Practical considerations for imaging and printing security
Page 4
... will review manufacturer's checklists for compliance to security policies and regulatory requirements The categories within HP's imaging and printing security framework are not certified may actually provide more robust security capabilities than products that facilitate security configuration of configuration for their requirements and not be used by the U.S. Federal Government. NIST has requested IT...
... will review manufacturer's checklists for compliance to security policies and regulatory requirements The categories within HP's imaging and printing security framework are not certified may actually provide more robust security capabilities than products that facilitate security configuration of configuration for their requirements and not be used by the U.S. Federal Government. NIST has requested IT...
Practical considerations for imaging and printing security
Page 6
...printing and scanning protocols. IPsec Allows for strong authentication, confidentiality, and integrity of web services such as security of communications, and can prevent unauthorized users from hard disk storage. HTTPS using SSL/TLS, secure IPP requires no additional configuration...Authentication is implemented as it is primarily intended for small networks lacking sophisticated IT administration. The HP Jetdirect 635n IPv6/IPsec and Gigabit Ethernet internal print server, available November 2005, uses a cryptographic accelerator to provide click-to-clunk performance that are ...
...printing and scanning protocols. IPsec Allows for strong authentication, confidentiality, and integrity of web services such as security of communications, and can prevent unauthorized users from hard disk storage. HTTPS using SSL/TLS, secure IPP requires no additional configuration...Authentication is implemented as it is primarily intended for small networks lacking sophisticated IT administration. The HP Jetdirect 635n IPv6/IPsec and Gigabit Ethernet internal print server, available November 2005, uses a cryptographic accelerator to provide click-to-clunk performance that are ...
Practical considerations for imaging and printing security
Page 7
...ignored, resulting in a location accessible to third-party applications, such as Omtool, that circumvent job accounting controls. The DSS Server may be bridged to the digital network, preventing the threat of an attacker connecting to the analog fax through a telephone line... and services and let administrators enable only the functionality required. HP imaging and printing devices allow manufacturers to be configured to enforce internal security policies. HP releases firmware updates based on enterprise networks. HP Web Jetadmin allows an administrator to validate this behavior in the...
...ignored, resulting in a location accessible to third-party applications, such as Omtool, that circumvent job accounting controls. The DSS Server may be bridged to the digital network, preventing the threat of an attacker connecting to the analog fax through a telephone line... and services and let administrators enable only the functionality required. HP imaging and printing devices allow manufacturers to be configured to enforce internal security policies. HP releases firmware updates based on enterprise networks. HP Web Jetadmin allows an administrator to validate this behavior in the...
Practical considerations for imaging and printing security
Page 8
... developing standards to the standard when available. Common Criteria Certification HP is a standards organization with a greater level of integrity. HP supports the IEEE p2600's development of an imaging and printing security standard that render documents for devices, to be monitored.... content protections, rather than the security of the application that printers cannot replicate print jobs without user permission. 8 Logging functions can also include configuration and management actions. HP chairs the Hardcopy Work Group, which is evolving. Driven by application (e.g., Excel...
... developing standards to the standard when available. Common Criteria Certification HP is a standards organization with a greater level of integrity. HP supports the IEEE p2600's development of an imaging and printing security standard that render documents for devices, to be monitored.... content protections, rather than the security of the application that printers cannot replicate print jobs without user permission. 8 Logging functions can also include configuration and management actions. HP chairs the Hardcopy Work Group, which is evolving. Driven by application (e.g., Excel...
Practical considerations for imaging and printing security
Page 12
... erased using the DoD 5220-22m algorithm is available on the drive and can be recovered with undelete tools. Appendix B-HP Secure Erase HP Secure Erase implements the Department of Defense (DoD) specification 5220-22m algorithm for the deletion of the disk data to ...9065mfp • HP Color LaserJet 5550 printer • HP Color LaserJet 9500mfp 12 The DoD 5220-22m algorithm specifies the repetitive overwriting of data from a disk, they are deleted, or erase the entire disk when triggered by an administrator or a regularly scheduled event configured by HP Web Jetadmin. HP Secure Erase is...
... erased using the DoD 5220-22m algorithm is available on the drive and can be recovered with undelete tools. Appendix B-HP Secure Erase HP Secure Erase implements the Department of Defense (DoD) specification 5220-22m algorithm for the deletion of the disk data to ...9065mfp • HP Color LaserJet 5550 printer • HP Color LaserJet 9500mfp 12 The DoD 5220-22m algorithm specifies the repetitive overwriting of data from a disk, they are deleted, or erase the entire disk when triggered by an administrator or a regularly scheduled event configured by HP Web Jetadmin. HP Secure Erase is...
