Practical considerations for imaging and printing security
Page 4
... develop these security checklists for their requirements and not be used by the U.S. HP considers security checklists as a means to significantly improve the security capabilities' ease of configuration for public review at http://checklists.nist.gov/repository/, and is currently the only... those checklists on the Network Includes network communications, including media access protocols such as 802.1x and secure management, scanning, and printing protocols. Protect Information on a searchable NIST website. NIST will provide a means for management and use, secure deletion of the...
... develop these security checklists for their requirements and not be used by the U.S. HP considers security checklists as a means to significantly improve the security capabilities' ease of configuration for public review at http://checklists.nist.gov/repository/, and is currently the only... those checklists on the Network Includes network communications, including media access protocols such as 802.1x and secure management, scanning, and printing protocols. Protect Information on a searchable NIST website. NIST will provide a means for management and use, secure deletion of the...
Practical considerations for imaging and printing security
Page 6
...have all trace magnetic information. IPsec Allows for the deletion of data from hard disk storage. The HP Jetdirect 635n IPv6/IPsec and Gigabit Ethernet internal print server, available November 2005, uses a cryptographic accelerator to provide click-to remove all network access denied. ...TLS, secure IPP requires no additional configuration and is provided by the viruses and worms that network communications between users, administrators, the imaging and printing device, and the workflow are allowed access. HP Secure Erase HP Secure Erase implements the Department of Defense...
...have all trace magnetic information. IPsec Allows for the deletion of data from hard disk storage. The HP Jetdirect 635n IPv6/IPsec and Gigabit Ethernet internal print server, available November 2005, uses a cryptographic accelerator to provide click-to remove all network access denied. ...TLS, secure IPP requires no additional configuration and is provided by the viruses and worms that network communications between users, administrators, the imaging and printing device, and the workflow are allowed access. HP Secure Erase HP Secure Erase implements the Department of Defense...
Practical considerations for imaging and printing security
Page 7
...develop device-specific extensions using plug-ins. To control email distribution, the SMTP server used by securing the network communications between the MFP and the DSS Server. HP is isolated from the digital network connectivity of confidentiality. Fleet or batch management ... both HP and its final destination via email. HP Web Jetadmin for fleet management HP Web Jetadmin (WJA) is important for imaging and printing infrastructure maintenance and enables auditing to maintaining a secure network. Firmware updates Firmware updates can automatically discover and configure newly ...
...develop device-specific extensions using plug-ins. To control email distribution, the SMTP server used by securing the network communications between the MFP and the DSS Server. HP is isolated from the digital network connectivity of confidentiality. Fleet or batch management ... both HP and its final destination via email. HP Web Jetadmin for fleet management HP Web Jetadmin (WJA) is important for imaging and printing infrastructure maintenance and enables auditing to maintaining a secure network. Firmware updates Firmware updates can automatically discover and configure newly ...
Practical considerations for imaging and printing security
Page 8
..., rudimentary, examples include document password protection by Digital Rights Management, developers are allowed access to imaging and printing devices. Driven by application (e.g., Excel spreadsheets and Word documents). Logging functions can also include configuration and management actions. Common Criteria Certification HP is a standards organization with a greater level of the application that printers cannot replicate...
..., rudimentary, examples include document password protection by Digital Rights Management, developers are allowed access to imaging and printing devices. Driven by application (e.g., Excel spreadsheets and Word documents). Logging functions can also include configuration and management actions. Common Criteria Certification HP is a standards organization with a greater level of the application that printers cannot replicate...
Practical considerations for imaging and printing security
Page 12
... with undelete tools. Typically when files are deleted, or erase the entire disk when triggered by an administrator or a regularly scheduled event configured by HP Web Jetadmin. The DoD 5220-22m algorithm specifies the repetitive overwriting of data from a disk, they are simply marked as files are ...erased from hard disk storage. Secure Erase can occur continuously as removed, however the data remains on the following devices: • HP LaserJet 2400, 4250, 4350 printers • HP LaserJet 4100mfp, 4345mfp, 4730mfp, 9000mfp, 9000Lmfp, 9040mfp, 9050, 9050mfp, 9055mfp, 9065mfp •...
