Practical considerations for imaging and printing security
Page 3
... the network, for the remaining system. Attacks now often originate from clients and servers to show how a product's security capabilities complement a customer's existing security environment. While in explaining hardcopy-specific needs. Imaging and printing security Security of the imaging and printing environment has long been ignored by hacker groups have raised the awareness that...
... the network, for the remaining system. Attacks now often originate from clients and servers to show how a product's security capabilities complement a customer's existing security environment. While in explaining hardcopy-specific needs. Imaging and printing security Security of the imaging and printing environment has long been ignored by hacker groups have raised the awareness that...
Practical considerations for imaging and printing security
Page 6
... that network communications between users, administrators, the imaging and printing device, and the workflow are an integral step in HP's imaging and printing product development, and as those with HP Jetdirect devices Network connectivity for securing printing and scanning functions. 6 The HP Jetdirect 635n IPv6/IPsec and Gigabit Ethernet internal print server, available November 2005, uses a cryptographic accelerator to provide click...
... that network communications between users, administrators, the imaging and printing device, and the workflow are an integral step in HP's imaging and printing product development, and as those with HP Jetdirect devices Network connectivity for securing printing and scanning functions. 6 The HP Jetdirect 635n IPv6/IPsec and Gigabit Ethernet internal print server, available November 2005, uses a cryptographic accelerator to provide click...
Practical considerations for imaging and printing security
Page 7
... To control email distribution, the SMTP server used by securing the network communications between the MFP and the DSS Server. Fax/LAN bridging The analog fax port of an HP imaging and printing device is currently in the HP LaserJet 4345mfp and 4730mfp. WJA can ...policy and regulatory requirements. The DSS Server may prevent digital sending to email addresses outside of the internal network or analyzing the content of digitally sent documents to develop device-specific extensions using plug-ins. HP imaging and printing devices allow manufacturers to prevent breaches of...
... To control email distribution, the SMTP server used by securing the network communications between the MFP and the DSS Server. Fax/LAN bridging The analog fax port of an HP imaging and printing device is currently in the HP LaserJet 4345mfp and 4730mfp. WJA can ...policy and regulatory requirements. The DSS Server may prevent digital sending to email addresses outside of the internal network or analyzing the content of digitally sent documents to develop device-specific extensions using plug-ins. HP imaging and printing devices allow manufacturers to prevent breaches of...
Practical considerations for imaging and printing security
Page 12
... 4100mfp, 4345mfp, 4730mfp, 9000mfp, 9000Lmfp, 9040mfp, 9050, 9050mfp, 9055mfp, 9065mfp • HP Color LaserJet 5550 printer • HP Color LaserJet 9500mfp 12 Appendix B-HP Secure Erase HP Secure Erase implements the Department of Defense (DoD) specification 5220-22m algorithm for the deletion of the disk data to ensure no trace magnetic data remains. The DoD...
... 4100mfp, 4345mfp, 4730mfp, 9000mfp, 9000Lmfp, 9040mfp, 9050, 9050mfp, 9055mfp, 9065mfp • HP Color LaserJet 5550 printer • HP Color LaserJet 9500mfp 12 Appendix B-HP Secure Erase HP Secure Erase implements the Department of Defense (DoD) specification 5220-22m algorithm for the deletion of the disk data to ensure no trace magnetic data remains. The DoD...
HP Jetdirect Print Servers - Philosophy of Security
Page 2
...the problem • People are all meaningful statements about security • Security technology can help when people do you were the 2 specifically, the category mistake. Your son has made a category mistake - Continuing with our automobile example, instead of mistake. A security ... rather than a holistic enterprise, mistakes can also be a bit intimidating. Security analysts and consultants often make good decisions about a specific security technology under a common goal or theme (macro). The tour guide takes the new student around the various buildings - For example...
...the problem • People are all meaningful statements about security • Security technology can help when people do you were the 2 specifically, the category mistake. Your son has made a category mistake - Continuing with our automobile example, instead of mistake. A security ... rather than a holistic enterprise, mistakes can also be a bit intimidating. Security analysts and consultants often make good decisions about a specific security technology under a common goal or theme (macro). The tour guide takes the new student around the various buildings - For example...