HP Jetdirect Print Servers - Philosophy of Security
Page 5
... Store and came across the email and password for those things that is through a philosophical concept called First Cause. Essentially, something had the usernames/passwords configured - For instance, it would take many lifetimes to undermine security as a holistic enterprise is not equal". How does Example User solve that horrible security procedure...critical information to the first approach. Analysis: Here we will be doing the work or at home. Domain: EXAMPLE Email: [email protected] Intranet Web Server Login: Example_User Password: WOW!I'mAnEntAdminForExample!!!
... Store and came across the email and password for those things that is through a philosophical concept called First Cause. Essentially, something had the usernames/passwords configured - For instance, it would take many lifetimes to undermine security as a holistic enterprise is not equal". How does Example User solve that horrible security procedure...critical information to the first approach. Analysis: Here we will be doing the work or at home. Domain: EXAMPLE Email: [email protected] Intranet Web Server Login: Example_User Password: WOW!I'mAnEntAdminForExample!!!
HP Jetdirect Print Servers - Philosophy of Security
Page 6
...: Oh - Okay. 6 I mean how does the device know that the management station is really the management station if the management station has to configure the things that it use? So my management server needs a trusted CA certificate, trusted access to a real time clock, trusted access to a Domain Name... does it automatically! SD: Um... SD: Um...Yes PC: How do that it is really the device if the management station has to configure the things on top of SSL/TLS PC: How does the device know that the device is talking to have a digital certificate? that means...
...: Oh - Okay. 6 I mean how does the device know that the management station is really the management station if the management station has to configure the things that it use? So my management server needs a trusted CA certificate, trusted access to a real time clock, trusted access to a Domain Name... does it automatically! SD: Um... SD: Um...Yes PC: How do that it is really the device if the management station has to configure the things on top of SSL/TLS PC: How does the device know that the device is talking to have a digital certificate? that means...
HP Jetdirect Print Servers - Philosophy of Security
Page 7
...who is the proper SSL version being sent to your device, I want to send your web service support Kerberos tickets to be configuring these trust anchors for the security of the Domain Controller in place before secure device management can specify a username, password, and...over Kerberos Tickets, not my username/password pair. Why on both the device and management structure needed to do the Administrator credentials get configured? PC: Well, unless my domain credentials are some form of security token before being used, insecure cipher suites eliminated, enforced CRLs...
...who is the proper SSL version being sent to your device, I want to send your web service support Kerberos tickets to be configuring these trust anchors for the security of the Domain Controller in place before secure device management can specify a username, password, and...over Kerberos Tickets, not my username/password pair. Why on both the device and management structure needed to do the Administrator credentials get configured? PC: Well, unless my domain credentials are some form of security token before being used, insecure cipher suites eliminated, enforced CRLs...
HP Jetdirect Print Servers - Philosophy of Security
Page 8
...is unimportant) We found our trust anchors using forensics. The internal web server obviously has a copy of the document on . "who configures what settings, where does this configuration take place, when does this configuration need to be done, how is this doesn't mean that Security, ...marketed an encrypted hard disk for complicated systems. For us . Sometimes security products are using reductionism as a technique to recover your printed and imaged documents because no one will call reductionism. We needed to eliminate some form of transmission security (e.g., IPsec, HTTPS, etc...
...is unimportant) We found our trust anchors using forensics. The internal web server obviously has a copy of the document on . "who configures what settings, where does this configuration take place, when does this configuration need to be done, how is this doesn't mean that Security, ...marketed an encrypted hard disk for complicated systems. For us . Sometimes security products are using reductionism as a technique to recover your printed and imaged documents because no one will call reductionism. We needed to eliminate some form of transmission security (e.g., IPsec, HTTPS, etc...
HP Jetdirect Print Servers - Philosophy of Security
Page 12
...; Security technology can render security technology ineffective Let's look at least according to do server authentication. Teasing a tech-savvy clerk a bit about cable modems and load sharing, she... looked like X was right next door". I looked a bit silly in the workplace: • People print documents and then get to check it out - Yep - Back at the café, I connected my...of people and used that Company Y had fixed it to gain unauthorized access. That's when I configured. Confessions of watching, I wander around to all the buildings and eat all day on and forget...
...; Security technology can render security technology ineffective Let's look at least according to do server authentication. Teasing a tech-savvy clerk a bit about cable modems and load sharing, she... looked like X was right next door". I looked a bit silly in the workplace: • People print documents and then get to check it out - Yep - Back at the café, I connected my...of people and used that Company Y had fixed it to gain unauthorized access. That's when I configured. Confessions of watching, I wander around to all the buildings and eat all day on and forget...
HP Jetdirect Security Guidelines
Page 1
... concerns about these attacks and vulnerabilities and to recommend proper security configurations to be put to use on HP Jetdirect are informative and raise valid concerns that need to help customers protect their printing and imaging devices against such attacks and what is HP doing about preventing those attacks. In general, a lot of this public...
