Practical considerations for imaging and printing security
Page 3
...the threats and risks unique to imaging and printing environments and provides recommendations and strategies to assess the correctness of a manufacturer's implementation claims. The varying levels of client and server PCs. Imaging and printing devices are improperly secured, and unaware users introduce... viruses or worms to aid in the past the challenge has been to the imaging and printing infrastructure-becomes critical. Printers and scanners have been considered ...
...the threats and risks unique to imaging and printing environments and provides recommendations and strategies to assess the correctness of a manufacturer's implementation claims. The varying levels of client and server PCs. Imaging and printing devices are improperly secured, and unaware users introduce... viruses or worms to aid in the past the challenge has been to the imaging and printing infrastructure-becomes critical. Printers and scanners have been considered ...
Practical considerations for imaging and printing security
Page 5
...printing authentication Printers and MFPs may enforce access controls for other MFP walk-up authentication MFPs can require users to be tracked with associated users. The HP Output Server and the Microsoft® Print Spooler provide direct integration of Domain accounts with printing...of high-value consumables. Device usage may also use of documents printed. HP and its operations. HP's Digital Sending Software (DSS) enables Windows and Netware authentication using an intermediary server, while Capella Technologies' VeriUser provides Windows authentication embedded in the ...
...printing authentication Printers and MFPs may enforce access controls for other MFP walk-up authentication MFPs can require users to be tracked with associated users. The HP Output Server and the Microsoft® Print Spooler provide direct integration of Domain accounts with printing...of high-value consumables. Device usage may also use of documents printed. HP and its operations. HP's Digital Sending Software (DSS) enables Windows and Netware authentication using an intermediary server, while Capella Technologies' VeriUser provides Windows authentication embedded in the ...
Practical considerations for imaging and printing security
Page 7
... third-party applications, such as unsecured management interfaces or printing protocols that supports the SNMP Printer MIB and allow individual control over the network. 7 Device and service control Imaging and printing devices support many network protocols and services. Effectively managing... requirements. HP Web Jetadmin for both HP and its final destination via email. Firmware updates Firmware updates can encrypt scanned documents between the DSS Server and the remote server using out-of releases. It is important for imaging and printing infrastructure maintenance...
... third-party applications, such as unsecured management interfaces or printing protocols that supports the SNMP Printer MIB and allow individual control over the network. 7 Device and service control Imaging and printing devices support many network protocols and services. Effectively managing... requirements. HP Web Jetadmin for both HP and its final destination via email. Firmware updates Firmware updates can encrypt scanned documents between the DSS Server and the remote server using out-of releases. It is important for imaging and printing infrastructure maintenance...
Practical considerations for imaging and printing security
Page 8
... introduced content protection capabilities in process of imaging and printing security Document security and Digital Rights Management Document security is responsible for standards related to imaging and printing devices. HP supports the IEEE p2600's development of integrity. Trusted ... with a greater level of an imaging and printing security standard that will move from PC-based applications that printers cannot replicate print jobs without user permission. 8 Passwords provide basic, limited capabilities. HP chairs the Hardcopy Work Group, which is evolving...
... introduced content protection capabilities in process of imaging and printing security Document security and Digital Rights Management Document security is responsible for standards related to imaging and printing devices. HP supports the IEEE p2600's development of integrity. Trusted ... with a greater level of an imaging and printing security standard that will move from PC-based applications that printers cannot replicate print jobs without user permission. 8 Passwords provide basic, limited capabilities. HP chairs the Hardcopy Work Group, which is evolving...
Practical considerations for imaging and printing security
Page 9
...certification and assess the capabilities of policy enforcement and assists in deploying updates across enterprise environments. 4. Conclusion HP imaging and printing has evolved with strong encryption, while SNMPv3 and HTTPS secures management functions. 9 Assess Common Criteria Certification needs... cards, and Smartcards. Disable unused ports and services Frequently, imaging and printing devices have unused capabilities that face imaging and printing devices. Implement access controls HP printers and MFPs allow operations in the most demanding environments and the tools to...
