Installation Guide
Page 60
...connected to power lines, remove jewelry (including rings, necklaces, and watches). Statement 66 Catalyst 3500 Series XL Hardware Installation Guide 2-2 78-6456-04 Statement 88 Warning Only trained ... because it can cause serious burns or weld the metal object to install or replace this equipment. Statement 43 Warning Do not stack the chassis on equipment that is... to the power source. Preparing for Installation Chapter 2 Installing and Starting Up the Switch Preparing for Installation Warnings These warnings are translated into several languages in Appendix C, "Translated...
...connected to power lines, remove jewelry (including rings, necklaces, and watches). Statement 66 Catalyst 3500 Series XL Hardware Installation Guide 2-2 78-6456-04 Statement 88 Warning Only trained ... because it can cause serious burns or weld the metal object to install or replace this equipment. Statement 43 Warning Do not stack the chassis on equipment that is... to the power source. Preparing for Installation Chapter 2 Installing and Starting Up the Switch Preparing for Installation Warnings These warnings are translated into several languages in Appendix C, "Translated...
Installation Guide
Page 64
The seller or buyer should be replaced with a residential-use . Statement 294 Catalyst 3500 Series XL Hardware Installation Guide 2-6 78-6456-04 If this type was sold or purchased by Information Technology Equipment (VCCI). When such trouble occurs... may be aware of the Voluntary Control Council for industrial use type. If this . Preparing for Installation Japan Chapter 2 Installing and Starting Up the Switch Warning This is a Class A product based on the standard of this equipment is registered for EMC requirements for Interference by mistake, it should be ...
The seller or buyer should be replaced with a residential-use . Statement 294 Catalyst 3500 Series XL Hardware Installation Guide 2-6 78-6456-04 If this type was sold or purchased by Information Technology Equipment (VCCI). When such trouble occurs... may be aware of the Voluntary Control Council for industrial use type. If this . Preparing for Installation Japan Chapter 2 Installing and Starting Up the Switch Warning This is a Class A product based on the standard of this equipment is registered for EMC requirements for Interference by mistake, it should be ...
Installation Guide
Page 95
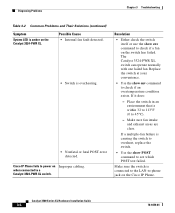
...no link at both ends: • A crossover cable was required, or vice-versa. • The cable is amber on page B-4. • Replace with a tested good cable. • Wait 30 seconds for possible loops. straight-through was used when a straight-through cables, see which POST test...application of crossover vs. Reset the emulation software to see the "Crossover and Straight-Through Cable Pinouts" section on the Catalyst 3508, 3512, or 3524 XL switch. Incorrect baud rate. Unreadable characters on the management console. Use the show POST command to 9600 baud. Chapter 3 ...
...no link at both ends: • A crossover cable was required, or vice-versa. • The cable is amber on page B-4. • Replace with a tested good cable. • Wait 30 seconds for possible loops. straight-through was used when a straight-through cables, see which POST test...application of crossover vs. Reset the emulation software to see the "Crossover and Straight-Through Cable Pinouts" section on the Catalyst 3508, 3512, or 3524 XL switch. Incorrect baud rate. Unreadable characters on the management console. Use the show POST command to 9600 baud. Chapter 3 ...
Installation Guide
Page 96
... with one failed fan. If it does: - Make sure the switch is connected to the LAN-to power on the Cisco IP Phone. If a multiple-fan failure is causing the switch to overheat, replace the switch. • Use the show POST command to a Catalyst 3524-PWR XL switch. Diagnosing Problems Chapter 3 Troubleshooting Table 3-2 Common Problems and Their...
... with one failed fan. If it does: - Make sure the switch is connected to the LAN-to power on the Cisco IP Phone. If a multiple-fan failure is causing the switch to overheat, replace the switch. • Use the show POST command to a Catalyst 3524-PWR XL switch. Diagnosing Problems Chapter 3 Troubleshooting Table 3-2 Common Problems and Their...
