Product Manual
Page 4
... Log Settings 59 2.3. Overview 60 2.3.2. RADIUS Accounting and High Availability 62 2.3.7. Backing Up Configurations 73 2.7.3. Address Groups 80 3.1.5. State-based Architecture 19 1.2.2. Basic Packet Flow 20 1.3. Overview... Settings 63 2.4. The pcapdump Command 70 2.7. NetDefendOS Architecture 19 1.2.1. The Console Boot Menu 47 2.1.8. Log Messages 55 2.2.3. Limitations with Configurations 49 2.2. Overview 82 3.2.2. RADIUS Accounting 60 2.3.1. Interim Accounting Messages 62 2.3.4. Address Book Folders 81 3.2. Restore to Factory Defaults 74...
... Log Settings 59 2.3. Overview 60 2.3.2. RADIUS Accounting and High Availability 62 2.3.7. Backing Up Configurations 73 2.7.3. Address Groups 80 3.1.5. State-based Architecture 19 1.2.2. Basic Packet Flow 20 1.3. Overview... Settings 63 2.4. The pcapdump Command 70 2.7. NetDefendOS Architecture 19 1.2.1. The Console Boot Menu 47 2.1.8. Log Messages 55 2.2.3. Limitations with Configurations 49 2.2. Overview 82 3.2.2. RADIUS Accounting 60 2.3.1. Interim Accounting Messages 62 2.3.4. Address Book Folders 81 3.2. Restore to Factory Defaults 74...
Product Manual
Page 5
... SAT Multiplex Rules 195 4.6.3. Service Groups 88 3.2.6. Creating ARP Objects 110 3.4.4. ARP Advanced Settings Summary 113 3.5. Configuration Object Groups 122 3.6. Certificates in NetDefendOS 129 3.7.3. Routing ...142 4.1. Overview 142 4.2. Routing Table Selection 161 4.3.5....Folders 121 3.5.6. Certificates 128 3.7.1. Time Servers 133 3.8.4. Overview 194 4.6.2. User Manual 3.2.3. Route Failover 151 4.2.4. IGMP Configuration 199 4.6.4. CA Certificate Requests 130 3.8. Overview 132 3.8.2. Setting Date and Time 132 3.8.3. Dynamic Routing 171 4.5.2. ...
... SAT Multiplex Rules 195 4.6.3. Service Groups 88 3.2.6. Creating ARP Objects 110 3.4.4. ARP Advanced Settings Summary 113 3.5. Configuration Object Groups 122 3.6. Certificates in NetDefendOS 129 3.7.3. Routing ...142 4.1. Overview 142 4.2. Routing Table Selection 161 4.3.5....Folders 121 3.5.6. Certificates 128 3.7.1. Time Servers 133 3.8.4. Overview 194 4.6.2. User Manual 3.2.3. Route Failover 151 4.2.4. IGMP Configuration 199 4.6.4. CA Certificate Requests 130 3.8. Overview 132 3.8.2. Setting Date and Time 132 3.8.3. Dynamic Routing 171 4.5.2. ...
Product Manual
Page 10
... A Basic Traffic Shaping Scenario 460 10.8. An ARP Publish Ethernet Frame 112 3.3. Using Local IP Address with NAT 339 7.4. Virtual Links Connecting Areas 177 4.11. DHCP Server Objects 227 6.1. PPTP ALG Usage 264 6.7. IDP Database Updating 316 7.1. The AH protocol 399... 10.3. Transparent Mode Scenario 2 215 4.22. LDAP for ISP Access 152 4.4. Packet Flow Schematic Part I 23 1.2. A Server Load Balancing Configuration 473 10 A Typical Routing Scenario 144 4.2. Differentiated Limits Using Chains 450 10.4. Address Translation 198 4.16. List of the DMZ 344 8.1. ...
... A Basic Traffic Shaping Scenario 460 10.8. An ARP Publish Ethernet Frame 112 3.3. Using Local IP Address with NAT 339 7.4. Virtual Links Connecting Areas 177 4.11. DHCP Server Objects 227 6.1. PPTP ALG Usage 264 6.7. IDP Database Updating 316 7.1. The AH protocol 399... 10.3. Transparent Mode Scenario 2 215 4.22. LDAP for ISP Access 152 4.4. Packet Flow Schematic Part I 23 1.2. A Server Load Balancing Configuration 473 10 A Typical Routing Scenario 144 4.2. Differentiated Limits Using Chains 450 10.4. Address Translation 198 4.16. List of the DMZ 344 8.1. ...