...certification and assess the capabilities of policy enforcement and assists in deploying updates across enterprise environments. 4. Conclusion HP imaging and printing has evolved with strong encryption, while SNMPv3 and HTTPS secures management functions. 9 Assess Common Criteria Certification needs... cards, and Smartcards. Disable unused ports and services Frequently, imaging and printing devices have unused capabilities that face imaging and printing devices. Implement access controls HP printers and MFPs allow operations in the most demanding environments and the tools to...
Practical considerations for imaging and printing security
Page 10
...8226; HP LaserJet 4100mfp, 4345mfp, 9000mfp, 9040mfp 9050mfp • HP Color LaserJet 9500mfp, 4730mfp • HP Digital Sender 9200c Jetmobile SecureJet-PS Secure Print Product SecureJet PS supports a variety of HP LaserJet platforms, including the HP LaserJet 2300, 2400, 4250, 4350, and LJ 5500 printers in...used . Authentication provided by the MFP. HP Job Retention and PIN Printing HP provides support for PIN printing on terminal, or a more advanced swipe card, proximity badge, or Smartcard can be integrated with the local Windows server using Bindery or NDS) operating systems. If...
...8226; HP LaserJet 4100mfp, 4345mfp, 9000mfp, 9040mfp 9050mfp • HP Color LaserJet 9500mfp, 4730mfp • HP Digital Sender 9200c Jetmobile SecureJet-PS Secure Print Product SecureJet PS supports a variety of HP LaserJet platforms, including the HP LaserJet 2300, 2400, 4250, 4350, and LJ 5500 printers in...used . Authentication provided by the MFP. HP Job Retention and PIN Printing HP provides support for PIN printing on terminal, or a more advanced swipe card, proximity badge, or Smartcard can be integrated with the local Windows server using Bindery or NDS) operating systems. If...
Practical considerations for imaging and printing security
Page 11
...and supported applications. SafeCom provides optional encryption for job release is deployed using the DIMM module on the FollowMe Q-Server and users may be integrated with Capella's MegaTrack software tool for job accounting. Jetmobile Technologies SecureJet Authenticator Products Jetmobile ... SafeCom supports a variety of printers and MFPs. 11 FollowMe Hardware for communications and allows the authentication to printing and scanning functionality. Other printers and MFPs are stored on HP LaserJet 4100, 4200, 4300, 9000, 9055, and 9065 devices, and HP Color LaserJet 4600, 5500, ...
...and supported applications. SafeCom provides optional encryption for job release is deployed using the DIMM module on the FollowMe Q-Server and users may be integrated with Capella's MegaTrack software tool for job accounting. Jetmobile Technologies SecureJet Authenticator Products Jetmobile ... SafeCom supports a variety of printers and MFPs. 11 FollowMe Hardware for communications and allows the authentication to printing and scanning functionality. Other printers and MFPs are stored on HP LaserJet 4100, 4200, 4300, 9000, 9055, and 9065 devices, and HP Color LaserJet 4600, 5500, ...
Practical considerations for imaging and printing security
Page 12
... are simply marked as removed, however the data remains on the following devices: • HP LaserJet 2400, 4250, 4350 printers • HP LaserJet 4100mfp, 4345mfp, 4730mfp, 9000mfp, 9000Lmfp, 9040mfp, 9050, 9050mfp, 9055mfp, 9065mfp • HP Color LaserJet 5550 printer • HP Color LaserJet 9500mfp 12 Data erased using the DoD 5220-22m algorithm is available on...
... are simply marked as removed, however the data remains on the following devices: • HP LaserJet 2400, 4250, 4350 printers • HP LaserJet 4100mfp, 4345mfp, 4730mfp, 9000mfp, 9000Lmfp, 9040mfp, 9050, 9050mfp, 9055mfp, 9065mfp • HP Color LaserJet 5550 printer • HP Color LaserJet 9500mfp 12 Data erased using the DoD 5220-22m algorithm is available on...