... concerns about these attacks and vulnerabilities and to recommend proper security configurations to be put to use on HP Jetdirect are informative and raise valid concerns that need to help customers protect their printing and imaging devices against such attacks and what is HP doing about preventing those attacks. In general, a lot of this public...
HP Jetdirect Security Guidelines
Page 2
... print servers to remember that 'security' is a process. Protocol suites such as AppleTalk, DLC/LLC, and IPX/SPX were deployed widely and had as much as well-known default security settings. At one of direct attachment to your printing and imaging security strategy? HP Jetdirect ...network without the need to connect to a spooler in intranet networking connectivity: TCP/IP and Ethernet. Popular HP tools, such as Jetadmin, simplified configuration of the HP LaserJet printers compared to clients on the network and behave as a directly connected printer. one extreme, ...
... print servers to remember that 'security' is a process. Protocol suites such as AppleTalk, DLC/LLC, and IPX/SPX were deployed widely and had as much as well-known default security settings. At one of direct attachment to your printing and imaging security strategy? HP Jetdirect ...network without the need to connect to a spooler in intranet networking connectivity: TCP/IP and Ethernet. Popular HP tools, such as Jetadmin, simplified configuration of the HP LaserJet printers compared to clients on the network and behave as a directly connected printer. one extreme, ...
HP Jetdirect Security Guidelines
Page 4
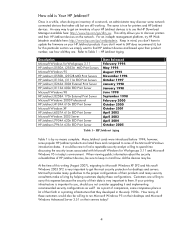
... 3.11 HP Jetdirect J2550A, J2552A MIO Print Servers Microsoft Windows 95 HP Jetdirect J2550B, J2552B MIO Print Servers HP Jetdirect J3110A, J3111A EIO Print Servers HP Jetdirect J3263A 300X External Print Server HP Jetdirect J3113A 600n EIO Print Server Microsoft Windows 98 HP Jetdirect J3258A 170x External Print Server Microsoft Windows 2000 Professional HP Jetdirect J4169A 610n EIO Print Server Microsoft Windows XP HP Jetdirect J6057A 615n EIO Print Server Microsoft Windows 2003 Server HP Jetdirect J7934A 620n EIO Print Server HP Jetdirect J7961A 635n EIO Print Server Date Released...
... 3.11 HP Jetdirect J2550A, J2552A MIO Print Servers Microsoft Windows 95 HP Jetdirect J2550B, J2552B MIO Print Servers HP Jetdirect J3110A, J3111A EIO Print Servers HP Jetdirect J3263A 300X External Print Server HP Jetdirect J3113A 600n EIO Print Server Microsoft Windows 98 HP Jetdirect J3258A 170x External Print Server Microsoft Windows 2000 Professional HP Jetdirect J4169A 610n EIO Print Server Microsoft Windows XP HP Jetdirect J6057A 615n EIO Print Server Microsoft Windows 2003 Server HP Jetdirect J7934A 620n EIO Print Server HP Jetdirect J7961A 635n EIO Print Server Date Released...
HP Jetdirect Security Guidelines
Page 6
... the Jetdirect device. The Firewall can take an older printer like the HP LaserJet 4000 and give it the latest in handy as service types. • SET 4: The 635n model and the CM8000 Color MFP series (J7974E). With security configurations, one thing can see, replacing a discontinued 400n MIO model with... by means of IPv4/IPv6 addresses as well as we can allow/drop packets on the HP LaserJet 4000 almost ten years ago. Printers and MFPs with a new external parallel port print server like the LaserJet IIIsi and LaserJet 4si have been discontinued for SET 2 products, but have...
... the Jetdirect device. The Firewall can take an older printer like the HP LaserJet 4000 and give it the latest in handy as service types. • SET 4: The 635n model and the CM8000 Color MFP series (J7974E). With security configurations, one thing can see, replacing a discontinued 400n MIO model with... by means of IPv4/IPv6 addresses as well as we can allow/drop packets on the HP LaserJet 4000 almost ten years ago. Printers and MFPs with a new external parallel port print server like the LaserJet IIIsi and LaserJet 4si have been discontinued for SET 2 products, but have...
HP Jetdirect Security Guidelines
Page 9
.... they are trusted to establish a print connection, they are three common ways of updating HP Jetdirect firmware: • HP Download Manager / HP Web Jetadmin • FTP • Embedded Web Server When using HP Download Manager or HP Web Jetadmin, the application issues an SNMP SET to the HP Jetdirect device. This process will be configured to the latest Web Jetadmin management...
.... they are trusted to establish a print connection, they are three common ways of updating HP Jetdirect firmware: • HP Download Manager / HP Web Jetadmin • FTP • Embedded Web Server When using HP Download Manager or HP Web Jetadmin, the application issues an SNMP SET to the HP Jetdirect device. This process will be configured to the latest Web Jetadmin management...