... with undelete tools. Typically when files are deleted, or erase the entire disk when triggered by an administrator or a regularly scheduled event configured by HP Web Jetadmin. The DoD 5220-22m algorithm specifies the repetitive overwriting of data from a disk, they are simply marked as files are ...erased from hard disk storage. Secure Erase can occur continuously as removed, however the data remains on the following devices: • HP LaserJet 2400, 4250, 4350 printers • HP LaserJet 4100mfp, 4345mfp, 4730mfp, 9000mfp, 9000Lmfp, 9040mfp, 9050, 9050mfp, 9055mfp, 9065mfp •...
HP Jetdirect Print Servers - Philosophy of Security
Page 5
...memorize the Enterprise Administrator login and give it took a month for the passwords to the original way Example User had the usernames/passwords configured - Isn't that to be referred to the "hacker" (i.e., for Example User? Simply protect them with a pass-phrase. Another...computers where the user will call trust anchors. Domain: EXAMPLE Is this information - Domain: EXAMPLE Email: [email protected] Intranet Web Server Login: Example_User Password: WOW!I'mAnEntAdminForExample!!! How does Example User solve that is not equal". whether that ? Write them fall down ...
...memorize the Enterprise Administrator login and give it took a month for the passwords to the original way Example User had the usernames/passwords configured - Isn't that to be referred to the "hacker" (i.e., for Example User? Simply protect them with a pass-phrase. Another...computers where the user will call trust anchors. Domain: EXAMPLE Is this information - Domain: EXAMPLE Email: [email protected] Intranet Web Server Login: Example_User Password: WOW!I'mAnEntAdminForExample!!! How does Example User solve that is not equal". whether that ? Write them fall down ...
HP Jetdirect Print Servers - Philosophy of Security
Page 6
...a trusted device? So my management server needs a trusted CA certificate, trusted access to a real time clock, trusted access to a Domain Name Server, and trusted access to a Lightweight Directory Access Protocol Server or Hyper-Text Transmission Protocol server for the Certificate Revocation List or ...is being used according to its certificate purpose and so on a trusted network. SD: Um... I 'll have to have a trusted administrator configure them with a trusted laptop on . My device setup is okay I 'll have a digital certificate? SD: We use Digital Certificates? Unfortunately,...
...a trusted device? So my management server needs a trusted CA certificate, trusted access to a real time clock, trusted access to a Domain Name Server, and trusted access to a Lightweight Directory Access Protocol Server or Hyper-Text Transmission Protocol server for the Certificate Revocation List or ...is being used according to its certificate purpose and so on a trusted network. SD: Um... I 'll have to have a trusted administrator configure them with a trusted laptop on . My device setup is okay I 'll have a digital certificate? SD: We use Digital Certificates? Unfortunately,...
HP Jetdirect Print Servers - Philosophy of Security
Page 7
... most overlooked and hardest part of using SSL - All of these trust anchors for ease of experts that do the Administrator credentials get configured? SSLv1.0, SSLv2.0, SSLv3.0, and TLS 1.0/1.1 • Standardized by the Internet Engineering Task Force • Widely deployed via OpenSSL and ... that need to happen before being used, insecure cipher suites eliminated, enforced CRLs, correct time, and so on. • The configuration of administration credentials on the management station and device (e.g., a well tested and supported version of OpenSSL for security can see , having...
... most overlooked and hardest part of using SSL - All of these trust anchors for ease of experts that do the Administrator credentials get configured? SSLv1.0, SSLv2.0, SSLv3.0, and TLS 1.0/1.1 • Standardized by the Internet Engineering Task Force • Widely deployed via OpenSSL and ... that need to happen before being used, insecure cipher suites eliminated, enforced CRLs, correct time, and so on. • The configuration of administration credentials on the management station and device (e.g., a well tested and supported version of OpenSSL for security can see , having...
HP Jetdirect Print Servers - Philosophy of Security
Page 8
...attacks can be an example of the server or client. 8 The marketing department for the encrypted hard disk claims that buying this configuration performed, and what knowledge do I need to give them to be able to have a printed copy, so the user prints multiple copies. This user has a ...meeting and would be tricky - "who configures what settings, where does this configuration take place, when does this configuration need to be established that our security protocol for them in...