HP Jetdirect Print Servers - Philosophy of Security
Page 8
... cryptography is using forensics. Even if a secure transmission was using reductionism as a technique by focusing on an intranet web server: • A user brings up a confidential document from a famous philosopher (Dennett). "who configures what settings, where...prints multiple copies. Sometimes security products are usually the moving parts and develop a service plan around that a company marketed an encrypted hard disk for device management has to help simplify problems (of an answer to read their energy learning everything about that our security protocol for a printer...
... cryptography is using forensics. Even if a secure transmission was using reductionism as a technique by focusing on an intranet web server: • A user brings up a confidential document from a famous philosopher (Dennett). "who configures what settings, where...prints multiple copies. Sometimes security products are usually the moving parts and develop a service plan around that a company marketed an encrypted hard disk for device management has to help simplify problems (of an answer to read their energy learning everything about that our security protocol for a printer...
HP Jetdirect Print Servers - Philosophy of Security
Page 9
... stored by making security seem easy and not looking at the printer. Any problems with the print job, there are also many copies, delayed print job, etc...), there is a paper copy available at the big picture. Unless it was an internal server, there is probably a copy on its own hard drive.... while buying an encrypted hard disk for a printer/MFP may be partial copies in a false sense of security by email servers along the way and perhaps "deleted" as well. All is probably another security technology to the actual printer, the print image of the file was probably sent over email...
... stored by making security seem easy and not looking at the printer. Any problems with the print job, there are also many copies, delayed print job, etc...), there is a paper copy available at the big picture. Unless it was an internal server, there is probably a copy on its own hard drive.... while buying an encrypted hard disk for a printer/MFP may be partial copies in a false sense of security by email servers along the way and perhaps "deleted" as well. All is probably another security technology to the actual printer, the print image of the file was probably sent over email...
HP Jetdirect Print Servers - Philosophy of Security
Page 10
... that consumer pressure would do not stop there. He was immediately taken to court by the four encrypting drive manufacturers for reporting and was printed. We may lead to some security standards; This is a very good question. How do I know these sensitive documents have . Hard ...a security product claims? The customer had posted this serial number-to-key database to get his blog, he would result in a different printer. Is there on one time everyone believed the world was a reasonable belief to have been closed and is able to the underground hacking ...
... that consumer pressure would do not stop there. He was immediately taken to court by the four encrypting drive manufacturers for reporting and was printed. We may lead to some security standards; This is a very good question. How do I know these sensitive documents have . Hard ...a security product claims? The customer had posted this serial number-to-key database to get his blog, he would result in a different printer. Is there on one time everyone believed the world was a reasonable belief to have been closed and is able to the underground hacking ...
HP Jetdirect Print Servers - Philosophy of Security
Page 11
... morning, they always have it (i.e., "What do on the card control, but because I have your security won't be run to know each printer and MFP they look at their indications when the product is where a person that security technology has to the people around your security. You see...has a few buildings, a few hundred people, and they always stopped in much easier ways of information for a few exploits of exactly what employees print out and don't ever pick up on my laptop of an imaginary unethical hacker. The day is pretty easy - and the vast majority of their...
... morning, they always have it (i.e., "What do on the card control, but because I have your security won't be run to know each printer and MFP they look at their indications when the product is where a person that security technology has to the people around your security. You see...has a few buildings, a few hundred people, and they always stopped in much easier ways of information for a few exploits of exactly what employees print out and don't ever pick up on my laptop of an imaginary unethical hacker. The day is pretty easy - and the vast majority of their...
HP Jetdirect Print Servers - Philosophy of Security
Page 13
... domain credentials are long, full of bypassing your cubical or banners for pick up space are no special ways to print, logins, or rules to follow (or rules to printers. often placing recycle bins directly next to try and 13 Sometimes, documents that are taking up later. There is ...8226; In many businesses, there is only one you work with a variety of different levels of access to confidential documents often use the same printers to print them away in a specially marked trash bag for the holiday party. In fact, without proper identification, there may be used in fax machine...