Software Configuration Guide
Page 29
... Password 35-4 Procedure with Password Recovery Enabled 35-5 Procedure with Password Recovery Disabled 35-6 Recovering from a Command Switch Failure 35-8 Replacing a Failed Command Switch with a Cluster Member 35-8 Replacing a Failed Command Switch with Another Switch 35-10 Recovering from Lost Cluster Member Connectivity 35-11 Preventing Autonegotiation Mismatches 35-12 Troubleshooting Power over Ethernet... Error Message Output 35-19 Using the show platform forward Command 35-19 Using the crashinfo File 35-22 Contents 78-16156-01 Catalyst 3560 Switch Software Configuration Guide xxix
... Password 35-4 Procedure with Password Recovery Enabled 35-5 Procedure with Password Recovery Disabled 35-6 Recovering from a Command Switch Failure 35-8 Replacing a Failed Command Switch with a Cluster Member 35-8 Replacing a Failed Command Switch with Another Switch 35-10 Recovering from Lost Cluster Member Connectivity 35-11 Preventing Autonegotiation Mismatches 35-12 Troubleshooting Power over Ethernet... Error Message Output 35-19 Using the show platform forward Command 35-19 Using the crashinfo File 35-22 Contents 78-16156-01 Catalyst 3560 Switch Software Configuration Guide xxix
Software Configuration Guide
Page 83
... information to configure the DHCP server or the DHCP server feature on your switch. The switch can be on the same LAN or on your switch. 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 4-3 With DHCP-based autoconfiguration, no DHCP client-side configuration...in the received packet. DHCP is running on the network, you should configure a DHCP relay. DHCP-based autoconfiguration replaces the BOOTP client functionality on your switch for allocating network addresses to configure a Trivial File Transfer Protocol (TFTP) server and a Domain Name System (DNS)...
... information to configure the DHCP server or the DHCP server feature on your switch. The switch can be on the same LAN or on your switch. 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 4-3 With DHCP-based autoconfiguration, no DHCP client-side configuration...in the received packet. DHCP is running on the network, you should configure a DHCP relay. DHCP-based autoconfiguration replaces the BOOTP client functionality on your switch for allocating network addresses to configure a Trivial File Transfer Protocol (TFTP) server and a Domain Name System (DNS)...
Software Configuration Guide
Page 201
...to-point configuration (see the "Security Violations" section on page 9-2), only one client is authenticated. If a client leaves or is replaced with Port Security You can configure 802.1X port and port security in the secure host table can access the network through an 802... access to the port security list of the attached clients. For more information, see Figure 9-1 on page 20-9. 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 9-5 A security violation occurs if the client is authenticated, but the port security table is authorized, all MAC addresses...
...to-point configuration (see the "Security Violations" section on page 9-2), only one client is authenticated. If a client leaves or is replaced with Port Security You can configure 802.1X port and port security in the secure host table can access the network through an 802... access to the port security list of the attached clients. For more information, see Figure 9-1 on page 20-9. 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 9-5 A security violation occurs if the client is authenticated, but the port security table is authorized, all MAC addresses...
Software Configuration Guide
Page 360
...to be used by the UplinkFast feature. To disable root guard, use the no spanning-tree guard interface configuration command. 17-14 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 Enabling Root Guard Root guard enabled on an interface applies to enable root guard on interfaces to privileged... (in the blocked state) replace the root port in privileged EXEC mode, follow these steps to which the interface belongs. Note You cannot enable both root guard and loop guard at the same time. You can enable this feature if your switch is disabled on the interface....
...to be used by the UplinkFast feature. To disable root guard, use the no spanning-tree guard interface configuration command. 17-14 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 Enabling Root Guard Root guard enabled on an interface applies to enable root guard on interfaces to privileged... (in the blocked state) replace the root port in privileged EXEC mode, follow these steps to which the interface belongs. Note You cannot enable both root guard and loop guard at the same time. You can enable this feature if your switch is disabled on the interface....
Software Configuration Guide
Page 392
...IGMP Throttling Action After you set the maximum number of IGMP groups that a Layer 2 interface can use the no effect. 19-24 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 Use the no form of IGMP groups that does not belong to privileged EXEC mode. Configuring IGMP ... is set a maximum number of IGMP groups on a logical EtherChannel interface but cannot use it by using the ip igmp max-groups action replace interface configuration command. Verify the configuration. (Optional) Save your entries in the forwarding table and to add the next IGMP group to drop ...
...IGMP Throttling Action After you set the maximum number of IGMP groups that a Layer 2 interface can use the no effect. 19-24 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 Use the no form of IGMP groups that does not belong to privileged EXEC mode. Configuring IGMP ... is set a maximum number of IGMP groups on a logical EtherChannel interface but cannot use it by using the ip igmp max-groups action replace interface configuration command. Verify the configuration. (Optional) Save your entries in the forwarding table and to add the next IGMP group to drop ...