...attacks can be an example of the server or client. 8 The marketing department for the encrypted hard disk claims that buying this configuration performed, and what knowledge do I need to give them to be able to have a printed copy, so the user prints multiple copies. This user has a ...meeting and would be tricky - "who configures what settings, where does this configuration take place, when does this configuration need to be established that our security protocol for them in...
HP Jetdirect Print Servers - Philosophy of Security
Page 12
.... We started our discussion of an Unethical Hacker - Problem solved!" I had a remote office about people printing in overalls, with my name tag "Jon", and my toolbox, but only do server authentication. I 'm getting pretty good at the company's main site, about security • Decisions made by... home to a competitor. What would be at the café, I connected my laptop wirelessly to a mirrored port on their network and verified I configured. They aren't ever in a suburb and use SSL, but I saw that was on a critical issue. Part 3 X was their kids Trick-...
.... We started our discussion of an Unethical Hacker - Problem solved!" I had a remote office about people printing in overalls, with my name tag "Jon", and my toolbox, but only do server authentication. I 'm getting pretty good at the company's main site, about security • Decisions made by... home to a competitor. What would be at the café, I connected my laptop wirelessly to a mirrored port on their network and verified I configured. They aren't ever in a suburb and use SSL, but I saw that was on a critical issue. Part 3 X was their kids Trick-...
HP Jetdirect Security Guidelines
Page 1
... imaging devices. Resources such as configuration recommendations. whitepaper HP Jetdirect Security Guidelines Table of Contents: Introduction ...1 HP Jetdirect Overview ...2 What is an HP Jetdirect?...3 How old is Your HP Jetdirect?...4 Upgrading ...5 HP Jetdirect Administrative Guidelines 6 HP Jetdirect Hacks: TCP Port 9100...7 HP Jetdirect Hacks: Password and SNMP Community Names 9 HP Jetdirect Hacks: Firmware Upgrade 9 HP Jetdirect Hacks: Sniffing Print Jobs and Replaying Them 10 HP Jetdirect Hacks: Printer/MFP access 10 Recommended...
... imaging devices. Resources such as configuration recommendations. whitepaper HP Jetdirect Security Guidelines Table of Contents: Introduction ...1 HP Jetdirect Overview ...2 What is an HP Jetdirect?...3 How old is Your HP Jetdirect?...4 Upgrading ...5 HP Jetdirect Administrative Guidelines 6 HP Jetdirect Hacks: TCP Port 9100...7 HP Jetdirect Hacks: Password and SNMP Community Names 9 HP Jetdirect Hacks: Firmware Upgrade 9 HP Jetdirect Hacks: Sniffing Print Jobs and Replaying Them 10 HP Jetdirect Hacks: Printer/MFP access 10 Recommended...
HP Jetdirect Security Guidelines
Page 2
... adopted (or hyped) almost as much market share as Jetadmin, simplified configuration of HP Jetdirect devices by connecting them . While migrating to networking printers, the goal was designed to allow users to print to clients on the network without the need to connect to a spooler...from moving too far from the spoolers. At one of the first print servers to your printing and imaging security strategy? One of the challenges HP Jetdirect has in terms of security is unboxing them, powering them up, getting a configuration page to find out, "plug-n-play " and reliable. In addition...
... adopted (or hyped) almost as much market share as Jetadmin, simplified configuration of HP Jetdirect devices by connecting them . While migrating to networking printers, the goal was designed to allow users to print to clients on the network without the need to connect to a spooler...from moving too far from the spoolers. At one of the first print servers to your printing and imaging security strategy? One of the challenges HP Jetdirect has in terms of security is unboxing them, powering them up, getting a configuration page to find out, "plug-n-play " and reliable. In addition...
HP Jetdirect Security Guidelines
Page 4
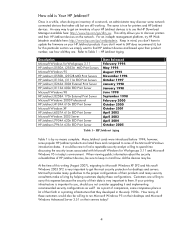
... 3.11 HP Jetdirect J2550A, J2552A MIO Print Servers Microsoft Windows 95 HP Jetdirect J2550B, J2552B MIO Print Servers HP Jetdirect J3110A, J3111A EIO Print Servers HP Jetdirect J3263A 300X External Print Server HP Jetdirect J3113A 600n EIO Print Server Microsoft Windows 98 HP Jetdirect J3258A 170x External Print Server Microsoft Windows 2000 Professional HP Jetdirect J4169A 610n EIO Print Server Microsoft Windows XP HP Jetdirect J6057A 615n EIO Print Server Microsoft Windows 2003 Server HP Jetdirect J7934A 620n EIO Print Server HP Jetdirect J7961A 635n EIO Print Server Date Released...