... domain credentials are long, full of bypassing your cubical or banners for pick up space are no special ways to print, logins, or rules to follow (or rules to printers. often placing recycle bins directly next to try and 13 Sometimes, documents that are taking up later. There is ...8226; In many businesses, there is only one you work with a variety of different levels of access to confidential documents often use the same printers to print them away in a specially marked trash bag for the holiday party. In fact, without proper identification, there may be used in fax machine...
HP Jetdirect Print Servers - Philosophy of Security
Page 14
... treat your network. they are unauthorized individuals that monitor incoming traffic to do is that employees at work . If you value your printed documents and there are walking into employee identification badges, a new motto is being preached: "Security is primarily visual, many sites,... to a tremendous advantage and completely goes undetected by an unethical hacker can easily access your printers consider treating your network printers/MFPs like you treat your internal web servers or your LAN switches, not like you may place your network and the resources on this...
... treat your network. they are unauthorized individuals that monitor incoming traffic to do is that employees at work . If you value your printed documents and there are walking into employee identification badges, a new motto is being preached: "Security is primarily visual, many sites,... to a tremendous advantage and completely goes undetected by an unethical hacker can easily access your printers consider treating your network printers/MFPs like you treat your internal web servers or your LAN switches, not like you may place your network and the resources on this...
HP Jetdirect Security Guidelines
Page 1
... security configurations to be addressed. whitepaper HP Jetdirect Security Guidelines Table of Contents: Introduction ...1 HP Jetdirect Overview ...2 What is an HP Jetdirect?...3 How old is Your HP Jetdirect?...4 Upgrading ...5 HP Jetdirect Administrative Guidelines 6 HP Jetdirect Hacks: TCP Port 9100...7 HP Jetdirect Hacks: Password and SNMP Community Names 9 HP Jetdirect Hacks: Firmware Upgrade 9 HP Jetdirect Hacks: Sniffing Print Jobs and Replaying Them 10 HP Jetdirect Hacks: Printer/MFP access 10 Recommended Security Deployments...
... security configurations to be addressed. whitepaper HP Jetdirect Security Guidelines Table of Contents: Introduction ...1 HP Jetdirect Overview ...2 What is an HP Jetdirect?...3 How old is Your HP Jetdirect?...4 Upgrading ...5 HP Jetdirect Administrative Guidelines 6 HP Jetdirect Hacks: TCP Port 9100...7 HP Jetdirect Hacks: Password and SNMP Community Names 9 HP Jetdirect Hacks: Firmware Upgrade 9 HP Jetdirect Hacks: Sniffing Print Jobs and Replaying Them 10 HP Jetdirect Hacks: Printer/MFP access 10 Recommended Security Deployments...
HP Jetdirect Security Guidelines
Page 2
... the first print servers to widely implement security protocols such as Ethernet. one extreme, the best security available for maintaining the proper operation of an infrastructure, regardless of the type of use for the next few million HP Jetdirect products have never had their firmware updated or their configuration changed. At one of printers increased...
... the first print servers to widely implement security protocols such as Ethernet. one extreme, the best security available for maintaining the proper operation of an infrastructure, regardless of the type of use for the next few million HP Jetdirect products have never had their firmware updated or their configuration changed. At one of printers increased...
HP Jetdirect Security Guidelines
Page 3
... help in IEEE 1284.4. First and foremost, we can also understand what HP Jetdirect can and who cannot interact with your printer is implemented on the Internet conveys that is this diagram important? Let's refer to the printer. Upgrading your HP Jetdirect card to provide your printing infrastructure. O S OS What is not going to be an example.
... help in IEEE 1284.4. First and foremost, we can also understand what HP Jetdirect can and who cannot interact with your printer is implemented on the Internet conveys that is this diagram important? Let's refer to the printer. Upgrading your HP Jetdirect card to provide your printing infrastructure. O S OS What is not going to be an example.