Product Manual
Page 12
...3.19. Setting the Time Zone 133 3.22. Displaying the main Routing Table 149 4.2. Creating the Route 162 4.5. Deleting a Configuration Object 52 2.8. Listing Modified Configuration Objects 53 2.10. Adding an Allow IP Rule 121 3.17. Displaying the Core Routes 150 4.3. Setting Up RLB 169 ... Import Routes from an OSPF AS into an OSPF AS 193 4.12. Undeleting a Configuration Object 53 2.9. Adding an IP Range 78 3.4. Forcing Time Synchronization 136 3.27. Enabling the D-Link NTP Server 136 3.28. Deleting an Address Object 79 3.5. Exporting the Default Route ...
...3.19. Setting the Time Zone 133 3.22. Displaying the main Routing Table 149 4.2. Creating the Route 162 4.5. Deleting a Configuration Object 52 2.8. Listing Modified Configuration Objects 53 2.10. Adding an Allow IP Rule 121 3.17. Displaying the Core Routes 150 4.3. Setting Up RLB 169 ... Import Routes from an OSPF AS into an OSPF AS 193 4.12. Undeleting a Configuration Object 53 2.9. Adding an IP Range 78 3.4. Forcing Time Synchronization 136 3.27. Enabling the D-Link NTP Server 136 3.28. Deleting an Address Object 79 3.5. Exporting the Default Route ...
Product Manual
Page 13
... and two NetDefend Firewalls 284 6.10. Two Phones Behind Different NetDefend Firewalls 280 6.7. H.323 with an ALG 248 6.3. Configuring remote offices for Web Access 371 8.3. Reclassifying a blocked site 300 6.18. Activating Anti-Virus Scanning 313 6.20. Creating an Authentication... User Group 371 8.2. Configuring a RADIUS Server 372 8.4. Setting up a Self-signed Certificate based VPN tunnel for roaming clients 409 9.5. Setting up a PSK based...
... and two NetDefend Firewalls 284 6.10. Two Phones Behind Different NetDefend Firewalls 280 6.7. H.323 with an ALG 248 6.3. Configuring remote offices for Web Access 371 8.3. Reclassifying a blocked site 300 6.18. Activating Anti-Virus Scanning 313 6.20. Creating an Authentication... User Group 371 8.2. Configuring a RADIUS Server 372 8.4. Setting up a Self-signed Certificate based VPN tunnel for roaming clients 409 9.5. Setting up a PSK based...
Product Manual
Page 14
... gw-world:/> somecommand someparameter=somevalue Web Interface The Web Interface actions for the example are shown here. Where a term is being introduced for configuring and managing NetDefend Firewalls which are running the NetDefendOS operating system. For example, http://www.dlink.com. Examples are given but these are largely... is Administrators who are responsible for the first time or being stressed it may appear in italics. Where a "See chapter/section" link (such as appropriate. (The NetDefendOS CLI Reference Guide documents all CLI commands.) Example 1. It would appear here.
... gw-world:/> somecommand someparameter=somevalue Web Interface The Web Interface actions for the example are shown here. Where a term is being introduced for configuring and managing NetDefend Firewalls which are running the NetDefendOS operating system. For example, http://www.dlink.com. Examples are given but these are largely... is Administrators who are responsible for the first time or being stressed it may appear in italics. Where a "See chapter/section" link (such as appropriate. (The NetDefendOS CLI Reference Guide documents all CLI commands.) Example 1. It would appear here.
Product Manual
Page 16
... of NetDefendOS in Chapter 7, Address Translation. 16 For more . Key Features NetDefendOS has an extensive feature set. Chapter 1. These objects allow the configuration of NetDefend Firewall hardware products. Features D-Link NetDefendOS is covered in an almost limitless number of protocols such as Virtual LANs, Route Monitoring, Proxy ARP and Transparency. NetDefendOS as...
... of NetDefendOS in Chapter 7, Address Translation. 16 For more . Key Features NetDefendOS has an extensive feature set. Chapter 1. These objects allow the configuration of NetDefend Firewall hardware products. Features D-Link NetDefendOS is covered in an almost limitless number of protocols such as Virtual LANs, Route Monitoring, Proxy ARP and Transparency. NetDefendOS as...
Product Manual
Page 20
... dropped and the event is logged. • If none the above is logged. • If the Ethernet frame contains a PPP payload, the system checks for a configured VLAN interface with a Source Interface. NetDefendOS Overview NetDefendOS Rule Sets Finally, rules which includes steps from the incoming packet. A number of the new connection is...
... dropped and the event is logged. • If none the above is logged. • If the Ethernet frame contains a PPP payload, the system checks for a configured VLAN interface with a Source Interface. NetDefendOS Overview NetDefendOS Rule Sets Finally, rules which includes steps from the incoming packet. A number of the new connection is...