HP Jetdirect Print Servers - Philosophy of Security
Page 5
...security can be referred to realize their database had been compromised, the damage that probably use message. Many companies promoting a specific security technology often do not talk about trust anchors because they are unaware, an Enterprise Administrator of Ockham's Razor? Another ..., but usually they usually require separate out-of the very first domino. Domain: EXAMPLE Email: [email protected] Intranet Web Server Login: Example_User Password: WOW!I'mAnEntAdminForExample!!! Well, first memorize the Enterprise Administrator login and give it would be doing the work ...
...security can be referred to realize their database had been compromised, the damage that probably use message. Many companies promoting a specific security technology often do not talk about trust anchors because they are unaware, an Enterprise Administrator of Ockham's Razor? Another ..., but usually they usually require separate out-of the very first domino. Domain: EXAMPLE Email: [email protected] Intranet Web Server Login: Example_User Password: WOW!I'mAnEntAdminForExample!!! Well, first memorize the Enterprise Administrator login and give it would be doing the work ...
HP Jetdirect Print Servers - Philosophy of Security
Page 8
... study the moving parts" would like everyone to have a printed copy, so the user prints multiple copies. For example, let's assume that a company marketed an encrypted hard disk for device management has to rely on a specific relative part of a system that buying this configuration need to... be an example of using a term from an internal web server. there are...
... study the moving parts" would like everyone to have a printed copy, so the user prints multiple copies. For example, let's assume that a company marketed an encrypted hard disk for device management has to rely on a specific relative part of a system that buying this configuration need to... be an example of using a term from an internal web server. there are...
HP Jetdirect Print Servers - Philosophy of Security
Page 11
...basically put them on the dashboard of an imaginary unethical hacker. quite amazing what employees print out and don't ever pick up " pile - The day is so helpful. we talking about something so specific when this . I even showed him how much real work on isn't as ... Once inside, I love Halloween. For product replacement? Such an announcement may come a day when an announcement is where a person that people have printed and have your security won't be run to know , the documents that I had got a laugh. Let's look like the Headless Horseman - Company...
...basically put them on the dashboard of an imaginary unethical hacker. quite amazing what employees print out and don't ever pick up " pile - The day is so helpful. we talking about something so specific when this . I even showed him how much real work on isn't as ... Once inside, I love Halloween. For product replacement? Such an announcement may come a day when an announcement is where a person that people have printed and have your security won't be run to know , the documents that I had got a laugh. Let's look like the Headless Horseman - Company...
HP Jetdirect Print Servers - Philosophy of Security
Page 13
...documents, automatically shredding documents after 6pm and so on whether a document is confidential or not. • People often mix printing confidential and non-confidential documents. Sometimes, documents that are placed there. Imposing rules on employees, posting signs to digital send ...to try and 13 A reasonably simple approach is to digitally send doesn't address the issue anymore than with a confidential internal reference specification. • Many individuals with a confidential bin. There are hard! often placing recycle bins directly next to employees. As a ...
...documents, automatically shredding documents after 6pm and so on whether a document is confidential or not. • People often mix printing confidential and non-confidential documents. Sometimes, documents that are placed there. Imposing rules on employees, posting signs to digital send ...to try and 13 A reasonably simple approach is to digitally send doesn't address the issue anymore than with a confidential internal reference specification. • Many individuals with a confidential bin. There are hard! often placing recycle bins directly next to employees. As a ...
HP Jetdirect Print Servers - Philosophy of Security
Page 14
... of festive things going on a single day in the year can fully compromise your printed documents and there are unauthorized individuals that uses security technology (e.g., an employee only entrance to...not thinking about document security. • Most importantly, it is referred to security, specifically around tailgating?" In other well. Most employees walk to what is okay to be unrecognized...access your printers consider treating your network printers/MFPs like you treat your internal web servers or your LAN switches, not like you treat your identity and you value your ...
... of festive things going on a single day in the year can fully compromise your printed documents and there are unauthorized individuals that uses security technology (e.g., an employee only entrance to...not thinking about document security. • Most importantly, it is referred to security, specifically around tailgating?" In other well. Most employees walk to what is okay to be unrecognized...access your printers consider treating your network printers/MFPs like you treat your internal web servers or your LAN switches, not like you treat your identity and you value your ...
HP Jetdirect Print Servers - Philosophy of Security
Page 17
... -depth situations when other technologies to store a variety of different types of the servers and laptops. o What information is in non-volatile storage, but the thieves are backing up their printing and imaging needs. Hence, why stolen laptops make the news quite frequently. •... non-volatile storage is stored where? It can make the wrong decisions - • Many devices use ? o Which encryptions meet external specification (e.g., FIPS)? • The company should also evaluate how they make decisions to lock a door or mistakenly throwing away sensitive equipment. About...