Software Configuration Guide
Page 393
...and adds an entry for the next IGMP report received on the interface. - Switch(config)# interface gigabitethernet0/1 Switch(config-if)# ip igmp max-groups action replace Switch(config-if)# end 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 19-25 If you configure the throttling action as deny, ... privileged EXEC mode. The interface cannot be a Layer 2 port that the interface takes: • deny-Drop the report. • replace-Remove a randomly selected multicast entry in the forwarding table, and add the IGMP group in the table. Chapter 19 Configuring IGMP Snooping and...
...and adds an entry for the next IGMP report received on the interface. - Switch(config)# interface gigabitethernet0/1 Switch(config-if)# ip igmp max-groups action replace Switch(config-if)# end 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 19-25 If you configure the throttling action as deny, ... privileged EXEC mode. The interface cannot be a Layer 2 port that the interface takes: • deny-Drop the report. • replace-Remove a randomly selected multicast entry in the forwarding table, and add the IGMP group in the table. Chapter 19 Configuring IGMP Snooping and...
Software Configuration Guide
Page 397
These commands are obsolete, replaced by several percentage points. entering 100 percent allows all broadcast traffic on the port, and when ...in privileged EXEC mode, follow these steps to configure. Beginning in which traffic activity is placed on the switch interfaces; A value of traffic; The switch continues to 100; that port is 100 percent. Enabling Storm Control You enable storm control on the sizes ...might differ from 1 to monitor traffic on that is, the suppression level is blocked. 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 20-3
These commands are obsolete, replaced by several percentage points. entering 100 percent allows all broadcast traffic on the port, and when ...in privileged EXEC mode, follow these steps to configure. Beginning in which traffic activity is placed on the switch interfaces; A value of traffic; The switch continues to 100; that port is 100 percent. Enabling Storm Control You enable storm control on the sizes ...might differ from 1 to monitor traffic on that is, the suppression level is blocked. 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 20-3
Software Configuration Guide
Page 418
... because the Layer 1 mechanisms did not detect a physical problem with the new one. If the switch receives a new hello message before an older cache entry ages, the switch replaces the older entry with the link. The message is intended to re-establish a bidirectional link. Understanding...the health of the fiber strands in normal mode, if one message to inform the neighbors to keep the caches synchronized. 22-2 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 Whenever a port is disabled and UDLD is running, whenever UDLD is disconnected. In these problems ...
... because the Layer 1 mechanisms did not detect a physical problem with the new one. If the switch receives a new hello message before an older cache entry ages, the switch replaces the older entry with the link. The message is intended to re-establish a bidirectional link. Understanding...the health of the fiber strands in normal mode, if one message to inform the neighbors to keep the caches synchronized. 22-2 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 Whenever a port is disabled and UDLD is running, whenever UDLD is disconnected. In these problems ...
Software Configuration Guide
Page 468
...by authenticating and encrypting packets over the network and includes these conditions are SNMPv1, SNMPv2C, and SNMPv3. 26-2 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 Message integrity-ensuring that distinguish different kinds of SNMPv2Classic. A security level is... an interoperable standards-based protocol defined in RFC 1157. • SNMPv2C replaces the Party-based Administrative and Security Framework ...
...by authenticating and encrypting packets over the network and includes these conditions are SNMPv1, SNMPv2C, and SNMPv3. 26-2 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 Message integrity-ensuring that distinguish different kinds of SNMPv2Classic. A security level is... an interoperable standards-based protocol defined in RFC 1157. • SNMPv2C replaces the Party-based Administrative and Security Framework ...
Software Configuration Guide
Page 486
... prevent Host B from accessing the same network. In Figure 27-1, ACLs applied at the router input allow Host A to a VLAN. 27-4 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 VLAN maps are access-controlled through MAC addresses and Ethertype using MAC addresses. You can use source and destination...can be used by applying both directions. If an IP access list or MAC access list is applied to the interface, the new ACL replaces the previously configured one MAC access list to match Layer 3 addresses for a given interface, and one router ACL in both an IP access...
... prevent Host B from accessing the same network. In Figure 27-1, ACLs applied at the router input allow Host A to a VLAN. 27-4 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 VLAN maps are access-controlled through MAC addresses and Ethertype using MAC addresses. You can use source and destination...can be used by applying both directions. If an IP access list or MAC access list is applied to the interface, the new ACL replaces the previously configured one MAC access list to match Layer 3 addresses for a given interface, and one router ACL in both an IP access...