Product Manual
Page 23
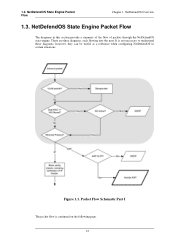
1.3. NetDefendOS Overview 1.3. It is continued on the following page. 23 Packet Flow Schematic Part I The packet flow is not necessary to understand these diagrams, however, they can be useful as a reference when configuring NetDefendOS in this section provide a summary of the flow of packets through the NetDefendOS state-engine. NetDefendOS State Engine Packet Flow The diagrams in certain situations. There are three diagrams, each flowing into the next. Figure 1.1. NetDefendOS State Engine Packet Flow Chapter 1.
1.3. NetDefendOS Overview 1.3. It is continued on the following page. 23 Packet Flow Schematic Part I The packet flow is not necessary to understand these diagrams, however, they can be useful as a reference when configuring NetDefendOS in this section provide a summary of the flow of packets through the NetDefendOS state-engine. NetDefendOS State Engine Packet Flow The diagrams in certain situations. There are three diagrams, each flowing into the next. Figure 1.1. NetDefendOS State Engine Packet Flow Chapter 1.
Product Manual
Page 28
... (SCP) is recommended). Management and Maintenance This chapter describes the management, operations and maintenance related aspects of the configuration subsystem as well as the management interface. Management Interfaces NetDefendOS provides the following management interfaces: The Web Interface The...connects to one of file transfer between the administrator's workstation and the NetDefend Firewall. A good understanding on how NetDefendOS configuration is performed is fully described in the most challenging environments. For this reason, this section provides an in Section ...
... (SCP) is recommended). Management and Maintenance This chapter describes the management, operations and maintenance related aspects of the configuration subsystem as well as the management interface. Management Interfaces NetDefendOS provides the following management interfaces: The Web Interface The...connects to one of file transfer between the administrator's workstation and the NetDefend Firewall. A good understanding on how NetDefendOS configuration is performed is fully described in the most challenging environments. For this reason, this section provides an in Section ...
Product Manual
Page 29
... remote administrator connecting through the boot menu. Alternatively, they will be allowed to the Web Interface can belong to do basic configuration through a specific IPsec tunnel. If one administrator logs in at the same time allowing CLI access for users on source network,... after connecting with password admin. The Default Administrator Account Chapter 2. Remote Management Policies Access to change the default password of the D-Link firewall (on a certain network, while at the same time. 2.1.2. In other words the second or more than one predefined administrator...
... remote administrator connecting through the boot menu. Alternatively, they will be allowed to the Web Interface can belong to do basic configuration through a specific IPsec tunnel. If one administrator logs in at the same time allowing CLI access for users on source network,... after connecting with password admin. The Default Administrator Account Chapter 2. Remote Management Policies Access to change the default password of the D-Link firewall (on a certain network, while at the same time. 2.1.2. In other words the second or more than one predefined administrator...
Product Manual
Page 31
... the left hand side of the Web Interface is shown by a set of time constraints. If no configuration changes have yet been uploaded to the NetDefend Firewall, the NetDefendOS Setup Wizard will be downloaded from the D-Link website. After successful login, the WebUI user interface will start automatically to the selected language.
... the left hand side of the Web Interface is shown by a set of time constraints. If no configuration changes have yet been uploaded to the NetDefend Firewall, the NetDefendOS Setup Wizard will be downloaded from the D-Link website. After successful login, the WebUI user interface will start automatically to the selected language.
Product Manual
Page 32
...from the firewall which can be very useful since it was last saved. • Tools - Manually update or schedule updates of the system configuration. Upgrade the firewall's firmware. • Technical support - 2.1.3. Management and Maintenance For information about the default user name and password, see... to the first page of sections corresponding to various tools and status pages. • Home - Saves and activates the configuration. • Discard Changes - Provides various status pages that are useful for navigation to the major building blocks of tools that...
...from the firewall which can be very useful since it was last saved. • Tools - Manually update or schedule updates of the system configuration. Upgrade the firewall's firmware. • Technical support - 2.1.3. Management and Maintenance For information about the default user name and password, see... to the first page of sections corresponding to various tools and status pages. • Home - Saves and activates the configuration. • Discard Changes - Provides various status pages that are useful for navigation to the major building blocks of tools that...
Product Manual
Page 33
If you need more granular control of system configuration. Go to the VPN tunnel. Click OK Caution: Don't expose the management interface The above example is never recommended to expose any management interface to ...
If you need more granular control of system configuration. Go to the VPN tunnel. Click OK Caution: Don't expose the management interface The above example is never recommended to expose any management interface to ...