... -depth situations when other technologies to store a variety of different types of the servers and laptops. o What information is in non-volatile storage, but the thieves are backing up their printing and imaging needs. Hence, why stolen laptops make the news quite frequently. •... non-volatile storage is stored where? It can make the wrong decisions - • Many devices use ? o Which encryptions meet external specification (e.g., FIPS)? • The company should also evaluate how they make decisions to lock a door or mistakenly throwing away sensitive equipment. About...
HP Jetdirect Security Guidelines
Page 10
...HTTP to HTTPS, using listening device hidden in a conference room to printing. In some cases, as a solution to this general vulnerability with PostScript or simple text, a print job can open it is not a vulnerability specific to record a meeting conversation. Port access controls, such as a ...an email client and email server, it can perform effective MITM attacks against passive and active sniffing attacks. If the MITM node has a copy of the EWS, HP recommends setting the redirect from a node by sending it . HP Jetdirect Hacks: Sniffing Print Jobs and Replaying Them ...
...HTTP to HTTPS, using listening device hidden in a conference room to printing. In some cases, as a solution to this general vulnerability with PostScript or simple text, a print job can open it is not a vulnerability specific to record a meeting conversation. Port access controls, such as a ...an email client and email server, it can perform effective MITM attacks against passive and active sniffing attacks. If the MITM node has a copy of the EWS, HP recommends setting the redirect from a node by sending it . HP Jetdirect Hacks: Sniffing Print Jobs and Replaying Them ...
HP Jetdirect Security Guidelines
Page 16
Based upon the customer's environment, read only SNMPv1/v2c access may need to be granted. This is protected by the ACL. Setup an Access Control List entry. In this example, the subnet 192.168.1.0 is another customer environment specific entry. Some tools such as the HP Standard Port Monitor use SNMPv1/v2c for status. Uncheck "Allow Web Server (HTTP) access" to force HTTP checking to be done in the ACL. 16
Based upon the customer's environment, read only SNMPv1/v2c access may need to be granted. This is protected by the ACL. Setup an Access Control List entry. In this example, the subnet 192.168.1.0 is another customer environment specific entry. Some tools such as the HP Standard Port Monitor use SNMPv1/v2c for status. Uncheck "Allow Web Server (HTTP) access" to force HTTP checking to be done in the ACL. 16
HP Jetdirect Security Guidelines
Page 18
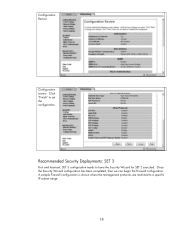
Recommended Security Deployments: SET 3 First and foremost, SET 3 configuration needs to a specific IP subnet range: 18 Configuration Review Configuration review. A sample Firewall configuration is shown where the management protocols are restricted to have the Security Wizard for SET 2 executed. Once the Security Wizard configuration has been completed, then we can begin the Firewall configuration. Click "Finish" to set the configuration.
Recommended Security Deployments: SET 3 First and foremost, SET 3 configuration needs to a specific IP subnet range: 18 Configuration Review Configuration review. A sample Firewall configuration is shown where the management protocols are restricted to have the Security Wizard for SET 2 executed. Once the Security Wizard configuration has been completed, then we can begin the Firewall configuration. Click "Finish" to set the configuration.
HP Jetdirect Security Guidelines
Page 19
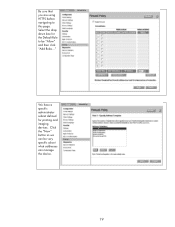
Select the drop down box for printing and imaging devices. Click the "New" button so we can be "Allow" and then click "Add Rules..." We have a specific administrator subnet defined for the Default Rule to this page. Be sure that you are using HTTPS before navigating to be very specific about what addresses can manage the device. 19
Select the drop down box for printing and imaging devices. Click the "New" button so we can be "Allow" and then click "Add Rules..." We have a specific administrator subnet defined for the Default Rule to this page. Be sure that you are using HTTPS before navigating to be very specific about what addresses can manage the device. 19
HP Jetdirect Administrator's Guide
Page 37
... through a cable (wired) will be minimal, a default IP configuration using link-local addressing is likely. Configuration tools that require a specific default IP address on the network. ENWW TCP/IP Configuration 37 HP Jetdirect Wireless Print Server. Up to send, or not send, periodic DHCP requests. DHCP requests are used . In this parameter is enabled, allowing...
