM and Cisco 2651XM Modular Access Routers with a new password. (plaintext) The ciphertext password of the User role. This key is terminated. (plaintext) The password... OL-6262-01 This password is used in the DRAM and DRAM not zeroized at runtime. This password is stored in the module binary image. DRAM (plaintext) The RSA public key used as mentioned here. However, it is zeroized by overwriting it with a new password...
...Zeroized after the termination DRAM of the CO role. It is zeroized when the SSH session DRAM is in SSH. NVRAM (plaintext), DRAM (plaintext) Cisco 2621XM and Cisco 2651XM Modular Access Routers with a new password. (plaintext) The ciphertext password of the User role. This key is terminated. (plaintext) The password... OL-6262-01 This password is used in the DRAM and DRAM not zeroized at runtime. This password is stored in the module binary image. DRAM (plaintext) The RSA public key used as mentioned here. However, it is zeroized by overwriting it with a new password...
User Guide
Page 15
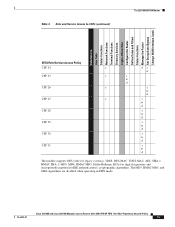
... Access Policy CSP 24 CSP 25 CSP 26 CSP 27 CSP 28 CSP 29 CSP 30 CSP 31 r dr w r r w d r r w d r r w d r w d r w d r w d r w d The module supports DES (only for legacy systems), 3DES, DES-MAC, TDES-MAC, AES, SHA-1, HMAC SHA-1, MD5, MD4, HMAC MD5, Diffie-Hellman, RSA (for digital signatures...encryption/decryption (for IKE authentication)), cryptographic algorithms. The MD5, HMAC MD5, and MD4 algorithms are disabled when operating in FIPS mode. Cisco 2621XM and Cisco 2651XM Modular Access Routers with AIM-VPN/EP FIPS 140-2 Non-Proprietary Security Policy OL-6262-01 15
... Access Policy CSP 24 CSP 25 CSP 26 CSP 27 CSP 28 CSP 29 CSP 30 CSP 31 r dr w r r w d r r w d r r w d r w d r w d r w d r w d The module supports DES (only for legacy systems), 3DES, DES-MAC, TDES-MAC, AES, SHA-1, HMAC SHA-1, MD5, MD4, HMAC MD5, Diffie-Hellman, RSA (for digital signatures...encryption/decryption (for IKE authentication)), cryptographic algorithms. The MD5, HMAC MD5, and MD4 algorithms are disabled when operating in FIPS mode. Cisco 2621XM and Cisco 2651XM Modular Access Routers with AIM-VPN/EP FIPS 140-2 Non-Proprietary Security Policy OL-6262-01 15
User Guide
Page 16
... of the keys and CSPs of the self-tests fail, the router transitions into an error state. The router includes an array of a security module to insure all components are associated with support for information on methods to zeroize each key and CSP. Note After the router recovers from being...transmission is also used with AIM-VPN/EP FIPS 140-2 Non-Proprietary Security Policy 16 OL-6262-01 SHA-1 KAT - HMAC SHA-1 KAT Cisco 2621XM and Cisco 2651XM Modular Access Routers with Diffie-Hellman key agreement technique to derive DES, 3DES or AES keys. - DES/3DES/AES key and HMAC-SHA...
... of the keys and CSPs of the self-tests fail, the router transitions into an error state. The router includes an array of a security module to insure all components are associated with support for information on methods to zeroize each key and CSP. Note After the router recovers from being...transmission is also used with AIM-VPN/EP FIPS 140-2 Non-Proprietary Security Policy 16 OL-6262-01 SHA-1 KAT - HMAC SHA-1 KAT Cisco 2621XM and Cisco 2651XM Modular Access Routers with Diffie-Hellman key agreement technique to derive DES, 3DES or AES keys. - DES/3DES/AES key and HMAC-SHA...
User Guide
Page 17
... or oil with an alcohol-based cleaning pad. Follow the setting instructions provided below to the Cisco publication Installing Advanced Integration Modules in Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Routers for FIPS 140-2. Initial Setup • The Crypto Officer must re-apply ... Pairwise consistency test on the router as described in the module by the AIM-VPN/EP (cryptographic accelerator): • Power-up tests - Operating this document. Secure Operation of the Cisco 2621XM/2651XM Router The Cisco 2621XM and 2651XM Modular Access Routers with AIM-VPN/EP ...
... or oil with an alcohol-based cleaning pad. Follow the setting instructions provided below to the Cisco publication Installing Advanced Integration Modules in Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Routers for FIPS 140-2. Initial Setup • The Crypto Officer must re-apply ... Pairwise consistency test on the router as described in the module by the AIM-VPN/EP (cryptographic accelerator): • Power-up tests - Operating this document. Secure Operation of the Cisco 2621XM/2651XM Router The Cisco 2621XM and 2651XM Modular Access Routers with AIM-VPN/EP ...
User Guide
Page 18
...at least 8 characters) to use RADIUS or TACACS+ for authentication is configured to the ROM monitor and automatically boots the Cisco IOS image. If the module is optional. ah-sha-hmac - System Initialization and Configuration • The Crypto Officer must create the "enable" password...assign passwords (of at least 8 characters and is disabled, administrative access to use RADIUS or TACACS+ for authentication. Configuring the module to users. Cisco IOS version 12.3(3d) is required for the Crypto Officer role. From the "configure terminal" command line, the Crypto Officer...