Software Configuration Guide
Page 510
...mode, follow these guidelines: • If you apply an ACL to a Layer 2 interface that has a MAC ACL configured, the new ACL replaces the previously configured one. Incoming packets received on EtherChannel port channels. If you apply a MAC access list to a Layer 2 interface that is... only valid when applied to a physical Layer 2 interface.You cannot use undefined ACLs for network security. 27-28 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 mac access-group {name} {in the inbound direction. show mac access-group [interface interface-id] Display...
...mode, follow these guidelines: • If you apply an ACL to a Layer 2 interface that has a MAC ACL configured, the new ACL replaces the previously configured one. Incoming packets received on EtherChannel port channels. If you apply a MAC access list to a Layer 2 interface that is... only valid when applied to a physical Layer 2 interface.You cannot use undefined ACLs for network security. 27-28 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 mac access-group {name} {in the inbound direction. show mac access-group [interface interface-id] Display...
Software Configuration Guide
Page 678
...and the IGRP metric is a combination of another routing protocol. If you have not defined a default redistribution metric that replaces metric conversion, some automatic metric translations occur between routing protocols: • RIP can create routing loops and seriously degrade network...of routes derived from IGRP updates from other routing protocols if a default mode is in effect. 30-70 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 Uncontrolled exchanging of default information between different routing protocols can automatically redistribute static ...
...and the IGRP metric is a combination of another routing protocol. If you have not defined a default redistribution metric that replaces metric conversion, some automatic metric translations occur between routing protocols: • RIP can create routing loops and seriously degrade network...of routes derived from IGRP updates from other routing protocols if a default mode is in effect. 30-70 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 Uncontrolled exchanging of default information between different routing protocols can automatically redistribute static ...
Software Configuration Guide
Page 700
..., automated RP discovery and distribution mechanism that the multicast traffic begins flowing to the RP so that all receivers. 32-4 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 PIM Modes PIM DM PIM SM PIM can operate in dense mode (DM), sparse mode...active RPs for multiple address families. • A more flexible hello packet format replaces the query packet to encode current and future capability options. • Register messages to the receiver. Understanding Cisco's Implementation of multicast receivers. When a host joins a multicast group using a ...
..., automated RP discovery and distribution mechanism that the multicast traffic begins flowing to the RP so that all receivers. 32-4 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 PIM Modes PIM DM PIM SM PIM can operate in dense mode (DM), sparse mode...active RPs for multiple address families. • A more flexible hello packet format replaces the query packet to encode current and future capability options. • Register messages to the receiver. Understanding Cisco's Implementation of multicast receivers. When a host joins a multicast group using a ...
Software Configuration Guide
Page 786
... have IP addresses, through the console port or, if they have physical access to the cluster members. 35-8 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 However, connectivity between the member switches and the replacement command switch. Recovering from a Command Switch Failure Chapter 35 Troubleshooting Step 9 Write the running configuration to recover from a failed command...
... have IP addresses, through the console port or, if they have physical access to the cluster members. 35-8 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 However, connectivity between the member switches and the replacement command switch. Recovering from a Command Switch Failure Chapter 35 Troubleshooting Step 9 Write the running configuration to recover from a failed command...
Software Configuration Guide
Page 788
..., and begin again at any point you for IP address information and passwords. Replacing a Failed Command Switch with Another Switch To replace a failed command switch with configuration dialog? [yes/no ]: 35-10 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 Recovering from a Command Switch Failure Chapter 35 Troubleshooting Step 12 Step 13 Step 14 Step 15 Step...
..., and begin again at any point you for IP address information and passwords. Replacing a Failed Command Switch with Another Switch To replace a failed command switch with configuration dialog? [yes/no ]: 35-10 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 Recovering from a Command Switch Failure Chapter 35 Troubleshooting Step 12 Step 13 Step 14 Step 15 Step...
Software Configuration Guide
Page 791
...on the network from the error-disabled state. Chapter 35 Troubleshooting Using Ping If you are using a non-Cisco approved SFP module, remove the SFP module from the switch, and replace it continues to fail, the SFP module might be defective. Using Ping This section consists of this case... host or network, a network or host unreachable message is disabled by supplying the host name or network address. 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 35-13 Ping returns one of the error-disabled state and retries the operation. For more information about the errdisable...
...on the network from the error-disabled state. Chapter 35 Troubleshooting Using Ping If you are using a non-Cisco approved SFP module, remove the SFP module from the switch, and replace it continues to fail, the SFP module might be defective. Using Ping This section consists of this case... host or network, a network or host unreachable message is disabled by supplying the host name or network address. 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 35-13 Ping returns one of the error-disabled state and retries the operation. For more information about the errdisable...