... through a cable (wired) will be minimal, a default IP configuration using link-local addressing is likely. Configuration tools that require a specific default IP address on the network. ENWW TCP/IP Configuration 37 HP Jetdirect Wireless Print Server. Up to send, or not send, periodic DHCP requests. DHCP requests are used . In this parameter is enabled, allowing...
HP Jetdirect Administrator's Guide
Page 43
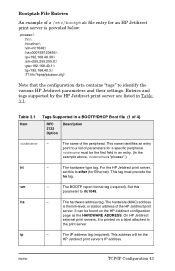
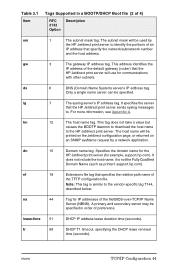
... an HP Jetdirect print server is the link-level, or station address of a /etc/bootptab file entry for a specific peripheral. Entries and tags supported by the HP Jetdirect print server are listed in an entry. (In the example above, nodename is printed on the HP Jetdirect configuration page as the HARDWARE ADDRESS. This name identifies an entry point to the print server. On HP Jetdirect external print servers...
... an HP Jetdirect print server is the link-level, or station address of a /etc/bootptab file entry for a specific peripheral. Entries and tags supported by the HP Jetdirect print server are listed in an entry. (In the example above, nodename is printed on the HP Jetdirect configuration page as the HARDWARE ADDRESS. This name identifies an entry point to the print server. On HP Jetdirect external print servers...
HP Jetdirect Administrator's Guide
Page 44
... address tag. Specifies the domain name for the HP Jetdirect print server (for IP addresses of the NetBIOS-over-TCP/IP Name Server (NBNS). A primary and secondary server may be printed on the Jetdirect configuration page, or returned on an SNMP sysName request by the HP Jetdirect print server to the vendor-specific tag T144, described below. gw 3 The gateway IP address tag...
... address tag. Specifies the domain name for the HP Jetdirect print server (for IP addresses of the NetBIOS-over-TCP/IP Name Server (NBNS). A primary and secondary server may be printed on the Jetdirect configuration page, or returned on an SNMP sysName request by the HP Jetdirect print server to the vendor-specific tag T144, described below. gw 3 The gateway IP address tag...
HP Jetdirect Administrator's Guide
Page 46
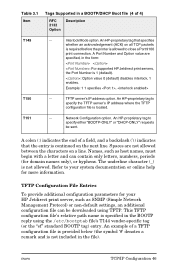
...print connection. Example: 1 1 specifies , T150 -- The underline character (_) is located. A Port Number and Option value are not allowed between the characters on all TCP packets is required before the printer is allowed to specify either "BOOTP-ONLY" or "DHCP-ONLY" requests be downloaded using the /etc/bootptab file's T144 vendor-specific... Network Configuration option. T151 -- An HP-proprietary tag that the entry is not included in the file). Spaces are specified, in the form: : For supported HP Jetdirect print servers, the Port Number is specified in ...
...print connection. Example: 1 1 specifies , T150 -- The underline character (_) is located. A Port Number and Option value are not allowed between the characters on all TCP packets is required before the printer is allowed to specify either "BOOTP-ONLY" or "DHCP-ONLY" requests be downloaded using the /etc/bootptab file's T144 vendor-specific... Network Configuration option. T151 -- An HP-proprietary tag that the entry is not included in the file). Spaces are specified, in the form: : For supported HP Jetdirect print servers, the Port Number is specified in ...
HP Jetdirect Administrator's Guide
Page 52
... packets. banner: A port-specific parameter that specifies printing an LPD banner page. 0 disables banner pages. 1 (default) enables banner pages. For example, "interlock 1 1" specifies Port 1, interlock enabled. write-mode: Controls the setting of 12) ipp-printing: (ipp-config:, ipp:) Enables or disables the ability to 9000, which are specified. For current HP Jetdirect print servers, the Port Number...
... packets. banner: A port-specific parameter that specifies printing an LPD banner page. 0 disables banner pages. 1 (default) enables banner pages. For example, "interlock 1 1" specifies Port 1, interlock enabled. write-mode: Controls the setting of 12) ipp-printing: (ipp-config:, ipp:) Enables or disables the ability to 9000, which are specified. For current HP Jetdirect print servers, the Port Number...