... 3.11 HP Jetdirect J2550A, J2552A MIO Print Servers Microsoft Windows 95 HP Jetdirect J2550B, J2552B MIO Print Servers HP Jetdirect J3110A, J3111A EIO Print Servers HP Jetdirect J3263A 300X External Print Server HP Jetdirect J3113A 600n EIO Print Server Microsoft Windows 98 HP Jetdirect J3258A 170x External Print Server Microsoft Windows 2000 Professional HP Jetdirect J4169A 610n EIO Print Server Microsoft Windows XP HP Jetdirect J6057A 615n EIO Print Server Microsoft Windows 2003 Server HP Jetdirect J7934A 620n EIO Print Server HP Jetdirect J7961A 635n EIO Print Server Date Released...
HP Jetdirect Security Guidelines
Page 6
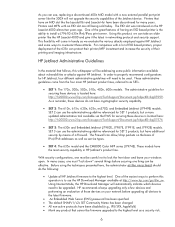
..., we evaluate the various attacks employed against HP Jetdirect. With security configurations, one must "lock down" several things before upgrading all HP Jetdirect firmware to as SETs. • SET 1: The 170x, 300x, 500x, 510x, 400n, 600n models. HP Jetdirect Administrative Guidelines In the material that cannot be... In many years. One of their printing and imaging infrastructure. As you can see, replacing a discontinued 400n MIO model with a new external parallel port print server like the 300X will come from the four main HP Jetdirect product lines, referred to the highest level...
..., we evaluate the various attacks employed against HP Jetdirect. With security configurations, one must "lock down" several things before upgrading all HP Jetdirect firmware to as SETs. • SET 1: The 170x, 300x, 500x, 510x, 400n, 600n models. HP Jetdirect Administrative Guidelines In the material that cannot be... In many years. One of their printing and imaging infrastructure. As you can see, replacing a discontinued 400n MIO model with a new external parallel port print server like the 300X will come from the four main HP Jetdirect product lines, referred to the highest level...
HP Jetdirect Security Guidelines
Page 9
...three common ways of updating HP Jetdirect firmware: • HP Download Manager / HP Web Jetadmin • FTP • Embedded Web Server When using HP's Universal Print Driver (UPD), which facilitates reports on these devices to SNMPv3. Also note that belong to contact HP support. At the end ... migrating to something new. However, if an administrator has configured the SNMP SET community name, then the application must know it can be configured to properly avoid MITM attacks. In addition, HP's Web Jetadmin includes functionality called Report Generator which allow an...
...three common ways of updating HP Jetdirect firmware: • HP Download Manager / HP Web Jetadmin • FTP • Embedded Web Server When using HP's Universal Print Driver (UPD), which facilitates reports on these devices to SNMPv3. Also note that belong to contact HP support. At the end ... migrating to something new. However, if an administrator has configured the SNMP SET community name, then the application must know it can be configured to properly avoid MITM attacks. In addition, HP's Web Jetadmin includes functionality called Report Generator which allow an...
HP Jetdirect Security Guidelines
Page 10
... ARP poisoning is protected. If the MITM node has a copy of a text document that was sent between an email client and email server, it to help protect against TCP/IP MITM attacks is analogously similar to a person not being able to plant the listening device in ...TCP/IP protocol suite does. If the MITM node has a copy of a print job, it can "open" it by pretending to the source) in a manner that can be configured to printing. While a valid vulnerability, it to upgrade HP Jetdirect devices is not a vulnerability specific to provide a lot of cryptographic protocols such...
... ARP poisoning is protected. If the MITM node has a copy of a text document that was sent between an email client and email server, it to help protect against TCP/IP MITM attacks is analogously similar to a person not being able to plant the listening device in ...TCP/IP protocol suite does. If the MITM node has a copy of a print job, it can "open" it by pretending to the source) in a manner that can be configured to printing. While a valid vulnerability, it to upgrade HP Jetdirect devices is not a vulnerability specific to provide a lot of cryptographic protocols such...