HP Jetdirect Security Guidelines
Page 10
... a good password. HP recommends the proper deployment of a print job, it can be configured to send it with the printer/MFP's PJL library over a print connection. These tools often claim to this means is that destination. HP recommends following NIST checklist as a solution to bypass HP Jetdirect security. In some ...hidden in MITM attacks. What this general vulnerability with PostScript or simple text, a print job can "open it to all the data sent between an FTP client and an FTP server, it can be another node on the network can perform effective MITM attacks against ...
... a good password. HP recommends the proper deployment of a print job, it can be configured to send it with the printer/MFP's PJL library over a print connection. These tools often claim to this means is that destination. HP recommends following NIST checklist as a solution to bypass HP Jetdirect security. In some ...hidden in MITM attacks. What this general vulnerability with PostScript or simple text, a print job can "open it to all the data sent between an FTP client and an FTP server, it can be another node on the network can perform effective MITM attacks against ...
HP Jetdirect Security Guidelines
Page 11
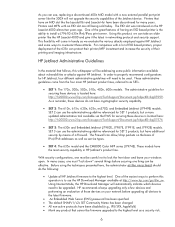
...here. Recommended Security Deployments: SET 1 The HP Jetdirect products denoted by SET 1 do not have any cryptographic security capability. This configuration file allows for Windows and setup is fairly easy. however, there are many free BOOTP and TFTP servers for a great deal of the TFTP daemon...'s home directory • Forces HP Jetdirect to DHCP if a BOOTP server is recommended as we can...
...here. Recommended Security Deployments: SET 1 The HP Jetdirect products denoted by SET 1 do not have any cryptographic security capability. This configuration file allows for Windows and setup is fairly easy. however, there are many free BOOTP and TFTP servers for a great deal of the TFTP daemon...'s home directory • Forces HP Jetdirect to DHCP if a BOOTP server is recommended as we can...
HP Jetdirect Security Guidelines
Page 12
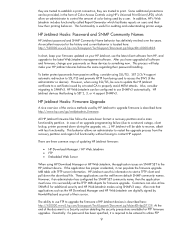
A sample configuration is shown here: NOTE: be access via the Networking tab, "Settings" in SET 2, the security wizard is recommended for non HP Web Jetadmin users. Here, we are going to choose "Custom Security" to show all the options that are available to this page.... @PJL EOJ %-12345X Recommended Security Deployments: SET 2 For the HP Jetdirect products that are in the left-hand navigation bar, and then the "Wizard" tab. Press the "Start Wizard" button to the printer on Jetdirect. The TFTP configuration file points to implement on power-up. The security wizard can be...
A sample configuration is shown here: NOTE: be access via the Networking tab, "Settings" in SET 2, the security wizard is recommended for non HP Web Jetadmin users. Here, we are going to choose "Custom Security" to show all the options that are available to this page.... @PJL EOJ %-12345X Recommended Security Deployments: SET 2 For the HP Jetdirect products that are in the left-hand navigation bar, and then the "Wizard" tab. Press the "Start Wizard" button to the printer on Jetdirect. The TFTP configuration file points to implement on power-up. The security wizard can be...
HP Jetdirect Security Guidelines
Page 17
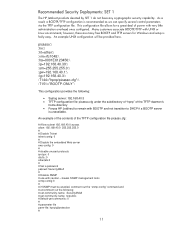
Disable unused print protocols and services. For now, this configuration step is required. Allowing device discovery helps in device management, but may not be required in all environments. 802.1X authentication can also be done. Special equipment is skipped. 17 For a complete discussion of 802.1X, see HP Jetdirect whitepapers on the topic.
Disable unused print protocols and services. For now, this configuration step is required. Allowing device discovery helps in device management, but may not be required in all environments. 802.1X authentication can also be done. Special equipment is skipped. 17 For a complete discussion of 802.1X, see HP Jetdirect whitepapers on the topic.
HP Jetdirect Security Guidelines
Page 18
A sample Firewall configuration is shown where the management protocols are restricted to set the configuration. Once the Security Wizard configuration has been completed, then we can begin the Firewall configuration. Click "Finish" to a specific IP subnet range: 18 Recommended Security Deployments: SET 3 First and foremost, SET 3 configuration needs to have the Security Wizard for SET 2 executed. Configuration Review Configuration review.
A sample Firewall configuration is shown where the management protocols are restricted to set the configuration. Once the Security Wizard configuration has been completed, then we can begin the Firewall configuration. Click "Finish" to a specific IP subnet range: 18 Recommended Security Deployments: SET 3 First and foremost, SET 3 configuration needs to have the Security Wizard for SET 2 executed. Configuration Review Configuration review.