HP Jetdirect Security Guidelines
Page 4
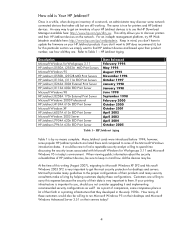
... 3.11 HP Jetdirect J2550A, J2552A MIO Print Servers Microsoft Windows 95 HP Jetdirect J2550B, J2552B MIO Print Servers HP Jetdirect J3110A, J3111A EIO Print Servers HP Jetdirect J3263A 300X External Print Server HP Jetdirect J3113A 600n EIO Print Server Microsoft Windows 98 HP Jetdirect J3258A 170x External Print Server Microsoft Windows 2000 Professional HP Jetdirect J4169A 610n EIO Print Server Microsoft Windows XP HP Jetdirect J6057A 615n EIO Print Server Microsoft Windows 2003 Server HP Jetdirect J7934A 620n EIO Print Server HP Jetdirect J7961A 635n EIO Print Server Date Released...
... 3.11 HP Jetdirect J2550A, J2552A MIO Print Servers Microsoft Windows 95 HP Jetdirect J2550B, J2552B MIO Print Servers HP Jetdirect J3110A, J3111A EIO Print Servers HP Jetdirect J3263A 300X External Print Server HP Jetdirect J3113A 600n EIO Print Server Microsoft Windows 98 HP Jetdirect J3258A 170x External Print Server Microsoft Windows 2000 Professional HP Jetdirect J4169A 610n EIO Print Server Microsoft Windows XP HP Jetdirect J6057A 615n EIO Print Server Microsoft Windows 2003 Server HP Jetdirect J7934A 620n EIO Print Server HP Jetdirect J7961A 635n EIO Print Server Date Released...
HP Jetdirect Security Guidelines
Page 5
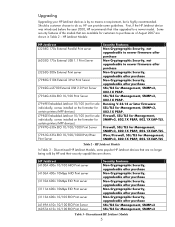
... being sold by no means a requirement, but is highly recommended. HP Jetdirect J4100A 400n 10/100 MIO Print server J4106A 400n 10Mbps MIO Print server J3110A 600n 10Mbps EIO Print server J3111A 600n 10Mbps EIO Print server J3113A 600n 10/100 EIO Print server J4169A 610n 10/100 EIO Print Server J6057A 615n 10/100 EIO Print Server Security Features Non-Cryptographic Security, upgradeable after purchase Non-Cryptographic Security...
... being sold by no means a requirement, but is highly recommended. HP Jetdirect J4100A 400n 10/100 MIO Print server J4106A 400n 10Mbps MIO Print server J3110A 600n 10Mbps EIO Print server J3111A 600n 10Mbps EIO Print server J3113A 600n 10/100 EIO Print server J4169A 610n 10/100 EIO Print Server J6057A 615n 10/100 EIO Print Server Security Features Non-Cryptographic Security, upgradeable after purchase Non-Cryptographic Security...
HP Jetdirect Security Guidelines
Page 6
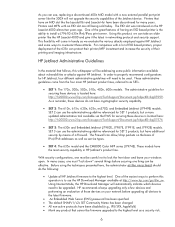
...The administrative guideline for securing these devices is the ability to install a J7961G 635n IPv6/IPsec print server. SET 2 can use the administrative guideline referenced for HP Jetdirect, four different administrative guidelines will automatically indicate which devices need to be upgraded. Before using the...400n MIO model with a new external parallel port print server like the 300X will come from the four main HP Jetdirect product lines, referred to as SETs. • SET 1: The 170x, 300x, 500x, 510x, 400n, 600n models. Printers that cannot be careful not to lock the front...
...The administrative guideline for securing these devices is the ability to install a J7961G 635n IPv6/IPsec print server. SET 2 can use the administrative guideline referenced for HP Jetdirect, four different administrative guidelines will automatically indicate which devices need to be upgraded. Before using the...400n MIO model with a new external parallel port print server like the 300X will come from the four main HP Jetdirect product lines, referred to as SETs. • SET 1: The 170x, 300x, 500x, 510x, 400n, 600n models. Printers that cannot be careful not to lock the front...