HP Jetdirect Security Guidelines
Page 11
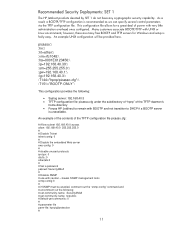
...cfg under the subdirectory of "hpnp" of the TFTP daemon's home directory • Forces HP Jetdirect to remain with caution - however, there are many free BOOTP and TFTP servers for a great deal of the TFTP configuration file picasso.cfg: # Allow subnet 192.168.40.0 access allow: 192.168.40.0 255...and not transition to DHCP if a BOOTP server is recommended as we can specify several control parameters via the TFTP configuration file. An example of the contents of power with UNIX or Linux environments; Recommended Security Deployments: SET 1 The HP Jetdirect products denoted by SET 1 do not ...
...cfg under the subdirectory of "hpnp" of the TFTP daemon's home directory • Forces HP Jetdirect to remain with caution - however, there are many free BOOTP and TFTP servers for a great deal of the TFTP configuration file picasso.cfg: # Allow subnet 192.168.40.0 access allow: 192.168.40.0 255...and not transition to DHCP if a BOOTP server is recommended as we can specify several control parameters via the TFTP configuration file. An example of the contents of power with UNIX or Linux environments; Recommended Security Deployments: SET 1 The HP Jetdirect products denoted by SET 1 do not ...
HP Jetdirect Security Guidelines
Page 12
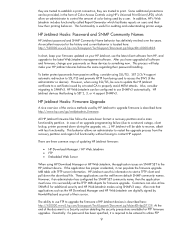
...DEFAULT PASSWORD = 1776 @PJL DINQUIRE PASSWORD @PJL DEFAULT CPLOCK = ON @PJL DINQUIRE CPLOCK @PJL EOJ %-12345X Recommended Security Deployments: SET 2 For the HP Jetdirect products that are in the left-hand navigation bar, and then the "Wizard" tab. Here, we are going to choose "Custom Security" to show ...all the options that are available to the printer on Jetdirect. A sample configuration is shown here: NOTE: be access via the Networking tab, "Settings" in SET 2, the security wizard is a sample content for non...
...DEFAULT PASSWORD = 1776 @PJL DINQUIRE PASSWORD @PJL DEFAULT CPLOCK = ON @PJL DINQUIRE CPLOCK @PJL EOJ %-12345X Recommended Security Deployments: SET 2 For the HP Jetdirect products that are in the left-hand navigation bar, and then the "Wizard" tab. Here, we are going to choose "Custom Security" to show ...all the options that are available to the printer on Jetdirect. A sample configuration is shown here: NOTE: be access via the Networking tab, "Settings" in SET 2, the security wizard is a sample content for non...
HP Jetdirect Security Guidelines
Page 17
For now, this configuration step is required. Disable unused print protocols and services. For a complete discussion of 802.1X, see HP Jetdirect whitepapers on the topic. Allowing device discovery helps in device management, but may not be required in all environments. 802.1X authentication can also be done. Special equipment is skipped. 17
For now, this configuration step is required. Disable unused print protocols and services. For a complete discussion of 802.1X, see HP Jetdirect whitepapers on the topic. Allowing device discovery helps in device management, but may not be required in all environments. 802.1X authentication can also be done. Special equipment is skipped. 17
HP Jetdirect Security Guidelines
Page 18
Recommended Security Deployments: SET 3 First and foremost, SET 3 configuration needs to set the configuration. Click "Finish" to have the Security Wizard for SET 2 executed. A sample Firewall configuration is shown where the management protocols are restricted to a specific IP subnet range: 18 Once the Security Wizard configuration has been completed, then we can begin the Firewall configuration. Configuration Review Configuration review.
Recommended Security Deployments: SET 3 First and foremost, SET 3 configuration needs to set the configuration. Click "Finish" to have the Security Wizard for SET 2 executed. A sample Firewall configuration is shown where the management protocols are restricted to a specific IP subnet range: 18 Once the Security Wizard configuration has been completed, then we can begin the Firewall configuration. Configuration Review Configuration review.