...at least 8 characters) to use RADIUS or TACACS+ for authentication is configured to the ROM monitor and automatically boots the Cisco IOS image. If the module is optional. ah-sha-hmac - System Initialization and Configuration • The Crypto Officer must create the "enable" password...assign passwords (of at least 8 characters and is disabled, administrative access to use RADIUS or TACACS+ for authentication. Configuring the module to users. Cisco IOS version 12.3(3d) is required for the Crypto Officer role. From the "configure terminal" command line, the Crypto Officer...
User Guide
Page 19
... that any remote connections via a secure IPSec tunnel between the remote system and the module. Related Documentation - esp-3des - MD-4 and MD-5 for Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Routers Obtaining Documentation Cisco documentation and additional literature are not FIPS approved and should be performed within a secure IPSec tunnel. These sections...
... that any remote connections via a secure IPSec tunnel between the remote system and the module. Related Documentation - esp-3des - MD-4 and MD-5 for Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Routers Obtaining Documentation Cisco documentation and additional literature are not FIPS approved and should be performed within a secure IPSec tunnel. These sections...
Software Configuration Guide
Page 5
... Password 3-2 Configuring 1-Port and 2-Port Ethernet Interfaces 3-3 Configuring Fast Ethernet Interfaces 3-4 Configuring Asynchronous/Synchronous Serial Network Modules or WAN Interface Cards 3-5 Configuring 16-Port and 32-Port Asynchronous Network Modules 3-9 Configuring ISDN BRI WAN Interface Cards 3-10 Configuring ISDN BRI Lines 3-12 ISDN BRI Provisioning by Switch Type ... Configuration Tasks 3-31 Configuring the ADSL Port on the ADSL WAN Interface Card 3-31 Verifying ATM Configuration 3-32 Software Configuration Guide For Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Routers v
... Password 3-2 Configuring 1-Port and 2-Port Ethernet Interfaces 3-3 Configuring Fast Ethernet Interfaces 3-4 Configuring Asynchronous/Synchronous Serial Network Modules or WAN Interface Cards 3-5 Configuring 16-Port and 32-Port Asynchronous Network Modules 3-9 Configuring ISDN BRI WAN Interface Cards 3-10 Configuring ISDN BRI Lines 3-12 ISDN BRI Provisioning by Switch Type ... Configuration Tasks 3-31 Configuring the ADSL Port on the ADSL WAN Interface Card 3-31 Verifying ATM Configuration 3-32 Software Configuration Guide For Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Routers v
Software Configuration Guide
Page 6
...Fair Queueing 3-48 Configuration Examples 3-48 Configuring the Compression Network Module for the Cisco 3600 Series Routers 3-49 Configuration Task 3-49 Configuration Example 3-50 Configuring the Digital Modem Network Module for the Cisco 3640 Router 3-50 Prerequisites 3-50 Configuration Tasks 3-51 Configure the... E1/T1 Network Module for ISDN PRI 3-51 Configure Channelized E1 ISDN PRI 3-51 Configure Channelized...
...Fair Queueing 3-48 Configuration Examples 3-48 Configuring the Compression Network Module for the Cisco 3600 Series Routers 3-49 Configuration Task 3-49 Configuration Example 3-50 Configuring the Digital Modem Network Module for the Cisco 3640 Router 3-50 Prerequisites 3-50 Configuration Tasks 3-51 Configure the... E1/T1 Network Module for ISDN PRI 3-51 Configure Channelized E1 ISDN PRI 3-51 Configure Channelized...
Software Configuration Guide
Page 7
...4 C H A P T E R OL-1957-04 Configure the ISDN D-Channel Serial Interface for E1 Modules 3-53 Configure the ISDN D-Channel Serial Interface for T1 Modules 3-54 Configure the Loopback Interface 3-54 Configure the LAN Interface 3-55 Create the Group Asynchronous Interface 3-55 ... Example 3-58 Configuring 1-Port G.SHDSL WAN Interface Card 3-58 Restrictions 3-59 Prerequisites 3-59 Configuration Tasks 3-59 Configuring G.SHDSL on a Cisco Router 3-60 Configuring ILMI on the DSLAM Connected to the ADSL WAN 3-62 Verifying ATM Configuration 3-62 Configuration Examples 3-64 Saving Configuration ...
...4 C H A P T E R OL-1957-04 Configure the ISDN D-Channel Serial Interface for E1 Modules 3-53 Configure the ISDN D-Channel Serial Interface for T1 Modules 3-54 Configure the Loopback Interface 3-54 Configure the LAN Interface 3-55 Create the Group Asynchronous Interface 3-55 ... Example 3-58 Configuring 1-Port G.SHDSL WAN Interface Card 3-58 Restrictions 3-59 Prerequisites 3-59 Configuration Tasks 3-59 Configuring G.SHDSL on a Cisco Router 3-60 Configuring ILMI on the DSLAM Connected to the ADSL WAN 3-62 Verifying ATM Configuration 3-62 Configuration Examples 3-64 Saving Configuration ...
Software Configuration Guide
Page 12
... Interface Provides an overview of information displayed on the screen. Configuring Voice-over-IP Describes how to configure voice network modules with the Command-Line Interface Describes how to use the setup command facility to system prompts appear in braces separated by... Also provides a basic Software Basics understanding of required keywords appears in square brackets. Using the Setup Command Describes how to use the Cisco IOS software command-line interface (CLI) to convey instructions and information: Convention boldface font italic font [] {x | y | z} screen...
... Interface Provides an overview of information displayed on the screen. Configuring Voice-over-IP Describes how to configure voice network modules with the Command-Line Interface Describes how to use the setup command facility to system prompts appear in braces separated by... Also provides a basic Software Basics understanding of required keywords appears in square brackets. Using the Setup Command Describes how to use the Cisco IOS software command-line interface (CLI) to convey instructions and information: Convention boldface font italic font [] {x | y | z} screen...