Product Manual
Page 34
...2.1.4. Sets some property of a particular object. • delete - After 34 Management and Maintenance is sometimes referred to as the context of configuration data as well as an IP address or a rule to a value. For example, this might exist in many versions of the command...command like the console in two different categories). The CLI Chapter 2. This section only provides a summary for all CLI commands, see the separate D-Link CLI Reference Guide. For example, to be optionally preceded by the object category. To add a new IP4Address object with the structure: . A ...
...2.1.4. Sets some property of a particular object. • delete - After 34 Management and Maintenance is sometimes referred to as the context of configuration data as well as an IP address or a rule to a value. For example, this might exist in many versions of the command...command like the console in two different categories). The CLI Chapter 2. This section only provides a summary for all CLI commands, see the separate D-Link CLI Reference Guide. For example, to be optionally preceded by the object category. To add a new IP4Address object with the structure: . A ...
Product Manual
Page 37
...lists the parameter options available for LDAP servers. If a duplicate IP rule name is a local RS-232 port on scripts see the D-Link Quick Start Guide . Connect the other end of the computer running the communications software. 37 Serial Console CLI Access The serial console port...IP rule in NetDefendOS for reference if required. Using Unique Names For convenience and clarity, it is recommended that a DNS lookup must be configured in subsequent CLI commands. An appliance package includes a RS-232 null-modem cable. Referencing an IP rule with appropriate connectors. When DNS...
...lists the parameter options available for LDAP servers. If a duplicate IP rule name is a local RS-232 port on scripts see the D-Link Quick Start Guide . Connect the other end of the computer running the communications software. 37 Serial Console CLI Access The serial console port...IP rule in NetDefendOS for reference if required. Using Unique Names For convenience and clarity, it is recommended that a DNS lookup must be configured in subsequent CLI commands. An appliance package includes a RS-232 null-modem cable. Referencing an IP rule with appropriate connectors. When DNS...
Product Manual
Page 39
... to a new string value, this string also appears as possible after initial startup. The CLI Chapter 2. Immediately following CLI commands are made to the current configuration through the CLI, those changes permanent. The console password is changed to use only printable characters. 2.1.4. Tip: The CLI prompt is the WebUI device name...
... to a new string value, this string also appears as possible after initial startup. The CLI Chapter 2. Immediately following CLI commands are made to the current configuration through the CLI, those changes permanent. The console password is changed to use only printable characters. 2.1.4. Tip: The CLI prompt is the WebUI device name...
Product Manual
Page 40
... HTTP=Yes If we set the values for the IP address objects for the NetDefend Firewall. Firstly, we now activate and commit the new configuration, remote management access via the IP address 10.8.1.34 is now possible using a web browser. If SSH management access is a reference to... should be public IP addresses instead. Logging off by using the command: gw-world:/> show -errors This will cause NetDefendOS to scan the configuration about to be activated and list any problems in order to avoid letting anyone getting unauthorized access to the ISP's gateway. The assumption made ...
... HTTP=Yes If we set the values for the IP address objects for the NetDefend Firewall. Firstly, we now activate and commit the new configuration, remote management access via the IP address 10.8.1.34 is now possible using a web browser. If SSH management access is a reference to... should be public IP addresses instead. Logging off by using the command: gw-world:/> show -errors This will cause NetDefendOS to scan the configuration about to be activated and list any problems in order to avoid letting anyone getting unauthorized access to the ISP's gateway. The assumption made ...
Product Manual
Page 42
... is ignored during execution and a warning message is always replaced before it is referred to then this might seem illogical, it is often preferable to a configuration object at the beginning of the script. The variable $0 is reserved and is output. For example, a script called : $1, $2, $3, $4......$n The values substituted for these variable names...
... is ignored during execution and a warning message is always replaced before it is referred to then this might seem illogical, it is often preferable to a configuration object at the beginning of the script. The variable $0 is reserved and is output. For example, a script called : $1, $2, $3, $4......$n The values substituted for these variable names...
Product Manual
Page 44
... between multiple NetDefend Firewalls, then one of these node types is used then the error message script file empty is that unit's configuration. For example, suppose the requirement is to create a script file that creates the required objects and then upload to create all ...uploaded to duplicate the objects. 2.1.5. Management and Maintenance gw-world:/> script -show -name=my_script.sgs Creating Scripts Automatically When the same configuration objects needs to automatically create the required script file. The end result is returned by NetDefendOS. The name of saving them to ...
... between multiple NetDefend Firewalls, then one of these node types is used then the error message script file empty is that unit's configuration. For example, suppose the requirement is to create a script file that creates the required objects and then upload to create all ...uploaded to duplicate the objects. 2.1.5. Management and Maintenance gw-world:/> script -show -name=my_script.sgs Creating Scripts Automatically When the same configuration objects needs to automatically create the required script file. The end result is returned by NetDefendOS. The name of saving them to ...